-
Cisco 1800 Series Integrated Services Routers (Fixed) Software Configuration Guide
-
Preface
-
Basic Router Configuration
-
Sample Network Deployments
-
Configuring PPP over Ethernet with NAT
-
Configuring PPP over ATM with NAT
-
Configuring a LAN with DHCP and VLANs
-
Configuring a VPN Using Easy VPN and an IPSec Tunnel
-
Configuring VPNs Using an IPSec Tunnel and Generic Routing Encapsulation
-
Configuring a Simple Firewall
-
Configuring a Wireless LAN Connection
-
Sample Configuration
-
Additional Configuration Options
-
Configuring Security Features
-
Configuring Dial Backup and Remote Management
-
Troubleshooting
-
Cisco IOS Software Basic Skills
-
Concepts
-
ROM Monitor
-
Common Port Assignments
-
Index
-
Table Of Contents
Apply Access Lists and Inspection Rules to Interfaces
Configuring a Simple Firewall
The Cisco 1800 integrated services routers support network traffic filtering by means of access lists. The router also supports packet inspection and dynamic temporary access lists by means of Context-Based Access Control (CBAC).
Basic traffic filtering is limited to configured access list implementations that examine packets at the network layer or, at most, the transport layer, permitting or denying the passage of each packet through the firewall. However, the use of inspection rules in CBAC allows the creation and use of dynamic temporary access lists. These dynamic lists allow temporary openings in the configured access lists at firewall interfaces. These openings are created when traffic for a specified user session exits the internal network through the firewall. The openings allow returning traffic for the specified session (that would normally be blocked) back through the firewall.
See the Cisco IOS Security Configuration Guide, Release 12.3, for more detailed information on traffic filtering and firewalls.
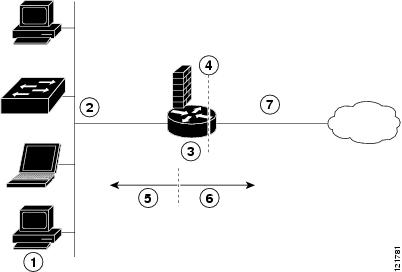
Figure 8-1 shows a network deployment using PPPoE or PPPoA with NAT and a firewall.
Figure 8-1 Router with Firewall Configured
In the configuration example that follows, the firewall is applied to the outside WAN interface (FE0) on the Cisco 1811 or Cisco 1812 and protects the Fast Ethernet LAN on FE2 by filtering and inspecting all traffic entering the router on the Fast Ethernet WAN interface FE1. Note that in this example, the network traffic originating from the corporate network, network address 10.1.1.0, is considered safe traffic and is not filtered.
Configuration Tasks
Perform the following tasks to configure this network scenario:
•
Apply Access Lists and Inspection Rules to Interfaces
An example showing the results of these configuration tasks is shown in the section "Configuration Example."
Note
The procedures in this chapter assume that you have already configured basic router features as well as PPPoE or PPPoA with NAT. If you have not performed these configurations tasks, see Chapter 1, "Basic Router Configuration," Chapter 3, "Configuring PPP over Ethernet with NAT," and Chapter 4, "Configuring PPP over ATM with NAT," as appropriate for your router. You may have also configured DHCP, VLANs, and secure tunnels.
Configure Access Lists
Perform these steps to create access lists for use by the firewall, beginning in global configuration mode:
Step 1
access-list access-list-number {deny | permit} protocol source source-wildcard [operator [port]] destination
Example:
Router(config)# access-list 103 permit host 200.1.1.1 eq isakmp anyRouter(config)#Creates an access list which prevents Internet- initiated traffic from reaching the local (inside) network of the router, and which compares source and destination ports.
See the Cisco IOS IP Command Reference, Volume 1 of 4: Addressing and Services for details about this command.
Step 2
access-list access-list-number {deny | permit} protocol source source-wildcard destination destination-wildcard
Example:
Router(config)# access-list 105 permit ip 10.1.1.0 0.0.0.255 192.168.0.0 0.0.255.255Router(config)#Creates an access list that allows network traffic to pass freely between the corporate network and the local networks through the configured VPN tunnel.
Configure Inspection Rules
Perform these steps to configure firewall inspection rules for all TCP and UDP traffic, as well as specific application protocols as defined by the security policy, beginning in global configuration mode:
Apply Access Lists and Inspection Rules to Interfaces
Perform these steps to apply the ACLs and inspection rules to the network interfaces, beginning in global configuration mode:
Configuration Example
A telecommuter is granted secure access to a corporate network, using IPSec tunneling. Security to the home network is accomplished through firewall inspection. The protocols that are allowed are all TCP, UDP, RTSP, H.323, NetShow, FTP, and SQLNet. There are no servers on the home network; therefore, no traffic is allowed that is initiated from outside. IPSec tunneling secures the connection from the Home LAN to the corporate network.
Like the Internet Firewall Policy, HTTP need not be specified because Java blocking is not necessary. Specifying TCP inspection allows for single-channel protocols such as Telnet and HTTP. UDP is specified for DNS.
The following configuration example shows a portion of the configuration file for the simple firewall scenario described in the preceding sections.
! Firewall inspection is setup for all tcp and udp traffic as well as specific applicationprotocols as defined by the security policy.ip inspect name firewall tcpip inspect name firewall udpip inspect name firewall rtspip inspect name firewall h323ip inspect name firewall netshowip inspect name firewall ftpip inspect name firewall sqlnet!interface vlan 1 ! This is the internal home networkip inspect firewall in ! inspection examines outbound trafficno cdp enable!interface fastethernet 0 ! FE0 is the outside or internet exposed interface.ip access-group 103 in ! acl 103 permits ipsec traffic from the corp. router as well asdenies internet initiated traffic inbound.ip nat outsideno cdp enable!! acl 103 defines traffic allowed from the peer for the ipsec tunnel.access-list 103 permit udp host 200.1.1.1 any eq isakmpaccess-list 103 permit udp host 200.1.1.1 eq isakmp anyaccess-list 103 permit esp host 200.1.1.1 anyaccess-list 103 permit icmp any any ! allow icmp for debugging but should be disabled dueto security implications.access-list 103 deny ip any any ! prevents internet initiated traffic inbound.no cdp run!

 Feedback
Feedback