Table Of Contents
System Testing
Revised: December 21, 2009This chapter describes the tests performed on the Services Ready Large Branch Network.
Contents
Test Result Summary
Table 1 lists the test cases and their results.
Test Setups
The test cases described in this section use the test setups shown in Figure 1 through Figure 4, in addition to test setups shown in the other figures referenced in the specific test case.
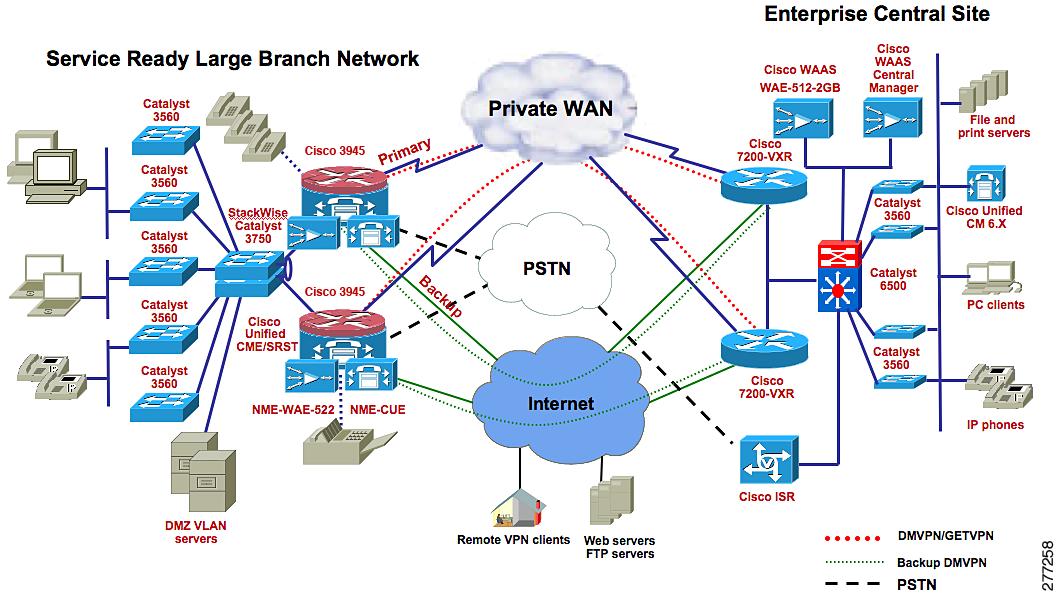
Figure 1 Private WAN, Cisco Unified CME Mode
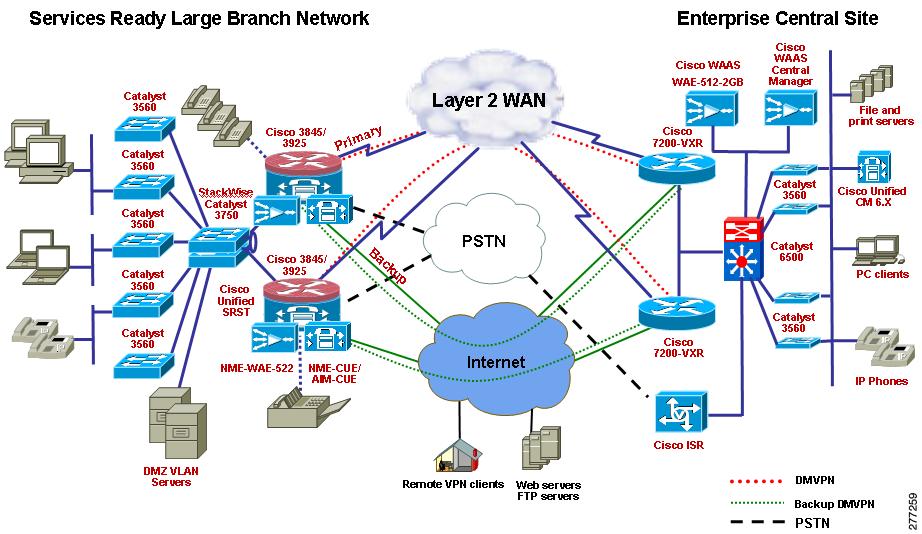
Figure 2 Private WAN, Cisco Unified SRST Mode
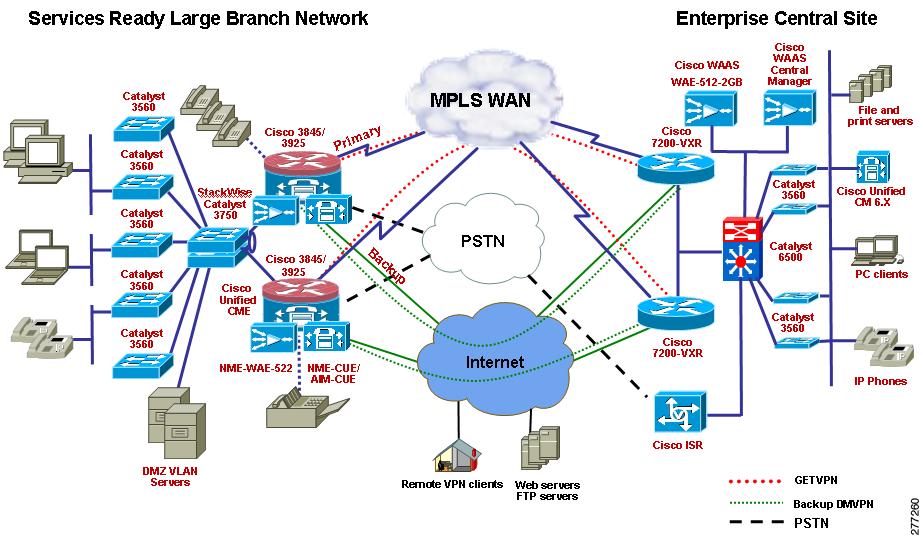
Figure 3 MPLS WAN, Cisco Unified CME Mode
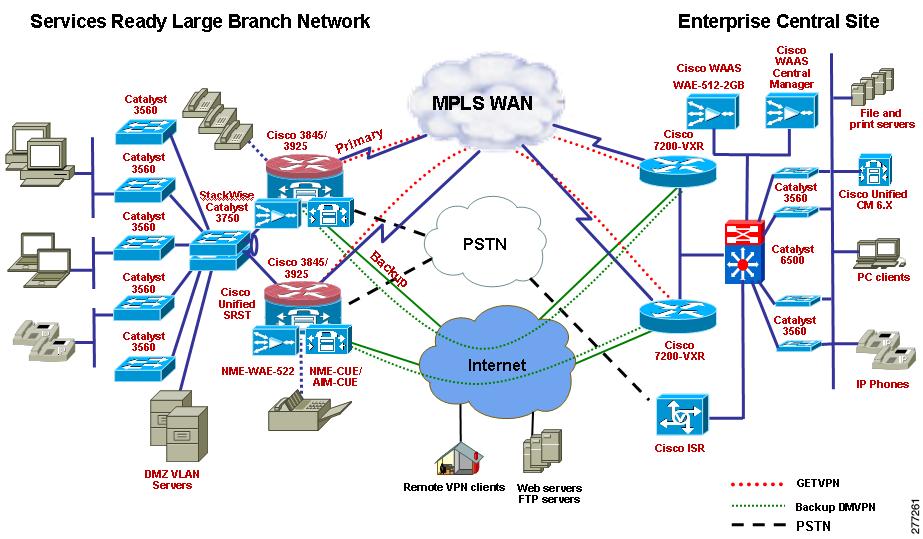
Figure 4 MPLS WAN, Cisco Unified SRST Mode
Traffic Profile
The following traffic profile was used to represent typical traffic in a large enterprise branch network.
HTTP Traffic—75 percent
•
16 KB object size representing large HTML files containing images (10 URLs)
•
4 KB object size representing transactional data (10 URLs)
FTP Traffic—10 percent
•
1 MB file size
SMTP Traffic—10 percent
•
4 KB fixed object size
DNZ Traffic—5 percent
•
89 byte object size
Test Cases
This section contains the following test cases:
•
Network Management Test Cases
•
Cisco Unified SRST Test Cases
WAN Connectivity Test Cases
DS3 Primary WAN Connections for Cisco 3900 Series Large Branch
Gigabit Ethernet Primary WAN Connection for Cisco 3900 Series Large Branch
MLPPP Primary WAN Connection for Cisco 3900 Series Large Branch
MLFR Primary WAN Connection for Cisco 3900 Series Large Branch
SHDSL IMA Secondary WAN Connection for Cisco 3900 Series Large Branch
Interface Removal and Addition to SHDSL IMA Interface
Network Services Test Cases
Layer 2 Access Layer Switch
Set up Catalyst 3560 switches as access layer switches
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure Catalyst 3560 switches in Layer 2 mode.
2.
Define VLANs for voice, data, management, and DMZ.
3.
Enable RSPT for subsecond switchover in case of master distribution switch failure.
4.
Do not enable Layer 3 routing on the access layer switches.
Layer 2 voice, data, management, and DMZ VLANs should come up. During master distribution switch failure, Layer 2 convergence should happen within a second.
Passed
L2 Security-802.1x Authentication on the Access Layer Switch
Set up to verify 802.1x authentication on one of the access layer switches.
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure DHCP snooping on the switch.
2.
Configure a trunk port connecting the access switch to the distribution switches as the trusted port. Configure all other ports as non-trusted ports.
3.
Configure the router as the DHCP server.
4.
Add a Windows DHCP server and connect it to one of the non-trusted ports of the switch.
5.
Configure DAI for VLAN (x,y).
6.
Assign all the switch ports to either x or y VLAN.
7.
Configure the DHCP scope in the DHCP servers to assign IP addresses to x and y VLANs.
8.
Connect phones and PCs to the switch ports.
9.
Place all IP Phones in VLAN x and PCs in VLAN y.
The IP Phones and PCs should obtain IP addresses from the DHCP server on the router and not from the Windows DHCP server, because the Widows server is connected to a non-trusted port.
DAI should build dynamic entries (ACLs) with IP addresses (obtained through DHCP) and corresponding MAC addresses for the phones and PCs.
If a laptop with a statically configured IP address (in the y VLAN) is connected to a switch port associated to the y VLAN, the DAI should prevent the laptop from obtaining network connectivity; that is, it builds a deny ACL for this laptop.
Passed
L2 Security-DHCP Snooping and Dynamic ARP Inspection on Access Layer Switch
Set up to verify DHCP snooping and Dynamic ARP inspection on one of the access switches
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure 802.1x port authentication on several of the switch ports along with DHCP snooping and DAI.
2.
Configure AAA on the switch.
3.
Configure the IP address of the RADIUS server.
4.
Set up the EtherSwitch module as a NAS by providing its IP address in the Cisco Secure ACS server located in HQ.
5.
Install a self-signed certificate on the ACS server.
6.
Configure EAP-PEAP MSCHAPV2 authentication on the ACS server.
7.
Download the ACS certificate onto one of the PCs that is running Windows XP and that is located in the branch office.
8.
Install the certificate on the PC.
9.
Configure the PC for EAP-PEAP MSCHAPV2 authentication.
10.
Connect the IP Phone to the switch port on which 802.1x authentication is enabled.
11.
Connect the PC to the switch port of the IP Phone.
12.
Connect another PC that does not have the ACS certificate installed to another switch port on which 802.1x port authentication is enabled.
The traffic should be distributed 2:1 between the primary and secondary router.
The standby router should take over control after the primary router is power cycled.
When power returns to the primary router, it should take over control from the standby router after waiting for the preemption time to expire.
Passed
L2 Security-Port Security on Access Layer Switch
Set up to verify port security on one of the access layer switches
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure the port security feature on one of the switch ports of the access switch to allow only one MAC address.
2.
Configure the port security aging timer to be 2 seconds, and configure the port security violation policy to Restrict.
3.
Connect a laptop to the switch port.
4.
After the laptop gets an IP address through DHCP, disconnect the laptop and connect a different laptop to the same switch port.
When the laptop is connected to the switch port, it should get an IP address through DHCP. The switch should populate the laptop's MAC address and port information into a port security table.
When another laptop with a different MAC address is connected to the same port, a port security violation error should be displayed on the console of the switch, and the new laptop should not be provided with an IP address.
Passed
L2 Security-IP Source Guard on the Access Layer Switch
Set up to verify IP source guard on one of the access layer switches
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure IP source guard on the switch ports.
2.
Connect a traffic generator to the switch port on which the IP source guard is configured, and send line rate traffic to HQ.
3.
Obtain the IP address of the traffic generator, using DHCP before sending the traffic.
4.
After sending traffic for about 15 minutes, change the source MAC address of the traffic generator connected to the switch port, and observe the behavior.
The traffic from the traffic generator should be successfully allowed from the switch port and should reach the traffic generator at HQ.
The IP source guard feature validates the source MAC address of the host that is connected to the switch port on which the IP source guard is enabled. It associates the host MAC address to the IP address obtained through DHCP.
Once the traffic generator MAC address is changed, traffic should be dropped and not be allowed to pass from the switch port.
Passed
L2 Security-BPDU Guard on the Access Layer Switch
Set up to verify BPDU guard on one of the access layer switches
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure Spanning Tree PortFast with the BPDU guard on the switch port that is connected to PC and phones.
2.
Remove the PC or phone from one of the ports where BPDU guard is enabled, and connect another switch.
The phones and PC ports should be operational and able to send traffic normally after enabling BPDU guard.
The port shut down after connecting the switch.
Passed
Layer 3 Distribution Switches in a Stack
Connect Catalyst 3750 distribution layer switches (at least two) using Cisco StackWise technology, and enable Layer 3 routing.
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Connect Catalyst 3750 switches, using Cisco StackWise technology in the form of a loop.
2.
Configure SVIs for the voice, data, management, and DMZ VLANs.
3.
Configure VTP trunking, and configure the distribution switch as the VTP server and the access layer switches as VTP clients.
4.
Connect one of the uplink ports of the distribution layer switch to the branch router onboard GE ports.
5.
Configure the uplink port as a trunk port, and enable 802.1q trunking.
When the Catalyst 3750 switches are stacked together, they should appear as one switch to any outside entity, such as a branch router. One of the switches in the stack is the stack master, and the rest of them are slaves. The stack master should hold the VLAN database and configuration; the slaves should retain a copy. The stack master should also have console access to the stacked switches.
Passed
QoS on the LAN
Enable conditionally trusted IP Phone and PC and scavenger-class traffic (Advanced) Model Configuration on the Catalyst 3750 and Catalyst 3560 switches
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Enable QoS on the access layer switch. Re-mark all the packets coming from PC endpoints, servers, and so on, with appropriate CoS or DSCP values. Trust the voice and signaling packets coming out of Cisco IP Phones, but re-mark all the packets coming from PCs attached to the IP Phones. Use Ethereal to verify proper packet marking.
2.
Enable MLS QoS on the Catalyst switches.
3.
Configure CoS to DSCP mapping to map CoS 5 to DSCP EF.
4.
Re-mark excess data VLAN traffic marked 0, AF11, AF21, CS3, DSCP 25, and AF41 to scavenger class (CS1).
5.
Define class maps for voice VLAN, voice signaling, interactive video, transactional data, mission-critical data, bulk data, and default (best effort).
6.
Define policy maps and mark voice traffic to DSCP 46 (EF), voice signaling traffic to DSCP 24 (CS3), interactive video to DSCP 34 (AF41), mission-critical traffic to DSCP 25 (CS3), transactional data traffic to DSCP 18 (AF21), bulk data to DSCP 10 (AF11), and default to DSCP 0.
7.
Configure policing (rate limiting) for each class.
8.
Configure Catalyst switch egress queue in 1P3Q3T mode, that is, set up Q1 as the priority queue to carry all voice traffic, and set up the rest of the three queues in shared-bandwidth mode. Assign Q2 for mission-critical data traffic, Q3 for best-effort traffic, and Q2 for scavenger and bulk traffic. Configure shared weights of 70, 25, and 5 for Q2, Q3, and Q4, respectively.
9.
Configure Weighted Tail Drop (WTD) thresholds per queue as shown in Figure 37. For Q2 set the first threshold to 70% and the second threshold to 80%. For Q4, set the first threshold to 40% and the second threshold to 100%.
10.
Verify, using the following show commands:
show mls qos
show mls qos map
show mls qos interface
show mls qos interface policers
show class-map
show policy-map
show policy interface
Voice and data packets should be properly marked by the switches.
Excess traffic should be re-marked to scavenger class and dropped if the scavenger class limit is also exceeded.
Queuing should be engaged only during congestion.
Each traffic type should be properly queued based on the queue assignments.
Passed
WAN Edge QoS-8 Class QoS Model
LLQ for Voice and Interactive Video Traffic
CBWFQ and WRED for Data Traffic
Traffic Shaping on Different WAN Links
Enable traffic shaping on the WAN interface as part of the hierarchical QoS configuration
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure traffic shaping on the WAN links to shape the egress traffic to 95% of the available bandwidth.
2.
Send voice and data traffic to oversubscribe bandwidth.
The egress traffic should be shaped to an average of 95% of the total available bandwidth.
Passed
DSCP/CoS Marking Incoming/Returning Traffic from WAN to LAN
Re-mark ingress traffic to the router coming from the WAN and going to the LAN
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure DSCP to CoS mapping for the various ingress traffic types from the WAN. The marking should match the DSCP value of similar or the same type of traffic egressing the WAN interface.
