-
Cisco Unified Communications Manager Express System Administrator Guide
-
Feature Map
-
Feature History
-
Cisco Unified CME Overview
-
Before You Begin
-
Installing and Upgrading Cisco Unified CME Software
- Setting Up Basic Configuration
-
Configuring Dialing Plans
-
Configuring Localization Support
-
Configuring Transcoding Resources
-
Configuring Video Transcoding
-
Configuring Toll Fraud Prevention
-
Enabling the GUI
-
Integrating Voice Mail
-
Configuring Security
-
Adding Features
-
Configuring Automatic Line Selection
-
Configuring Barge and Privacy
-
Configuring Call Blocking
-
Configuring Call Park
-
Call Restriction Regulations
-
Configuring Call Transfer and Forwarding
-
Configuring Call-Coverage Features
-
Configuring Caller ID Blocking
-
Configuring Conferencing
-
Configuring Video Conferences
-
Configuring Voice and Video Hardware Conferencing
-
Configuring Directory Services
-
Configuring Do Not Disturb
-
Configuring Enhanced 911 Services
-
Configuring Extension Mobility
-
Configuring Fax Relay
-
Configuring Feature Access Codes
-
Configuring Forced Authorization
-
Configuring Headset Auto-Answer
-
Configuring Intercom Lines
-
Configuring Loopback Call Routing
-
Configuring MLPP
-
Configuring Music on Hold
-
Configuring Paging
-
Configuring Presence Service
-
Configuring Ring Tones
-
Configuring Single Number Reach
-
Customizing Soft Keys
-
Configuring Speed Dial
-
Configuring Video Support
-
Configuring SSL VPN Client for SCCP IP Phones
-
-
Creating Templates
-
Modifying Cisco Unified IP Phone Options
-
Configuring Interoperability with Cisco Unified CCX
-
Configuring the CTI CSTA Protocol Suite
-
Configuring SRST Fallback Mode
-
Configuring VRF Support on Cisco Unified CME
-
Configuring the XML API
-
Index
-
Table Of Contents
Phone Authentication Components
Configuration File Maintenance
Manually Importing MIC Root Certificate
Feature Design of Media Encryption
Secure SIP Trunk Support on Cisco Unified CME
Secure Cisco Unified CME in an H.450 Environment
Secure Cisco Unified CME in a Non H.450 Environment
Secure Transcoding for Remote Phones with DSP Farm Transcoding Configured
Secure Cisco Unified CME with Cisco Unity Express
Secure Cisco Unified CME with Cisco Unity
HTTPS Provisioning For Cisco Unified IP Phones
HTTPS support for an External Server
HTTPS Support in Cisco Unified CME
Configuring the Cisco IOS Certification Authority
Obtaining Certificates for Server Functions
Configuring Telephony-Service Security Parameters
Verifying Telephony-Service Security Parameters
Configuring the CTL Client on a Cisco Unified CME Router
Configuring the CTL Client on a Router That is Not a Cisco Unified CME Router
Configuring Ephone Security Parameters
Verifying Ephone Security Parameters
Configuring the Registration Authority
Entering the Authentication String on the Phone
Manually Importing the MIC Root Certificate
Configuring Media Encryption (SRTP) in Cisco Unified CME
Configuring Cisco Unified CME SRTP Fallback for H.323 Dial Peers
Configuring Cisco Unity for Secure Cisco Unified CME Operation
Configuring Integration Between Cisco Unified CME and Cisco Unity
Importing the Cisco Unity Root Certificate to Cisco Unified CME
Configuring Cisco Unity Ports for Secure Registration
HTTPS Provisioning for Cisco Unified IP Phones
Configuration Examples for Security
Manually Importing MIC Root Certificate on the Cisco Unified CME Router: Example
Telephony-Service Security Parameters: Example
CTL Client Running on Cisco Unified CME Router: Example
Secure Cisco Unified CME: Example
Configuring HTTPS Support for Cisco Unified CME: Example
Feature Information for Security
Configuring Security
Last Updated: July 25, 2013This chapter describes the phone authentication support in Cisco Unified Communications Manager Express (Cisco Unified CME), Hypertext Transfer Protocol Secure (HTTPS) provisioning for Cisco Unified IP Phones, and the Media Encryption (SRTP) on Cisco Unified CME feature that provides the following secure voice call capabilities:
•
Secure call control signaling and media streams in Cisco Unified CME networks using Secure Real-Time Transport Protocol (SRTP) and H.323 protocols.
•
Secure supplementary services for Cisco Unified CME networks using H.323 trunks.
•
Secure Cisco VG224 Analog Phone Gateway endpoints.
Finding Feature Information in This Module
Your Cisco Unified CME version may not support all of the features documented in this module. For a list of the versions in which each feature is supported, see the "Feature Information for Security" section.
Contents
•
Configuration Examples for Security
•
Feature Information for Security
Prerequisites for Security
•
Cisco Unified CME 4.0 or a later version for Phone Authentication.
•
Cisco Unified CME 4.2 or a later version for Media Encryption (SRTP) on Cisco Unified CME.
•
Cisco IOS feature set Advanced Enterprise Services (adventerprisek9) or Advanced IP Services (advipservicesk9) on supported platforms.
•
Firmware 9.0(4) or a later version must be installed on the IP phone for HTTPS provisioning.
•
System clock must be set by using one of the following methods:
–
Configure Network Time Protocol (NTP). For configuration information, see the "Enabling Network Time Protocol on the Cisco Unified CME Router" section.
–
Manually set the software clock using the clock set command. For information about this command, see Cisco IOS Network Management Command Reference.
Restrictions for Security
Phone Authentication
•
Cisco Unified CME phone authentication is not supported on the Cisco IAD 2400 series or the Cisco 1700 series.
Media Encryption
•
Secure three-way software conferencing is not supported. A secure call beginning with SRTP will always fall back to nonsecure Real-Time Transport Protocol (RTP) when it is joined to a conference.
•
If a party drops from a three-party conference, the call between the remaining two parties returns to secure if the two parties are SRTP-capable local Skinny Client Control Protocol (SCCP) endpoints to a single Cisco Unified CME and the conference creator is one of the remaining parties. If either of the two remaining parties are only RTP-capable, the call remains nonsecure. If the two remaining parties are connected through FXS, PSTN, or VoIP, the call remains nonsecure.
•
Calls to Cisco Unity Express are not secure.
•
Music on Hold (MOH) is not secure.
•
Video calls are not secure.
•
Modem relay and T.3 fax relay calls are not secure.
•
Media flow-around is not supported for call transfer and call forward.
•
Conversion between inband tone and RFC 2833 DTMF is not supported. RFC 2833 DTMF handling is supported when encryption keys are sent to secure DSP Farm devices but is not supported for codec passthrough.
•
Secure Cisco Unified CME supports SIP trunks and H.323 trunks.
•
Secure calls are supported in the default session application only.
Information About Security
To enable security, you should understand the following concepts:
Phone Authentication
•
Phone Authentication Overview
•
Phone Authentication Components
•
Configuration File Maintenance
•
Manually Importing MIC Root Certificate
Media Encryption
•
Feature Design of Media Encryption
•
Secure Supplementary Services
•
Secure SIP Trunk Support on Cisco Unified CME
•
Secure Transcoding for Remote Phones with DSP Farm Transcoding Configured
•
Secure Cisco Unified CME with Cisco Unity Express
•
Secure Cisco Unified CME with Cisco Unity
HTTPS Support for an External Server
•
HTTPS support for an External Server
•
HTTPS Support in Cisco Unified CME
Phone Authentication Overview
Phone authentication is a security infrastructure for providing secure SCCP signaling between Cisco Unified CME and IP phones. The goal of Cisco Unified CME phone authentication is to create a secure environment for a Cisco Unified CME IP telephony system.
Phone authentication addresses the following security needs:
•
Establishing the identity of each endpoint in the system
•
Authenticating devices
•
Providing signaling-session privacy
•
Providing protection for configuration files
Cisco Unified CME phone authentication implements authentication and encryption to prevent identity theft of the phone or Cisco Unified CME system, data tampering, call-signaling tampering, or media-stream tampering. To prevent these threats, the Cisco Unified IP telephony network establishes and maintains authenticated communication streams, digitally signs files before they are transferred to phones, and encrypts call signaling between Cisco Unified IP phones.
Cisco Unified CME phone authentication depends on the following processes:
Phone Authentication
The phone authentication process occurs between the Cisco Unified CME router and a supported device when each entity accepts the certificate of the other entity; only then does a secure connection between the entities occur. Phone authentication relies on the creation of a Certificate Trust List (CTL) file, which is a list of known, trusted certificates and tokens. Phones communicate with Cisco Unified CME using a Transport Layer Security (TLS) session connection, which requires that the following criteria be met:
•
A certificate must exist on the phone.
•
A phone configuration file must exist on the phone, and the Cisco Unified CME entry and certificate must exist in the file.
File Authentication
The file authentication process validates digitally signed files that a phone downloads from a Trivial File Transfer Protocol (TFTP) server—for example, configuration files, ring list files, locale files, and CTL files. When the phone receives these types of files from the TFTP server, the phone validates the file signatures to verify that file tampering did not occur after the files were created.
Signaling Authentication
The signaling authentication process, also known as signaling integrity, uses the TLS protocol to validate that signaling packets have not been tampered with during transmission. Signaling authentication relies on the creation of the CTL file.
Public Key Infrastructure
Cisco Unified CME phone authentication uses the public-key-infrastructure (PKI) capabilities in Cisco IOS software for certificate-based authentication of IP phones. PKI provides customers with a scalable, secure mechanism for distributing, managing, and revoking encryption and identity information in a secure data network. Every entity (a person or a device) participating in the secure communication is enrolled in the PKI using a process in which the entity generates a Rivest-Shamir-Adleman (RSA) key pair (one private key and one public key) and has its identity validated by a trusted entity (also known as a certification authority [CA] or trustpoint).
After each entity enrolls in a PKI, every peer (also known as an end host) in a PKI is granted a digital certificate that has been issued by a CA.
When peers must negotiate a secure communication session, they exchange digital certificates. Based on the information in the certificate, a peer can validate the identity of another peer and establish an encrypted session with the public keys contained in the certificate.
For more information about PKI, see the "Implementing and Managing a PKI Features Roadmap" section of Cisco IOS Security Configuration Guide for your Cisco IOS release.
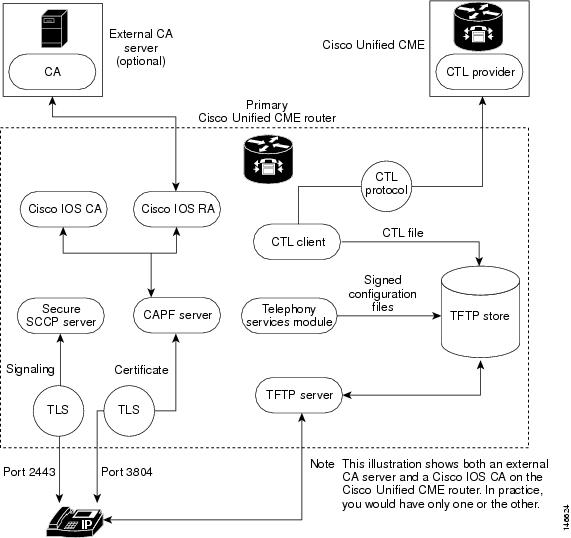
Phone Authentication Components
A variety of components work together to ensure secure communications in a Cisco Unified CME system. Table 5 describes the Cisco Unified CME phone authentication components.
Figure 3 shows the components in a Cisco Unified CME phone authentication environment.
Figure 3 Cisco Unified CME Phone Authentication
Phone Authentication Process
The following is a high-level summary of the phone-authentication process.
To enable Cisco Unified CME phone authentication:
1.
Certificates are issued.
The CA issues certificates to Cisco Unified CME, SAST, CAPF, and TFTP functions.
2.
The CTL file is created, signed and published.
a.
The CTL file is created by the CTL client, which is configuration driven. Its goal is to create a CTLfile.tlv for each phone and deposit it in the TFTP directory. To complete its task, the CTL client needs the certificates and public key information of the CAPF server, Cisco Unified CME server, TFTP server, and SASTs.
b.
The CTL file is signed by the SAST credentials. There are two SAST records pertaining to two different certificates in the CTL file for security reasons. If one of the certificates is lost or compromised, then the CTL client regenerates the CTL file using the other certificate. When a phone downloads the new CTL file, it verifies the download with only one of the two original public keys that was installed earlier. This mechanism prevents IP phones from accepting CTL files from unknown sources.
c.
The CTL file is published on the TFTP server. Because an external TFTP server is not supported in secure mode, the configuration files are generated by the Cisco Unified CME system itself and are digitally signed by the TFTP server's credentials. The TFTP server credentials can be the same as the Cisco Unified CME credentials. If desired, a separate certificate can be generated for the TFTP function if the appropriate trustpoint is configured under the CTL-client interface.
3.
The telephony service module signs phone configuration files and each phone requests its file.
4.
When an IP phone boots up, it requests the CTL file (CTLfile.tlv) from the TFTP server and downloads its digitally signed configuration file, which has the filename format of SEP<mac-address>.cnf.xml.sgn.
5.
The phone then reads the CAPF configuration status from the configuration file. If a certificate operation is needed, the phone initiates a TLS session with the CAPF server on TCP port 3804 and begins the CAPF protocol dialogue. The certificate operation can be an upgrade, delete, or fetch operation. If an upgrade operation is needed, the CAPF server makes a request on behalf of the phone for a certificate from the CA. The CAPF server uses the CAPF protocol to obtain the information it needs from the phone, such as the public key and phone ID. After the phone successfully receives a certificate from the server, the phone stores it in its flash memory.
6.
With the certificate in its flash, the phone initiates a TLS connection with the secure Cisco Unified CME server on a well-known TCP port (2443) if the device security mode settings in the .cnf.xml file are set to authenticated or encrypted. This TLS session is mutually authenticated by both parties. The IP phone knows the Cisco Unified CME server's certificate from the CTL file, which it initially downloaded from the TFTP server. The phone's LSC is a trusted party for the Cisco Unified CME server because the issuing CA certificate is present in the router.
