-
Catalyst 3550 Multilayer Switch Software Configuration Guide, 12.1(9)EA1
-
Index
-
Preface
-
Overview
-
Using the Command-Line Interface
-
Getting Started with CMS
-
Configuring the Switch IP Address and Default Gateway
-
Configuring IE2100 CNS Agents
-
Clustering Switches
-
Administering the Switch
-
Configuring 802.1X Port-Based Authentication
-
Configuring Interface Characteristics
-
Creating and Maintaining VLANs
-
Configuring VTP
-
Configuring Voice VLAN
-
Configuring 802.1Q and Layer 2 Protocol Tunneling
-
Configuring STP
-
Configuring RSTP and MSTP
-
Configuring Optional Spanning-Tree Features
-
Configuring the DHCP Option 82 for Subscriber Identification
-
Configuring IGMP Snooping and MVR
-
Configuring Port-Based Traffic Control
-
Configuring CDP
-
Configuring UDLD
-
Configuring SPAN
-
Configuring RMON
-
Configuring System Message Logging
-
Configuring SNMP
-
Configuring Network Security with ACLs
-
Configuring QoS
-
Configuring EtherChannels
-
Configuring IP Unicast Routing
-
Configuring HSRP
-
Configuring IP Multicast Routing
-
Configuring MSDP
-
Configuring Fallback Bridging
-
Troubleshooting
-
Supported MIBs
-
Working with the IOS File System, Configuration Files, and Software Images
-
Unsupported CLI Commands for Release 12.1(9)EA1
-
Table Of Contents
Using SNMP to Access MIB Variables
Configuring Trap Managers and Enabling Traps
Setting the Agent Contact and Location Information
Limiting TFTP Servers Used Through SNMP
Configuring SNMP
This chapter describes how to configure the Simple Network Management Protocol (SNMP) on your switch.
Note
For complete syntax and usage information for the commands used in this chapter, refer to the Catalyst 3550 Multilayer Switch Command Reference for this release and to the Cisco IOS Configuration Fundamentals Command Reference for Release 12.1.
This chapter consists of these sections:
Understanding SNMP
SNMP is an application-layer protocol that provides a message format for communication between SNMP managers and agents. The SNMP manager can be part of a network management system (NMS) such as CiscoWorks. The agent and management information base (MIB) reside on the switch. To configure SNMP on the switch, you define the relationship between the manager and the agent.
The SNMP agent contains MIB variables whose values the SNMP manager can request or change. A manager can get a value from an agent or store a value into the agent. The agent gathers data from the MIB, the repository for information about device parameters and network data. The agent can also respond to a manager's requests to get or set data.
An agent can send unsolicited traps to the manager. Traps are messages alerting the SNMP manager to a condition on the network. Traps can mean improper user authentication, restarts, link status (up or down), MAC address tracking, closing of a TCP connection, loss of connection to a neighbor, or other significant events.
This section includes this conceptual information:
•
Using SNMP to Access MIB Variables
SNMP Versions
This software release supports these SNMP versions:
•
SNMPv1—The Simple Network Management Protocol, a Full Internet Standard, defined in RFC 1157.
•
SNMPv2C, which has these features:
–
SNMPv2—Version 2 of the Simple Network Management Protocol, a Draft Internet Standard, defined in RFCs 1902 through 1907.
–
SNMPv2C—The Community-based Administrative Framework for SNMPv2, an Experimental Internet Protocol defined in RFC 1901.
SNMPv2C replaces the Party-based Administrative and Security Framework of SNMPv2Classic with the Community-based Administrative Framework of SNMPv2C while retaining the bulk retrieval and improved error handling of SNMPv2Classic.
Both SNMPv1 and SNMPv2C use a community-based form of security. The community of managers able to access the agent's MIB is defined by an IP address access control list and password.
SNMPv2C includes a bulk retrieval mechanism and more detailed error message reporting to management stations. The bulk retrieval mechanism retrieves tables and large quantities of information, minimizing the number of round-trips required. The SNMPv2C improved error-handling includes expanded error codes that distinguish different kinds of error conditions; these conditions are reported through a single error code in SNMPv1. Error return codes now report the error type.
You must configure the SNMP agent to use the version of SNMP supported by the management station. An agent can communicate with multiple managers; for this reason, you can configure the software to support communications with one management station using the SNMPv1 protocol and another using the SNMPv2 protocol.
SNMP Manager Functions
The SNMP manager uses information in the MIB to perform the operations described in Table 25-1.