2.
Verify using the show policy-map interface command and using the Ethereal packet sniffer on the LAN.
The ingress traffic should be properly marked.
Passed
Modification and Deletion of ACLs Defined with Class Map match access-group Command
Modify or delete ACLs defined under class-map configuration mode using match access-group statements
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Change ACLs' source and destination IP addresses.
2.
Change ACLs' source and destination ports.
3.
Delete ACLs.
4.
Save configuration.
5.
Run traffic while making the changes.
The ACL changes or deletions should not have no adverse impact on the router such as tracebacks, memory leaks, or a crash. The changes should be properly handled and applied to the traffic stream.
Passed
Unconfigure and Reconfigure QoS
Remove QoS configuration, and reapply QoS configuration
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Remove QoS configuration.
2.
Reapply QoS configuration.
There should be no adverse impact on the router such as tracebacks, memory leaks, or a crash.
Passed
Unconfigure QoS, Reload Router, and Reconfigure QoS
Remove QoS configuration, and reapply QoS configuration after router reload
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Remove the entire hierarchical QoS configuration from the branch router.
2.
Reload the router.
3.
Reapply the configuration to the branch router while running traffic.
There should be no adverse impact on the router such as tracebacks, memory leaks, or a crash.
Passed
BGP Routing on the Branch
Configure BGP routing to the ISP
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure External BGP (eBGP) on the branch router on the secondary WAN interface.
2.
Inject a default route and a limited set of required routes, using a route filter, into the branch Interior Gateway Protocol (IGP) from the ISP.
3.
Disable synchronization in the BGP configuration.
4.
Advertise only the outside address of the branch to the ISP.
5.
Do not advertise any inside addresses (LAN) of the branch router to the ISP.
6.
Verify by pinging the headend router.
BGP should come up between the branch and the ISP. The default route and all other routes injected from the ISP should be visible in the branch router's Routing Information Base (RIB).
Ping should be successful between the branch and headend router.
Passed
OSPF Routing as IGP Between Branch and Headquarters Network
Enable OSPF between the branch router and headend router, and advertise each other's LAN addresses
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure OSPF routing between the branch router and the headend router.
2.
Advertise all the LAN addresses attached to the branch and the LAN addresses attached to the headend so that the headend router can see the branch network and vice versa.
3.
Redistribute connected and static routes in the branch and headend into OSPF.
4.
Verify by OSPF adjacency, using the show ip ospf neighbors command.
5.
Verify by pinging from the branch LAN to the headend LAN and vice versa.
OSPF adjacency should be established between the branch router and the headend router.
Passed
EIGRP Routing as IGP Between the Branch Router and the Headquarters Router
Enable EIGRP between the branch router and headend router and advertise each other's LAN addresses
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure EIGRP routing between the branch router and the headend router.
2.
Advertise all the LAN addresses attached to the branch and the headend so that the headend router can see the branch network and vice versa.
3.
Redistribute connected and static routes in the branch and headend into EIGRP.
4.
Verify by EIGRP adjacency, using the show ip eigrp neighbors command.
5.
Verify by pinging from the branch LAN to the headend LAN and vice versa.
EIGRP adjacency should be established between the branch router and the headend router.
Ping should be 100% successful.
Passed
Traffic Measurement Using NetFlow When QoS is Enabled on the Branch Router
Enable NetFlow on the branch router
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure NetFlow version 5 or version 9 for both ingress and egress traffic on the WAN and LAN interfaces of the branch router.
2.
Send bidirectional HTTP, FTP, and voice traffic between the branch and the headend router.
3.
Collect protocol distribution charts, interface statistics, and QoS statistics.
4.
Export the statistics to a network analysis module (NAM) located at the enterprise headquarters.
NetFlow should collect the statistics and export it to the NAM. The collected statistics should be within performance requirements.
Passed
NBAR Classification with QoS
Modify Match Protocol Statements and Bandwidth Percentage
Modify "match protocol" statements and bandwidth percentage in the policy map configuration
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
Modify the match protocol statements in the NBAR configuration by adding more protocols, changing the existing HTTP URL, and modifying the percentage bandwidth allocated for each traffic class over a live network
Changes should not cause any abnormal behavior in the branch router such as tracebacks, memory leaks, or crashes. Changes should be applied to traffic.
Passed
100 ACLs
Configure about 100 ACLs on the branch router
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure about 100 ACLs, either dummy ACLs or ACLs matching certain hosts or networks.
2.
At the end of the list configure a permit ip any any statement.
3.
Configure the ACL on the primary and secondary WAN interface.
4.
Send data traffic.
If a packet does not match any of the statements in the list, the packet should match the permit ip any any statement at the end of the list and be allowed to pass through. If the packet matches any statement in the last, appropriate action such as permit or deny should be taken, depending on what is configured in the ACL statement.
Passed
NTP in the Branch Router
NTP in the branch router
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure NTP in the branch to source the clock from an NTP server in the network. The NTP server could be local to the branch, or it could be located in either the headquarters or the service provider premises.
2.
Configure Message Digest 5 (MD5) authentication for NTP.
3.
Verify, using the show ntp status command.
NTP should be sourced from the NTP server after successful authentication.
Passed
Branch Router as a DHCP Server
Branch router as a DHCP server
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure a DHCP server on the branch router to provide IP addresses for DHCP clients such as IP Phones and PCs.
2.
Verify, using the show ip dhcp binding and show ip dhcp server statistics commands.
The DHCP server on the router should be able to provide IP addresses to the clients using DHCP.
Passed
IP SLA VoIP UDP Jitter Codec G.711 u-law (Branch to HQ)
IP SLA VoIP UDP Jitter Codec G.729A u-law (Branch to HQ)
IP SLA ICMP Echo (Branch to HQ)
IPsec Site-to-Site VPN Using DMVPN
Setup an IPsec site-to-site VPN between the branch router and the headend router, using DMVPN.
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure the headend router as a DMVPN hub and Next Hop Resolution Protocol (NHRP) server with multipoint GRE.
2.
Configure the branch router as a spoke with multipoint GRE.
3.
Configure ISAKMP policy preshared authentication with 3-DES encryption for the keys.
4.
Configure ISAKMP SA lifetime to be 3600.
5.
Configure transform set with 3-DES, ESP-SHA, DH Group 2 and preshared keys.
6.
Configure IPsec SA lifetime to be 86400.
7.
Configure tunnel protection for the DMVPN tunnel interface.
8.
Add the DMVPN tunnel interface network address to the IGP configuration.
9.
Verify IPsec connectivity, using the following show commands:
•
show crypto isakmp sa
•
show crypto ipsec sa
•
show crypto engine connections active
10.
Send a sweep ping from a host connected to the branch data VLAN to a host connected to the headquarters data VLAN.
11.
Verify whether the ping traffic gets encrypted; use the show crypto engine accelerator statistics command.
ISAKMP and IPsec sessions should be established.
The DMVPN tunnel line protocol should come up.
Routing tables at both the branch and headquarters routers should be updated.
Ping should be 100% successful.
Ping traffic should be encrypted.
Passed
IPsec Using GETVPN
Set up an IPsec VPN between the branch router and the headend router, using GETVPN
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Set up a GDOI key server for GETVPN in headquarters. The key server can be a Cisco 2900 series ISR platform.
2.
Configure the key server to send unicast rekeys.
3.
Configure the network segments associated with branch and headquarters LANs for encryption, using an ACL. Associate the ACL to the GDOI SA.
4.
Configure AES 256-bit encryption for IPsec.
5.
Configure a rekey timeout of 10800 seconds.
6.
Configure antireplay protection.
7.
Configure the branch routers and the headend routers as group members.
8.
Configure the GDOI crypto map on the primary WAN interface of the branch router and the headend router.
9.
Configure the TCP maximum segment size (MSS) to 1360 bytes on the router interfaces.
10.
Register the group members to the key server.
11.
Send a sweep ping from a host connected to the branch data VLAN to a host connected to the headquarters data VLAN.
12.
Verify whether the ping traffic gets encrypted; use the show crypto engine accelerator statistics command.
13.
Verify GETVPN, using the following show commands:
•
show crypto isakmp sa
•
show crypto ipsec sa
•
show crypto engine connections active
Group members should be registered to the key server.
The key server should successfully push the IPsec SA ACL and rekey the ACL to the group members.
The routing tables at both the branch and head quarters routers should be updated.
Ping should be 100% successful.
Ping traffic should be encrypted.
Passed
GETVPN Unicast Rekeying
GETVPN unicast rekeying
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Set up a GDOI key server for GETVPN in the headquarters. The key server can be a Cisco 2900 series ISR platform.
2.
Configure the key server to send unicast rekeys.
3.
Configure the network segments associated with the branch and headquarters LANs for encryption, using an ACL. Associate the ACL to the GDOI SA.
4.
Configure AES 256-bit encryption for IPsec.
5.
Configure a rekey timeout of 10800 seconds.
6.
Configure the branch router(s) and the headend router (s) as group members.
7.
Configure the GDOI crypto map on the primary WAN interface of the branch router and headend router.
8.
Register the group members to the key server.
9.
Verify rekeying functionality.
10.
Use the show crypto isakmp sa command to verify.
Group members should be registered to the key server.
The key server should be able to successfully push the ACL for unicast rekeying to the group members.
After the rekey time out, the key server should send new keys to the group members. For some time, both old keys and new keys should be present in group members. The new key should take over after a certain amount of time, usually within a minute.
Passed
GETVPN Multicast Rekeying
GETVPN multicast rekeying
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Set up a GDOI key server for GETVPN in the headquarters. The key server can be a Cisco 2900 series ISR platform.
2.
Configure the key server to send multicast rekeys, with unicast rekeys as a backup mechanism.
3.
Define an ACL for multicast rekeying in the key server, and use the 239.x.x.x multicast group for rekeying.
4.
Configure PIM sparse mode (PIM-SM) on the key server and all the group members.
5.
Configure the headend router as the rendezvous point (RP).
6.
Configure the network segments associated with the branch and headquarters LANs for encryption, using an ACL. Associate the ACL to the GDOI SA.
7.
Configure AES 256-bit encryption for IPsec.
8.
Configure a rekey timeout of 10800 seconds.
9.
Configure the branch router(s) and the headend router(s) as group members.
10.
Configure the GDOI crypto map on the primary WAN interface of the branch router and the headend router.
11.
Register the group members to the key server.
12.
Verify rekeying functionality.
13.
Use the show crypto isakmp sa command to verify.
Group members should be registered to the key server.
The key server should be able to successfully push the ACL for multicast rekeying to the group members.
Group members should register to the 239.x.x.x multicast group successfully.
After the rekey timeout, the key server should send new keys to the multicast group. For some time, both old keys and new keys should be present in group members, and the new key should take over after a certain amount of time, usually within a minute.
Passed
IPsec DMVPN with Prefragmentation
IPsec DMVPN with prefragmentation
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure IPsec VPN between the branch and headquarters with a tunnel MTU of 1000 bytes.
2.
Enable prefragmentation.
3.
Send voice and data traffic through the IPsec VPN tunnel.
The IPsec packets that are larger than 1000 bytes should be fragmented.
Passed
IPsec DMVPN and IGP
IPsec DMVPN and IGP
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Bring down the IPsec tunnel between the branch and the headquarters router.
2.
Verify whether the routing table is updated at both the branch and headquarters routers.
3.
After 3 minutes, bring up the IPsec tunnel between the branch and headquarters routers.
4.
Verify whether the routing table is updated at both the branch and headquarters routers.
When the IPsec tunnel goes down, the routing tables at both the branch and headquarters are updated. At the branch, the headquarters becomes unreachable, and the routes should be removed from the routing table. Similarly, at the headquarters, the branch becomes unreachable, and routes should be removed from the routing table.
When the tunnel comes back up, the routes at both the branch and headquarters should reappear.
Passed
IPsec DMVPN and IGP
IPsec DMVPN and IGP
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Bring down the IPsec tunnel between the branch and the headquarters router.
2.
Verify whether the routing table is updated at both the branch and headquarters routers.
3.
After 3 minutes, bring up the IPsec tunnel between the branch and headquarters routers.
4.
Verify whether the routing table is updated at both the branch and headquarters routers.
When the IPsec tunnel goes down, the routing tables at both the branch and headquarters are updated. At the branch, the headquarters becomes unreachable, and the routes should be removed from the routing table. Similarly, at the headquarters, the branch becomes unreachable, and routes should be removed from the routing table.
When the tunnel comes back up, the routes at both the branch and headquarters should reappear.
Passed
DMVPN Backup for MPLS Network (Branch to HQ)
DMVPN backup on medium branch using static floating route (Spoke-to-HQ)
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
On the medium branch Cisco 2951 router, configure the serial interface on the branch that connects to the Internet Cloud router for frame-relay.
2.
Configure the static route in the branch router to reach to HQ with higher administrative distance (for example, 240).
3.
Redistribute the static route into the IGP on the branch router.
4.
Make sure that the entire traffic flow is going through the MPLS network when the branch WAN is up and running.
5.
Shut down the WAN and verify that the IP traffic flows to HQ using the Internet Cloud.
Verify that you can reach HQ from the branch when the primary WAN is down.
Passed
DMVPN Backup for MPLS Network (Branch to Branch)
DMVPN backup on medium branch using static floating route (Spoke-to-Spoke)
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
On the medium branch Cisco 2951 router, configure the serial interface on the branch that connects to the Internet Cloud router for frame-relay.
2.
Configure the static route in the branch router to reach to HQ with higher administrative distance (for example, 240).
3.
Redistribute the static route into the IGP on the branch router.
4.
Make sure that the entire traffic is going through the MPLS network when the branch WAN is up and running.
5.
Shut down the WAN and verify that IP traffic flows to HQ through the Internet Cloud.
6.
Verify that from small branch running DMVPN that you can reach the medium branch when the WAN link is down.
7.
Check the DMVPN hub for the NHRP database for all the spoke addresses (registered branch address).
8.
Verify that a dynamic tunnel has been created between the medium branch and the small branch.
Verify that you can reach HQ and the small branch from the medium branch when the primary WAN is down.
Passed
DMVPN Backup for MPLS Metwork Using BFD (Branch to HQ)
DMVPN backup with BFD using EIGRP as IGP (Branch to HQ)
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure the primary WAN interface and secondary WAN interface on the branch router.
2.
Configure the secondary WAN interface as a Frame Relay interface that accesses the Internet.
3.
Configure DMVPN on the branch router.
4.
Configure the secondary WAN to be a higher cost route than the primary WAN so that primary WAN is always the preferred route.
5.
Configure BFD on the primary WAN interface of the branch router and the primary WAN interface of the head-end router with a BFD interval of 50 ms, min_rx of 50 ms, and a BFD multiplier of 5.
6.
Configure BFD on the secondary WAN interface.
7.
Enable BFD for all interfaces in the EIGRP routing process.
8.
Verify whether BFD is up and running by issuing show bfd neighbor command
9.
Send HTTP and voice traffic between the branch and HQ.
10.
Bring down the primary WAN interface by either disconnecting the cable or shutting down the link on the head-end side.
11.
After about three minutes, bring up the primary WAN interface.
Verify that, when the primary WAN fails, EIGRP reconvergence occurs within a second because of BFD.
Verify that all the traffic is routed through the secondary WAN interface.
Verify that voice and HTTP sessions are maintained during reconvergence.
Verify that, when the primary WAN comes up after three minutes, the traffic is routed over the primary WAN interface.
Passed
DMVPN Backup for MPLS Network Using BFD (Branch to Branch)
DMVPN backup with BFD using EIGRP as IGP (Branch to Branch)
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure the primary WAN interface and secondary WAN interface on the branch router.
2.
Configure the secondary WAN interface as a Frame Relay interface that assesses the Internet.
3.
Configure DMVPN on the branch router.
4.
Configure the secondary WAN to be a higher cost route than the primary WAN so that primary WAN is always the preferred route.
5.
Configure BFD on the primary WAN interface of the branch router and the primary WAN interface of the head-end router with BFD interval of 50 ms, min_rx of 50 ms, and a BFD multiplier of 5.
6.
Configure BFD on the secondary WAN interface.
7.
Enable BFD for all interfaces in the EIGRP routing process.
8.
Verify whether BFD is up and running by issuing show bfd neighbor command.
9.
Send HTTP and voice traffic between the branch and HQ.
10.
Bring down the primary WAN interface by either disconnecting the cable or shutting down the link on the head-end side.
11.
After about three minutes, bring up the primary WAN interface.
Verify that, when the primary WAN fails, EIGRP reconvergence occurs within a second because of BFD.
Verify that all the traffic is routed through the secondary WAN interface.
Verify that voice and HTTP sessions are maintained during reconvergence.
Verify that, when the primary WAN comes up after three minutes, the traffic is routed over the primary WAN interface.
Passed
DMVPN Backup for MPLS Network Using BFD IGP as OSPF (Branch to Branch)
DMVPN backup with BFD using OSPF as IGP (Branch to Branch)
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure the primary WAN interface and secondary WAN interface on the branch router.
2.
Configure the secondary WAN interface as a Frame Relay interface that assesses the Internet.
3.
Configure DMVPN on the branch router.
4.
Configure the secondary WAN to be a higher cost route than the primary WAN so that primary WAN is always the preferred route.
5.
Configure BFD on the primary WAN interface of the branch router and the primary WAN interface of the head-end router with BFD interval of 50 ms, min_rx of 50 ms, and a BFD multiplier of 5.