Startup Messages
If the certificate server is part of your startup configuration, you may see the following messages during the boot procedure:
% Failed to find Certificate Server's trustpoint at startup
% Failed to find Certificate Server's cert.
These messages are informational messages that show a temporary inability to configure the certificate server because the startup configuration has not been fully parsed yet. The messages are useful for debugging if the startup configuration has been corrupted.
Configuration File Maintenance
In a secure environment, several types of configuration files must be digitally signed before they can be hosted and used. The filenames of all signed files have a .sgn suffix.
The Cisco Unified CME telephony service module creates phone configuration files (.cnf.xml suffix) and hosts them on a Cisco IOS TFTP server. These files are signed by the TFTP server's credentials.
In addition to the phone configuration files, other Cisco Unified CME configuration files such as the network and user-locale files must be signed. These files are internally generated by Cisco Unified CME, and the signed versions are automatically created in the current code path whenever the unsigned versions are updated or created.
Other configuration files that are not generated by Cisco Unified CME, such as ringlist.xml, distinctiveringlist.xml, audio files, and so forth, are often used for Cisco Unified CME features. Signed versions of these configuration files are not automatically created. Whenever a new configuration file that has not been generated by Cisco Unified CME is imported into Cisco Unified CME, use the load-cfg-file command, which does all of the following:
•
Hosts the unsigned version of the file on the TFTP server.
•
Creates a signed version of the file.
•
Hosts the signed version of the file on the TFTP server.
You can also use the load-cfg-file command instead of the tftp-server command when only the unsigned version of a file needs to be hosted on the TFTP server.
CTL File Maintenance
The CTL file contains the SAST records and other records. (A maximum of two SAST records may exist.) The CTL file is digitally signed by one of the SAST credentials that are listed in the CTL file before the CTL file is downloaded by the phone and saved in its flash. After receiving the CTL file, a phone trusts a newer or changed CTL file only if it is signed by one of the SAST credentials that is present in the original CTL file.
For this reason, you should take care to regenerate the CTL file only with one of the original SAST credentials. If both SAST credentials are compromised and a CTL file must be generated with a new credential, you must reset the phone to its factory defaults.
CTL Client and Provider
The CTL client generates the CTL file. The CTL client must be provided with the names of the trustpoints it needs for the CTL file. It can run on the same router as Cisco Unified CME or on another, standalone router. When the CTL client runs on a standalone router (not a Cisco Unified CME router), you must configure a CTL provider on each Cisco Unified CME router. The CTL provider securely communicates the credentials of the Cisco Unified CME server functions to the CTL client that is running on another router.
When the CTL client is running on either a primary or secondary Cisco Unified CME router, you must configure a CTL provider on each Cisco Unified CME router on which the CTL client is not running.
The CTL protocol is used to communicate between the CTL client and a CTL provider. Using the CTL protocol ensures that the credentials of all Cisco Unified CME routers are present in the CTL file and that all Cisco Unified CME routers have access to the phone certificates that were issued by the CA. Both elements are prerequisites to secure communications.
To enable CTL clients and providers, see the "Configuring the CTL Client" section and the "Configuring the CTL Provider" section.
Manually Importing MIC Root Certificate
When a phone uses a MIC for authentication during the TLS handshake with the CAPF server, the CAPF server must have a copy of the MIC to verify it. Different certificates are used for different types of IP phones.
A phone uses a MIC for authentication when it has a MIC but no LSC. For example, you have a Cisco Unified IP Phone 7970 that has a MIC by default but no LSC. When you schedule a certificate upgrade with the authentication mode set to MIC for this phone, the phone presents its MIC to the Cisco Unified CME CAPF server for authentication. The CAPF server must have a copy of the MIC's root certificate to verify the phone's MIC. Without this copy, the CAPF upgrade operation fails.
To ensure that the CAPF server has copies of the MICs it needs, you must manually import certificates to the CAPF server. The number of certificates that you must import depends on your network configuration. Manual enrollment refers to copy-and-paste or TFTP transfer methods.
For more information on certificate enrollment, see the "Configuring Cut-and-Paste Certificate Enrollment" section of the "Configuring Certificate Enrollment for a PKI" chapter in Cisco IOS Security Configuration Guide for your Cisco IOS release.
To manually import the MIC root certificate, see the "Manually Importing the MIC Root Certificate" section.
Feature Design of Media Encryption
Companion voice security Cisco IOS features provide an overall architecture for secure end-to-end IP telephony calls on supported network devices that enable the following:
•
SRTP-capable Cisco Unified CME networks with secure interoperability
•
Secure Cisco IP phone calls
•
Secure Cisco VG224 Analog Phone Gateway endpoints
•
Secure supplementary services
These features are implemented using media and signaling authentication and encryption in Cisco IOS H.323 networks. H.323, the ITU-T standard that describes packet-based video, audio, and data conferencing, refers to a set of other standards, including H.450, to describe its actual protocols. H.323 allows dissimilar communication devices to communicate with each other by using a standard communication protocol and defines a common set of codecs, call setup and negotiating procedures, and basic data transport methods. H.450, a component of the H.323 standard, defines signaling and procedures that are used to provide telephony-like supplementary services. H.450 messages are used in H.323 networks to implement secure supplementary service support and also empty capability set (ECS) messaging for media capability negotiation.
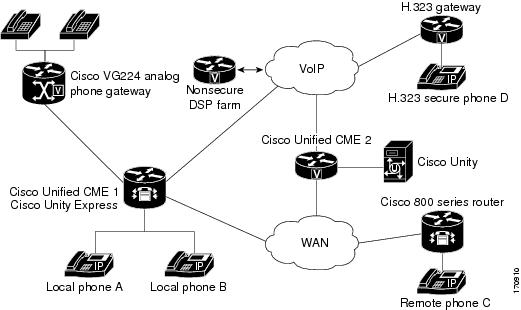
Secure Cisco Unified CME
The secure Cisco Unified CME solution includes secure-capable voice ports, SCCP endpoints, and a secure H.323 trunk between Cisco Unified CME and Cisco Unified Communications Manager for audio media. SIP trunks are not supported. Figure 4 shows the components of a secure Cisco Unified CME system.
Figure 4 Secure Cisco Unified CME System
Secure Cisco Unified CME implements call control signaling using Transport Layer Security (TLS) or IPsec (IP Security) for the secure channel and uses SRTP for media encryption. Secure Cisco Unified CME manages the SRTP keys to endpoints and gateways.
The Media Encryption (SRTP) on Cisco Unified CME feature supports the following features:
•
Secure voice calls using SRTP for SCCP endpoints.
•
Secure voice calls in a mixed shared line environment that allows both RTP- and SRTP-capable endpoints; shared line media security depends on the endpoint configuration.
•
Secure supplementary services using H.450 including:
–
Call forward
–
Call transfer
–
Call hold and resume
–
Call park and call pickup
–
Nonsecure software conference
Note
SRTP conference calls over H.323 may experience a zero- to two-second noise interval when the call is joined to the conference.
•
Secure calls in a non-H.450 environment.
•
Secure Cisco Unified CME interaction with secure Cisco Unity.
•
Secure Cisco Unified CME interaction with Cisco Unity Express (interaction is supported and calls are downgraded to nonsecure mode).
•
Secure transcoding for remote phones with DSP Farm transcoding configured.
These features are discussed in the following sections.
Secure Supplementary Services
The Media Encryption (SRTP) feature supports secure supplementary services in both H.450 and non-H.450 Cisco Unified CME networks. A secure Cisco Unified CME network should be either H.450 or non-H.450, not a hybrid.
Secure SIP Trunk Support on Cisco Unified CME
Prior to Cisco Unified CME Relese 10 release, supplementary services were not supported on the secure SIP trunk of the secure SCCP Cisco Unified CME. This feature supports the following supplementary services in the secure SRTP and SRTP fallback modes on the SIP trunk of the SCCP Cisco Unified CME:
•
Basic secure calls
•
Call hold and resume
•
Call transfer (blind and consult)
•
Call forward (CFA,CFB,CFNA)
•
DTMF support
•
Call park and pickup
•
Voice mail systems using CUE (works only with SRTP fallback mode)
To enable the supplementary services, use the existing "supplementary-service media-renegotiate" command as shown in the following example:
(config)# voice service voip(conf-voi-serv)# no ip address trusted authenticate(conf-voi-serv)# srtp(conf-voi-serv)# allow-connections sip to sip(conf-voi-serv)# no supplementary-service sip refer(conf-voi-serv)# supplementary-service media-renegotiate
Note
In the SRTP mode, nonsecure media (RTP) format is not allowed across the secure SIP trunk. For Music On Hold, Tone On Hold, and Ring Back Tone, the tone is not played across the SIP trunk. In SRTP fallback mode, media across the secure SIP trunk is switched over to RTP if the remote end is nonsecure or while playing the MMusic On Hold, Tone On Hold, and Ring Back Tone.
Restrictions
•
Secure SIP trunk is supported only on SCCP Cisco Unified CME and not on SIP Cisco Unified CME. Secure SIP lines are not supported on the Cisco Unified CME mode.
•
Xcoder support is not available for playing secure tones (Music On Hold, Tone On Hold, and Ring Back Tone).
•
Tones are not played in the SRTP mode because these tones are available only in non-secure (RTP) format.
•
We recommend that you configure no supplementary-service sip refer command for SCCP Cisco Unfied CME for the supplementary services.
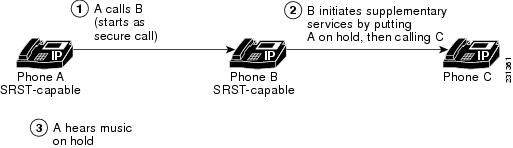
Secure Cisco Unified CME in an H.450 Environment
Signaling and media encryption among secure endpoints is supported, enabling supplementary services such as call transfer (H.450.2) and call forward (H.450.3) between secure endpoints. Call park and pick up use H.450 messages. Secure Cisco Unified CME is H.450-enabled by default; however, secure music on hold (MOH) and secure conferences (three-way calling) are not supported. For example, when supplementary services are initiated as shown in Figure 5, ECS and Terminal Capabilities Set (TCS) are used to negotiate the initially secure call between A and B down to RTP so A can hear MOH. When B resumes the call to A, the call goes back to SRTP. Similarly, when a transfer is initiated, the party being transferred is put on hold and the call is negotiated down to RTP. When the call is transferred, it goes back to SRTP if the other end is SRTP capable.
Figure 5 Music on Hold in an H.450 Environment
Secure Cisco Unified CME in a Non H.450 Environment
Security for supplementary services requires midcall key negotiation or midcall media renegotiation. In an H.323 network where there are no H.450 messages, media renegotiation is implemented using ECS for scenarios such as mismatched codecs and secure calls. If you disable H.450 on the router globally, the configuration is applied to RTP and SRTP calls. The signaling path is hairpin on XOR for Cisco Unified CME and Cisco Unified Communications Manager. For example, in Figure 6, the signaling path goes from A through B (the supplementary services initiator) to C. When deploying voice security in this scenario, consider that the media security keys will pass through XOR, that is, through B, the endpoint that issued the transfer request. To avoid the man-in-the-middle attack, the XOR must be a trusted entity.
Figure 6 Transfer in a Non-H.450 Environment
The media path is optional. The default media path for Cisco Unified CME is hairpin. However, whenever possible media flow around can be configured on Cisco Unified CME. When configuring media flow through, which is the default, remember that chaining multiple XOR gateways in the media path introduces more delay and thus reduces voice quality. Router resources and voice quality limit the number of XOR gateways that can be chained. The requirement is platform dependent and may vary between signaling and media. The practical chaining level is three.
A transcoder is inserted when there is a codec mismatch and ECS and TCS negotiation fails. For example, if Phone A and Phone B are SRTP capable, but Phone A uses the G.711 codec and Phone B uses the G.729 codec, a transcoder is inserted if Phone B has one. However, the call is negotiated down to RTP to fulfill the codec requirement so the call is not secure.
Secure Transcoding for Remote Phones with DSP Farm Transcoding Configured
Transcoding is supported for remote phones that have the dspfarm-assist keyword of the codec command configured. A remote phone is a phone that is registered to a Cisco Unified CME and is residing on a remote location across the WAN. To save bandwidth across the WAN connection, calls to such a phone can be made to use the G.729r8 codec by configuring the codec g729r8 dspfarm assist command for the ephone. The g729r8 keyword forces calls to such a phone to use the G.729 codec. The dspfarm-assist keyword enables using available DSP resources if an H.323 call to the phone needs to be transcoded.
Note
Transcoding is enabled only if an H.323 call with a different codec from the remote phone tries to make a call to the remote phone. If a local phone on the same Cisco Unified CME as the remote phone makes a call to the remote phone, the local phone is forced to change its codec to G.729 instead of using transcoding.
Secure transcoding for point-to-point SRTP calls can only occur when both the SCCP phone that is to be serviced by Cisco Unified CME transcoding and its peer in the call are SRTP capable and have successfully negotiated the SRTP keys. Secure transcoding for point-to-point SRTP calls cannot occur when only one of the peers in the call is SRTP capable.
If Cisco Unified CME transcoding is to be performed on a secure call, the Media Encryption (SRTP) on Cisco Unified CME feature allows Cisco Unified CME to provide the DSP Farm with the encryption keys for the secure call as additional parameters so that Cisco Unified CME transcoding can be performed successfully. Without the encryption keys, the DSP Farm would not be able to read the encrypted voice data to transcode it.
Note
The secure transcoding described here does not apply to IP-IP gateway transcoding.
Cisco Unified CME transcoding is different from IP-to-IP gateway transcoding because it is invoked for an SCCP endpoint only, instead of for bridging VoIP call legs. Cisco Unified CME transcoding and IP-to-IP gateway transcoding are mutually exclusive, that is, only one type of transcoding can be invoked for a call. If no DSP Farm capable of SRTP transcoding is available, Cisco Unified CME secure transcoding is not performed and the call goes through using G.711.