Table 25-1 SNMP Operations
get-request
Retrieves a value from a specific variable.
get-next-request
Retrieves a value from a variable within a table.1
get-bulk-request2
Retrieves large blocks of data, such as multiple rows in a table, that would otherwise require the transmission of many small blocks of data.
get-response
Replies to a get-request, get-next-request, and set-request sent by an NMS.
set-request
Stores a value in a specific variable.
trap
An unsolicited message sent by an SNMP agent to an SNMP manager when some event has occurred.
1 With this operation, an SNMP manager does not need to know the exact variable name. A sequential search is performed to find the needed variable from within a table.
2 The get-bulk command only works with SNMPv2.
SNMP Agent Functions
The SNMP agent responds to SNMP manager requests as follows:
•
Get a MIB variable—The SNMP agent begins this function in response to a request from the NMS. The agent retrieves the value of the requested MIB variable and responds to the NMS with that value.
•
Set a MIB variable—The SNMP agent begins this function in response to a message from the NMS. The SNMP agent changes the value of the MIB variable to the value requested by the NMS.
The SNMP agent also sends unsolicited trap messages to notify an NMS that a significant event has occurred on the agent. Examples of trap conditions include, but are not limited to, when a port or module goes up or down, when spanning-tree topology changes occur, and when authentication failures occur.
SNMP Community Strings
SNMP community strings authenticate access to MIB objects and function as embedded passwords. In order for the NMS to access the switch, the community string definitions on the NMS must match at least one of the three community string definitions on the switch.
A community string can have one of these attributes:
•
Read-only—Gives read access to authorized management stations to all objects in the MIB except the community strings, but does not allow write access
•
Read-write—Gives read and write access to authorized management stations to all objects in the MIB, but does not allow access to the community strings
•
Read-write-all—Gives read and write access to authorized management stations to all objects in the MIB, including the community strings
Note
When a cluster is created, the command switch manages the exchange of messages among member switches and the SNMP application. The Cluster Management software appends the member switch number (@esN, where N is the switch number) to the first configured RW and RO community strings on the command switch and propagates them to the member switches. For more information, see "Clustering Switches."
Using SNMP to Access MIB Variables
An example of an NMS is the CiscoWorks network management software. CiscoWorks 2000 software uses the switch MIB variables to set device variables and to poll devices on the network for specific information. The results of a poll can be displayed as a graph and analyzed to troubleshoot internetworking problems, increase network performance, verify the configuration of devices, monitor traffic loads, and more.
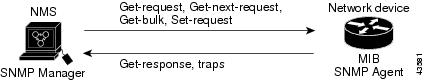
As shown in Figure 25-1, the SNMP agent gathers data from the MIB. The agent can send traps, or notification of certain events, to the SNMP manager, which receives and processes the traps. Traps are messages alerting the SNMP manager to a condition on the network such as improper user authentication, restarts, link status (up or down), MAC address tracking, and so forth. The SNMP agent also responds to MIB-related queries sent by the SNMP manager in get-request, get-next-request, and set-request format.
Figure 25-1 SNMP Network
For information on supported MIBs and how to access them, see "Supported MIBs."
Configuring SNMP
This section describes how to configure SNMP on your switch. It contains this configuration information:
•
Configuring Community Strings
•
Configuring Trap Managers and Enabling Traps
•
Setting the Agent Contact and Location Information
•
Limiting TFTP Servers Used Through SNMP
Default SNMP Configuration
Table 25-2 shows the default SNMP configuration.
Disabling the SNMP Agent
Beginning in privileged EXEC mode, follow these steps to disable the SNMP agent:
No specific IOS command exists to enable SNMP. The first snmp-server global configuration command that you enter enables SNMPv1 and SNMPv2.
Configuring Community Strings
You use the SNMP community string to define the relationship between the SNMP manager and the agent. The community string acts like a password to permit access to the agent on the switch. Optionally, you can specify one or more of these characteristics associated with the string:
•
An access list of IP addresses of the SNMP managers that are permitted to use the community string to gain access to the agent
•
A MIB view, which defines the subset of all MIB objects accessible to the given community
•
Read and write or read-only permission for the MIB objects accessible to the community
Beginning in privileged EXEC mode, follow these steps to configure a community string on the switch:
Note
To disable access for an SNMP community, set the community string for that community to the null string (do not enter a value for the community string).
To remove a specific community string, use the no snmp-server community string global configuration command.
This example shows how to assign the string comaccess to SNMP, to allow read-only access, and to specify that IP access list 4 can use the community string to gain access to the switch SNMP agent:
Switch(config)# snmp-server community comaccess ro 4Configuring Trap Managers and Enabling Traps
A trap manager is a management station that receives and processes traps. Traps are system alerts that the switch generates when certain events occur. By default, no trap manager is defined, and no traps are issued.
Switches running this IOS release can have an unlimited number of trap managers. Community strings can be any length.