6.
Configure BFD on the secondary WAN interface.
7.
Enable BFD for all interfaces in the EIGRP routing process.
8.
Verify whether BFD is up and running by issuing show bfd neighbor command.
9.
Send HTTP and voice traffic between the branch and HQ.
10.
Bring down the primary WAN interface by either disconnecting the cable or shutting down the link on the head-end side.
11.
After about three minutes, bring up the primary WAN interface.
Verify that, when the primary WAN fails, EIGRP reconvergence occurs within a second because of BFD.
Verify that all the traffic is routed through the secondary WAN interface.
Verify that voice and HTTP sessions are maintained during reconvergence.
Verify that, when the primary WAN comes up after three minutes, the traffic is routed over the primary WAN interface.
Passed
DMVPN Backup for MPLS Network Using EBGP (Branch to HQ)
DMVPN backup for MPLS using EBGP
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure the primary WAN interface and backup WAN interface on the branch router.
2.
Configure the secondary WAN interface as a Frame Relay interface that assesses the Internet.
3.
Configure DMVPN on the branch router.
4.
Configure EBGP peers with the Internet router on the branch router. Under normal conditions, when the primary WAN is up and running, the backup DMVPN is dormant.
5.
Shut down the primary WAN interface. The backup interface should come up and the EBGP peers become activated. Finally, the DMVPN should come up.
6.
Send 2 Mb/s of traffic from the backup interface (DMVPN is up) and check the QoS status and various queues.
7.
Send HTTP and Voice traffic between the branch and HQ
8.
After about three minutes, bring up the primary WAN interface
Verify that, when the primary WAN fails, the backup DMVPN comes up.
Verify that voice and HTTP sessions pass through.
Check for appropriate QoS Queues.
When the primary comes up after three minutes, verify that the traffic is routed over the primary WAN interface.
Passed
DMVPN with QoS
DMVPN with QoS
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure the 8-class QoS model as explained in the QoS test cases.
2.
Configure DMVPN with the qos pre-classify command to classify IPsec packets before encryption.
3.
Send voice and data traffic, and verify whether traffic going through the DMVPN tunnel gets the correct QoS treatment, such as voice put in strict priority queue with proper bandwidth percentages applied.
The IPsec packets should get the correct QoS treatment.
Passed
GETVPN with QoS
GETVPN with QoS
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure the 8-class QoS model as explained in the QoS test cases.
2.
Configure GETVPN with the qos pre-classify command to classify IPsec packets before encryption.
3.
Send voice traffic and data traffic, and verify whether traffic going through the GETVPN gets the correct QoS treatment, such as voice put in strict priority queue with proper bandwidth percentages applied.
The IPsec packets should get the correct QoS treatment.
Passed
DMVPN with QoS and NBAR
DMVPN with QoS and NBAR
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure the 8-class QoS model as explained in the QoS test cases.
2.
Configure NBAR with the custom ip nbar port-map and ip nbar protocol-discovery commands as in the NBAR test case.
3.
Configure DMVPN with the qos pre-classify command to classify IPsec packets before encryption.
4.
Send voice and data (HTTP, FTP, and ICMP) traffic, and verify whether traffic going through the DMVPN tunnel gets the correct NBAR and QoS treatment, such as voice put in the strict priority queue with the proper bandwidth percentages applied.
QoS and NBAR classification and bandwidth guarantees should be given to the voice and data traffic egressing the WAN interface before encryption.
Passed
GETVPN with QoS and NBAR
GETVPN with QoS and NBAR
Figure 1, Private WAN, Cisco Unified CME Mode or
Figure 2, Private WAN, Cisco Unified SRST Mode or
Figure 3, MPLS WAN, Cisco Unified CME Mode or
1.
Configure the 8-class QoS model as explained in the QoS test cases.
2.
Configure NBAR with the custom ip nbar port-map and ip nbar protocol-discovery commands as in the NBAR test case.
3.
Configure GETVPN with the qos pre-classify command to classify IPsec packets before encryption.
4.
Send voice and data (HTTP, FTP, and ICMP) traffic and verify whether traffic going through the IPsec tunnel gets the correct NBAR and QoS treatment, such as voice put in the strict priority queue with the proper bandwidth percentages applied.
QoS and NBAR classification and bandwidth guarantees should be given to the voice and data traffic egressing the WAN interface before encryption.
Passed
DMVPN/GETVPN with QoS, NBAR, and NetFlow
DMVPN/GETVPN with QoS, NBAR and NetFlow
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure the 8-class QoS model as explained in the QoS test cases.
2.
Configure NBAR with custom ip nbar port-map and ip nbar protocol-discovery commands as in the NBAR test case.
3.
Configure NetFlow version 5 or version 9 for both ingress and egress traffic on the WAN and LAN interfaces of the branch router.
4.
Configure IPsec with the qos pre-classify command to classify IPsec packets before encryption.
5.
Send voice and data (HTTP, FTP, and ICMP) traffic, and verify whether traffic going through the IPsec tunnel gets the correct NBAR and QoS treatment, such as voice put in the strict priority queue with the proper bandwidth percentages applied.
6.
Collect protocol distribution charts, interface statistics, and QoS statistics. Export the statistics to a NAM at the enterprise headquarters.
QoS and NBAR classification and bandwidth guarantees should be given to the voice and data traffic egressing the WAN interface before encryption
NetFlow should collect the statistics and export them to the NAM, and the collected statistics should be within performance requirements.
Passed
Zone-based Policy Firewall Configuration on the Branch Router
NAT and PAT Configuration on the Branch Router
Configure NAT and PAT for traffic going out to the Internet
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure static NAT translations for certain hosts on the data VLAN, using an address pool.
2.
For the rest of the hosts, configure PAT by using the overload command in the NAT configuration.
3.
Configure the secondary WAN interface as the interface connecting to the Internet through the ISP.
4.
Configure the LAN as NAT inside, and configure the secondary WAN interface as NAT outside.
5.
Send HTTP, HTTPS, ICMP, DNS, and SSH traffic from clients on the LAN to the Internet.
6.
Verify translations and statistics using the show ip nat translations and show ip nat statistics commands.
The inside address should be translated to the outside global address when the traffic from the LAN is going out to the Internet. The return traffic from the Internet to the LAN should always be directed to the outside global address of the inside hosts.
Passed
NAT, QoS, and NetFlow on the Branch
Configure NAT and QoS on the branch
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure static NAT translations for certain hosts on the data VLAN using an address pool and for the rest of the hosts configure PAT by using the overload command in the NAT configuration.
2.
Configure the secondary WAN interface as the interface connecting to the Internet through the ISP.
3.
Configure 8-class H-QoS on the secondary WAN interface.
4.
Mark all the traffic going out to the Internet as best-effort traffic.
5.
Configure traffic shaping to 95% of the available WAN bandwidth.
6.
Configure NetFlow on the secondary WAN interface for ingress and egress traffic.
7.
Collect traffic statistics and distribution charts, and export the statistics to a NAM, using either v5 or v9 NetFlow.
8.
Send HTTP, HTTPS, ICMP, DNS and SSH traffic from clients on the LAN to the Internet.
9.
Verify translations and statistics, using the show ip nat translations and show ip nat statistics commands.
10.
Verify QoS, using the show policy-map interface command.
11.
Verify NetFlow, using the show ip flow command.
The inside address should be translated to the outside global address when the traffic from the LAN is going out to the Internet. The return traffic from the Internet to the LAN should always be directed to the outside global address of the inside hosts.
All the Internet traffic should be marked as best effort.
Traffic should be shaped to 95% of the WAN bandwidth.
The NetFlow statistics collected should be within performance requirements.
Passed
ZPF, QoS, and NetFlow on the Branch
Configure ZPF, QoS, and NetFlow on the branch router
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure ZPF as explained in the Zone-based Policy Firewall Configuration on the Branch Router test case procedure.
2.
Configure the secondary WAN interface as the interface connecting to the Internet through the ISP.
3.
Assign the primary WAN interface to the Private zone.
4.
Assign the secondary WAN interface to the Public zone.
5.
Assign the voice VLAN and data VLAN interfaces to the Private zone.
6.
Configure 8-class hierarchical QoS on both the primary and secondary WAN interfaces.
7.
Mark all the traffic going out to the Internet as best-effort traffic.
8.
Configure traffic shaping to 95% of the available WAN bandwidth.
9.
Configure NetFlow on the WAN and LAN interfaces for ingress and egress traffic.
10.
Collect traffic statistics and distribution charts, and export the statistics to a NAM, using NetFlow version 5 or version 9.
11.
Send HTTP, HTTPS, ICMP, DNS, and SSH traffic from clients on the LAN to the Internet.
12.
Send bidirectional HTTP, HTTPS, and FTP traffic between the branch and headquarters.
13.
Ping one of the clients on the LAN from the ISP.
14.
Verify translations and statistics, using the show ip nat translations and show ip nat statistics command.
15.
Verify QoS, using the show policy-map interface command.
16.
Verify NetFlow, using the show ip flow command.
Traffic from the branch to headquarters should not be inspected.
Traffic from the branch to the Internet should be inspected.
QoS should be applied to the traffic, and ZPF should have no adverse effect on the QoS.
All the Internet traffic should be marked as best effort.
Traffic should be shaped to 95% of the WAN bandwidth.
The NetFlow statistics collected should be within performance requirements.
The ping should fail.
Passed
ZPF, QoS, NBAR, and NetFlow on the Branch
Configure ZPF, QoS, NBAR, and NetFlow on the branch router
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure ZPF as explained in the Zone-based Policy Firewall Configuration on the Branch Router test case procedure.
2.
Configure the secondary WAN interface as the interface connecting to the Internet through the ISP.
3.
Assign the primary WAN interface to the Private zone.
4.
Assign the secondary WAN interface to the Public zone.
5.
Assign the voice VLAN and data VLAN interfaces to the Private zone.
6.
Configure 8-class hierarchical QoS on both primary and secondary WAN interfaces.
7.
Mark all the traffic going out to the Internet as best-effort traffic.
8.
Configure traffic shaping to 95% of the available WAN bandwidth.
9.
Configure NBAR as in the NBAR Classification with QoS test case.
10.
Configure NetFlow on the WAN and LAN interfaces for ingress and egress traffic.
11.
Collect traffic statistics and distribution charts, and export the statistics to a NAM, using NetFlow version 5 or version 9.
12.
Send HTTP, HTTPS, ICMP, DNS, and SSH traffic from clients on the LAN to the Internet.
13.
Send bidirectional HTTP, HTTPS, and FTP traffic between the branch and headquarters.
14.
Ping one of the clients on the LAN from the ISP.
15.
Verify translations and statistics using the show ip nat translations and show ip nat statistics commands.
16.
Verify QoS, using the show policy-map interface command.
17.
Verify NetFlow, using the show ip flow command.
Traffic from the branch to headquarters should not be inspected.
Traffic from the branch to the Internet should be inspected.
QoS should be applied to the traffic, and ZPF should have no adverse effect on the QoS.
All the Internet traffic should be marked as best effort.
Traffic should be shaped to 95% of the WAN bandwidth.
NBAR should provide bandwidth guarantees to different flows and should detect and stop worms such as NIMDA and CODE RED.
The NetFlow statistics collected should be within performance requirements.
The ping should fail.
Passed
ZPF, QoS, NBAR, NAT, and NetFlow on the Branch
Configure ZPF, QoS, NBAR, and NetFlow on the branch router
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure ZPF as explained in the Zone-based Policy Firewall Configuration on the Branch Router test case procedure.
2.
Configure the secondary WAN interface as the interface connecting to the Internet through the ISP.
3.
Assign the primary WAN interface to the Private zone.
4.
Assign the secondary WAN interface to the Public zone.
5.
Assign the voice VLAN and data VLAN interfaces to the Private zone.
6.
Configure static NAT translations for certain hosts on the data VLAN using an address pool. For the rest of the hosts, configure PAT by using the overload keyword in the ip nat inside source command in the NAT configuration.
7.
Configure the data VLAN as NAT inside, and configure the secondary WAN interface as NAT outside.
8.
Configure 8-class hierarchical QoS on both primary and secondary WAN interfaces.
9.
Mark all the traffic going out to the Internet as best-effort traffic.
10.
Configure traffic shaping to 95% of the available WAN bandwidth.
11.
Configure NBAR as in the NBAR Classification with QoS test case.
12.
Configure NetFlow on the WAN and LAN interfaces for ingress and egress traffic.
13.
Collect traffic statistics and distribution charts, and export the statistics to a NAM, using NetFlow version 5 or version 9.
14.
Send HTTP, HTTPS, ICMP, DNS, and SSH traffic from clients on the LAN to the Internet.
15.
Send bidirectional HTTP, HTTPS, and FTP traffic between the branch and headquarters.
16.
Ping one of the clients on the LAN from the ISP.
17.
Verify translations and statistics, using the show ip nat translations and show ip nat statistics commands.
18.
Verify QoS, using the show policy-map interface command.
19.
Verify NetFlow, using the show ip flow command.
Traffic from the branch to headquarters should not be inspected.
Traffic from the branch to the Internet should be inspected.
Inside addresses should be translated to outside global addresses when the traffic from the LAN is going out to the Internet. The return traffic from the Internet to the LAN should always be directed to the outside global address of the inside hosts.
QoS should be applied to the traffic, and ZPF should not have any adverse effect on the QoS.
All the Internet traffic should be marked as best effort.
Traffic should be shaped to 95% of the WAN bandwidth.
NBAR should provide bandwidth guarantees to different flows and should detect and stop worms such as NIMDA and CODE RED.
The NetFlow statistics collected should be within performance requirements.
The ping should fail.
Passed
ZPF with DMVPN
Configure ZPF with DMVPN on the primary WAN interface connecting the branch and headquarters
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure ZPF as explained in the Zone-based Policy Firewall Configuration on the Branch Router test case procedure.
2.
Configure the secondary WAN interface as the interface connecting to the Internet through the ISP.
3.
Assign the primary WAN interface to the Private zone.
4.
Assign the DMVPN tunnel interface over the primary WAN to the Private zone.
5.
Assign the voice VLAN and data VLAN interfaces to the Private zone.
6.
Assign the secondary WAN interface to the Public zone.
7.
Configure firewall policy for the Private zone to the Public zone, the Private zone to the DMZ zone, and the Public zone to the DMZ zone.
8.
Send bidirectional HTTP, HTTPS, and FTP traffic between the branch and headquarters.
ZPF should have no adverse impact on DMVPN.
Traffic between the branch and headquarters over the primary WAN interface should be encrypted.
Passed
ZPF with GETVPN
Configure ZPF with GETVPN connecting the branch and headquarters
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure ZPF as explained in the Zone-based Policy Firewall Configuration on the Branch Router test case procedure.
2.
Assign the primary WAN interface to the Public zone.
3.
Assign the voice VLAN and data VLAN interfaces to the Private zone.
4.
Configure GETVPN as in the IPsec Using GETVPN test case procedure.
5.
Send bidirectional HTTP, HTTPS, and FTP traffic between the branch and headquarters.
Traffic between the branch and headquarters should be encrypted.
ZPF should have no effect on the traffic between the branch and headquarters.
Passed
IPsec, ZPF, QoS, NBAR, NAT, and NetFlow on the Branch
Configure ZPF, QoS, NBAR, and NetFlow on the branch router
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure IPsec VPN, using either DMVPN or GETVPN on the primary WAN interface.
2.
Configure ZPF as explained in the Zone-based Policy Firewall Configuration on the Branch Router test case procedure.
3.
Configure the secondary WAN interface as the interface connecting to the Internet through the ISP.
4.
Assign the primary WAN interface to the Private zone.
5.
Assign the secondary WAN interface to the Public zone.
6.
Assign the voice VLAN and data VLAN interfaces to the Private zone.
7.
Configure static NAT translations for certain hosts on the data VLAN, using an address pool. For the rest of the hosts, configure PAT by using the overload command in the NAT configuration.
8.
Configure the data VLAN as NAT inside, and configure the secondary WAN interface as NAT outside.
9.
Configure 8-class hierarchical QoS on both the primary and secondary WAN interfaces.
10.
Mark all the traffic going out to the Internet as best-effort traffic.
11.
Configure traffic shaping to 95% of the available WAN bandwidth.
12.
Configure NBAR as in the NBAR Classification with QoS test case.
13.
Configure NetFlow on the WAN and LAN interfaces for ingress and egress traffic.
14.
Collect traffic statistics and distribution charts, and export the statistics to a NAM using NetFlow version 5 or version 9.
15.
Send HTTP, HTTPS, ICMP, DNS, and SSH traffic from clients on the LAN to the Internet.
16.
Send bidirectional HTTP, HTTPS, and FTP traffic between the branch and headquarters.
17.
Ping one of the clients on the LAN from the ISP.
18.
Verify translations and statistics, using the show ip nat translations and show ip nat statistics commands.
19.
Verify QoS, using the show policy-map interface command.
20.
Verify NetFlow, using the show ip flow command.
Traffic from the branch to headquarters should be encrypted.
Traffic from the branch to headquarters should not be inspected.
Traffic from the branch to the Internet should be inspected.
Inside addresses should be translated to outside global addresses when the traffic from the LAN is going out to the Internet. The return traffic from the Internet to the LAN should always be directed to the outside global address of the inside hosts.