For configuration information, see the "Registering the DSP Farm with Cisco Unified CME 4.2 or a Later Version in Secure Mode" section.
Secure Cisco Unified CME with Cisco Unity Express
Cisco Unity Express does not support secure signaling and media encryption. Secure Cisco Unified CME interoperates with Cisco Unity Express but calls between Cisco Unified CME and Cisco Unity Express are not secure.
In a typical Cisco Unity Express deployment with Cisco Unified CME in a secure H.323 network, Session Initiation Protocol (SIP) is used for signaling and the media path is G.711 with RTP. For Call Forward No Answer (CFNA) and Call Forward All (CFA), before the media path is established, signaling messages are sent to negotiate an RTP media path. If codec negotiation fails, a transcoder is inserted. The Media Encryption (SRTP) on Cisco Unified CME feature's H.323 service provider interface (SPI) supports fast start calls. In general, calls transferred or forwarded back to Cisco Unified CME from Cisco Unity Express fall into existing call flows and are treated as regular SIP and RTP calls.
The Media Encryption (SRTP) on Cisco Unified CME feature supports blind transfer back to Cisco Unified CME only. When midcall media renegotiation is configured, the secure capability for the endpoint is renegotiated regardless of which transfer mechanism, H.450.2 or Empty Capability Set (ECS), is used.
Secure Cisco Unified CME with Cisco Unity
The Media Encryption (SRTP) on Cisco Unified CME feature supports Cisco Unity 4.2 or a later version and Cisco Unity Connection 1.1 or a later version using SCCP. Secure Cisco Unity for Cisco Unified CME acts like a secure SCCP phone. Some provisioning is required before secure signaling can be established. Cisco Unity receives Cisco Unified CME device certificates from the Certificate Trust List (CTL) and Cisco Unity certificates are inserted into Cisco Unified CME manually. Cisco Unity with SIP is not supported.
The certificate for the Cisco Unity Connection is in the Cisco Unity administration web application under the "port group settings."
HTTPS Provisioning For Cisco Unified IP Phones
This section contains the following topics:
•
HTTPS support for an External Server
•
HTTPS Support in Cisco Unified CME
HTTPS support for an External Server
There is an increasing need to securely access web content on Cisco Unified IP phones using HTTPS. The X.509 certificate of a third-party web server must be stored in the IP phone's CTL file to authenticate the web server but the server command used to enter trustpoint information cannot be used to import the certificate to the CTL file. Because the server command requires the private key from the third-party web server for certificate chain validation and you cannot obtain that private key from the web server, the import certificate command is added to save the trusted certificate in the CTL file.
For information on how to import a trusted certificate to an IP phone's CTL file for HTTPS provisioning, see the "HTTPS Provisioning for Cisco Unified IP Phones" section.
For information on phone authentication support in Cisco Unified CME, see the "Phone Authentication Overview" section.
HTTPS Support in Cisco Unified CME
Cisco Unified IP phones use HTTP for some of the services offered by Cisco Unified CME. These services, which include local-directory lookup on Cisco Unified CME, My Phone Apps, and Extension Mobility, are invoked by pressing the "Services" button on the phones.
With Hypertext Transfer Protocol Secure (HTTPS) support in Cisco Unified CME 9.5 and later versions, these services can be invoked using an HTTPS connection from the phones to Cisco Unified CME.
Note
Ensure that the configured phone is provisioned for HTTPS-based services that run on Cisco Unified CME before configuring HTTPS globally or locally. Please refer to the appropriate phone administrator guide to know if your Cisco Unified IP phone supports HTTPS access. HTTP services continue to run for other phones that do not support HTTPS.
For information on provisioning Cisco Unified IP phones for secure access to web content using HTTPS, see the"HTTPS Provisioning for Cisco Unified IP Phones" section.
For configuration examples, see the "Configuring HTTPS Support for Cisco Unified CME: Example" section.
How to Configure Security
This section contains the following tasks:
Phone Authentication
•
Configuring the Cisco IOS Certification Authority (required)
•
Obtaining Certificates for Server Functions (required)
•
Configuring Telephony-Service Security Parameters (required)
•
Configuring the CTL Client (required)
•
Configuring the CAPF Server (required)
•
Configuring Ephone Security Parameters (required)
•
Configuring the CTL Provider (optional)
•
Configuring the Registration Authority (optional)
•
Entering the Authentication String on the Phone (optional)
•
Manually Importing the MIC Root Certificate (optional)
Media Encryption
•
Configuring Media Encryption (SRTP) in Cisco Unified CME (required)
•
Configuring Cisco Unified CME SRTP Fallback for H.323 Dial Peers (optional)
•
Configuring Cisco Unity for Secure Cisco Unified CME Operation (optional)
HTTPS Provisioning
•
HTTPS Provisioning for Cisco Unified IP Phones (optional)
Configuring the Cisco IOS Certification Authority
To configure a Cisco IOS Certification Authority (CA) on a local or external router, perform the following steps.
Tip
For more information, see Configuring and Managing a Cisco IOS Certificate Server for PKI Deployment.
Note
If you use a third-party CA, follow the provider's instructions instead of performing these steps.
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
ip http server
4.
crypto pki server label
5.
database level {minimal | names | complete}
6.
database url root-url
7.
lifetime certificate time
8.
issuer-name CN=label
9.
exit
10.
crypto pki trustpoint label
11.
enrollment url ca-url
12.
exit
13.
crypto pki server label
14.
grant auto
15.
no shutdown
16.
end
DETAILED STEPS
Step 1
enable
Example:Router> enable
Enables privileged EXEC mode.
•
Enter your password if prompted.
Step 2
configure terminal
Example:Router# configure terminal
Enters global configuration mode.
Step 3
ip http server
Example:Router(config)# ip http server
Enables the Cisco web-browser user interface on the local Cisco Unified CME router.
Step 4
crypto pki server label
Example:Router(config)# crypto pki server sanjose1
Defines a label for the Cisco IOS CA and enters certificate-server configuration mode.
Step 5
database level {minimal | names | complete}
Example:Router(config-cs-server)# database level complete
(Optional) Controls the type of data stored in the certificate enrollment database.
•
minimal—Enough information is stored only to continue issuing new certificates without conflict. This is the default value.
•
names—In addition to the minimal information given, the serial number and subject name of each certificate are also provided.
•
complete—In addition to the information given in the minimal and names levels, each issued certificate is written to the database. If you use this keyword, you must also specify an external TFTP server in which to store the data by using the database url command.
Step 6
database url root-url
Example:Router(config-cs-server)# database url nvram:
(Optional) Specifies the location, other than NVRAM, where all database entries for the certificate server are to be written out.
•
Required if you configured the complete keyword with the database level command in the previous step.
•
root-url—URL that is supported by the Cisco IOS file system and where database entries are to be written out. If the CA is going to issue a large number of certificates, select an appropriate storage location like flash or other storage device to store the certificates.
•
When the storage location chosen is flash and the file system type on this device is Class B (LEFS), make sure to check free space on the device periodically and use the squeeze command to free the space used up by deleted files. This process may take several minutes and should be done during scheduled maintenance periods or off-peak hours.
Step 7
lifetime certificate time
Example:Router(config-cs-server) lifetime certificate 888
(Optional) Specifies the lifetime, in days, of certificates issued by this Cisco IOS CA.
•
time—Number of days until a certificate expires. Range is 1 to 1825 days. Default is 365. The maximum certificate lifetime is 1 month less than the lifetime of the CA certificate.
•
Configure this command before the Cisco IOS CA is enabled by using the no shutdown command.
Step 8
issuer-name CN=label
Example:Router(config-cs-server)# issuer-name CN=sanjose1
(Optional) Specifies a distinguished name (DN) as issuer name for the Cisco IOS CA.
•
Default is already-configured label for the Cisco IOS CA. See Step 4.
Step 9
exit
Example:Router(config-cs-server)# exit
Exits certificate-server configuration mode.
Step 10
crypto pki trustpoint label
Example:Router(config)# crypto pki trustpoint sanjose1
(Optional) Declares a trustpoint and enters ca-trustpoint configuration mode.
•
For local CA only. This command is not required for Cisco IOS CA on an external router.
•
If you must use a specific RSA key for the Cisco IOS CA, use this command to create your own trustpoint by using the same label to be used with the crypto pki server command. If the router sees a configured trustpoint with the same label as the crypto pki server, it uses this trustpoint and does not automatically create a trustpoint.
Step 11
enrollment url ca-url
Example:Router(config-ca-trustpoint)# enrollment url http://ca-server.company.com
Specifies the enrollment URL of the issuing Cisco IOS CA.
•
For local Cisco IOS CA only. This command is not required for Cisco IOS CA on an external router.
•
ca-url—URL of the router on which the Cisco IOS CA is installed.
Step 12
exit
Example:Router(config-ca-trustpoint)# exit
Exits ca-trustpoint configuration mode.
Step 13
crypto pki server label
Example:Router(config)# crypto pki server sanjose1
Enters certificate-server configuration mode.
•
label—Name of the Cisco IOS CA being configured.
Step 14
grant auto
Example:Router(config-cs-server)# grant auto
(Optional) Allows certificates to be issued automatically to any requester.
•
Default and recommended method is manual enrollment.
•
Use this command only when testing and building simple networks. Use the no grant auto command after configuration is complete to prevent certificates from being automatically granted.
Step 15
no shutdown
Example:Router(config-cs-server)# no shutdown
(Optional) Enables the Cisco IOS CA.
•
Use this command only after you are finished configuring the Cisco IOS CA.
Step 16
end
Example:Router(config-cs-server)# end
Returns to privileged EXEC mode.
Examples
The following partial output from the show running-config command shows the configuration for a Cisco IOS CA named "sanjose1" running on the local Cisco Unified CME router:
ip http server
crypto pki server sanjose1
database level complete
database url nvram:
crypto pki trustpoint sanjose1
enrollment url http://ca-server.company.com
crypto pki server authority1
no grant auto
no shutdown
Obtaining Certificates for Server Functions
The CA issues certificates for the following server functions:
•
Cisco Unified CME—Requires a certificate for TLS sessions with phones.
•
TFTP—Requires a key pair and certificate for signing configuration files.
•
HTTPS—Requires a key pair and certificate for signing configuration files.
•
CAPF—Requires a certificate for TLS sessions with phones.
•
SAST—Required for signing the CTL file. We recommend creating two SAST certificates, one for primary use and one for backup.
To obtain a certificate for a server function, perform the following steps for each server function.
Note
You can configure a different trustpoint for each server function (see the "Examples" section) or you can configure the same trustpoint for more than one server function as shown in the "Configuration Examples for Security" section at the end of this module.
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
crypto pki trustpoint trustpoint-label
4.
enrollment url url
5.
revocation-check method1 [method2 [method3]]
6.
rsakeypair key-label [key-size [encryption-key-size]]
7.
exit
8.
crypto pki authenticate trustpoint-label
9.
crypto pki enroll trustpoint-label
10.
exit
DETAILED STEPS
Examples
The following partial output from the show running-config command show how to obtain certificates for a variety of server functions:
Obtaining a certificate for the CAPF server function
!configuring a trust point
crypto pki trustpoint capf-server
enrollment url http://192.168.1.1:80
revocation-check none
!authenticate w/ the CA and download its certificate
crypto pki authenticate capf-server
! enroll with the CA and obtain this trustpoint's certificate
crypto pki enroll capf-server
Obtaining a certificate for the Cisco Unified CME server function:
crypto pki trustpoint cme-server
enrollment url http://192.168.1.1:80
revocation-check none
crypto pki authenticate cme-server
crypto pki enroll cme-server
Obtaining a certificate for the TFTP server function:
crypto pki trustpoint tftp-server
enrollment url http://192.168.1.1:80
revocation-check none
crypto pki authenticate tftp-server
crypto pki enroll tftp-server
Obtaining a certificate for the first SAST server function (sast1):
crypto pki trustpoint sast1
enrollment url http://192.168.1.1:80
revocation-check none
crypto pki authenticate sast1
crypto pki enroll sast1
Obtaining a certificate for the second SAST server function (sast2):
crypto pki trustpoint sast2
enrollment url http://192.168.1.1:80
revocation-check none
crypto pki authenticate sast2
crypto pki enroll sast2
Configuring Telephony-Service Security Parameters
To configure security parameters for telephony service, perform the following steps.
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
telephony-service
4.
secure-signaling trustpoint label
5.
tftp-server-credentials trustpoint label
6.
device-security-mode {authenticated | none | encrypted}
7.
cnf-file perphone
8.
load-cfg-file file-url alias file-alias [sign] [create]
9.
server-security-mode {erase | non-secure | secure}
10.
end
DETAILED STEPS
Verifying Telephony-Service Security Parameters
Step 1
show telephony-service security-info
Use this command to display the security-related information that is configured in telephony-service configuration mode.
Router# show telephony-service security-info
Skinny Server Trustpoint for TLS: cme-sccp
TFTP Credentials Trustpoint: cme-tftp
Server Security Mode: Secure
Global Device Security Mode: Authenticated
Step 2
show running-config
Use this command to display the running configuration to verify telephony and per-phone security configuration.
Router# show running-config
telephony-service
secure-signaling trustpoint cme-sccp
server-security-mode secure
device-security-mode authenticated
tftp-server-credentials trustpoint cme-tftp
.
.
.
Configuring the CTL Client
Perform one of the following tasks, depending upon your network configuration:
•
Configuring the CTL Client on a Cisco Unified CME Router
•
Configuring the CTL Client on a Router That is Not a Cisco Unified CME Router
Configuring the CTL Client on a Cisco Unified CME Router
To configure a CTL client for creating a list of known, trusted certificates and tokens on a local Cisco Unified CME router, perform the following steps.
Note
If you have primary and secondary Cisco Unified CME routers, you can configure the CTL client on either one of them.