Table 25-3 describes the supported switch traps (notification types). You can enable any or all of these traps and configure a trap manager to receive them.
Note
Though visible in the command-line help string, the hsrp keyword takes affect only when the enhanced multilayer software image (EMI) is installed. All Catalyst 3550 Gigabit Ethernet switches ship with the EMI installed. Catalyst 3550 Fast Ethernet switches can be shipped with either the standard multilayer software image (SMI) or EMI pre-installed. You can order the Enhanced Multilayer Software Image Upgrade kit to upgrade Catalyst 3550 Fast Ethernet switches from the SMI to the EMI.
Some notification types cannot be controlled with the snmp-server enable global configuration command, for example, tty and udp-port. These notification types are always enabled. You can use the snmp-server host global configuration command to a specific host to receive the notification types listed in Table 25-3.
Beginning in privileged EXEC mode, follow these steps to configure the switch to send traps to a host:
Step 1
configure terminal
Enter global configuration mode.
Step 2
snmp-server host host-addr {traps | informs} {version {1 | 2c}} community-string notification-type
Specify the recipient of the trap message.
•
For host-addr, specify the name or address of the host (the targeted recipient).
•
Specify traps (the default) to send SNMP traps to the host. Specify informs to send SNMP informs to the host.
•
Specify the SNMP version to support. Version 1, the default, is not available with informs.
Note
Though visible in the command-line help string, the version 3 keyword (SNMPv3) is not supported.
•
For community-string, specify the string to send with the notification operation. Though you can set this string using the snmp-server host command, we recommend that you define this string by using the snmp-server community command before using the snmp-server host command.
•
For notification-type, use the keywords listed in Table 25-3.
Step 3
snmp-server enable traps notification-types
Enable the switch to send specific traps. For a list of traps, see Table 25-3.
To enable multiple types of traps, you must issue a separate snmp-server enable traps command for each trap type.
Step 4
end
Return to privileged EXEC mode.
Step 5
show running-config
Verify your entries.
Step 6
copy running-config startup-config
(Optional) Save your entries in the configuration file.
To remove the specified host from receiving traps, use the no snmp-server host host global configuration command. To disable a specific trap type, use the no snmp-server enable traps notification-types global configuration command.
Setting the Agent Contact and Location Information
Beginning in privileged EXEC mode, follow these steps to set the system contact and location of the SNMP agent so that these descriptions can be accessed through the configuration file:
Limiting TFTP Servers Used Through SNMP
Beginning in privileged EXEC mode, follow these steps to limit the TFTP servers used for saving and loading configuration files through SNMP to the servers specified in an access list:
SNMP Examples
This example shows how to enable SNMPv1 and SNMPv2C. The configuration permits any SNMP manager to access all objects with read-only permissions using the community string public. This configuration does not cause the switch to send any traps.
Switch(config)# snmp-server community publicThis example shows how to permit any SNMP manager to access all objects with read-only permission using the community string public. The switch also sends VTP traps to the hosts 192.180.1.111 and 192.180.1.33 using SNMPv1 and to the host 192.180.1.27 using SNMPv2C. The community string public is sent with the traps.
Switch(config)# snmp-server community publicSwitch(config)# snmp-server enable traps vtpSwitch(config)# snmp-server host 192.180.1.27 version 2c publicSwitch(config)# snmp-server host 192.180.1.111 version 1 publicSwitch(config)# snmp-server host 192.180.1.33 publicThis example shows how to allow read-only access for all objects to members of access list 4 that use the comaccess community string. No other SNMP managers have access to any objects. SNMP Authentication Failure traps are sent by SNMPv2C to the host cisco.com using the community string public.
Switch(config)# snmp-server community comaccess ro 4Switch(config)# snmp-server enable traps snmp authenticationSwitch(config)# snmp-server host cisco.com version 2c publicThis example shows how to send Entity MIB traps to the host cisco.com. The community string is restricted. The first line enables the switch to send Entity MIB traps in addition to any traps previously enabled. The second line specifies the destination of these traps and overwrites any previous snmp-server host commands for the host cisco.com.
Switch(config)# snmp-server enable traps entitySwitch(config)# snmp-server host cisco.com restricted entityThis example shows how to enable the switch to send all traps to the host myhost.cisco.com using the community string public:
Switch(config)# snmp-server enable trapsSwitch(config)# snmp-server host myhost.cisco.com publicDisplaying SNMP Status
To display SNMP input and output statistics, including the number of illegal community string entries, errors, and requested variables, use the show snmp privileged EXEC command. For information about the fields in this display, refer to the Cisco IOS Configuration Fundamentals Command Reference for Release 12.1.

 Feedback
Feedback