QoS should be applied to the traffic, and ZPF should not have any adverse effect on the QoS.
All the Internet traffic should be marked as best-effort.
Traffic should be shaped to 95% of the WAN bandwidth.
NBAR should provide bandwidth guarantees to different flows and should detect and stop worms such as NIMDA and CODE RED.
The NetFlow statistics collected should be within performance requirements.
The ping should fail.
Passed
DDOS Prevention Using Cisco IOS IPS
Configure Cisco IOS IPS with IDCONF v5.0 in the branch router to prevent denial-of-service attacks
1.
Download the latest IPS signature pack from: http://www.cisco.com/cgi-bin/tablebuild.pl/ios-v5sigup to the router flash.
2.
Configure Cisco IOS IPS with IDCONF v5.0 on the router.
3.
Enable the advanced category signature set.
4.
Configure Cisco IOS IPS for both directions of traffic on the data VLAN and WAN interfaces.
5.
Enable syslog on the router and log the syslog messages to a syslog server located in the branch.
6.
Launch DDOS attacks from a PC attached to the branch router data VLAN to a server at the headquarters.
7.
Verify whether the attacks are detected by Cisco IOS IPS and whether the alert messages are logged to the syslog server.
The attacks should be detected by Cisco IOS IPS, and appropriate signatures should be triggered.
Actions such as warning, dropping the packets, or dropping the session should be taken based on a particular signature configuration.
The alert messages related to the attack should be logged to a syslog server.
Passed
Cisco IOS IPS with Background Data Traffic
Configure Cisco IOS IPS with IDCONF v5.0 in the branch router to prevent denial-of-service attacks
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Download the latest IPS signature pack from: http://www.cisco.com/cgi-bin/tablebuild.pl/ios-v5sigup to the router flash.
2.
Configure Cisco IOS IPS with IDCONF v5.0 on the router.
3.
Enable advanced category signature set.
4.
Configure Cisco IOS IPS for both directions of traffic on the data VLAN and WAN interfaces.
5.
Enable syslog on the router, and log the syslog messages to a syslog server located in the branch.
6.
Send HTTP, HTTPS, and FTP traffic between the branch and headquarters.
7.
Launch DDOS attacks from a PC attached to the branch router data VLAN to a server at the headquarters.
8.
Verify whether the attacks are detected by Cisco IOS IPS and whether the alert messages, logged to the syslog server.
The attacks should be detected by Cisco IOS IPS, and appropriate signatures should be triggered.
Actions such as warning, dropping the packets, or dropping the session should be taken based on a particular signature configuration.
The alert messages related to the attack should be logged to a syslog server.
Passed
ZPF with NAT and Cisco IOS IPS
Configure ZPF with NAT and Cisco IOS IPS on the branch router
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure ZPF as explained in the Zone-based Policy Firewall Configuration on the Branch Router test case procedure
2.
Configure the secondary WAN interface as the interface connecting to the Internet through the ISP.
3.
Assign the primary WAN interface to the Private zone.
4.
Assign the secondary WAN interface to the Public zone.
5.
Assign the voice VLAN and data VLAN interfaces to the Private zone.
6.
Configure static NAT translations for certain hosts on the data VLAN, using an address pool. For the rest of the hosts, configure PAT by using the overload command in the NAT configuration.
7.
Configure the data VLAN as NAT inside, and configure the secondary WAN interface as NAT outside.
8.
Download the latest Cisco IOS IPS signature pack from: http://www.cisco.com/cgi-bin/tablebuild.pl/ios-v5sigup to the router flash.
9.
Configure Cisco IOS IPS with IDCONF v5.0 on the router.
10.
Enable advanced category signature set.
11.
Configure Cisco IOS IPS for both directions of traffic on the data and DMZ VLAN and WAN interfaces.
12.
Enable syslog on the router, and log the syslog messages to a syslog server located at the branch.
13.
Send HTTP, HTTPS, and FTP traffic between the branch and headquarters.
14.
Send HTTP, FTP, and DNS traffic between the branch and the Internet.
15.
Launch DDOS attacks from a PC attached to the branch router data VLAN to a server located at the headquarters.
16.
Launch threats from a host in the Internet to the DMZ servers.
17.
Verify whether the attacks are detected by Cisco IOS IPS and whether the alert messages are logged to the syslog server.
Traffic from the branch to headquarters should not be inspected.
Traffic from the branch to Internet should be inspected.
Inside addresses should be translated to outside global addresses when the traffic from the LAN is going out to the Internet. The return traffic from the Internet to the LAN should always be directed to the outside global address of the inside hosts.
The attacks should be detected by Cisco IOS IPS, and appropriate signatures should be triggered.
Actions such as warning, dropping the packets or dropping the session, or blocking the host should be taken based on a particular signature configuration.
The alert messages related to the attack should be logged to a syslog server.
Passed
IPsec, ZPF, QoS, NBAR, NAT, Cisco IOS IPS, and NetFlow on the Branch
Configure ZPF, QoS, NBAR, NAT, Cisco IOS IPS, and NetFlow on the branch router
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure IPsec VPN using either DMVPN or GETVPN on the primary WAN interface.
2.
Configure ZPF as explained in the Zone-based Policy Firewall Configuration on the Branch Router test case procedure.
3.
Configure the secondary WAN interface as the interface connecting to the Internet through the ISP.
4.
Assign the primary WAN interface to the Private zone.
5.
Assign the secondary WAN interface to the Public zone.
6.
Assign the voice VLAN and data VLAN interfaces to the Private zone.
7.
Configure static NAT translations for certain hosts on the data VLAN, using an address pool. For the rest of the hosts, configure PAT by using the overload command in the NAT configuration.
8.
Configure the data VLAN as NAT inside, and configure the secondary WAN interface as NAT outside.
9.
Configure Cisco IOS IPS with IDCONF v5.0 on the router.
10.
Enable advanced category signature set.
11.
Configure Cisco IOS IPS for both directions of traffic on the data and DMZ VLAN and WAN interfaces.
12.
Enable syslog on the router and log the syslog messages to a syslog server at the branch.
13.
Configure 8-class hierarchical QoS on both primary and secondary WAN interfaces.
14.
Mark all the traffic going out to the Internet as best-effort traffic.
15.
Configure traffic shaping to 95% of the available WAN bandwidth.
16.
Configure NBAR as in the NBAR Classification with QoS test case.
17.
Configure NetFlow on the WAN and LAN interfaces for ingress and egress traffic.
18.
Collect traffic statistics and distribution charts, and export the statistics to a NAM, using NetFlow version 5 or version 9.
19.
Send HTTP, HTTPS, ICMP, DNS, and SSH traffic from clients on the LAN to the Internet.
20.
Send bidirectional HTTP, HTTPS, and FTP traffic between the branch and headquarters.
21.
Ping one of the clients on the LAN from the ISP.
22.
Launch DDOS attacks from a PC attached the branch router data VLAN to a server located at the headquarters.
23.
Launch threats from a host in the Internet to the DMZ servers.
24.
Verify translations and statistics, using the show ip nat translations and show ip nat statistics commands.
25.
Verify whether the attacks are detected by Cisco IOS IPS and whether the alert messages are logged to the syslog server.
26.
Verify QoS, using the show policy-map interface command.
27.
Verify NetFlow, using show ip flow command.
All traffic should be Cisco Express Forwarding switched.
Traffic from the branch to headquarters should be encrypted.
Traffic from the branch to headquarters should not be inspected.
Traffic from the branch to the Internet should be inspected.
Inside addresses should be translated to the outside global address when the traffic from the LAN is going out to the Internet. The return traffic from the Internet to the LAN should always be directed to the outside global address of the inside hosts.
QoS should be applied to the traffic, and ZPF should not have any adverse effect on the QoS.
All the Internet traffic should be marked as best-effort.
Traffic should be shaped to 95% of the WAN bandwidth.
The attacks should be detected by Cisco IOS IPS, and appropriate signatures should be triggered.
Actions such as warning, dropping the packets or dropping the session, blocking host should be taken based on a particular signature configuration.
The alert messages related to the attack should be logged to a syslog server.
NBAR should provide bandwidth guarantees to different flows and should detect and stop worms such as NIMDA and CODE RED.
NetFlow statistics collected should be within performance requirements.
The ping should fail.
Passed
Remote Users Using WebVPN (SSL VPN)
Remote Users Using WebVPN (SSL VPN) Full Tunnel
Complete Baseline Test
Enable all the baseline services in the branch and headend routers. The baseline features include BGP routing, OSPF/EIGRP routing, IPsec using DMVPN or GETVPN, ZPF, NAT, IPS, QoS, NBAR, ACL, NetFlow, DHCP, AAA RADIUS server, NTP, syslog, SNMP, WebVPN, PIM-v2, and IGMP v2.
Configure L2 and L3 switching on the access and distribution layer switches.
Enable QoS on the L3 distribution switches.
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure L2 switching with RSTP on the Catalyst 3560 switches. Verify, using the show spanning tree command.
2.
Configure L3 switching on the Catalyst 3750 switches with VTP trunking. Configure voice, data, and DMZ VLANs.
3.
Configure Catalyst QoS on the Catalyst 3750 switch.
4.
Configure BGP routing. Verify whether the default route is injected into the branch router, using the show ip route and show ip bgp summary commands.
5.
Configure OSPF/EIGRP routing as the IGP. Verify the neighbor relationship between headquarters and branch routers, using the show ip ospf neighbors or show ip eigrp neighbors command. Verify the routes using the show ip route command.
6.
Configure IPsec (DMVPN/GETVPN) over the primary and secondary WAN interfaces. Verify, using the show crypto engine connections active and show crypto session commands.
7.
Configure ZPF with voice VLAN, data VLAN, and primary WAN in the Private zone, DMZ VLAN in the DMZ zone, secondary WAN in the Public zone, and IPsec tunnel in the VPN zone. Verify, using the show policy-map type inspect command.
8.
Configure the 8-class QoS model with the qos pre-classify command. Verify, using the show policy-map interface command.
9.
Configure NBAR to provide bandwidth guarantees to different protocols such as HTTP, HTTPS, FTP, DNS, SSH, and ICMP. Verify, using the show ip nbar protocol-discovery command.
10.
Configure NAT to translate the addresses of hosts in the data VLAN when accessing the Internet through the secondary WAN interface. Verify, using the show ip nat translations command.
11.
Configure IPS to prevent DDOS attacks, slackware, malware, worms, and so on, against the branch/headquarters clients and servers. Send alert messages to a syslog server.
12.
Configure NetFlow on all the interfaces, and export the statistics to a NAM in headquarters. Verify NetFlow statistics, using the show ip flow command.
13.
Configure NTP in the branch router, and authenticate the NTP server using MD5 authentication. Verify, using the show ntp status command.
14.
Configure the DHCP server on the branch router to provide dynamic IP addresses to clients in the voice, data, and DMZ VLANs. Verify, using the show ip dhcp bindings command.
15.
Configure AAA to authenticate and authorize users using a RADIUS server located in the headquarters.
16.
Configure SNMP to collect traps.
17.
Configure WebVPN in clientless mode, and have at least five remote users access the branch web-based applications and Windows File Sharing from the Internet.
18.
Configure an IPTV server in the headquarters to stream 300 kb/s video using multicast. Set up the headquarters router as an RP, and configure PIM-SM on branch and headend routers.
19.
Send HTTP, HTTPS, DNS, SSH, ICMP, and CIFS traffic between the branch and headquarters.
20.
Send HTTP, FTP, DNS, and SSH traffic between the branch and the Internet.
21.
Send HTTP traffic between the Internet and the DMZ.
22.
Join four clients to the multicast group to receive IPTV video streams.
23.
Launch threats from hosts on the branch LAN to servers on the headquarters.
All traffic should be Cisco Express Forwarding switched.
The Catalyst switch should properly mark the traffic and put it in appropriate queues.
Traffic from the branch to headquarters should be encrypted.
Traffic from the branch to headquarters should not be inspected.
Traffic from the branch to the Internet should be inspected.
Inside addresses should be translated to outside global addresses when the traffic from the LAN is going out to the Internet. The return traffic from the Internet to the LAN should always be directed to the outside global address of the inside hosts.
QoS should be applied to the traffic, and ZPF should not have any adverse effect on the QoS.
All Internet traffic should be marked as best effort.
Traffic should be shaped to 95% of the WAN bandwidth.
The attacks should be detected by Cisco IOS IPS, and appropriate signatures should be triggered.
Actions such as warning, dropping the packets or dropping the session, or blocking the host should be taken based on a particular signature configuration.
The alert messages related to the attack should be logged to a syslog server.
NBAR should provide bandwidth guarantees to different flows and should detect and stop worms such as NIMDA and CODE RED.
Remote users should be able to access the branch intranet web-based applications and shared Windows network drives. The WebVPN traffic should be accelerated.
The NetFlow statistics should be collected and exported, and they should be within performance requirements.
The router should be able to source the clock from the NTP server after successful authentication.
The DHCP server on the router should provide IP addresses to the clients on the LAN.
AAA should be able to authenticate users using a RADIUS server.
Passed
High Availability Test Cases
EtherChannel Uplink from Access Layer Switch
Set up a cross-stack EtherChannel connection between access layer switch(es) and distribution layer switch(es)
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Bundle two Gigabit Ethernet uplinks on the Catalyst 3560 switches into an LACP EtherChannel, and connect each of the ports to different distribution switches, which are stacked together as shown in the test setup.
2.
Send LAN traffic between the access and distribution switches.
3.
Bring down one of the links in the EtherChannel bundle; after about 30 seconds, bring up the link again.
The two Gigabit Ethernet bundle EtherChannel link should behave as one 2-Gigabit Ethernet link. The LAN traffic between the access and distribution switches should be load balanced between the two Gigabit Ethernet links in the EtherChannel. When one of the Gigabit Ethernet links goes down, the EtherChannel should stay up, and there should be no impact on the LAN traffic. All the traffic should now be carried by just one Gigabit Ethernet link. When the other Gigabit Ethernet link comes up, load balancing should resume.
Passed
EIGRP Subsecond Convergence During Primary WAN Failure
Enable BFD for EIGRP subsecond convergence during primary WAN failure
Figure 1, Private WAN, Cisco Unified CME Mode or
Figure 2, Private WAN, Cisco Unified SRST Mode or
Figure 3, MPLS WAN, Cisco Unified CME Mode or
1.
Set up a primary WAN interface and a secondary WAN interface on the branch router.
2.
Set up a secondary WAN interface to be an SHDSL IMA interface.
3.
Configure the secondary WAN to be a higher cost route than the primary WAN so that the primary WAN is always preferred.
4.
Configure BFD on the primary WAN interface of the branch router. Configure the primary WAN interface of the headend router with a BFD interval of 50 ms, a min_rx of 50 ms, and a BFD multiplier of 5.
5.
Configure BFD on the secondary WAN interface.
6.
Enable BFD for all interfaces in the EIGRP routing process.
7.
Verify whether BFD is up by entering the show bfd neighbor command.
8.
Send HTTP and voice traffic between the branch and headquarters.
9.
Bring down the primary WAN interface by either pulling out the cable or shutting down the link on the headend side.
10.
After about 3 minutes, bring up the primary WAN interface.
When the primary WAN fails, EIGRP reconvergence should occur within a second because of BFD, and all the traffic should be routed through the secondary WAN interface.
Voice and HTTP sessions should be maintained during reconvergence.
When the primary WAN comes up after 3 minutes, the traffic should be routed over the primary WAN interface.
Passed on Gigabit Ethernet interfaces.
BFD is supported only on Gigabit Ethernet interfaces. Support for additional WAN encapsulations such as Frame Relay and PPP is planned for future releases.
OSPF Subsecond Convergence During Primary WAN Failure
Enable BFD for OSPF subsecond convergence during primary WAN failure
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Set up a primary WAN interface and a secondary WAN interface on the branch router.
2.
Set up a secondary WAN interface to be an SHDSL IMA interface.
3.
Configure the secondary WAN to be a higher cost route than the primary WAN, using the OSPF ip ospf cost command, so that the primary WAN is always preferred.
4.
Configure BFD on the primary WAN interface of the branch router and the primary WAN interface of the headend router with a BFD interval of 50 ms, a min_rx of 50 ms, and a BFD multiplier of 5.
5.
Configure BFD on the secondary WAN interface.
6.
Enable BFD for all interfaces in the OSPF routing process.
7.
Verify whether BFD is up by entering the show bfd neighbor command.
8.
Send HTTP and voice traffic between the branch and headquarters.
9.
Bring down the primary WAN interface by either pulling out the cable or shutting down the link on the headend side.
10.
After about 3 minutes bring up the primary WAN interface.
When the primary WAN fails, OSPF reconvergence should occur within a second because of BFD, and all the traffic should be routed through the secondary WAN interface.
Voice and HTTP sessions should be maintained during reconvergence.
When the primary WAN comes up after 3 minutes, the traffic should be routed over the primary WAN interface.
Passed on Gigabit Ethernet interfaces
BFD is supported only on Gigabit Ethernet interfaces. Support for additional WAN encapsulations such as Frame Relay and PPP is planned for future releases.
IPsec over Backup SHDSL WAN Link
Encryption over backup link between the branch and headquarters
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Set up a primary WAN interface and a secondary WAN interface on the branch router.
2.
Set up the secondary WAN interface to be an SHDSL IMA interface.
3.
Configure the secondary WAN to be a higher cost route than the primary WAN, using the OSPF ip ospf cost command, so that the primary WAN is always preferred.