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
ctl-client
4.
sast1 trustpoint label
5.
sast2 trustpoint label
6.
server {capf | cme | cme-tftp | tftp} ip-address trustpoint trustpoint-label
7.
server cme ip-address username name-string password {0 | 1} password-string
8.
regenerate
9.
end
DETAILED STEPS
Examples
The following sample output from the show ctl-client command displays the trustpoints in the system:
Router# show ctl-client
CTL Client Information
-----------------------------
SAST 1 Certificate Trustpoint: cmeserverSAST 1 Certificate Trustpoint: sast2List of Trusted Servers in the CTLCME 10.1.1.1 cmeserverTFTP 10.1.1.1 cmeserverCAPF 10.1.1.1 cmeserverWhat to do Next
You are finished configuring the CTL client. See the "Configuring the CAPF Server" section.
Configuring the CTL Client on a Router That is Not a Cisco Unified CME Router
To configure a CTL client on a stand-alone router that is not a Cisco Unified CME router, perform the following steps.
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
ctl-client
4.
sast1 trustpoint label
5.
sast2 trustpoint label
6.
server cme ip-address username name-string password {0 | 1} password-string
7.
regenerate
8.
end
DETAILED STEPS
Examples
The following sample output from the show ctl-client command displays the trustpoints in the system:
Router# show ctl-client
CTL Client Information
-----------------------------
SAST 1 Certificate Trustpoint: cmeserverSAST 1 Certificate Trustpoint: sast2List of Trusted Servers in the CTLCME 10.1.1.1 cmeserverTFTP 10.1.1.1 cmeserverCAPF 10.1.1.1 cmeserverConfiguring the CAPF Server
A certificate must be obtained for the CAPF server so that it can establish a TLS session with the phone during certificate operation. The CAPF server can install, fetch, or delete locally significant certificates (LSCs) on security-enabled phones. To enable the CAPF server on the Cisco Unified CME router, perform the following steps.
Tip
When you use the CAPF server to install phone certificates, arrange to do so during a scheduled period of maintenance. Generating many certificates at the same time may cause call-processing interruptions.
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
capf-server
4.
trustpoint-label label
5.
cert-enroll-trustpoint label password {0 | 1} password-string
6.
source-addr ip-address
7.
auth-mode {auth-string | LSC | MIC | none | null-string}
8.
auth-string {delete | generate} {all | ephone-tag} [digit-string]
9.
phone-key-size {512 | 1024 | 2048}
10.
port tcp-port
11.
keygen-retry number
12.
keygen-timeout minutes
13.
cert-oper {delete all | fetch all | upgrade all}
14.
end
DETAILED STEPS
Verifying the CAPF Server
Use the show capf-server summary command to display CAPF-server configuration information.
Router# show capf-server summaryCAPF Server Configuration DetailsTrustpoint for TLS With Phone: tp1Trustpoint for CA operation: ra1Source Address: 10.10.10.1Listening Port: 3804Phone Key Size: 1024Phone KeyGen Retries: 3Phone KeyGen Timeout: 30 minutes
Configuring Ephone Security Parameters
To configure security parameters for individual phones, perform the following steps for each phone.
Prerequisites
•
Phones to be configured for security must be configured for basic calling in Cisco Unified CME. For configuration information, see the "Configuring Phones to Make Basic Calls" section.
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
ephone phone-tag
4.
device-security-mode {authenticated | none | encrypted}
5.
codec {g711ulaw | g722r64 | g729r8 [dspfarm-assist]}
6.
capf-auth-str digit-string
7.
cert-oper {delete | fetch | upgrade} auth-mode {auth-string | LSC | MIC | null-string}
8.
reset
9.
end
DETAILED STEPS
Step 1
enable
Example:Router> enable
Enables privileged EXEC mode.
•
Enter your password if prompted.
Step 2
configure terminal
Example:Router# configure terminal
Enters global configuration mode.
Step 3
ephone phone-tag
Example:Router(config)# ephone 24
Enters ephone configuration mode.
•
phone-tag—Unique identifier of phone to be configured.
Step 4
device-security-mode {authenticated | none | encrypted}
Example:Router(config-ephone)# device-security-mode authenticated
(Optional) Enables security mode for an individual SCCP IP phone.
•
authenticated—Instructs device to establish a TLS connection with no encryption. There is no Secure Real-Time Transport Protocol (SRTP) in the media path.
•
none—SCCP signaling is not secure. This is the default.
•
encrypted—Instructs device to establish an encrypted TLS connection to secure media path using SRTP.
•
This command can also be configured in telephony-service configuration mode. The value set in ephone configuration mode has priority over the value set in telephony-service configuration mode.
Step 5
codec {g711ulaw | g722r64 | g729r8 [dspfarm-assist]}
Example:Router(config-ephone)# codec g711ulaw dspfarm-assist
(Optional) Sets the security mode for SCCP signaling for a phone communicating with the Cisco Unified CME router.
•
dspfarm-assist—Required for secure transcoding with Cisco Unified CME. Causes the system to attempt to use DSP Farm resources for transcoding the segment between the phone and the Cisco Unified CME router if G.711 is negotiated for the call. This keyword is ignored if the SCCP endpoint type is ATA, VG224, or VG248.
Step 6
capf-auth-str digit-string
Example:Router(config-ephone)# capf-auth-str 2734
(Optional) Defines a string to use as a personal identification number (PIN) for CAPF authentication.
Note
For instructions on how to enter the string on a phone, see the "Entering the Authentication String on the Phone" section.
•
digit-string—Digits that the phone user must dial for CAPF authentication. The length of string is 4 to 10 digits.
•
This command can also be configured in telephony-service configuration mode. The value set in ephone configuration mode has priority over the value set in telephony-service configuration mode.
•
You can also define a PIN for CAPF authentication by using the auth-string command in CAPF-server configuration mode.
Step 7
cert-oper {delete | fetch | upgrade} auth-mode {auth-string | LSC | MIC | null-string}
Example:Router(config-ephone)# cert-oper upgrade auth-mode auth-string
(Optional) Initiates the indicated certificate operation on the ephone being configured.
•
delete—Removes the phone certificate.
•
fetch—Retrieves the phone certificate for troubleshooting.
•
upgrade—Upgrades the phone certificate.
•
auth-mode—Type of authentication to use during CAPF sessions to verify endpoints that request certificates.
•
auth-string—Authentication string to be entered on the phone by the phone user. Use the capf-auth-str command to configure the auth-string. For configuration information, see the "Entering the Authentication String on the Phone" section.
•
LSC—Phone provides its phone certificate for authentication. Precedence is given to an LSC if one exists.
•
MIC—Phone provides its phone certificate for authentication. Precedence is given to an MIC if one exists. MIC's issuer certificate must be imported into a PKI trustpoint. For information, see the "Manually Importing the MIC Root Certificate" section.
•
null-string—No authentication.
•
This command can also be configured in CAPF-server configuration mode to initiate certificate operations at a global level. This command in ephone configuration mode has priority over this command in CAPF-server configuration mode.
•
You can also use the auth-mode command in CAPF-server configuration mode to configure authentication at a global level.
Step 8
reset
Example:Router(config-ephone)# reset
Performs a complete reboot of the phone.
Step 9
end
Example:Router(config-ephone)# end
Returns to privileged EXEC mode.
Verifying Ephone Security Parameters
Use the show capf-server auth-string command to display configured authentication strings (PINs) that users enter at the phone to establish CAPF authentication.
Router# show capf-server auth-string
Authentication Strings for configured Ephones
Mac-Addr Auth-String
-------- -----------
000CCE3A817C 2734
001121116BDD 922
000D299D50DF 9182
000ED7B10DAC 3114
000F90485077 3328
0013C352E7F1 0678
What to Do Next
•
When you have more than one Cisco Unified CME router in your network, you must configure a CTL provider on each Cisco Unified CME router that is not running the CTL client. To configure a CTL provider on each Cisco Unified CME router on which the CTL client is not running, see the "Configuring the CTL Provider" section.
•
If the CA is a third-party CA or if the Cisco IOS CA is on a Cisco IOS router external to the Cisco Unified CME router, you must configure an RA to issue certificates to phones. For information, see the "Configuring the Registration Authority" section
•
If the specified authentication mode for the CAPF session is authentication-string, you must enter an authentication string on each phone that is receiving an updated LSC. For information, see the "Entering the Authentication String on the Phone" section.
•
If the specified authentication mode for the CAPF session is MIC, the MIC's issuer certificate must be imported into a PKI trustpoint. For information, see the "Manually Importing the MIC Root Certificate" section.
•
To configure Media Encryption, see the "Configuring Media Encryption (SRTP) in Cisco Unified CME" section.
Configuring the CTL Provider
When you have more than one Cisco Unified CME router in your network, you must configure a CTL provider on each Cisco Unified CME router that is not running the CTL client. To configure a CTL provider on each Cisco Unified CME router on which the CTL client is not running, perform the following steps.
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
credentials
4.
ip source-address ip-address port port-number
5.
trustpoint trustpoint-label
6.
ctl-service admin username secret {0 | 1} password-string
7.
end
DETAILED STEPS
Verifying the CTL Provider
Use the show credentials command to display credentials settings.
Router# show credentials
Credentials IP: 172.19.245.1
Credentials PORT: 2444
Trustpoint: ctlpv
What to Do Next
•
If the CA is a third-party CA or if the Cisco IOS CA is on a Cisco IOS router external to the Cisco Unified CME router, you must configure an RA to issue certificates to phones. For information, see the "Configuring the Registration Authority" section
•
If the specified authentication mode for the CAPF session is authentication-string, you must enter an authentication string on each phone that is receiving an updated LSC. For information, see the "Entering the Authentication String on the Phone" section.
•
If the specified authentication mode for the CAPF session is MIC, the MIC's issuer certificate must be imported into a PKI trustpoint. For information, see the "Manually Importing the MIC Root Certificate" section.
•
To configure Media Encryption, see the "Configuring Media Encryption (SRTP) in Cisco Unified CME" section.
Configuring the Registration Authority
A registration authority (RA) is the authority charged with recording or verifying some or all of the data required for the CA to issue certificates. In many cases the CA undertakes all of the RA functions itself, but where a CA operates over a wide geographical area or when there is security concern over exposing the CA at the edge of the network, it may be advisable to delegate some of the tasks to an RA and let the CA concentrate on its primary tasks of signing certificates.
You can configure a CA to run in RA mode. When the RA receives a manual or Simple Certificate Enrollment Protocol (SCEP) enrollment request, the administrator can either reject or grant it on the basis of local policy. If the request is granted, it is forwarded to the issuing CA, and the CA automatically generates the certificate and returns it to the RA. The client can later retrieve the granted certificate from the RA.
To configure an RA, perform the following steps on the Cisco Unified CME router.
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
crypto pki trustpoint label
4.
enrollment url ca-url
5.
revocation-check method1 [method2 [method3]]
6.
serial-number [none]
7.
rsakeypair key-label [key-size [encryption-key-size]]
8.
exit
9.
crypto pki server label
10.
mode ra
11.
lifetime certificate time
12.
grant auto
13.
no shutdown
14.
end
DETAILED STEPS
Step 1
enable
Example:Router> enable
Enables privileged EXEC mode.
•
Enter your password if prompted.
Step 2
configure terminal
Example:Router# configure terminal
Enters global configuration mode.
Step 3
crypto pki trustpoint label
Example:Router(config)# crypto pki trustpoint ra12
Declares the trustpoint that your RA mode certificate server should use and enters CA-trustpoint configuration mode.
•
label—Name for the trustpoint and RA.
TipThis label is also required for the cert-enroll-trustpoint command when you set up the CA proxy. See the "Configuring the CAPF Server" section.
Step 4
enrollment url ca-url
Example:Router(config-ca-trustpoint)# enrollment url http://ca-server.company.com
Specifies the enrollment URL of the issuing CA (root CA).
•
ca-url—URL of the router on which the root CA has been installed.
Step 5
revocation-check method1 [method2 [method3]]
Example:Router(config-ca-trustpoint)# revocation-check none
(Optional) Checks the revocation status of a certificate and specifies one or more methods to check the status. If a second and third method are specified, each method is used only if the previous method returns an error, such as a server being down.
Valid values for methodn are as follows:
•
crl—Certificate checking is performed by a certificate revocation list (CRL). This is the default behavior.
•
none—Certificate checking is not required.
•
ocsp—Certificate checking is performed by an Online Certificate Status Protocol (OCSP) server.
Step 6
serial-number [none]
Example:Router(config-ca-trustpoint)# serial-number
(Optional) Specifies whether the router serial number should be included in the certificate request. When this command is not used, you are prompted for the serial number during certificate enrollment.
•
none—(Optional) A serial number is not included in the certificate request.
Step 7
rsakeypair key-label [key-size [encryption-key-size]]
Example:Router(config-ca-trustpoint)# rsakeypair exampleCAkeys 1024 1024
(Optional) Specifies an RSA key pair to use with a certificate.
•
key-label—Name of the key pair, which is generated during enrollment if it does not already exist or if the auto-enroll regenerate command is used.
•
key-size—(Optional) Size of the desired RSA key. If not specified, the existing key size is used.
•
encryption-key-size—(Optional) Size of the second key, which is used to request separate encryption, signature keys, and certificates.
•
Multiple trustpoints can share the same key.
Step 8
exit
Example:Router(config-ca-trustpoint)# exit
Exits ca-trustpoint configuration mode.
Step 9
crypto pki server label
Example:Router(config)# crypto pki server ra12
Defines a label for the certificate server and enters certificate-server configuration mode.
•
label—Name for the trustpoint and RA. Use the same label that you previously created as a trustpoint and RA in Step 3.
Step 10
mode ra
Example:Router(config-cs-server)# mode ra
Places the PKI server into certificate-server mode for the RA.
Step 11
lifetime certificate time
Example:Router(config-cs-server)# lifetime certificate 1800
(Optional) Specifies the lifetime, in days, of a certificate.
•
time—Number of days until the certificate expires. Range is 1 to 1825. Default is 365. The maximum certificate lifetime is 1 month less than the lifetime of the CA certificate.
•
This command must be used before the server is enabled with the no shutdown command.
Step 12
grant auto
Example:Router(config-cs-server)# grant auto
Allows a certificate to be issued automatically to any requester.