4.
Configure BFD on the primary WAN interface of the branch router and the primary WAN interface of the headend router with a BFD interval of 50 ms, a min_rx of 50 ms, and a BFD multiplier of 5.
5.
Configure BFD on the secondary WAN interface.
6.
Enable BFD for all interfaces in the OSPF routing process.
7.
Verify whether BFD is up by entering the show bfd neighbor command.
8.
Configure one of the IPsec types, that is, IPsec DMVPN or GETVPN, on both the primary and secondary WAN interfaces between the branch and headquarters.
9.
Send HTTP, FTP, and ICMP traffic between the branch and headquarters.
10.
Bring down the primary WAN interface by either pulling out the cable or shutting down the link on the headend side.
11.
After about 3 minutes bring up the primary WAN interface.
When the primary WAN fails, OSPF reconvergence should occur within a second because of BFD.
All the traffic should be sent through the IPsec tunnel over the secondary WAN interface.
HTTP, FTP, and ICMP sessions should be maintained during the switchover and switchback.
When the primary WAN comes up after 3 minutes, the traffic should be routed over the primary WAN interface IPsec tunnel.
No router tracebacks, memory leaks, or crashes should be observed.
All the traffic should be Cisco Express Forwarding switched.
Passed on Gigabit Ethernet interfaces.
BFD is supported only on Gigabit Ethernet interfaces. Support for additional WAN encapsulations such as Frame Relay and PPP is planned for future releases.
ZPF, NAT, and IPsec over Backup SHDSL WAN Link
ZPF, NAT, and IPsec over backup SHDSL WAN link
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Set up a primary WAN interface and a secondary WAN interface on the branch router.
2.
Set up a secondary WAN interface to be an SHDSL IMA interface.
3.
Configure the secondary WAN to be a higher cost route than the primary WAN, using the OSPF ip ospf cost command, so that the primary WAN is always preferred.
4.
Configure BFD on the primary WAN interface of the branch router and the primary WAN interface of the headend router with a BFD interval of 50 ms, a min_rx of 50 ms, and a BFD multiplier of 5.
5.
Configure BFD on the secondary WAN interface.
6.
Enable BFD for all interfaces in the OSPF routing process.
7.
Verify whether BFD is up by entering the show bfd neighbor command.
8.
Configure one of the IPsec types, that is, IPsec DMVPN or GETVPN, on both the primary and secondary WAN interfaces between the branch and headquarters.
9.
Configure ZPF as explained in the Zone-based Policy Firewall Configuration on the Branch Router test case procedure.
10.
Configure the secondary WAN interface as the interface connecting to the Internet through the ISP.
11.
Assign the primary WAN interface to the Private zone.
12.
Assign the secondary WAN interface to the Public zone.
13.
Assign the voice VLAN and data VLAN interfaces to the Private zone.
14.
If you are using DMVPN, assign the tunnel interface to the VPN zone.
15.
Define a firewall policy between the VPN zone and the Public zone.
16.
Define a firewall policy between the VPN zone and the Private zone.
17.
Configure static NAT translations for certain hosts on the data VLAN using an address pool. For the rest of the hosts, configure PAT by using the overload command in the NAT configuration.
18.
Configure the data VLAN as NAT inside, and configure the secondary WAN interface as NAT outside.
19.
Send HTTP, FTP, and ICMP traffic between the branch and headquarters.
20.
Send HTTP, FTP, DNS, and ICMP traffic between PCs on the branch data VLAN to the Internet.
21.
Verify translations and statistics, using the show ip nat translations and show ip nat statistics commands.
22.
Bring down the primary WAN interface by either pulling the cable out or shutting down the link on the headend side.
23.
After about 3 minutes bring up the primary WAN interface.
When the primary WAN fails, OSPF reconvergence should occur within a second because of BFD.
ZPF should inspect all traffic going out of the secondary WAN interface.
All the traffic between the branch and headquarters should be sent through the IPsec tunnel over the secondary WAN interface.
Inside addresses should be translated to outside global addresses when the traffic from the LAN is going out to the Internet. The return traffic from the Internet to the LAN should always be directed to the outside global addresses of the inside hosts.
HTTP, FTP, and ICMP sessions should be maintained during the switchover and switchback.
When the primary comes up after 3 minutes, the traffic should be routed over the primary WAN interface IPsec tunnel.
No router tracebacks, memory leaks, or crashes should be observed.
All the traffic should be Cisco Express Forwarding switched.
Passed on Gigabit Ethernet interfaces.
BFD is supported only on Gigabit Ethernet interfaces. Support for additional WAN encapsulations such as Frame Relay and PPP is planned for future releases.
IPsec, ZPF, QoS, NBAR, and NefFlow on Both Primary and Secondary Link, and NAT on the Secondary Link
ZPF, NAT, and IPsec over backup SHDSL WAN link
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Set up a primary WAN interface and a secondary WAN interface on the branch router.
2.
Set up the secondary WAN interface to be an SHDSL IMA interface.
3.
Configure the secondary WAN to be a higher cost route than the primary WAN, using the OSPF ip ospf cost command, so that the primary WAN is always preferred.
4.
Configure BFD on the primary WAN interface of the branch router and the primary WAN interface of the headend router with a BFD interval of 50 ms, a min_rx of 50 ms and a BFD multiplier of 5.
5.
Configure BFD on the secondary WAN interface.
6.
Enable BFD for all interfaces in the OSPF routing process.
7.
Verify whether BFD is up by entering the show bfd neighbor command.
8.
Configure one of the IPsec types, that is, DMVPN or GETVPN, on both the primary and secondary WAN interfaces between the branch and headquarters.
9.
Configure ZPF as explained in the Zone-based Policy Firewall Configuration on the Branch Router test case procedure.
10.
Configure the secondary WAN interface as the interface connecting to the Internet through the ISP.
11.
Assign the primary WAN interface to the Private zone.
12.
Assign the secondary WAN interface to the Public zone.
13.
Assign the voice VLAN and data VLAN interfaces to the Private zone.
14.
If you are using DMVPN, assign the tunnel interface to the VPN zone.
15.
Define a firewall policy between the VPN zone and the Public zone.
16.
Define a firewall policy between the VPN zone and the Private zone.
17.
Configure static NAT translations for certain hosts on the data VLAN, using an address pool. For the rest of the hosts, configure PAT by using the overload command in the NAT configuration.
18.
Configure the data VLAN as NAT inside, and configure the secondary WAN interface as NAT outside.
19.
Configure Cisco IOS IPS with IDCONF v5.0 on the router.
20.
Enable advanced category signature set.
21.
Configure Cisco IOS IPS for both directions of traffic on the data and DMZ VLAN and WAN interfaces.
22.
Enable syslog on the router, and log the syslog messages to a syslog server located in the branch.
23.
Configure 8-class hierarchical QoS on both the primary and secondary WAN interfaces.
24.
Mark all the traffic going out to the Internet as best-effort traffic.
25.
Configure traffic shaping to 95% of the available WAN bandwidth.
26.
Configure NBAR as in the NBAR Classification with QoS test case.
(continued)27.
Configure NetFlow on the WAN and LAN interfaces for ingress and egress traffic.
28.
Collect traffic statistics and distribution charts, and export the statistics to a NAM, using NetFlow version 5 or version 9.
29.
Send HTTP, FTP, and ICMP traffic between the branch and headquarters.
30.
Send HTTP, FTP, DNS, and ICMP traffic between PCs on the branch, and configure NetFlow on the WAN and LAN interfaces for ingress and egress traffic.
31.
Verify translations and statistics, using the show ip nat translations and show ip nat statistics commands.
32.
Launch DDOS attacks from a PC attached to the branch router data VLAN to a server located in the headquarters.
33.
Launch threats from a host in the Internet to the DMZ servers.
34.
Verify translations and statistics, using the show ip nat translations and show ip nat statistics commands.
35.
Verify whether the attacks are detected by Cisco IOS IPS and the alert messages logged to the syslog server.
36.
Verify QoS, using the show policy-map interface command.
37.
Verify NetFlow, using the show ip flow command.
38.
Bring down the primary WAN interface by either pulling out the cable or shutting down the link on the headend side.
39.
After about 3 minutes bring up the primary WAN interface.
When the primary WAN fails, OSPF reconvergence should occur within a second because of BFD.
ZPF should inspect all traffic going out the secondary WAN interface.
All the traffic between the branch and headquarters should be sent through the IPsec tunnel over the secondary WAN interface.
Inside addresses should be translated to outside global addresses when the traffic from the LAN is going out to the Internet. The return traffic from the Internet to the LAN should always be directed to the outside global address of the inside hosts.
HTTP, FTP, and ICMP sessions should be maintained during the switchover and switchback.
QoS should be applied to the traffic, and ZPF should not have any adverse effect on the QoS.
All the Internet traffic should be marked as best effort.
Traffic should be shaped to 95% of the WAN bandwidth.
Since the secondary WAN link bandwidth is less than the primary WAN bandwidth, only conforming high-priority traffic, such as voice traffic or mission-critical traffic, should be carried over the secondary WAN link. The rest should be dropped.
The attacks should be detected by Cisco IOS IPS, and appropriate signatures should be triggered.
Actions such as warning, dropping the packets or dropping the session, or blocking the host should be taken based on a particular signature configuration.
The alert messages related to the attack should be logged to a syslog server.
NBAR should provide bandwidth guarantees to different flows and should detect and stop worms such as NIMDA and CODE RED.
NetFlow statistics collected should be within performance requirements.
When the primary comes up after 3 minutes, the traffic should be routed over the primary WAN interface IPsec tunnel.
No router tracebacks, memory leaks, or crashes should be observed.
All the traffic should be Cisco Express Forwarding switched.
Passed on Gigabit Ethernet interfaces.
BFD is supported only on Gigabit Ethernet interfaces. Support for additional WAN encapsulations such as Frame Relay and PPP is planned for future releases.
Multicast with Security and QoS Features
Configure multicast PIM-v2 sparse mode on the branch and headend routers to send/receive multicast traffic
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Set up a primary WAN interface and a secondary WAN interface on the branch router.
2.
Set up the secondary WAN interface to be an SHDSL IMA interface.
3.
Configure secondary WAN to be a higher cost route than the primary WAN, using the OSPF ip ospf cost command, so that the primary WAN is always preferred.
4.
Configure BFD on the primary WAN interface of the branch router and the primary WAN interface of the headend router with a BFD interval of 50 ms, a min_rx of 50 ms, and a BFD multiplier of 5.
5.
Configure BFD on the secondary WAN interface.
6.
Enable BFD for all interfaces in the OSPF routing process.
7.
Verify whether BFD is up by entering the show bfd neighbor command.
8.
Configure an IPTV server on the headend to stream a 300-kb/s stream to a multicast group 239.10.x.x.
9.
Configure the headend router as an RP, and configure PIM-SM on both the headend and branch routers.
10.
Configure IGMP v2 on the access and distribution switches.
11.
Configure one of the IPsec types, that is, DMVPN or GETVPN, on both the primary and secondary WAN interface between the branch and headquarters.
12.
Configure ZPF as explained in the Zone-based Policy Firewall Configuration on the Branch Router test case procedure.
13.
Configure the secondary WAN interface as the interface connecting to the Internet through the ISP.
14.
Assign the primary WAN interface to the Private zone.
15.
Assign the secondary WAN interface to the Public zone.
16.
Assign the voice VLAN and data VLAN interfaces to the Private zone.
17.
If you are using DMVPN, assign the tunnel interface to the VPN zone.
18.
Define a firewall policy between the VPN zone and the Public zone.
19.
Define a firewall policy between the VPN zone and the Private zone.
20.
Configure static NAT translations for certain hosts on the data VLAN, using an address pool. For the rest of the hosts, configure PAT by using the overload command in the NAT configuration.
21.
Configure the data VLAN as NAT inside, and configure the secondary WAN interface as NAT outside.
22.
Configure Cisco IOS IPS with IDCONF v5.0 on the router.
23.
Enable advanced category signature set.
24.
Configure Cisco IOS IPS for both directions of traffic on the data and DMZ VLAN and WAN interfaces.
25.
Enable syslog on the router, and log the syslog messages to a syslog server located in the branch.
(continued)26.
Configure 8-class hierarchical QoS on both the primary and secondary WAN interfaces.
27.
Mark all the traffic going out to the Internet as best-effort traffic.
28.
Configure traffic shaping to 95% of the available WAN bandwidth.
29.
Configure NBAR as in the NBAR Classification with QoS test case.
30.
Configure NetFlow on the WAN and LAN interfaces for ingress and egress traffic.
31.
Collect traffic statistics and distribution charts, and export the statistics to a NAM, using NetFlow version 5 or version 9.
32.
Send HTTP, FTP, and ICMP traffic between the branch and headquarters.
33.
Send HTTP, FTP, DNS, and ICMP traffic between PCs on the branch data VLAN to the Internet.
34.
Four clients in the branch join the multicast group 239.10.x.x to view the IPTV video stream.
35.
Verify translations and statistics, using the show ip nat translations and show ip nat statistics commands.
36.
Launch DDOS attacks from a PC attached the branch router data VLAN to a server located in the headquarters.
37.
Launch threats from a host in the Internet to the DMZ servers.
38.
Verify translations and statistics, using the show ip nat translations and show ip nat statistics commands.
39.
Verify whether the attacks are detected by Cisco IOS IPS and whether the alert messages are logged to the syslog server.
40.
Verify QoS, using the show policy-map interface command.
41.
Verify NetFlow, using the show ip flow command.
42.
Verify multicast traffic, using the show ip mroute active and show ip mroute count commands.
43.
Bring down the primary WAN interface by either pulling out the cable or shutting down the link on the headend side.
44.
After about 3 minutes, bring up the primary WAN interface.
Note
IPTV clients leave the group after 5 minutes.
When the primary WAN fails, OSPF reconvergence should occur within a second because of BFD.
ZPF should inspect all traffic going out of the secondary WAN interface.
All the traffic between the branch and headquarters should be sent through the IPsec tunnel over the secondary WAN interface.
Inside addresses should be translated to outside global addresses when the traffic from the LAN is going out to the Internet. The return traffic from the Internet to the LAN should always be directed to the outside global address of the inside hosts.
HTTP, FTP, and ICMP sessions should be maintained during the switchover and switchback.
QoS should be applied to the traffic, and ZPF should not have any adverse effect on the QoS.
All the Internet traffic should be marked as best-effort.
Traffic should be shaped to 95% of the WAN bandwidth.
Since the secondary WAN link bandwidth is less than the primary WAN bandwidth, only conforming high-priority traffic, such as voice traffic or mission-critical traffic, should be carried over the secondary WAN link. The rest should be dropped.
The attacks should be detected by Cisco IOS IPS, and appropriate signatures should be triggered.
Actions such as warning, dropping the packets or dropping the session, or blocking the host should be taken based on a particular signature configuration.
The alert messages related to the attack should be logged to a syslog server.
NBAR should provide bandwidth guarantees to different flows and should detect and stop worms such as NIMDA and CODE RED.
The multicast join should be successful, and IPTV clients should be able to view the IPTV video stream.
Even when multiple clients join the multicast group, only one stream should be coming from the headend to the branch.
The multicast clients should continue to receive the video stream during primary WAN link failure.
NetFlow statistics collected should be within performance requirements.
When the primary comes up after 3 minutes, the traffic should be routed over the primary WAN interface IPsec tunnel.
No router tracebacks, memory leaks, or crashes should be observed.
The multicast stream should cease from the headend to the branch when all the clients leave the multicast group.
All the traffic should be Cisco Express Forwarding switched.
Passed on Gigabit Ethernet interfaces.
BFD is supported only on Gigabit Ethernet interfaces. Support for additional WAN encapsulations such as Frame Relay and PPP is planned for future releases.
Box-to-Box Redundancy with HSRP
Configure HSRP to provide box-to-box redundancy so that if the primary router fails, the standby router takes over and routes all the traffic
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Configure HSRP on both routers in the branch.
2.
Configure one of the router as a primary router by setting the standby priority to be higher; for example, 140.
3.
Configure the remaining router as the secondary router with a standby priority of 110.
4.
Configure preemption delay of 60 seconds.
5.
Configure separate HSRP addresses for voice, data, and DMZ VLANs.
6.
Track the LAN and WAN interfaces of the primary router.
7.
Configure the default gateway as the HSRP address on the PC clients and servers in the LAN.
8.
Send HTTP, FTP, and ICMP traffic from the branch to headquarters.
9.
Power-cycle the primary router.
10.
Verify HSRP, using the show standby command.
The standby router should take over when the power is cycled on the primary router.
All the traffic should be routed through the standby router.
The existing sessions for HTTP and FTP traffic should be torn down and new sessions should be set up through the standby router.
When the primary router comes back, it should take over from the standby after waiting for preemption time to expire.
Passed
Network Management Test Cases
Enable SNMP on the UUTs for Management and Monitoring
Enable SYSLOG on the UUT for Management and Monitoring
Using Cisco CCP for Configuration and Monitoring of the UUTs
WAN Optimization Test Cases
Cisco WCCP Redirection
Cisco WAE Automatic Discovery to Identify WAE Appliances
Cisco WAE Optimization Feature (TFO)
Cisco WAAS, Cisco IOS Zone-based Firewall, and Cisco IOS IPS Interoperability
Cisco WAAS with security feature interoperability
1.