•
Configure this command only during enrollment when testing and building simple networks.
•
As a security best practice, use the no grant auto command to disable this functionality after configuration so that certificates are not continually granted.
Step 13
no shutdown
Example:Router(config-cs-server)# no shutdown
(Optional) Enables the certificate server.
•
When prompted, provide input regarding acceptance of the CA certificate, the router certificate, the challenge password, and a password for protecting the private key.
•
Use this command only after you have completely configured your certificate server.
Step 14
end
Example:Router(config-cs-server)# end
Returns to privileged EXEC mode.
What to Do Next
•
When you have more than one Cisco Unified CME router in your network, you must configure a CTL provider on each Cisco Unified CME router that is not running the CTL client. To configure a CTL provider on each Cisco Unified CME router on which the CTL client is not running, see the "Configuring the CTL Provider" section.
•
If the specified authentication mode for the CAPF session is authentication-string, you must enter an authentication string on each phone that is receiving an updated LSC. For information, see the "Entering the Authentication String on the Phone" section.
•
If the specified authentication mode for the CAPF session is MIC, the MIC's issuer certificate must be imported into a PKI trustpoint. For information, see the "Manually Importing the MIC Root Certificate" section.
•
To configure Media Encryption, see the "Configuring Media Encryption (SRTP) in Cisco Unified CME" section.
Entering the Authentication String on the Phone
This procedure is required only for the one-time installation of an LSC on a phone and only if you configured the authentication mode for the CAPF session as authentication-string. The authentication string must be communicated to the phone user so that it can be entered on the phone before the LSC is installed.
To install the certificate, perform the following steps.
Note
You can list authentication strings for phones by using the show capf-server auth-string command.
Prerequisites
•
Signed image exists on the IP phone; see the Cisco Unified IP phone administration documentation that supports your phone model.
•
IP phone is registered in Cisco Unified CME.
•
CAPF certificate exists in the CTL file. For information, see the "Configuring the CTL Client" section.
•
Authentication string to be entered is configured using auth-string command in CAPF-server configuration mode or the capf-auth-str command in ephone configuration mode. For information, see the "Configuring Telephony-Service Security Parameters" section.
•
The device-security-mode command is configured using the none keyword. For information, see the "Configuring Telephony-Service Security Parameters" section.
Restrictions
•
Authentication string applies for one-time use only.
DETAILED STEPS
Step 1
Press the Settings button. On the Cisco Unified IP Phone 7921, press Down Arrow to access the Settings menu.
Step 2
If the configuration is locked, press **# (asterisk, asterisk, pound sign) to unlock it.
Step 3
Scroll down the Settings menu. Highlight Security Configuration and press the Select soft key.
Step 4
Scroll down the Security Configuration menu. Highlight LSC and press the Update soft key. On the Cisco Unified IP Phone 7921, press **# to unlock the Security Configuration menu.
Step 5
When prompted for the authentication string, enter the string provided by the system administrator and press the Submit soft key.
The phone installs, updates, deletes, or fetches the certificate, depending on the CAPF configuration.
You can monitor the progress of the certificate operation by viewing the messages that display on the phone. After you press Submit, the message "Pending" appears under the LSC option. The phone generates the public and private key pair and displays the information on the phone. When the phone successfully completes the process, the phone displays a successful message. If the phone displays a failure message, you entered the wrong authentication string or did not enable the phone for upgrade.
You can stop the process by choosing Stop at any time.
Step 6
Verify that the certificate was installed on the phone. From the Settings menu on the phone screen, choose Model Information and then press the Select soft key to display the Model Information.
Step 7
Press the navigation button to scroll to LSC. The value for this item indicates whether LSC is Installed or Not Installed.
What to Do Next
•
When you have more than one Cisco Unified CME router in your network, you must configure a CTL provider on each Cisco Unified CME router that is not running the CTL client. To configure a CTL provider on each Cisco Unified CME router on which the CTL client is not running, see the "Configuring the CTL Provider" section.
•
If the CA is a third-party CA or if the Cisco IOS CA is on a Cisco IOS router external to the Cisco Unified CME router, you must configure an RA to issue certificates to phones. For information, see the "Configuring the Registration Authority" section
•
If the specified authentication mode for the CAPF session is MIC, the MIC's issuer certificate must be imported into a PKI trustpoint. For information, see the "Manually Importing the MIC Root Certificate" section.
•
To configure Media Encryption, see the "Configuring Media Encryption (SRTP) in Cisco Unified CME" section.
Manually Importing the MIC Root Certificate
The MIC root certificate must be present in the Cisco Unified CME router to allow Cisco Unified CME to authenticate the MIC that is presented to it. To manually import the MIC root certificate on the Cisco Unified CME router, perform the following steps for each type of phone that requires a MIC for authentication.
Prerequisites
One of the following must be true before you perform this task:
•
The device-security-mode command is configured using the none keyword. For information, see the "Configuring Telephony-Service Security Parameters" section.
•
MIC is the specified authentication mode for phone authentication during a CAPF session.
•
A phone's MIC, rather than an LSC, is used to establish the TLS session for SCCP signaling.
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
crypto pki trustpoint name
4.
revocation-check none
5.
enrollment terminal
6.
exit
7.
crypto pki authenticate name
8.
Download the four MIC root files. Cut and paste the appropriate text for the certificate. Accept the certificates.
9.
exit
DETAILED STEPS
What to Do Next
•
When you have more than one Cisco Unified CME router in your network, you must configure a CTL provider on each Cisco Unified CME router that is not running the CTL client. To configure a CTL provider on each Cisco Unified CME router on which the CTL client is not running, see the "Configuring the CTL Provider" section.
•
If the CA is a third-party CA or if the Cisco IOS CA is on a Cisco IOS router external to the Cisco Unified CME router, you must configure an RA to issue certificates to phones. For information, see the "Configuring the Registration Authority" section
•
If the specified authentication mode for the CAPF session is authentication-string, you must enter an authentication string on each phone that is receiving an updated LSC. For information, see the "Entering the Authentication String on the Phone" section.
•
To configure Media Encryption, see the "Configuring Media Encryption (SRTP) in Cisco Unified CME" section.
Configuring Media Encryption (SRTP) in Cisco Unified CME
To configure the network for secure calls between Cisco Unified CME systems across an H.323 trunk, perform the following steps on the Cisco Unified CME router.
Prerequisites
•
Cisco Unified CME 4.2 or a later version.
•
To make secure H.323 calls, telephony-service security parameters must be configured. See the "Configuring Telephony-Service Security Parameters" section.
•
Compatible Cisco IOS Release on the Cisco VG224 Analog Phone Gateway. For information, see Cisco Unified CME and Cisco IOS Release Compatibility Matrix.
Restrictions
•
Secure three-way software conferencing is not supported. A secure call beginning with SRTP always falls back to nonsecure Real-Time Transport Protocol (RTP) when it is joined to a conference.
•
If a party drops from a three-party conference, the call between the remaining two parties returns to secure if the two parties are SRTP-capable local Skinny Client Control Protocol (SCCP) endpoints to a single Cisco Unified CME and the conference creator is one of the remaining parties. If either of the two remaining parties are only RTP-capable, the call remains nonsecure. If the two remaining parties are connected through FXS, PSTN, or VoIP, the call remains nonsecure.
•
Calls to Cisco Unity Express are not secure.
•
Music on Hold (MOH) is not secure.
•
Video calls are not secure.
•
Modem relay and T.3 fax relay calls are not secure.
•
Media flow-around is not supported for call transfer and call forward.
•
Conversion between inband tone and RFC 2833 DTMF is not supported. RFC 2833 DTMF handling is supported when encryption keys are sent to secure DSP Farm devices but is not supported for codec passthrough.
•
Secure Cisco Unified CME does not support SIP trunks; only H.323 trunks are supported.
•
Media Encryption (SRTP) supports secure supplementary services in both H.450 and non-H.450 Cisco Unified CME networks. A secure Cisco Unified CME network should be either H.450 or non-H.450, not a hybrid.
•
Secure calls are supported in the default session application only.
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
voice service voip
4.
supplementary-service media-renegotiate
5.
srtp fallback
6.
h323
7.
emptycapability
8.
exit
DETAILED STEPS
What to Do Next
You have completed the required task for configuring Media Encryption (SRTP) on Cisco Unified CME. You can now perform the following optional tasks:
•
Configuring Cisco Unified CME SRTP Fallback for H.323 Dial Peers (optional)
•
Configuring Cisco Unity for Secure Cisco Unified CME Operation (optional)
Configuring Cisco Unified CME SRTP Fallback for H.323 Dial Peers
To configure SRTP fallback for an individual dial peer, perform the following steps on the Cisco Unified CME router.
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
voice class codec tag
4.
codec preference value codec-type
5.
exit
6.
dial-peer voice tag voip
7.
srtp fallback
8.
voice-class codec tag
9.
exit
DETAILED STEPS
Configuring Cisco Unity for Secure Cisco Unified CME Operation
This section contains the following tasks:
•
Configuring Integration Between Cisco Unified CME and Cisco Unity
•
Importing the Cisco Unity Root Certificate to Cisco Unified CME
•
Configuring Cisco Unity Ports for Secure Registration
•
Verifying that Cisco Unity are Registering Securely
Prerequisites
•
Cisco Unity 4.2 or later version.
Configuring Integration Between Cisco Unified CME and Cisco Unity
To change the settings for the integration between Cisco Unified CME and Cisco Unity, perform the following steps on the Cisco Unity server:
Step 1
If Cisco Unity Telephony Integration Manager (UTIM) is not yet open on the Cisco Unity server, choose Programs > Cisco Unity > Manage Integrations from the Windows Start menu. The UTIM window appears.
Step 2
In the left pane, double-click Cisco Unity Server. The existing integrations appear.
Step 3
Click Cisco Unified Communications Manager integration.
Step 4
In the right pane, click the cluster for the integration.
Step 5
Click the Servers tab.
Step 6
In the Cisco Unified Communications Manager Cluster Security Mode field, click the applicable setting.
Step 7
If you clicked Non-secure, click Save and skip the remaining steps in this procedure.
If you clicked Authenticated or Encrypted, the Security tab and the Add TFTP Server dialog box appear. In the IP Address or Host Name field of the Add TFTP Server dialog box, enter the IP address (or DNS name) of the primary TFTP server for the Cisco Unified Communications Manager cluster and click OK.
Step 8
If there are more TFTP servers that Cisco Unity will use to download the Cisco Unified Communications Manager certificates, click Add. The Add TFTP Server dialog box appears.
Step 9
In the IP Address or Host Name field, enter the IP address (or DNS name) of the secondary TFTP server for the Cisco Unified Communications Manager cluster and click OK.
Step 10
Click Save.
Cisco Unity creates the voice messaging port device certificates, exports the Cisco Unity server root certificate, and displays the Export Cisco Unity Root Certificate dialog box.
Step 11
Note the filename of the exported Cisco Unity server root certificate and click OK.
Step 12
On the Cisco Unity server, navigate to the CommServer\SkinnyCerts directory.
Step 13
Locate the Cisco Unity server root certificate file that you exported in Step 11.
Step 14
Right-click the file and click Rename.
Step 15
Change the file extension from .0 to .pem. For example, change the filename "12345.0" to "12345.pem" for the exported Cisco Unity server root certificate file.
Step 16
Copy this file to a PC from which you can access the Cisco Unified CME router.
Importing the Cisco Unity Root Certificate to Cisco Unified CME
To import the Cisco Unity root certificate to Cisco Unified CME, perform the following steps on the Cisco Unified CME router:
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
crypto pki trustpoint name
4.
revocation-check none
5.
enrollment terminal
6.
exit
7.
crypto pki authenticate trustpoint-label
8.
Open the root certificate file that you copied from the Cisco Unity Server in Step 16.
9.
You will be prompted to enter the CA certificate. Cut and paste the entire contents of the base 64 encoded certificate between "BEGIN CERTIFICATE" and "END CERTIFICATE" at the command line. Press Enter and type "quit." The router prompts you to accept the certificate. Enter "yes" to accept the certificate.
DETAILED STEPS
Step 1
enable
Example:Router> enable
Enables privileged EXEC mode.
•
Enter your password if prompted.
Step 2
configure terminal
Example:Router# configure terminal
Enters global configuration mode.
Step 3
crypto pki trustpoint name
Example:Router(config)# crypto pki trustpoint PEM
Declares the trustpoint that your RA mode certificate server should use and enters ca-trustpoint configuration mode.
•
label—Name for the trustpoint and RA.
Step 4
revocation-check none
Example:Router(ca-trustpoint)# revocation-check none
(Optional) Specifies that certificate checking is not required.
Step 5
enrollment terminal
Example:Router(ca-trustpoint)# enrollment terminal
Specifies manual cut-and-paste certificate enrollment.
Step 6
exit
Example:Router(ca-trustpoint)# exit
Exits ca-trustpoint configuration mode.
Step 7
crypto pki authenticate trustpoint-label
Example:Router(config)# crypto pki authenticate pem
Retrieves the CA certificate and authenticates it. Checks the certificate fingerprint when prompted.
•
trustpoint-label—Already-configured name for the trustpoint and RA. See Step 3.
Step 8
Open the root certificate file that you copied from the Cisco Unity Server in Step 16.
Step 9
You will be prompted to enter the CA certificate. Cut and paste the entire contents of the base 64 encoded certificate between "BEGIN CERTIFICATE" and "END CERTIFICATE" at the command line. Press Enter and type "quit." The router prompts you to accept the certificate. Enter "yes" to accept the certificate.
Completes the copying of the Cisco Unity root certificate to the Cisco Unified CME router.
Configuring Cisco Unity Ports for Secure Registration
To configure Cisco Unity ports for registration in secure mode, perform the following steps:
Step 1
Choose the Cisco voice-mail port that you want to update.
Step 2
From the Device Security Mode drop-down list, choose Encrypted.
Step 3
Click Update.
Verifying that Cisco Unity are Registering Securely
Use the show sccp connections command to verify that Cisco Unity ports are registered securely with Cisco Unified CME.
show sccp connection: Example
In the following example, the secure value of the type field shows that the connections are secure.
Router# show sccp connections
sess_id conn_id stype mode codec ripaddr rport sport
16777222 16777409 secure-xcode sendrecv g729b 10.3.56.120 16772 19534
16777222 16777393 secure-xcode sendrecv g711u 10.3.56.50 17030 18464
Total number of active session(s) 1, and connection(s) 2
HTTPS Provisioning for Cisco Unified IP Phones
To provision a Cisco Unified IP phone for secure access to web content using HTTPS, perform the following steps:
Prerequisites
•
Firmware 9.0 (4) or a later version must be installed on the IP phone to prevent an infinite registration loop.
•
Certificate file to be imported from flash memory to the IP phone must be in privacy-enhanced mail format.
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
ip http server
4.
crypto pki server cs-label
5.
database level {minimum | names | complete}
6.
database url root url
7.
grant auto
8.
exit
9.
crypto pki trustpoint name
10.
enrollment url url
11.
exit
12.
crypto pki server cs-label
13.
no shutdown
14.
exit
15.
crypto pki trustpoint name
16.
enrollment url url
17.
revocation-check method1 [method2[method3]]
18.
rsakeypair key-label
19.
exit
20.
crypto pki authenticate name
21.
crypto pki enroll name
22.
crypto pki trustpoint name
23.
enrollment url url
24.
revocation-check method1 [method2[method3]]
25.
rsakeypair key-label
26.
exit
27.
crypto pki authenticate name
28.
crypto pki enroll name
29.
ctl-client
30.
sast1 trustpoint label
31.
sast2 trustpoint label
32.
import certificate tag description flash:cert_name
33.
server application server address trustpoint label
34.
regenerate
35.
end
DETAILED STEPS
Configuration Examples for Security
This section contains the following examples:
Phone Authentication
•
Manually Importing MIC Root Certificate on the Cisco Unified CME Router: Example
•
Telephony-Service Security Parameters: Example
•
CTL Client Running on Cisco Unified CME Router: Example
Media Encryption
•
Secure Cisco Unified CME: Example
Configuring HTTPS Support for Cisco Unified CME
•
Configuring HTTPS Support for Cisco Unified CME: Example
Cisco IOS CA: Example
crypto pki server iosca
grant auto
database url flash:
!
crypto pki trustpoint iosca
revocation-check none
rsakeypair iosca
!
crypto pki certificate chain iosca
certificate ca 01
308201F9 30820162 ...
Manually Importing MIC Root Certificate on the Cisco Unified CME Router: Example
The following example shows three certificates imported to the router (7970, 7960, PEM):
Router(config)# crypto pki trustpoint 7970
Router(ca-trustpoint)# revocation-check none
Router(ca-trustpoint)# enrollment terminal
Router(ca-trustpoint)# exit
Router(config)# crypto pki authenticate 7970
Enter the base 64 encoded CA certificate.
End with a blank line or the word "quit" on a line by itself
MIIDqDCCApCgAwIBAgIQNT+yS9cPFKNGwfOprHJWdTANBgkqhkiG9w0BAQUFADAu
MRYwFAYDVQQKEw1DaXNjbyBTeXN0ZW1zMRQwEgYDVQQDEwtDQVAtUlRQLTAwMjAe
Fw0wMzEwMTAyMDE4NDlaFw0yMzEwMTAyMDI3MzdaMC4xFjAUBgNVBAoTDUNpc2Nv
IFN5c3RlbXMxFDASBgNVBAMTC0NBUC1SVFAtMDAyMIIBIDANBgkqhkiG9w0BAQEF
AAOCAQ0AMIIBCAKCAQEAxCZlBK19w/2NZVVvpjCPrpW1cCY7V1q9lhzI85RZZdnQ
2M4CufgIzNa3zYxGJIAYeFfcRECnMB3f5A+x7xNiEuzE87UPvK+7S80uWCY0Uhtl
AVVf5NQgZ3YDNoNXg5MmONb8lT86F55EZyVac0XGne77TSIbIdejrTgYQXGP2MJx
Qhg+ZQlGFDRzbHfM84Duv2Msez+l+SqmqO80kIckqE9Nr3/XCSj1hXZNNVg8D+mv
Hth2P6KZqAKXAAStGRLSZX3jNbS8tveJ3Gi5+sj9+F6KKK2PD0iDwHcRKkcUHb7g
lI++U/5nswjUDIAph715Ds2rn9ehkMGipGLF8kpuCwIBA6OBwzCBwDALBgNVHQ8E
BAMCAYYwDwYDVR0TAQH/BAUwAwEB/zAdBgNVHQ4EFgQUUpIr4ojuLgmKTn5wLFal
mrTUm5YwbwYDVR0fBGgwZjBkoGKgYIYtaHR0cDovL2NhcC1ydHAtMDAyL0NlcnRF
bnJvbGwvQ0FQLVJUUC0wMDIuY3Jshi9maWxlOi8vXFxjYXAtcnRwLTAwMlxDZXJ0
RW5yb2xsXENBUC1SVFAtMDAyLmNybDAQBgkrBgEEAYI3FQEEAwIBADANBgkqhkiG
9w0BAQUFAAOCAQEAVoOM78TaOtHqj7sVL/5u5VChlyvU168f0piJLNWip2vDRihm
E+DlXdwMS5JaqUtuaSd/m/xzxpcRJm4ZRRwPq6VeaiiQGkjFuZEe5jSKiSAK7eHg
tup4HP/ZfKSwPA40DlsGSYsKNMm3OmVOCQUMH02lPkS/eEQ9sIw6QS7uuHN4y4CJ
NPnRbpFRLw06hnStCZHtGpKEHnY213QOy3h/EWhbnp0MZ+hdr20FujSI6G1+L39l
aRjeD708f2fYoz9wnEpZbtn2Kzse3uhU1Ygq1D1x9yuPq388C18HWdmCj4OVTXux
V6Y47H1yv/GJM8FvdgvKlExbGTFnlHpPiaG9tQ==
quit
Certificate has the following attributes:
Fingerprint MD5: F7E150EA 5E6E3AC5 615FC696 66415C9F
Fingerprint SHA1: 1BE2B503 DC72EE28 0C0F6B18 798236D8 D3B18BE6
% Do you accept this certificate? [yes/no]: y
Trustpoint CA certificate accepted.
% Certificate successfully imported
Router(config)# crypto pki trustpoint 7960
Router(ca-trustpoint)# revocation-check none
Router(ca-trustpoint)# enrollment terminal
Router(ca-trustpoint)# exit
Router(config)# crypto pki authenticate 7960
Enter the base 64 encoded CA certificate.
End with a blank line or the word "quit" on a line by itself
MIICKDCCAZGgAwIBAgIC8wEwDQYJKoZIhvcNAQEFBQAwQDELMAkGA1UEBhMCVVMx
GjAYBgNVBAoTEUNpc2NvIFN5c3RlbXMgSW5jMRUwEwYDVQQDEwxDQVBGLTdEN0Qw
QzAwHhcNMDQwNzE1MjIzODMyWhcNMTkwNzEyMjIzODMxWjBAMQswCQYDVQQGEwJV
UzEaMBgGA1UEChMRQ2lzY28gU3lzdGVtcyBJbmMxFTATBgNVBAMTDENBUEYtN0Q3
RDBDMDCBnzANBgkqhkiG9w0BAQEFAAOBjQAwgYkCgYEA0hvMOZZ9ENYWme11YGY1
it2rvE3Nk/eqhnv8P9eqB1iqt+fFBeAG0WZ5bO5FetdU+BCmPnddvAeSpsfr3Z+h
x+r58fOEIBRHQLgnDZ+nwYH39uwXcRWWqWwlW147YHjV7M5c/R8T6daCx4B5NBo6
kdQdQNOrV3IP7kQaCShdM/kCAwEAAaMxMC8wDgYDVR0PAQH/BAQDAgKEMB0GA1Ud
JQQWMBQGCCsGAQUFBwMBBggrBgEFBQcDBTANBgkqhkiG9w0BAQUFAAOBgQCaNi6x
sL6M5NlDezpSBO3QmUVyXMfrONV2ysrSwcXzHu0gJ9MSJ8TwiQmVaJ47hSTlF5a8
YVYJ0IdifXbXRo+/EEO7kkmFE8MZta5rM7UWj8bAeR42iqA3RzQaDwuJgNWT9Fhh
GgfuNAlo5h1AikxsvxivmDlLdZyCMoqJJd7B2Q==
quit
Certificate has the following attributes:
Fingerprint MD5: 4B9636DF 0F3BA6B7 5F54BE72 24762DBC
Fingerprint SHA1: A9917775 F86BB37A 5C130ED2 3E528BB8 286E8C2D
% Do you accept this certificate? [yes/no]: y
Trustpoint CA certificate accepted.
% Certificate successfully imported
Router(config)# crypto pki trustpoint PEM
Router(ca-trustpoint)# revocation-check none
Router(ca-trustpoint)# enrollment terminal
Router(ca-trustpoint)# exit
Router(config)# crypto pki authenticate PEM
Enter the base 64 encoded CA certificate.
End with a blank line or the word "quit" on a line by itself
MIIDqDCCApCgAwIBAgIQdhL5YBU9b59OQiAgMrcjVjANBgkqhkiG9w0BAQUFADAu
MRYwFAYDVQQKEw1DaXNjbyBTeXN0ZW1zMRQwEgYDVQQDEwtDQVAtUlRQLTAwMTAe
Fw0wMzAyMDYyMzI3MTNaFw0yMzAyMDYyMzM2MzRaMC4xFjAUBgNVBAoTDUNpc2Nv
IFN5c3RlbXMxFDASBgNVBAMTC0NBUC1SVFAtMDAxMIIBIDANBgkqhkiG9w0BAQEF
AAOCAQ0AMIIBCAKCAQEArFW77Rjem4cJ/7yPLVCauDohwZZ/3qf0sJaWlLeAzBlq
Rj2lFlSij0ddkDtfEEo9VKmBOJsvx6xJlWJiuBwUMDhTRbsuJz+npkaGBXPOXJmN
Vd54qlpc/hQDfWlbrIFkCcYhHws7vwnPsLuy1Kw2L2cP0UXxYghSsx8H4vGqdPFQ
NnYy7aKJ43SvDFt4zn37n8jrvlRuz0x3mdbcBEdHbA825Yo7a8sk12tshMJ/YdMm
vny0pmDNZXmeHjqEgVO3UFUn6GVCO+K1y1dUU1qpYJNYtqLkqj7wgccGjsHdHr3a
U+bw1uLgSGsQnxMWeMaWo8+6hMxwlANPweufgZMaywIBA6OBwzCBwDALBgNVHQ8E
BAMCAYYwDwYDVR0TAQH/BAUwAwEB/zAdBgNVHQ4EFgQU6Rexgscfz6ypG270qSac
cK4FoJowbwYDVR0fBGgwZjBkoGKgYIYtaHR0cDovL2NhcC1ydHAtMDAxL0NlcnRF
bnJvbGwvQ0FQLVJUUC0wMDEuY3Jshi9maWxlOi8vXFxjYXAtcnRwLTAwMVxDZXJ0
RW5yb2xsXENBUC1SVFAtMDAxLmNybDAQBgkrBgEEAYI3FQEEAwIBADANBgkqhkiG
9w0BAQUFAAOCAQEAq2T96/YMMtw2Dw4QX+F1+g1XSrUCrNyjx7vtFaRDHyB+kobw
dwkpohfkzfTyYpJELzV1r+kMRoyuZ7oIqqccEroMDnnmeApc+BRGbDJqS1Zzk4OA
c6Ea7fm53nQRlcSPmUVLjDBzKYDNbnEjizptaIC5fgB/S9S6C1q0YpTZFn5tjUjy
WXzeYSXPrcxb0UH7IQJ1ogpONAAUKLoPaZU7tVDSH3hD4+VjmLyysaLUhksGFrrN
phzZrsVVilK17qpqCPllKLGAS4fSbkruq3r/6S/SpXS6/gAoljBKixP7ZW2PxgCU
1aU9cURLPO95NDOFN3jBk3Sips7cVidcogowPQ==
quit
Certificate has the following attributes:
Fingerprint MD5: 233C8E33 8632EA4E 76D79FEB FFB061C6
Fingerprint SHA1: F7B40B94 5831D2AB 447AB8F2 25990732 227631BE
% Do you accept this certificate? [yes/no]: y
Trustpoint CA certificate accepted.
% Certificate successfully imported
Use the show crypto pki trustpoint status command to show that enrollment has succeeded and that five CA certificates have been granted. The five certificates include the three certificates just entered, the CA server certificate, and the router certificate.