Configure Cisco WCCP redirection so that the TCP flows are redirected to the Cisco WAE module on the UUT as mentioned in the previous test cases.
2.
Configure zone-based firewall as described in the previous test cases.
3.
Configure Cisco IOS Intrusion Prevention as described in the previous test cases.
4.
Send stateful TCP traffic from the branch network on the UUT to the headquarters data network.
5.
Monitor the traffic, using show commands.
Verify that the TCP traffic is being optimized with all other Cisco IOS features being executed by using show commands listed in the "Cisco Wide Area Application Services Verification" section on page 7.
Passed
Cisco WAAS with NBAR
Cisco WAAS with CIFS
Cisco WAE with Data Redundancy Elimination
Negative Test Case for DRE
Cisco Unified CME Test Cases
SCCP Phone Registration to Cisco Unified CME
Register SCCP phones to the Cisco Unified CME
Figure 1, Private WAN, Cisco Unified CME Mode, or
1.
Configure Cisco Unified CME on the branch router with the Cisco Unified CME address belonging to the voice VLAN segment.
2.
For the Cisco 3945 branch, configure the maximum ephones to be 240 phones.
3.
For the Cisco 3925 branch, configure the maximum ephones to be 160 phones.
4.
Configure dual lines and auto-registration for each of the phones.
5.
Configure a TFTP server on the branch router for the phones to download the firmware.
6.
Configure a DHCP server on the branch router to provide IP addresses for Cisco IP Phone endpoints.
7.
Register SCCP phones to Cisco Unified CME. Register multiple phone types such as 7960, 7962, 7965, 7971, 7975, 7985, and 7936 phones.
8.
Verify the configuration, using the show telephony-service and show ephone registered commands.
All the phones should successfully register to the Cisco Unified CME.
Passed
SIP Phone Registration to Cisco Unified CME
Register SIP phones to Cisco Unified CME
Figure 1, Private WAN, Cisco Unified CME Mode, or
1.
Configure Cisco Unified CME on the branch router with the Cisco Unified CME address belonging to the voice VLAN segment.
2.
For the Cisco 3945 branch, configure the maximum ephones to be 240 phones.
3.
For the Cisco 3925 branch, configure the maximum ephones to be 160 phones.
4.
Configure dual lines and auto-registration for each of the phones.
5.
Configure a TFTP server on the branch router for the phones to download the firmware.
6.
Configure a DHCP server on the branch router to provide IP addresses for the Cisco IP Phone endpoints.
7.
Register SIP phones to Cisco Unified CME. Register multiple phone types such as 7960, 7962, 7965, 7971, 7975, 7985, and 7936 phones.
8.
Verify the configuration, using the show voice register command.
All the phones should successfully register to the Cisco Unified CME.
Passed
SCCP Local Calls
Make calls between the SCCP phones registered to the Cisco Unified CME
Figure 1, Private WAN, Cisco Unified CME Mode, or
1.
Make a call between two phones registered to the Cisco Unified CME.
2.
Verify ringback tone when the phone is ringing.
3.
Verify the voice path, and pass DTMF digits between the phones.
Voice call should be successful with 100% path confirmation.
DTMF digit passing should successful.
Passed
SIP Local Calls
Make calls between the SIP phones registered to the Cisco Unified CME
Figure 1, Private WAN, Cisco Unified CME Mode or
1.
Make a call between two phones registered to the Cisco Unified CME.
2.
Verify the ringback tone when the phone is ringing.
3.
Verify the voice path, and pass DTMF digits between the phones.
The voice call should be successful with 100% path confirmation.
DTMF digit passing should be successful.
Passed
PSTN Calls
Make calls between the IP Phones registered to Cisco Unified CME to PSTN
Figure 1, Private WAN, Cisco Unified CME Mode, or
1.
Configure a PRI trunk to the PSTN on the branch router.
2.
Configure voice translation rules to translate incoming calls from the PSTN.
3.
Make a call from a PSTN phone to the branch IP Phone.
4.
Verify the ringback tone when the phone is ringing.
5.
Verify the voice path, and pass DTMF digits.
6.
Verify for both SCCP and SIP phones.
Voice call should be successful with 100% path confirmation.
DTMF digit passing should be successful.
Passed
Branch to Headquarters Calls over the WAN with a SIP Trunk
Make calls between the IP Phones registered to Cisco Unified CME in the branch and IP Phones registered to Cisco Unified CM in the headquarters
Figure 1, Private WAN, Cisco Unified CME Mode, or
1.
Configure a SIP trunk over the WAN interface between Cisco Unified CME and Cisco Unified CM.
2.
Configure voice class with G.729 and G.711 as the codec options, with the first choice being G.729, and the second choice being G.711.
3.
Configure RFC 2833 for DTMF relay.
4.
Associate the voice class to the SIP trunk dial peer.
5.
Make a call from an IP Phone in the branch to the IP Phone in the headquarters.
6.
Verify the ringback tone when the phone is ringing.
7.
Verify the voice path, and pass DTMF digits.
8.
Verify for both SCCP and SIP phones.
Voice call should be successful with 100% path confirmation.
DTMF digit passing should be successful.
Passed
Branch to Headquarters Calls over the WAN with an H.323 trunk
Make calls between the IP Phones registered to Cisco Unified CME in the branch and IP Phones registered to Cisco Unified CM in the headquarters
Figure 1, Private WAN, Cisco Unified CME Mode, or
1.
Configure an H.323 trunk over the WAN interface between Cisco Unified CME and Cisco Unified CM.
2.
Configure voice class with G.729 and G.711 as the codec options, with the first choice being G.729, and the second choice being G.711.
3.
Configure RFC 2833 DTMF relay.
4.
Associate the voice class to the H.323 dial peer.
5.
Make a call from an IP Phone in the branch to the IP Phone in the headquarters.
6.
Verify the ringback tone when the phone is ringing.
7.
Verify the voice path, and pass DTMF digits.
8.
Verify for both SCCP and SIP Phones.
Voice call should be successful with 100% path confirmation.
DTMF digit passing should be successful.
Passed
Supplementary Services with Cisco Unified CME
Test the various supplementary features in Cisco Unified CME with all the phones local to the branch
Figure 1, Private WAN, Cisco Unified CME Mode, or
1.
Configure transfer system full-consult on the Cisco Unified CME.
2.
Configure music on hold (MOH) to source from a file in flash memory.
3.
Verify call transfer full consult between phones A, B, and C, with C being the transferrer; that is, make a call from phone A to phone B, and transfer the call to phone C.
4.
Verify MOH on phone A during call transfer.
5.
Configure transfer system full-blind on the Cisco Unified CME.
6.
Verify call transfer full-blind between phones A, B, and C with C being the transferrer, that is, make a call from phone A to phone B, and transfer the call to phone C.
7.
Verify MOH on phone A during call transfer.
8.
Configure call forward functionality by configuring forward-to numbers under the ephone-dns.
9.
Verify call forward no answer to another ephone extension.
10.
Verify call forward all to another ephone extension.
Voice call should be successful with 100% path confirmation.
Call transfer full-consult should be successful.
Call transfer full-blind should be successful.
Call forward no answer should be successful.
Call forward all should be successful.
MOH should be heard.
Passed
Supplementary Services Between Phones in the Branch, Headquarters, and PSTN
Test the various supplementary features between phones in the branch registered to Cisco Unified CME, phones registered to Cisco Unified CM, and PSTN phones
Figure 1, Private WAN, Cisco Unified CME Mode, or
1.
Configure transfer system full-consult on the Cisco Unified CME.
2.
Configure MOH to source from a file in flash memory.
3.
Configure multicast MOH.
4.
Verify call transfer full-consult between phones A, B, and C with C being the transferrer; that is, make a call from phone A to phone B, and transfer the call to phone C. Phone A is located in headquarters, Phone B is located in the branch, and Phone C is in the PSTN.
5.
Verify MOH on phone A during call transfer.
6.
Configure transfer system full-blind on the Cisco Unified CME.
7.
Verify call transfer full-blind between phones A, B, and C with C being the transferrer; that is, make a call from phone A to phone B, and transfer the call to phone C.
8.
Verify MOH on phone A during call transfer.
9.
Configure call forward functionality for Cisco Unified CME phones by configuring forward-to numbers under the ephone-dns.
10.
Verify call forward no answer to another ephone extension.
11.
Verify call forward all to another ephone extension.
Voice call should be successful with 100% path confirmation.
Call transfer full-consult should be successful.
Call transfer full-blind should be successful.
Call forward no answer should be successful.
Call forward all should be successful.
MOH should be heard.
Passed
Call Conference in the Branch Cisco Unified CME
Test a three-party conference with the branch IP Phone as the conference initiator
Figure 1, Private WAN, Cisco Unified CME Mode, or
1.
Make a three-party conference between a branch phone, a headquarters phone, and a PSTN phone, with the branch phone as the conference initiator.
Conference call should be successful.
Passed
Call Forward to Voice Mail
Test call forward to Cisco Unity Express with transcoding on the Cisco Unified CME
Figure 1, Private WAN, Cisco Unified CME Mode, or
1.
Configure call forward on no answer or busy to voice mail on the ephone DNs of the IP Phones on the branch.
2.
Set up Cisco Unity Express as the voice mail system.
3.
Configure DSP farm on the branch router for Cisco Unified CME transcoding to transcode G.729 codec to G.711-ulaw codec.
4.
Make a call from the headquarters phone to the branch phone that uses the G.729 codec.
5.
Make a branch phone busy.
6.
Verify whether the call was forwarded to voice mail.
7.
Verify whether the MWI appears on the branch phone.
8.
Retrieve the voice mail from Cisco Unity Express by dialing the voice mail from the branch phone.
9.
Verify whether the MWI disappears once the message is heard.
The call should be forwarded to voice mail.
Cisco Unified CME transcoding resources should be invoked when the call is forwarded to voice mail, because Cisco Unity Express supports only the G.711u-law codec.
The MWI light should appear when the message is left in Cisco Unity Express and should disappear once the message is retrieved.
Passed
Video Call Between Branch and Headquarters
Test a video call between the branch and headquarters using either Cisco Unified Video Advantage or the Cisco Unified IP Phone 7985G.
Figure 1, Private WAN, Cisco Unified CME Mode, or
1.
Make a video call between the branch phone and the headquarters phone using either Cisco Unified Video Advantage or the Cisco Unified IP Phone 7985G with H.263 for the video and G.711u-law codec for the voice.
2.
Test Hold and Resume on the Cisco Unified CME phone.
3.
Test mute.
4.
Verify the voice and video path.
The voice and video path confirmation should be 100%.
When the Cisco Unified CME phone puts the call on hold, the headquarters phone should hear MOH.
When the Cisco Unified CME phone mutes the call, the headquarters phone should not hear anything, and the video should freeze.
Passed
T.38 Fax Between Branch and Headquarters
Test T.38 fax between the branch and headquarters
Figure 1, Private WAN, Cisco Unified CME Mode, or
1.
Configure T.38 fax on the branch router and T.38 fax the Cisco Unified CM.
2.
Using a fax machine in the branch, send a multipage fax to a fax machine in the headquarters.
The fax should be received properly on the headquarters fax machine.
Passed
IP SLA VoIP UDP Jitter Codec g711ulaw (Branch to HQ)
VoIP UDP Jitter IP SLA codec g711ulaw
Figure 1, Private WAN, Cisco Unified CME Mode, or
1.
Enable the IP SLA responder on the HQ router.
2.
Configure the basic VoIP UDP Jitter operation type on the branch router.
3.
Configure any options available, such as codec g711ulaw, for the VoIP UDP Jitter SLAs operation type.
4.
Configure the threshold conditions, if required.
5.
Schedule the operation to run and let the operation run for enough of a period of time to gather statistics.
6.
Display and interpret the results of the operation using either the Cisco IOS CLI or an NMS system with SNMP.
To view and interpret the operational results of an IP SLA, use the show ip sla monitor statistics command to check the boundaries the limits, for example:
ICPIF Range MOS Quality
0-3 5 Best
4-13 4 High
14-23 3 Medium
24-33 2 Low
34-43 1 Poor
Passed
Remote Phones on the Cisco Unified CME
Test remote phone support in the Cisco Unified CME
Figure 1, Private WAN, Cisco Unified CME Mode or
1.
Register a remote phone to the Cisco Unified CME through the Internet; that is, the remote phone is located in the remote teleworker's home office.
2.
Configure the G.729 codec for remote phones.
3.
Configure the media termination point (MTP) option on the Cisco Unified CME to terminate and originate RTP packets from and to the remote phone.
4.
Configure DSP farm assist for the remote phone to transcode G.729 calls to G.711 calls.
5.
Make a call from the remote phone to a branch IP Phone.
6.
Verify the ringback tone when the phone is ringing.
7.
Verify the voice path and also pass DTMF digits.
The ringback tone should be heard.
The voice path confirmation should be 100%.
DTMF digit passing should be successful.
Passed
Cisco Unified CME with WAN Failure Scenario to Headquarters
Test the Cisco Unified CME functionality to the headquarters during WAN failure
Figure 1, Private WAN, Cisco Unified CME Mode, or
1.
Make a call between a branch IP Phone and a headquarters IP Phone.
2.
Make a call between a branch IP Phone and a PSTN phone.
3.
Make a call between two branch IP Phones.
4.
Bring down the WAN interface of the router.
During WAN failure the call between the branch IP Phone and the headquarters IP Phone should be dropped; however, the call between the IP Phone and the PSTN phone and the call between the two IP Phones in the branch should be sustained.
Passed
Cisco Unified CME with IPsec over the WAN
Test Cisco Unified CME functionality with IPsec over the WAN
Figure 1, Private WAN, Cisco Unified CME Mode, or
1.
Configure IPsec over the WAN, and test with all types of IPsec.
2.
Make a video call from a branch IP Phone to a headquarters IP Phone.
3.
Verify ringback.
4.
Verify whether signaling, voice, and video packets are encrypted and decrypted properly.
5.
Verify voice and video path, and pass DTMF digits.
Signaling, voice, and video packets should be encrypted and decrypted properly.
The ringback tone should be heard when the remote phone rings.
The voice and video path confirmation should be 100%.
DTMF digit passing should be successful.
Passed
Cisco Unified CME with QoS and NBAR
Test Cisco Unified CME functionality with QoS and NBAR applied to signaling and RTP packets
Figure 1, Private WAN, Cisco Unified CME Mode, or
1.
Configure the 8-class QoS model over the primary WAN interface.
2.
Configure LLQ for voice and video traffic and allocate X% and Y% of the bandwidth for voice and video, but make sure not to exceed 33% of the total bandwidth.
3.
Configure 1P3Q3T on the Catalyst switch, and trust the COS value coming from the Cisco IP Phones.
4.
Configure a DSCP value of CS3 on the SIP/H.323 dial peer to give priority to signaling traffic.
5.
Make voice and video calls from branch IP Phones to headquarters IP Phones.
6.
Verify whether the IP Phone marks the voice traffic with a DSCP value of EF.
7.
Verify whether the Catalyst switch marks the video packets with a DSCP value of AF41.
8.
Verify whether call signaling, voice, and video traffic are classified properly and put in priority queue.
9.
Send more voice and video traffic to exceed the allocated bandwidth, and verify whether voice and video traffic is dropped.
The IP Phone should mark the voice traffic with DSCP value of EF.
The IP Phone should mark SCCP signaling traffic with DSCP value of CS3.
The Catalyst switch should trust the COS value marked by IP Phone.
Catalyst switch should remark the video traffic to AF41.
QoS on the router should properly classify signaling, voice, and video packets, based on their DSCP value.
Voice and video should get strict priority queuing treatment; that is, adhering voice and video traffic should be sent out first, and exceeding voice and video traffic should be dropped.
Passed
Cisco Unified CME with ZPF
Test Cisco Unified CME functionality with ZPF
Figure 1, Private WAN, Cisco Unified CME Mode, or
1.
Configure ZPF, with data and voice VLANs in the Private zone and with WAN interface in the Public zone.
2.
Configure a policy to inspect router-generated SIP, H.323, and RTP traffic from system-defined self-zone to Public zone, and vice versa.
3.
Configure access lists to allow calls originated in headquarters through the firewall.
4.
Make a voice call from a branch IP Phone to a headquarters IP Phone.
5.
Verify the ringback tone.
6.
Verify the voice path and pass DTMF digits.
ZPF should inspect call signaling and RTP packets and open holes for the return traffic.
The ringback tone should be heard.
The voice path confirmation should be 100%.
DTMF digit passing should be successful.
Passed
Cisco Unified CME Remote Phones with ZPF
Test Cisco Unified CME remote phone support with ZPF
Figure 1, Private WAN, Cisco Unified CME Mode, or
1.
Configure ZPF, with data and voice VLANs in the Private zone and WAN interface in the Public zone.
2.
Configure a policy to inspect router generated SIP, H.323, and RTP traffic from system-defined self-zone to Public zone, and vice versa.
3.
Configure a policy to inspect SCCP traffic for the remote phone.
4.
Configure an access list to allow incoming SCCP and RTP traffic from a remote phone to the Cisco Unified CME.
5.
Configure MTP on the Cisco Unified CME.
6.
Configure DSP farm assist for the remote phone.
7.
Configure an access list to allow calls originated in headquarters through the firewall.
8.
Make a voice call from a remote IP Phone to a branch IP Phone.
9.
Verify the ringback tone.
10.
Verify the voice path and pass DTMF digits.
11.