Router# show crypto pki trustpoint status
Trustpoint 7970:
Issuing CA certificate configured:
Subject Name:
cn=CAP-RTP-002,o=Cisco Systems
Fingerprint MD5: F7E150EA 5E6E3AC5 615FC696 66415C9F
Fingerprint SHA1: 1BE2B503 DC72EE28 0C0F6B18 798236D8 D3B18BE6
State:
Keys generated ............. Yes (General Purpose)
Issuing CA authenticated ....... Yes
Certificate request(s) ..... None
Trustpoint 7960:
Issuing CA certificate configured:
Subject Name:
cn=CAPF-508A3754,o=Cisco Systems Inc,c=US
Fingerprint MD5: 6BAE18C2 0BCE391E DAE2FE4C 5810F576
Fingerprint SHA1: B7735A2E 3A5C274F C311D7F1 3BE89942 355102DE
State:
Keys generated ............. Yes (General Purpose)
Issuing CA authenticated ....... Yes
Certificate request(s) ..... None
Trustpoint PEM:
Issuing CA certificate configured:
Subject Name:
cn=CAP-RTP-001,o=Cisco Systems
Fingerprint MD5: 233C8E33 8632EA4E 76D79FEB FFB061C6
Fingerprint SHA1: F7B40B94 5831D2AB 447AB8F2 25990732 227631BE
State:
Keys generated ............. Yes (General Purpose)
Issuing CA authenticated ....... Yes
Certificate request(s) ..... None
Trustpoint srstcaserver:
Issuing CA certificate configured:
Subject Name:
cn=srstcaserver
Fingerprint MD5: 6AF5B084 79C93F2B 76CC8FE6 8781AF5E
Fingerprint SHA1: 47D30503 38FF1524 711448B4 9763FAF6 3A8E7DCF
State:
Keys generated ............. Yes (General Purpose)
Issuing CA authenticated ....... Yes
Certificate request(s) ..... None
Trustpoint srstca:
Issuing CA certificate configured:
Subject Name:
cn=srstcaserver
Fingerprint MD5: 6AF5B084 79C93F2B 76CC8FE6 8781AF5E
Fingerprint SHA1: 47D30503 38FF1524 711448B4 9763FAF6 3A8E7DCF
Router General Purpose certificate configured:
Subject Name:
serialNumber=F3246544+hostname=c2611XM-sSRST.cisco.com
Fingerprint: 35471295 1C907EC1 45B347BC 7A9C4B86
State:
Keys generated ............. Yes (General Purpose)
Issuing CA authenticated ....... Yes
Certificate request(s) ..... Yes
Telephony-Service Security Parameters: Example
The following example shows Cisco Unified CME security parameters:
telephony-service
device-security-mode authenticated
secure-signaling trustpoint cme-sccp
tftp-server-credentials trustpoint cme-tftp
load-cfg-file slot0:Ringlist.xml alias Ringlist.xml sign create
ephone 24
device-security-mode authenticated
capf-auth-str 2734
cert-oper upgrade auth-mode auth-string
CTL Client Running on Cisco Unified CME Router: Example
ctl-clientserver capf 10.1.1.1 trustpoint cmeserverserver cme 10.1.1.1 trustpoint cmeserverserver tftp 10.1.1.1 trustpoint cmeserversast1 trustpoint cmeserversast2 trustpoint sast2CTL Client Running on Another Router: Examplectl-clientserver cme 10.1.1.100 trustpoint cmeserverserver cme 10.1.1.1 username cisco password 1 0822455D0A16544541sast1 trustpoint cmeserversast2 trustpoint sast1CAPF Server: Example!ip dhcp pool cme-poolnetwork 10.1.1.0 255.255.255.0option 150 ip 10.1.1.1default-router 10.1.1.1!capf-serverport 3804auth-mode null-stringcert-enroll-trustpoint iosra password 1 00071A1507545A545Ctrustpoint-label cmeserversource-addr 10.1.1.1!crypto pki server iosragrant automode radatabase url slot0:!crypto pki trustpoint cmeserverenrollment url http://10.1.1.100:80serial-numberrevocation-check nonersakeypair cmeserver!crypto pki trustpoint sast2enrollment url http://10.1.1.100:80serial-numberrevocation-check nonersakeypair sast2!!crypto pki trustpoint iosra
enrollment url http://10.1.1.200:80
revocation-check none
rsakeypair iosra
!
!
crypto pki certificate chain cmeserver
certificate 1B
30820207 30820170 A0030201 0202011B 300D0609 2A864886 F70D0101 04050030
....
quit
certificate ca 01
3082026B 308201D4 A0030201 02020101 300D0609 2A864886 F70D0101 04050030
...
quit
crypto pki certificate chain sast2
certificate 1C
30820207 30820170 A0030201 0202011C 300D0609 2A864886 F70D0101 04050030
....
quit
certificate ca 01
3082026B 308201D4 A0030201 02020101 300D0609 2A864886 F70D0101 04050030
.....
quit
crypto pki certificate chain capf-tp
crypto pki certificate chain iosra
certificate 04
30820201 3082016A A0030201 02020104 300D0609 2A864886 F70D0101 04050030
......
certificate ca 01
308201F9 30820162 A0030201 02020101 300D0609 2A864886 F70D0101 04050030
....
quit
!
!
credentials
ctl-service admin cisco secret 1 094F471A1A0A464058
ip source-address 10.1.1.1 port 2444
trustpoint cmeserver
!
!
telephony-service
no auto-reg-ephone
load 7960-7940 P00307010200
load 7914 S00104000100
load 7941GE TERM41.7-0-0-129DEV
load 7970 TERM70.7-0-0-77DEV
max-ephones 20
max-dn 10
ip source-address 10.1.1.1 port 2000 secondary 10.1.1.100
secure-signaling trustpoint cmeserver
cnf-file location flash:
cnf-file perphone
dialplan-pattern 1 2... extension-length 4
max-conferences 8 gain -6
transfer-pattern ....
tftp-server-credentials trustpoint cmeserver
server-security-mode secure
device-security-mode encrypted
load-cfg-file slot0:Ringlist.xml alias Ringlist.xml sign
load-cfg-file slot0:P00307010200.bin alias P00307010200.bin
load-cfg-file slot0:P00307010200.loads alias P00307010200.loads
load-cfg-file slot0:P00307010200.sb2 alias P00307010200.sb2
load-cfg-file slot0:P00307010200.sbn alias P00307010200.sbn
load-cfg-file slot0:cnu41.2-7-4-116dev.sbn alias cnu41.2-7-4-116dev.sbn
load-cfg-file slot0:Jar41.2-9-0-101dev.sbn alias Jar41.2-9-0-101dev.sbn
load-cfg-file slot0:CVM41.2-0-0-96dev.sbn alias CVM41.2-0-0-96dev.sbn
load-cfg-file slot0:TERM41.DEFAULT.loads alias TERM41.DEFAULT.loads
load-cfg-file slot0:TERM70.DEFAULT.loads alias TERM70.DEFAULT.loads
load-cfg-file slot0:Jar70.2-9-0-54dev.sbn alias Jar70.2-9-0-54dev.sbn
load-cfg-file slot0:cnu70.2-7-4-58dev.sbn alias cnu70.2-7-4-58dev.sbn
load-cfg-file slot0:CVM70.2-0-0-49dev.sbn alias CVM70.2-0-0-49dev.sbn
load-cfg-file slot0:DistinctiveRingList.xml alias DistinctiveRingList.xml sign
load-cfg-file slot0:Piano1.raw alias Piano1.raw sign
load-cfg-file slot0:S00104000100.sbn alias S00104000100.sbn
create cnf-files version-stamp 7960 Aug 13 2005 12:39:24
!
!
ephone 1
device-security-mode encrypted
cert-oper upgrade auth-mode null-string
mac-address 000C.CE3A.817C
type 7960 addon 1 7914
button 1:2 8:8
!
!
ephone 2
device-security-mode encrypted
capf-auth-str 2476
cert-oper upgrade auth-mode null-string
mac-address 0011.2111.6BDD
type 7970
button 1:1
!
!
ephone 3
device-security-mode encrypted
capf-auth-str 5425
cert-oper upgrade auth-mode null-string
mac-address 000D.299D.50DF
type 7970
button 1:3
!
!
ephone 4
device-security-mode encrypted
capf-auth-str 7176
cert-oper upgrade auth-mode null-string
mac-address 000E.D7B1.0DAC
type 7960
button 1:4
!
!
ephone 5
device-security-mode encrypted
mac-address 000F.9048.5077
type 7960
button 1:5
!
!
ephone 6
device-security-mode encrypted
mac-address 0013.C352.E7F1
type 7941GE
button 1:6
!
Secure Cisco Unified CME: Example
Router# show running-config
Building configuration...
Current configuration : 12735 bytes
!
! No configuration change since last restart
!
version 12.4
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
service internal
!
hostname Router
!
boot-start-marker
boot-end-marker
!
card type e1 1 1
logging queue-limit 10000
logging buffered 9999999 debugging
logging rate-limit 10000
no logging console
!
aaa new-model
!
!
aaa accounting connection h323 start-stop group radius
!
aaa session-id common
!
resource policy
!
clock timezone IST 5
no network-clock-participate slot 1
!
!
ip cef
!
!
isdn switch-type primary-net5
!
voice-card 0
no dspfarm
!
voice-card 1
no dspfarm
!
!
ctl-client
server capf 10.13.32.11 trustpoint mytrustpoint1
server tftp 10.13.32.11 trustpoint mytrustpoint1
server cme 10.13.32.11 trustpoint mytrustpoint1
sast1 trustpoint mytrustpoint1
sast2 trustpoint sast2
!
capf-server
port 3084
auth-mode null-string
cert-enroll-trustpoint iosra password 1 mypassword
trustpoint-label mytrustpoint1
source-addr 10.13.32.11
phone-key-size 512
!
voice call debug full-guid
!
voice service voip
srtp fallback
allow-connections h323 to h323
no supplementary-service h450.2
no supplementary-service h450.3
no supplementary-service h450.7
supplementary-service media-renegotiate
h323
emptycapability
ras rrq ttl 4000
!
!
voice class codec 2
codec preference 1 g711alaw
codec preference 2 g711ulaw
!
voice class codec 3
codec preference 1 g729r8
codec preference 8 g711alaw
codec preference 9 g711ulaw
!
voice class codec 1
codec preference 1 g729r8
codec preference 2 g728
codec preference 3 g723ar63
codec preference 4 g711ulaw
!
!
voice iec syslog
voice statistics type iec
voice statistics time-range since-reset
!
!
!
crypto pki server myra
database level complete
grant auto
lifetime certificate 1800
!
crypto pki trustpoint myra
enrollment url http://10.13.32.11:80
revocation-check none
rsakeypair iosra
!
crypto pki trustpoint mytrustpoint1
enrollment url http://10.13.32.11:80
revocation-check none
rsakeypair mytrustpoint1
!
crypto pki trustpoint sast2
enrollment url http://10.13.32.11:80
revocation-check none
rsakeypair sast2
!
!
crypto pki certificate chain myra
certificate ca 01
308201F9 30820162 A0030201 02020101 300D0609 2A864886 F70D0101 04050030
10310E30 0C060355 04031305 696F7372 61301E17 0D303630 37303730 35343031
375A170D 30393037 30363035 34303137 5A301031 0E300C06 03550403 1305696F
73726130 819F300D 06092A86 4886F70D 01010105 0003818D 00308189 02818100
D8CE29F9 C9FDB1DD 0E1517E3 6CB4AAF7 52B83DE2 1C017ACA DFC4AF42 F9D10D08
E74BF95B 29378902 B49E32C4 85907384 84CAE4B2 7759BB84 8AB1F578 580793C4
B11A2DBE B2ED02CC DA0C3824 A5FCC377 18CE87EA C0C297BA BE54530F E62247D8
1483CD14 9FD89EFE 05DFBB37 E03FD3F8 B2B1C0B8 A1931BCC B1174A9E 6566F8F5
02030100 01A36330 61300F06 03551D13 0101FF04 05300301 01FF300E 0603551D
0F0101FF 04040302 0186301F 0603551D 23041830 168014B7 16F6FD67 29666C90
D0C62515 E14265A9 EB256230 1D060355 1D0E0416 0414B716 F6FD6729 666C90D0
C62515E1 4265A9EB 2562300D 06092A86 4886F70D 01010405 00038181 002B7F41
64535A66 D20D888E 661B9584 5E3A28DF 4E5A95B9 97E57CAE B07A7C38 7F3B60EE
75C7E5DE 6DF19B06 5F755FB5 190BABFC EF272CEF 865FE01B 1CE80F98 F320A569
CAFFA5D9 3DB3E7D8 8A86C66C F227FF81 6C4449F2 AF8015D9 8129C909 81AFDC01
180B61E8 85E19873 96DB3AE3 E6B70726 9BF93521 CA2FA906 99194ECA 8F
quit
crypto pki certificate chain mytrustpoint1
certificate 02
308201AB 30820114 A0030201 02020102 300D0609 2A864886 F70D0101 04050030
10310E30 0C060355 04031305 696F7372 61301E17 0D303630 37303730 35343233
385A170D 30393037 30363035 34303137 5A301A31 18301606 092A8648 86F70D01
09021609 32383531 2D434D45 32305C30 0D06092A 864886F7 0D010101 0500034B
00304802 4100B3ED A902646C 3851B7F6 CF94887F 0EC437E3 3B6FEDB2 2B4B45A6
3611C243 5A0759EA 1E8D96D1 60ABE028 ED6A3F2A E95DCE45 BE0921AF 82E53E57
17CC12F0 C1270203 010001A3 4F304D30 0B060355 1D0F0404 030205A0 301F0603
551D2304 18301680 14B716F6 FD672966 6C90D0C6 2515E142 65A9EB25 62301D06
03551D0E 04160414 4EE1943C EA817A9E 7010D5B8 0467E9B0 6BA76746 300D0609
2A864886 F70D0101 04050003 81810003 564A6DA1 868B2669 7C096F9A 41173CFC
E49246EE C645E30B A0753E3B E1A265D1 6EA5A829 F10CD0E8 3F2E3AD4 39D8DFE8
83525F2B D19F5E15 F27D6262 62852D1F 43629B68 86D91B5F 7B2E2C25 3BD2CCC3
00EF4028 714339B2 6A7E0B2F 131D2D9E 0BE08853 5CCAE47C 4F74953C 19305A20
B2C97808 D6E01351 48366421 A1D407
quit
certificate ca 01
308201F9 30820162 A0030201 02020101 300D0609 2A864886 F70D0101 04050030
10310E30 0C060355 04031305 696F7372 61301E17 0D303630 37303730 35343031
375A170D 30393037 30363035 34303137 5A301031 0E300C06 03550403 1305696F
73726130 819F300D 06092A86 4886F70D 01010105 0003818D 00308189 02818100
D8CE29F9 C9FDB1DD 0E1517E3 6CB4AAF7 52B83DE2 1C017ACA DFC4AF42 F9D10D08
E74BF95B 29378902 B49E32C4 85907384 84CAE4B2 7759BB84 8AB1F578 580793C4
B11A2DBE B2ED02CC DA0C3824 A5FCC377 18CE87EA C0C297BA BE54530F E62247D8