When the call is verified, transfer the call, using full-consult transfer, to a headquarters, with the branch phone being the transferrer. Commit the transfer.
12.
Verify whether the transfer completes.
13.
Verify whether the voice path between the remote phone and the headquarters phone is set up.
14.
Verify DTMF digit passing.
ZPF should open holes for SCCP traffic for remote phone registration.
ZPF should inspect call signaling and RTP packets and open holes for the return traffic.
The ringback tone should be heard.
The voice path confirmation should be 100%.
DTMF digit passing should be successful.
Transfer should be successful.
Passed
Cisco Unified CME Failover with Secondary Cisco Unified CME
Test Cisco Unified CME failover to a secondary Cisco Unified CME
Figure 1, Private WAN, Cisco Unified CME Mode, or
1.
Set up Cisco Unified CMEs on two branch routers; make one of the routers the primary Cisco Unified CME, and make the other the secondary.
2.
Register all the phones to the primary Cisco Unified CME.
3.
Verify in the phone network configuration whether both Cisco Unified CMEs exist.
4.
Make a call between the branch IP Phone and the headquarters IP Phone.
5.
Make a call between the branch IP Phone and another branch IP Phone.
6.
Bring down the primary Cisco Unified CME by reloading that router.
7.
Verify whether all the phones register to the secondary Cisco Unified CME.
8.
Verify the status of active calls.
9.
Verify MWI status of phones with active voice mail.
10.
Verify whether the phones fall back to the primary Cisco Unified CME when it comes back up.
When the primary Cisco Unified CME fails, all the phones with no active calls should immediately register to the secondary Cisco Unified CME.
For phones with active calls over the WAN to headquarters or the PSTN, those calls should be dropped. The phones should immediately register to the secondary Cisco Unified CME.
For phones with active calls local to the branch, those calls should be sustained. When those calls complete, those phones should register to the secondary Cisco Unified CME.
Phones with active voice mail should lose their MWI.
When the primary Cisco Unified CME comes up, all the phones should register to primary Cisco Unified CME.
Passed
Baseline Features Plus Cisco Unified CME
Test baseline features plus Cisco Unified CME
Figure 1, Private WAN, Cisco Unified CME Mode, or
1.
Enable all baseline features as described in the Complete Baseline Test test case.
2.
Configure a primary Cisco Unified CME and a secondary Unified CME.
3.
Register all the phones to the primary Cisco Unified CME.
4.
Make voice and video calls between branch IP Phones and headquarters IP Phones.
a.
Verify the ringback tone, verify the voice and video path, and pass DTMF digits.
5.
Make voice calls between branch IP Phones and PSTN phones.
a.
Verify the ringback tone, verify the voice path, and pass DTMF digits.
6.
Make voice calls between branch IP Phones.
a.
Verify the ringback tone, verify the voice path, and pass DTMF digits.
7.
Make a 4-party conference call with a branch IP Phone, a branch FXS phone, a headquarters IP Phone, and a PSTN phone as the conference participants.
a.
Verify that when the conference initiator leaves the conference, all the parties are dropped.
8.
Make a call from a headquarters IP Phone to a branch IP Phone, which is busy.
a.
Verify whether the headquarters IP Phone is able to leave voice mail.
b.
Verify whether Cisco Unified CME transcoding is invoked.
c.
Verify whether the branch phone receives an MWI.
9.
Retrieve voice mail from branch IP Phones.
a.
Verify whether MWI changes status once the voice mail messages are retrieved.
10.
Make a call from a remote Cisco Unified CME phone to a branch IP Phone.
a.
Verify the ringback tone, verify the voice path, and pass DTMF digits.
11.
Verify supplementary services.
The voice and video path confirmation should be 100%.
Cisco Unified CME transcoding gets invoked for call transfers to voice mail, with the calling party being in headquarters.
DSP farm assist gets invoked for remote phones.
The MWI light should turn on when voice mail messages are left and should turn off when the voice mail messages are retrieved.
The conference call should be successful.
Supplementary services such as call transfer and call forward should be successful.
Passed
Cisco Unified SRST Test Cases
SCCP Phone Registration to Cisco Unified CM
Register IP Phones in the branch to the Cisco Unified CM located in the headquarters using SCCP
Figure 2, Private WAN, Cisco Unified SRST Mode, or
1.
For the Cisco 3945 branch, register 240 phones to Cisco Unified CM.
2.
For the Cisco 3925 branch register 160 phones to Cisco Unified CM.
3.
Use Cisco Unified CM bulk registration utility to register all the phones.
4.
Configure regions in Cisco Unified CM for each branch.
5.
Configure dual lines for each phone.
6.
Configure the TFTP server as the Cisco Unified CM in the branch router that is used to download the firmware.
7.
Configure a DHCP server on the branch router to provide IP addresses to IP Phone endpoints.
8.
Register SCCP phones to Cisco Unified CM. Register multiple phone types such as 7960, 7962, 7965, 7971, 7975, 7985, and 7936 phones.
All the phones should successfully register to the Cisco Unified CM.
Passed
SIP Phone Registration to Cisco Unified CM
Register IP Phones in the branch to the Cisco Unified Communications Manager, located in the headquarters using SIP
Figure 2, Private WAN, Cisco Unified SRST Mode, or
1.
For the Cisco 3945 branch, register 240 phones to Cisco Unified CM.
2.
For the Cisco 3925 branch, register 160 phones to Cisco Unified CM.
3.
Use the Cisco Unified CM bulk registration utility to register all the phones.
4.
Configure regions in the Cisco Unified CM for each branch.
5.
Configure dual lines for each of the phones.
6.
Configure a TFTP server as the Cisco Unified Communications Manager in the branch router for the phones to download the firmware.
7.
Configure a DHCP server on the branch router to provide IP addresses to IP Phone endpoints.
8.
Register SIP phones to Cisco Unified CM. Register multiple phone types such as 7960, 7962, 7965, 7971, 7975, 7985, and 7936 phones.
All the phones should successfully register to the Cisco Unified CM.
Passed
SIP Local Calls
Make calls between the SIP phones registered to the Cisco Unified CM
Figure 2, Private WAN, Cisco Unified SRST Mode, or
1.
Make a call between two phones registered to the Cisco Unified CM.
2.
Verify the ringback tone when the phone is ringing.
3.
Verify the voice path, and pass DTMF digits between the phones.
The voice calls should be successful with 100% path confirmation.
DTMF digit passing should be successful.
Passed
SCCP Local Calls
Make calls between the SCCP phones registered to the Cisco Unified CM.
Figure 2, Private WAN, Cisco Unified SRST Mode, or
1.
Make a call between two phones registered to the Cisco Unified CM.
2.
Verify the ringback tone when the phone is ringing.
3.
Verify the voice path, and pass DTMF digits between the phones.
The voice call should be successful with 100% path confirmation.
DTMF digit passing should be successful.
Passed
PSTN Calls with SIP Gateway
Make calls between the IP Phones registered to Cisco Unified CM and PSTN phones
Figure 2, Private WAN, Cisco Unified SRST Mode, or
1.
Configure a PRI trunk to the PSTN on the branch router.
2.
Configure voice translation rules to translate incoming calls from the PSTN.
3.
Configure a SIP trunk between the branch router and Cisco Unified CM.
4.
Register the branch router as a SIP gateway in Cisco Unified CM.
5.
Configure a autoattendant in Cisco Unified CM that includes route lists, route groups, and route pattern.
6.
Make a call from a PSTN phone to the branch IP Phone.
7.
Verify the ringback tone when the phone is ringing.
8.
Verify the voice path, and pass DTMF digits.
The voice call should be successful with 100% path confirmation.
DTMF digit passing should be successful.
Passed
PSTN Calls with H.323 Gateway
Make calls between the IP Phones registered to Cisco Unified CM to PSTN
Figure 2, Private WAN, Cisco Unified SRST Mode, or
1.
Configure a PRI trunk to the PSTN on the branch router.
2.
Configure voice translation rules to translate incoming calls from the PSTN.
3.
Configure an H.323 trunk between the branch router and Cisco Unified CM.
4.
Register the branch router as an H.323 gateway in Cisco Unified CM.
5.
Configure a autoattendant in Cisco Unified CM that includes route lists, route groups, and route pattern.
6.
Make a call from a PSTN phone to the branch IP Phone.
7.
Verify the ringback tone when the phone is ringing.
8.
Verify the voice path, and pass DTMF digits.
The voice call should be successful with 100% path confirmation.
DTMF digit passing should be successful.
Passed
Branch to Headquarters Calls over the WAN
Make calls between the branch IP Phones registered to Cisco Unified CM and IP Phones registered to Cisco Unified CM in the headquarters
Figure 2, Private WAN, Cisco Unified SRST Mode, or
1.
Make a call from an IP Phone in the branch to the IP Phone in the headquarters.
2.
Verify the ringback tone when the phone is ringing.
3.
Verify the voice path, and pass DTMF digits.
4.
Verify for both SCCP and SIP Phones.
The voice call should be successful with 100% path confirmation.
DTMF digit passing should be successful.
Passed
Supplementary Services Between Phones in Branch, Headquarters, and PSTN
Test the various supplementary features between phones in the branch registered to Cisco Unified CM, phones in headquarters registered to Cisco Unified CM, and PSTN phones
Figure 2, Private WAN, Cisco Unified SRST Mode, or
1.
Configure the branch router as a SIP gateway.
2.
Configure multicast MOH on Cisco Unified CM.
3.
Enable PIM-SM on the branch router and headend router, with the headend router as the RP.
4.
Verify call transfer full-consult between phones A (located in headquarters), B (located in the branch), and C (on the PSTN) with C being the transferrer; that is, make a call from phone A to phone B, and transfer the call to phone C.
5.
Verify MOH on phone A during call transfer.
6.
Configure call forward functionality for IP Phones by configuring forward-to numbers in the phone configuration in Cisco Unified CM.
7.
Verify call forward no answer to another IP Phone extension.
8.
Verify call forward all to another IP Phone extension.
The voice call should be successful with 100% path confirmation.
Call transfer full-consult should be successful.
Call forward no answer should be successful.
Call forward all should be successful.
MOH should be heard.
Passed
Call Conference in the Branch
Test a three-party conference with the branch IP Phone as the conference initiator
Figure 2, Private WAN, Cisco Unified SRST Mode, or
1.
Configure DSP farm conferencing on the branch router to utilize the DSP resources in the branch router for conferencing.
2.
Configure a media resources group for conference in the Cisco Unified CM.
3.
Add the branch router DSP farm resource to the media resource group.
4.
Register the DSP farm to the Cisco Unified CM.
5.
Make a three-party conference between a branch phone, headquarters phone, and a PSTN phone, with the branch phone as the conference initiator.
6.
Verify whether DSP farm conferencing resources is utilized, using the show dspfarm and show sccp connections commands.
Conference call should be successful.
The DSP farm resources on the branch router should be utilized for conferencing.
When the conference initiator drops the call, all the parties should drop out of the conference.
Passed
Call Forward to Voice Mail
Test call forward to Cisco Unity Express with DSP farm transcoding
Figure 2, Private WAN, Cisco Unified SRST Mode, or
1.
Set up Cisco Unity Express on the branch router and register Cisco Unity Express to Cisco Unified CM using JTAPI.
2.
Configure CTI ports on Cisco Unified CM.
3.
Configure call forward on no answer or busy to voice mail in the device, phone configuration in Cisco Unified CM.
4.
Configure DSP farm transcoding on the branch router to transcode G.729 codec to G.711ulaw codec.
5.
Configure a media resource group for transcoder in Cisco Unified CM, and add the branch DSP farm transcoding resource to the media resource group.
6.
Make a call from the headquarters phone to the branch phone using the G.729 codec.
7.
Make the branch phone busy.
8.
Verify whether the call was forwarded to voice mail.
9.
Verify whether MWI appears on the branch phone when the voice mail is left.
10.
Retrieve the voice mail from the Cisco Unity Express by dialing the voice mail from the branch phone.
11.
Verify whether the MWI disappears when the message is heard.
The call should be forwarded to voice mail.
The DSP farm transcoding resources should be invoked when the call is forwarded to voice mail, since Cisco Unity Express supports only the G.71u-law codec.
The MWI light should appear when the message is left in Cisco Unity Express and should disappear when the message is retrieved.
Passed
Phone Registration During Cisco Unified Survivable Remote Site Telephony (Cisco Unified SRST)
Test IP Phone registrations during Cisco Unified SRST mode
Figure 2, Private WAN, Cisco Unified SRST Mode, or
1.
Initially register all the branch phones to Cisco Unified CM.
2.
Configure Cisco Unified SRST in the branch router.
3.
Configure Cisco Unified SRST in Cisco Unified CM as the branch router.
4.
Make calls between branch phones and headquarters phones, local calls, and calls from the branch to the PSTN.
5.
Bring down the WAN interface or bring down Cisco Unified CM by shutting it down.
6.
Verify the state of active calls during WAN/Cisco Unified CM failure.
7.
Verify whether all the phones register to Cisco Unified SRST.
8.
Bring up the Cisco Unified CM after about 10 minutes, and verify whether all the phones register to Cisco Unified Communications Manager.
Phones with no active calls should immediately register to Cisco Unified SRST.
Phones with active calls to headquarters should drop the call and register to Cisco Unified SRST.
Local calls and calls to the PSTN should be sustained. When the call completes, those phones should register to Cisco Unified SRST.
All the phones should immediately register to Cisco Unified CM when it comes up.
Passed
Local and PSTN Calls in Cisco Unified SRST Mode
Test local and PSTN calls in Cisco Unified SRST mode
Figure 2, Private WAN, Cisco Unified SRST Mode, or
1.
Configure MOH to source audio files from flash memory.
2.
Make locals calls, and make calls to the PSTN.
3.
Verify the ringback tone.
4.
Verify the voice path, and pass DTMF digits.
5.
Place local calls on hold for 30 seconds, and then resume the call.
6.
Place PSTN calls on hold for 30 seconds, and then resume the call.
The ringback tone should be heard.
The voice path confirmation should be 100%.
DMTF digit passing should be successful.
Local call hold/resume should be successful.
PSTN call hold/resume should be successful.
Locals call should hear tone on hold.
PSTN callers should hear music on hold.
Passed
Supplementary Services in Cisco Unified SRST Mode
Test supplementary services such as call transfers and call forwards in Cisco Unified SRST mode
Figure 2, Private WAN, Cisco Unified SRST Mode, or
1.
Configure transfer system full-consult on the Cisco Unified SRST.
2.
Configure MOH to source from a file in flash memory.
3.
Configure Multicast MOH.
4.
Verify call transfer full-consult between phones A, B, and C with C being the transferrer; that is, make a call from phone A to phone B, and transfer the call to phone C. Phone C and phone B are located in the branch, and phone A is in the PSTN.
5.
Make a call from phone A to phone B, and transfer the call to phone C.
6.
Verify MOH on phone A during call transfer.
7.
Configure transfer system full-blind on the Cisco Unified SRST.
8.
Verify call transfer full-blind between phones A, B, and C, with C being the transferer; that is, make a call from phone A to phone C, and transfer the call to phone B.
9.
Verify MOH on phone A during call transfer.
10.
Configure call forward functionality for the Cisco Unified SRST phones.
11.
Verify call forward no answer to another ephone extension.
12.
Verify call forward all to another ephone extension.
The voice call should be successful with 100% path confirmation.
Call transfer full-consult should be successful.
Call forward no answer should be successful.
Call forward all should be successful.
MOH should be heard.
Passed
Call Forward to Voice Mail in Cisco Unified SRST Mode
Test call forward to Cisco Unity Express with transcoding on the Cisco Unified CME
Figure 1, Private WAN, Cisco Unified CME Mode, or
1.
Configure call forward on no answer or busy to voice mail in Cisco Unified Communications Manager phone configuration.
2.
Go to Cisco Unified SRST mode.
3.
Set up Cisco Unity Express as the voice mail system.
4.
Make a call from the PSTN phone to a busy branch phone.
5.
Verify whether the call was forwarded to voice mail.
6.
Verify whether MWI appears on the branch phone.
7.
Retrieve the voice mail from Cisco Unity Express by dialing the voice mail from the branch phone.
8.
Verify whether the MWI disappears when the message is heard.
The call should be forwarded to voice mail.
The MWI light should appear when the message is left in Cisco Unity Express and should disappear when the message is retrieved.
Passed
Call Conference in Cisco Unified SRST Mode
Test a three-party conference with the branch IP Phone as the conference initiator
Figure 2, Private WAN, Cisco Unified SRST Mode or
1.
Make a three-party conference call between two branch phones and a PSTN phone, with one of the branch phones as the conference initiator.
The conference call should be successful.
Passed
Branch to Headquarters Calls with IPsec over the WAN
Test branch to headquarters calls with IPsec over the WAN
Figure 2, Private WAN, Cisco Unified SRST Mode, or
1.
Configure IPsec over the WAN, and test with all types of IPsec.
2.
Register the branch phones to the Cisco Unified Communications Manager.
3.
Make a video call from a branch IP Phone to a headquarters IP Phone.
4.
Verify the ringback tone.
5.
Verify whether signaling, voice, and video packets are encrypted and decrypted properly.
6.
Verify voice and video path, and pass DTMF digits.
Signaling, voice, and video packets should be encrypted and decrypted properly.
The ringback tone should be heard when the remote phone rings.
The voice and video path confirmation should be 100%.
DTMF digit passing should be successful.