1483CD14 9FD89EFE 05DFBB37 E03FD3F8 B2B1C0B8 A1931BCC B1174A9E 6566F8F5
02030100 01A36330 61300F06 03551D13 0101FF04 05300301 01FF300E 0603551D
0F0101FF 04040302 0186301F 0603551D 23041830 168014B7 16F6FD67 29666C90
D0C62515 E14265A9 EB256230 1D060355 1D0E0416 0414B716 F6FD6729 666C90D0
C62515E1 4265A9EB 2562300D 06092A86 4886F70D 01010405 00038181 002B7F41
64535A66 D20D888E 661B9584 5E3A28DF 4E5A95B9 97E57CAE B07A7C38 7F3B60EE
75C7E5DE 6DF19B06 5F755FB5 190BABFC EF272CEF 865FE01B 1CE80F98 F320A569
CAFFA5D9 3DB3E7D8 8A86C66C F227FF81 6C4449F2 AF8015D9 8129C909 81AFDC01
180B61E8 85E19873 96DB3AE3 E6B70726 9BF93521 CA2FA906 99194ECA 8F
quit
crypto pki certificate chain sast2
certificate 03
308201AB 30820114 A0030201 02020103 300D0609 2A864886 F70D0101 04050030
10310E30 0C060355 04031305 696F7372 61301E17 0D303630 37303730 35343331
375A170D 30393037 30363035 34303137 5A301A31 18301606 092A8648 86F70D01
09021609 32383531 2D434D45 32305C30 0D06092A 864886F7 0D010101 0500034B
00304802 4100C703 840B11A7 81FCE5AE A14FE593 5114D3C2 5473F488 B8FB4CC5
41EAFA3A D99381D8 21AE6AA9 BA83A84E 9DF3E8C6 54978787 5EF6CC35 C334D55E
A3051372 17D30203 010001A3 4F304D30 0B060355 1D0F0404 030205A0 301F0603
551D2304 18301680 14B716F6 FD672966 6C90D0C6 2515E142 65A9EB25 62301D06
03551D0E 04160414 EB2146B4 EE24AA61 8B5D2F8D 2AD3B786 CBADC8F2 300D0609
2A864886 F70D0101 04050003 81810057 BA0053E9 8FD54B25 72D85A4C CAB47F26
8316F494 E94DFFB9 8E9D065C 9748465C F54719CA C7724F50 67FBCAFF BC332109
DC2FB93D 5AD86583 EDC3E648 39274CE8 D4A5F002 5F21ED3C 6D524AB7 7F5B1876
51867027 9BD2FFED 06984558 C903064E 5552015F 289BA9BB 308D327A DFE0A3B9
78CF2B02 2DD4C208 80CDC0A8 43A26A
quit
certificate ca 01
308201F9 30820162 A0030201 02020101 300D0609 2A864886 F70D0101 04050030
10310E30 0C060355 04031305 696F7372 61301E17 0D303630 37303730 35343031
375A170D 30393037 30363035 34303137 5A301031 0E300C06 03550403 1305696F
73726130 819F300D 06092A86 4886F70D 01010105 0003818D 00308189 02818100
D8CE29F9 C9FDB1DD 0E1517E3 6CB4AAF7 52B83DE2 1C017ACA DFC4AF42 F9D10D08
E74BF95B 29378902 B49E32C4 85907384 84CAE4B2 7759BB84 8AB1F578 580793C4
B11A2DBE B2ED02CC DA0C3824 A5FCC377 18CE87EA C0C297BA BE54530F E62247D8
1483CD14 9FD89EFE 05DFBB37 E03FD3F8 B2B1C0B8 A1931BCC B1174A9E 6566F8F5
02030100 01A36330 61300F06 03551D13 0101FF04 05300301 01FF300E 0603551D
0F0101FF 04040302 0186301F 0603551D 23041830 168014B7 16F6FD67 29666C90
D0C62515 E14265A9 EB256230 1D060355 1D0E0416 0414B716 F6FD6729 666C90D0
C62515E1 4265A9EB 2562300D 06092A86 4886F70D 01010405 00038181 002B7F41
64535A66 D20D888E 661B9584 5E3A28DF 4E5A95B9 97E57CAE B07A7C38 7F3B60EE
75C7E5DE 6DF19B06 5F755FB5 190BABFC EF272CEF 865FE01B 1CE80F98 F320A569
CAFFA5D9 3DB3E7D8 8A86C66C F227FF81 6C4449F2 AF8015D9 8129C909 81AFDC01
180B61E8 85E19873 96DB3AE3 E6B70726 9BF93521 CA2FA906 99194ECA 8F
quit
!
!
username admin password 0 mypassword2
username cisco password 0 mypassword2
!
!
controller E1 1/0
pri-group timeslots 1-31
!
controller E1 1/1
pri-group timeslots 1-31
gw-accounting aaa
!
!
!
!
!
interface GigabitEthernet0/0
ip address 10.13.32.11 255.255.255.0
duplex auto
speed auto
fair-queue 64 256 32
h323-gateway voip interface
h323-gateway voip id GK1 ipaddr 10.13.32.13 1719
h323-gateway voip id GK2 ipaddr 10.13.32.16 1719
h323-gateway voip h323-id 2851-CiscoUnifiedCME
h323-gateway voip tech-prefix 1#
ip rsvp bandwidth 1000 100
!
interface GigabitEthernet0/1
no ip address
shutdown
duplex auto
speed auto
!
interface Serial1/0:15
no ip address
encapsulation hdlc
isdn switch-type primary-net5
isdn protocol-emulate network
isdn incoming-voice voice
no cdp enable
!
interface Serial1/1:15
no ip address
encapsulation hdlc
isdn switch-type primary-net5
isdn protocol-emulate network
isdn incoming-voice voice
no cdp enable
!
ip route 0.0.0.0 0.0.0.0 10.13.32.1
!
!
ip http server
ip http authentication local
no ip http secure-server
ip http path flash:
!
!
!
!
!
!
tftp-server flash:music-on-hold.au
tftp-server flash:TERM70.DEFAULT.loads
tftp-server flash:TERM71.DEFAULT.loads
tftp-server flash:P00308000300.bin
tftp-server flash:P00308000300.loads
tftp-server flash:P00308000300.sb2
tftp-server flash:P00308000300.sbn
tftp-server flash:SCCP70.8-0-3S.loads
tftp-server flash:cvm70sccp.8-0-2-25.sbn
tftp-server flash:apps70.1-1-2-26.sbn
tftp-server flash:dsp70.1-1-2-26.sbn
tftp-server flash:cnu70.3-1-2-26.sbn
tftp-server flash:jar70sccp.8-0-2-25.sbn
radius-server host 10.13.32.241 auth-port 1645 acct-port 1646
radius-server timeout 40
radius-server deadtime 2
radius-server key cisco
radius-server vsa send accounting
!
control-plane
!
no call rsvp-sync
!
!
voice-port 1/0/0
!
voice-port 1/0/1
!
voice-port 1/0:15
!
voice-port 1/1:15
!
!
!
!
!
dial-peer voice 1 voip
destination-pattern ........
voice-class codec 2
session target ras
incoming called-number 9362....
dtmf-relay h245-alphanumeric
req-qos controlled-load audio
!
dial-peer voice 2 pots
destination-pattern 93621101
!
dial-peer voice 3 pots
destination-pattern 93621102
!
dial-peer voice 10 voip
destination-pattern 2668....
voice-class codec 1
session target ipv4:10.13.46.200
!
dial-peer voice 101 voip
shutdown
destination-pattern 5694....
voice-class codec 1
session target ipv4:10.13.32.10
incoming called-number 9362....
!
dial-peer voice 102 voip
shutdown
destination-pattern 2558....
voice-class codec 1
session target ipv4:10.13.32.12
incoming called-number 9362....
!
dial-peer voice 103 voip
shutdown
destination-pattern 9845....
voice-class codec 1
session target ipv4:10.13.32.14
incoming called-number 9362....
!
dial-peer voice 104 voip
shutdown
destination-pattern 9844....
voice-class codec 1
session target ipv4:10.13.32.15
incoming called-number 9362....
!
dial-peer voice 201 pots
destination-pattern 93625...
no digit-strip
direct-inward-dial
port 1/0:15
!
dial-peer voice 202 pots
destination-pattern 93625...
no digit-strip
direct-inward-dial
port 1/1:15
!
!
gateway
timer receive-rtp 1200
!
!
!
telephony-service
load 7960-7940 P00308000300
max-ephones 4
max-dn 4
ip source-address 10.13.32.11 port 2000
auto assign 1 to 4
secure-signaling trustpoint mytrustpoint1
cnf-file location flash:
cnf-file perphone
voicemail 25589000
max-conferences 4 gain -6
call-forward pattern .T
moh flash:music-on-hold.au
web admin system name admin password mypassword2
dn-webedit
time-webedit
transfer-system full-consult
transfer-pattern ........
tftp-server-credentials trustpoint mytrustpoint1
server-security-mode secure
device-security-mode encrypted
create cnf-files version-stamp 7960 Oct 25 2006 07:19:39
!
!
ephone-dn 1
number 93621000
name 2851-PH1
call-forward noan 25581101 timeout 10
!
!
ephone-dn 2
number 93621001
name 2851-PH2
call-forward noan 98441000 timeout 10
!
!
ephone-dn 3
number 93621002
name 2851-PH3
!
!
ephone-dn 4
number 93621003
name 2851-PH4
!
!
ephone 1
no multicast-moh
device-security-mode encrypted
mac-address 0012.4302.A7CC
type 7970
button 1:1
!
!
!
ephone 2
no multicast-moh
device-security-mode encrypted
mac-address 0017.94CA.9CCD
type 7960
button 1:2
!
!
!
ephone 3
no multicast-moh
device-security-mode encrypted
mac-address 0017.94CA.9833
type 7960
button 1:3
!
!
!
ephone 4
no multicast-moh
device-security-mode none
mac-address 0017.94CA.A141
type 7960
button 1:4
!
!
!
line con 0
logging synchronous level all limit 20480000
line aux 0
line vty 0 4
!
scheduler allocate 20000 1000
ntp clock-period 17179791
ntp server 10.13.32.12
!
webvpn context Default_context
ssl authenticate verify all
!
no inservice
!
!
end
Configuring HTTPS Support for Cisco Unified CME: Example
Configurations similar to the following example are required before HTTPS support for services like local-directory lookup, My Phone Apps, and Extension Mobility in Cisco Unified CME can be configured at four different levels:
Router(config)# ip http serverRouter(config)# crypto pki server IOS-CARouter(cs-server)# database level completeRouter(cs-server)# database url flash:Router(cs-server)# grant autoRouter(cs-server)# exitRouter(config)# crypto pki trustpoint IOS-CARouter(ca-trustpoint)# enrollment url http://10.1.1.1:80Router(ca-trustpoint)# exitRouter(config)# crypto pki server IOS-CARouter(cs-server)# no shutdownRouter(cs-server)# exitRouter(config)# crypto pki trustpoint primary-cmeRouter(ca-trustpoint)# enrollment url http://10.1.1.1.80Router(ca-trustpoint)# revocation-check noneRouter(ca-trustpoint)# rsakeypair primary-cmeRouter(ca-trustpoint)# exitRouter(config)# crypto pki authenticate primary-cmeRouter(config)# crypto pki enroll primary-cmeRouter(config)# crypto pki trustpoint sast-secondaryRouter(ca-trustpoint)# enrollment url http://10.1.1.1:80Router(ca-trustpoint)# revocation-check noneRouter(ca-trustpoint)# rsakeypair sast-secondaryRouter(ca-trustpoint)# exitRouter(config)# crypto pki authenticate sast-secondaryRouter(config)# crypto pki enroll sast-secondaryRouter(config)# ctl-clientRouter(config-ctl-client)# sast1 trustpoint first-sastRouter(config-ctl-client)# sast2 trustpoint second-sastRouter(config-ctl-client)# server application 10.1.2.3 trustpoint first-sastRouter(config-ctl-client)# regenerateRouter(config-ctl-client)# endFor Cisco Unified SCCP IP Phones at the global level:
configure terminaltelephony-servicecnf-file perphoneservice httpsFor Cisco Unified SCCP IP Phones at the ephone-template level:
configure terminalephone-template 1service httpsFor Cisco Unified SIP IP Phones at the global level:
configure terminalvoice register globalservice httpsFor Cisco Unified SIP IP Phones at the voice register template level:
configure terminalvoice register template 1service httpsWhere to Go Next
PKI Management
Cisco IOS public key infrastructure (PKI) provides certificate management to support security protocols such as IP Security (IPsec), secure shell (SSH), and secure socket layer (SSL). For more information, see the following documents:
•
"Implementing and Managing a PKI Features Roadmap" in Cisco IOS Security Configuration Guide
•
Cisco IOS Security Command Reference
Cisco VG224 Analog Phone Gateway
•
To configure secure endpoints on the Cisco VG224 Analog Phone Gateway, see the "Configuring Secure Signalling and Media Encryption on the Cisco VG224" section of Supplementary Services Features for FXS Ports on Cisco IOS Voice Gateways Configuration Guide, Release 12.4T.
Additional References
The following sections provide references related to Cisco Unified CME features.
Related Documents
Cisco Unified CME configuration
•
Cisco Unified CME Command Reference
Cisco IOS commands
•
Cisco IOS Voice Command Reference
Cisco IOS configuration
•
Cisco IOS Voice Configuration Library
Cisco VG224 Analog Phone Gateway
Phone documentation for Cisco Unified CME
Technical Assistance
Feature Information for Security
Table 6 lists the features in this module and enhancements to the features by version.
To determine the correct Cisco IOS release to support a specific Cisco Unified CME version, see the Cisco Unified CME and Cisco IOS Software Version Compatibility Matrix at http://www.cisco.com/en/US/docs/voice_ip_comm/cucme/requirements/guide/33matrix.htm
Use Cisco Feature Navigator to find information about platform support and software image support. Cisco Feature Navigator enables you to determine which Cisco IOS software images support a specific software release, feature set, or platform. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.
Note
Table 6 lists the Cisco Unified CME version that introduced support for a given feature. Unless noted otherwise, subsequent versions of Cisco Unified CME software also support that feature.

 Feedback
Feedback