Passed
Branch to Headquarters Voice and Video Calls with QoS and NBAR
Test branch to headquarters voice and video calls with QoS and NBAR applied to signaling and RTP packets
Figure 2, Private WAN, Cisco Unified SRST Mode, or
1.
Configure the 8-class QoS Model over the primary WAN interface.
2.
Configure LLQ for voice and video traffic, and allocate X% and Y% of the bandwidth for voice and video, but make sure not to exceed 33% of the total bandwidth.
3.
Configure 1P3Q3T on the Catalyst switch, and trust the CoS value coming from the Cisco IP Phones.
4.
Configure a DSCP value of CS3 on the SIP/H.323 dial peer to give priority to signaling traffic.
5.
Register the branch phones to the Cisco Unified Communications Manager.
6.
Make voice and video calls from branch IP Phones to headquarters IP Phones.
7.
Verify whether the IP Phone marks the voice traffic with a DSCP value of EF.
8.
Verify whether the Catalyst switch marks the video packets with a DSCP value of AF41.
9.
Verify whether call signaling, voice, and video traffic is classified properly and put in priority queue.
10.
Send more voice and video traffic to exceed the allocated bandwidth, and verify whether voice and video traffic is dropped.
The IP Phone should mark the voice traffic with a DSCP value of EF.
The IP Phone should mark SCCP signaling traffic with a DSCP value of CS3.
The Catalyst switch should trust the COS value marked by the IP Phone.
The Catalyst switch should re-mark the video traffic to AF41.
QoS on the router should properly classify signaling, voice, and video packets, based on their DSCP values.
Voice and video traffic should receive strict priority queuing treatment; that is, adhering voice and video traffic should be sent out first, and exceeding voice and video traffic should be dropped.
Passed
Branch to Headquarters Voice and Video calls with ZPF
Test Cisco Unified CME functionality with ZPF
Figure 2, Private WAN, Cisco Unified SRST Mode, or
1.
Configure ZPF with data and voice VLANs in the Private zone and WAN interface in the Public zone.
2.
In the Private-Public zone policy, add statements to inspect SCCP and SIP signaling the traffic from the phones, and add access lists to all incoming calls to the branch from headquarters.
3.
Make a voice call from a branch IP Phone to a headquarters IP Phone.
4.
Verify the ringback tone.
5.
Verify the voice path, and pass DTMF digits.
ZPF should inspect call signaling and dynamically open holes for RTP packets.
The ringback tone should be heard.
The voice path confirmation should be 100%.
DTMF digit passing should be successful.
Passed
High Availability in Cisco Unified SRST mode
Test high availability in Cisco Unified SRST mode using HSRP
Figure 2, Private WAN, Cisco Unified SRST Mode, or
1.
Configure two branch routers with HSRP, with one as the primary router and the other as the secondary router.
2.
Configure the Cisco Unified SRST address as the HSRP virtual address on both the branch routers.
3.
Configure Cisco Unified SRST in Cisco Unified Communications Manager with the HSRP virtual address.
4.
Initially register all the phones to Cisco Unified Communications Manager.
5.
Make local calls in the branch.
6.
Bring down Cisco Unified Communications Manager.
7.
Verify that the phones register to Cisco Unified SRST except the one phone with active calls.
8.
Bring down the primary branch routers after 10 minutes.
9.
Verify that all the phones register to the secondary Cisco Unified SRST router.
10.
Tear down active calls, and verify whether those phones register to the secondary Cisco Unified SRST router.
11.
Bring up the primary branch router after 5 minutes.
12.
Verify whether all the phones register back to the primary Cisco Unified SRST router when it comes up.
13.
Bring up the Cisco Unified Communications Manager after 30 minutes.
14.
Verify whether all the phones register to Cisco Unified Communications Manager when it comes up.
The phones should successfully register to Cisco Unified Communications Manager.
The phones should successfully register to the primary Cisco Unified SRST router when Cisco Unified Communications Manager goes down.
The phones should successfully register to the secondary Cisco Unified SRST router when the primary Cisco Unified SRST goes down.
The phones should switch back to the primary Cisco Unified SRST router when it comes up.
The phones should switch back to Cisco Unified Communications Manager when it comes up.
Passed
Baseline Features Plus Cisco Unified Communications Manager
Test baseline features plus Cisco Unified Communications Manager
Figure 1, Private WAN, Cisco Unified CME Mode, or
1.
Enable all baseline features as described in the Complete Baseline Test test case.
2.
Register all the phones to the primary Cisco Unified Communications Manager.
3.
Register all DSP farm transcoding and conferencing resources to Cisco Unified Communications Manager.
4.
Make voice and video calls between branch IP Phones and headquarters IP Phones.
a.
Verify the ringback tone, verify the voice/video path, and pass DTMF digits.
5.
Make voice calls between branch IP Phones and PSTN phones.
a.
Verify the ringback tone, verify the voice path, and pass DTMF digits.
6.
Make voice calls between branch IP Phones.
a.
Verify the ringback tone, verify the voice path, and pass DTMF digits.
7.
Make a four-party conference call with a branch IP Phone, a branch FXS phone, a headquarters IP Phone and a PSTN phone as the conference participants.
a.
Verify that when the conference initiator leaves the conference, all the parties are dropped.
b.
Verify whether DSP farm conferencing resources are utilized.
8.
Make a call from a headquarters IP Phone to a branch IP Phone that is busy.
a.
Verify whether the headquarters IP Phone is able to leave voice mail.
b.
Verify whether DSP farm transcoding gets invoked.
c.
Verify whether the branch phone receives an MWI.
9.
Retrieve the voice mail messages from the branch IP Phones.
a.
Verify that MWI changes status when the voice mail messages are retrieved.
10.
Verify supplementary services.
Voice and video path confirmation should be 100%.
DSP farm transcoding is invoked for call transfers to voice mail when the calling party is in headquarters.
The MWI light should turn on when voice mail messages are left and should turn off when the voice mail messages are retrieved.
Conference call should be successful.
Supplementary services such as call transfers and call forwards should be successful.
Passed
RSVP Agent in SRST Router-HQ to Branch Call with Phones Registered to Cisco Unified CM
Test calls between the IP Phones in the HQ to phones registered in the branch in centralized call control deployment scenario with RSVP agent enabled in HQ and WAN router
Figure 1, Private WAN, Cisco Unified CME Mode or
1.
Enable SCCP and configure transcoder/MTP profile with RSVP and coded pass-through in SRST branch router and WAN router in HQ.
2.
Register both the transcoder and MTP to Cisco Unified CM.
3.
Configure HQ and branch phones in different locations.
4.
Configure RSVP policy as mandatory for voice and video calls in Cisco Unified CM.
5.
Make a voice call from the HQ phone to a branch phone.
6.
Make a video call from the HQ phone to a branch phone.
7.
Make multiple voice calls from the HQ to the branch, so that the voice bandwidth is consumed.
8.
Make a new voice call.
Verify that an RSVP reservation is made and that both voice and video calls are successful.
Verify the voice path and pass DTMF.
Verify that both SCCP and SIP Phones work properly.
Verify RSVP reservation fails and the call is not successful when the bandwidth is consumed.
Passed
RSVP Agent with Application ID in SRST Router-HQ to Branch Call with Phones Registered to Cisco Unified CM
Make calls between the IP Phones registered to Cisco Unified CM in the HQ and IP Phones registered to Cisco Unified CME in the branch with RSVP agent configured
Figure 1, Private WAN, Cisco Unified CME Mode or
1.
Enable SCCP and configure transcoder/MTP profile with RSVP and coded pass-through in SRST branch router and WAN router in HQ.
2.
Configure the RSVP application ID for voice and video calls and specify the bandwidth to be 384 for video.
3.
Register both the transcoder and MTP to Cisco Unified CM.
4.
Configure HQ and branch phones in different locations.
5.
Configure RSVP policy as mandatory for voice and video calls in Cisco Unified CM.
6.
Make a voice call from the HQ phone to a branch phone.
7.
Make a video call from the HQ phone to a branch phone.
Verify that an RSVP reservation is made and that both voice and video calls are successful.
Verify that the second video call fails because the bandwidth is configured in application ID for video.
Verify the voice path and pass DTMF.
Verify that both SCCP and SIP phones work properly.
Verify that RSVP reservation fails and that the call is not successful when the bandwidth is consumed.
Passed
RSVP Agent-HQ to Branch Call with H.323 Trunk
Make calls between the IP Phones in HQ to phones registered in the branch in centralized call control deployment scenario with RSVP agent enabled and with application ID in HQ and WAN router
Figure 1, Private WAN, Cisco Unified CME Mode or
1.
Configure H.323 trunk over the WAN interface between Cisco Unified CME and Cisco Unified CM
2.
Enable SCCP and configure transcoder/MTP profile with RSVP and coded pass-through in SRST branch router and WAN router in HQ.
3.
Register both the transcoder and MTP to Cisco Unified CM.
4.
Configure RSVP policy as mandatory for voice and video calls in Cisco Unified CM.
5.
Configure voice class with G.729 and G.711 as the codec options, with the first choice being G.729 and second choice being G.711.
6.
Associate the voice class to the H.323 dial peer.
7.
Make a voice call from the HQ phone to a branch phone.
8.
Make a video call from the HQ phone to a branch phone.
9.
Make multiple voice calls from the HQ to the branch so that the voice bandwidth is consumed, and then make a new voice call.
Verify that an RSVP reservation is made and that both voice and video calls are successful.
Verify the voice path and pass DTMF.
Verify that both SCCP and SIP phones work properly.
Verify that the RSVP reservation fails and the call is not successful when the bandwidth is consumed.
Passed
Performance Test Cases
Baseline Performance Test
Enable all the baseline services in the branch and headend routers. The baseline features include BGP routing, OSPF/EIGRP routing, IPsec using DMVPN or GETVPN, ZPF, NAT, IPS, QoS, NBAR, ACL, NetFlow, DHCP, AAA RADIUS server, NTP, syslog, SNMP, PIM-v2, and IGMP v2.
Configure L2 and L3 switching on the access and distribution layer switches.
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Before the start of the test, measure the CPU utilization and memory utilization of the router.
2.
Use the following traffic profile.
•
HTTP: 75% of the traffic
•
FTP: 10% of the traffic
•
SMTP: 10% of the traffic
•
DNS: 5% of the traffic
For HTTP, use two different object sizes:
•
16-KB object size for large html files (10 URLs)
•
4-KB object size for transactional type data
For FTP, use a 1-MB file size.
For SMTP, use a 4-KB fixed object size.
For DNS, use 89 bytes.
3.
Start the traffic to achieve line rate on the primary WAN interface.
4.
Record the router performance metrics such as CPU, processor and I/O memory utilization, and LAN/WAN throughput.
5.
Do not generate any threats to the router during the performance test.
6.
Start adding the features incrementally and measure performance. Take at least five measurements, 3 minutes apart, before turning on the next feature.
7.
When all the features are added, check whether the router CPU utilization is less than or equal to 75% with line rate traffic. If it is greater than the 75%, tune the traffic to reach 75% CPU utilization, with a tolerance of +/- 2%.
8.
At 75% CPU utilization, take performance readings of the router every 3 minutes for a duration of 1 hour.
9.
Stop all traffic at the end of the hour. Wait for about 30 minutes, and take router memory readings. Use the show memory debug leaks command to determine whether there were any memory leaks during the test.
10.
Collect the following performance readings:
•
Router CPU utilization at 5 seconds, 1 minute, and 5 minutes, using the show proc cpu command
•
Router memory, using the show mem free and show proc mem commands
•
Interface statistics, using the show interface summary command
•
Cisco Express Forwarding switching statistics, using the show interfaces stats command
11.
Also record the following feature-specific measurements:
•
QoS: show policy-map interface command
•
IPsec: show crypto engine connections active command
•
ZPF: show policy-map type inspect command
•
NAT: show ip nat statistics command
•
NetFlow: show ip cache flow command
•
Multicast: show ip mroute count command
•
NBAR: show ip nbar protocol-discovery command
•
IPS: show ip ips statistics command
There are no router tracebacks.
There are no router memory leaks.
There are no router crashes.
Most of the traffic should be Cisco Express Forwarding switched.
Passed
Baseline Plus Voice Performance Test with Cisco Unified CME
Enable all the baseline services in the branch and headend routers. The baseline features include BGP routing, OSPF/EIGRP routing, IPsec using DMVPN or GETVPN, ZPF, NAT, IPS, QoS, NBAR, ACL, NetFlow, DHCP, AAA RADIUS server, NTP, syslog, SNMP, PIM-v2, and IGMP v2.
Configure L2 and L3 switching on the access and distribution layer switches.
Enable QoS on the L3 distribution switches.
Enable Cisco Unified CME on the branch router.
Measure the performance of the branch router in terms of CPU utilization, throughput of WAN and LAN interfaces, and processor and IO memory consumption.
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Before the start of the test, measure the CPU utilization and memory utilization of the router.
2.
Register 240 phones to Cisco Unified CME on the Cisco 3945 platform.
3.
Register 160 phones to Cisco Unified CME on the Cisco 3925 platform.
4.
Configure dual lines for all the phones.
5.
Use the following voice traffic profiles:
•
For T3 WAN bandwidth or Gigabit Ethernet WAN rate limited to 50 Mb/s
–
On the Cisco 3945 platform:
18 voice calls over WAN with G.711u-law codec
2 384k H.263 video calls over WAN
4 calls with transcoding (DSP farm assist)
2 three-party conferences
12 calls to PSTN over PRI
80 local calls
–
On the Cisco 3925 platform:
13 voice calls over WAN with G.711u-law codec
1 384k H.263 video call over WAN
2 calls with transcoding
1 three-party conference
6 calls to PSTN over PRI
56 local calls
•
For 4 T1 or 8-Mb/s bandwidth:
–
On the Cisco 3945 platform:
20 voice calls over the WAN with G.729r8 codec
1 384-KB video call over the WAN
2 transcoding sessions
1 three-party conference
80 local calls
–
On the Cisco 3925 platform:
12 voice calls over the WAN with G.729r8 codec
1 384-KB video call over the WAN
2 transcoding sessions
1 three-party conference
80 local calls
•
Call duration of voice and video calls is 180 seconds with intercall delay of 10 seconds.
•
Call duration for conferences is 10 minutes.
6.
Use the following data traffic profile:
•
HTTP: 75% of the traffic
•
FTP: 10% of the traffic
•
SMTP: 10% of the traffic
•
DNS: 5% of the traffic
For HTTP, use two different object sizes:
•
16-KB object size for large HTML files (10 URLs)
•
4-KB object size for transactional type data (10 URLs)
For FTP, use a 1-MB file size.
For SMTP, use 4-KB fixed object size.
For DNS, use 89 bytes.
7.
Start all the voice and video calls. When the calls have stabilized, take a couple of CPU measurements 3 minutes apart. Stop all the voice and video traffic.
8.
Start the data traffic and take a CPU utilization measurement after stabilization. The CPU utilization measurement should be very close to 75% as measured in the baseline performance test.
9.
Adjust the data traffic throughput to accommodate all the voice and video traffic, while maintaining 75% CPU utilization. When the router has stabilized, take performance readings for about 1 hour, and stop all the traffic. Wait for about 30 minutes to record the memory readings.
10.
In addition to the metrics mentioned in the Baseline Performance Test, collect the following metrics:
•
Calls-per-second rate
•
Voice and video call completion rate
•
Throughput in bits per second
There are no router tracebacks.
There are no router memory leaks.
There are no router crashes.
Most of the traffic should be Cisco Express Forwarding switched.
Passed
Baseline Plus Voice Performance Test with Cisco Unified CM and Cisco Unified SRST
Enable all the baseline services in the branch and headend routers. The baseline features include BGP routing, OSPF/EIGRP routing, IPsec using DMVPN or GETVPN, ZPF, NAT, IPS, QoS, NBAR, ACL, NetFlow, DHCP, AAA Radius server, NTP, syslog, SNMP, PIM-v2, and IGMP v2.
Configure L2 and L3 switching on the access and distribution layer switches.
Enable QoS on the L3 distribution switches.
Enable Cisco Unified SRST on the branch router.
Measure the performance of the branch router in terms of CPU utilization, throughput of WAN and LAN interfaces, and processor and IO memory consumption.
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Before the start of the test, measure the CPU utilization and memory utilization of the router.
2.
Register 240 phones to Cisco Unified CM for the Cisco 3945 branch.
3.
Register 160 phones to Cisco Unified CM for the Cisco 3925 branch.
4.
Configure dual lines for all the phones.
5.
Use the following voice traffic profiles.
•
For T3 WAN bandwidth or Gigabit Ethernet WAN rate limited to 50 Mb/s.
–
On Cisco 3945 platform:
18 voice calls over WAN with G.711u-law codec
2 384-KB H.263 video calls over WAN
4 calls with transcoding (DSP farm assist)
2 three-party conferences
12 calls to PSTN over PRI
80 local calls
–
On the Cisco 3925 platform:
13 voice calls over WAN with G.711u-law codec
1 384-KB H.263 video call over WAN
2 calls with transcoding
1 three-party conference
6 calls to PSTN over PRI
56 local calls
•
For 4 T1 or 8-Mb/s bandwidth:
–
On the Cisco 3945 platform:
20 voice calls over the WAN with G.729r8 codec
1 384-KB video call over the WAN
2 transcoding sessions
1 three-party conference
80 local calls
–
On the Cisco 3925 platform:
12 voice calls over the WAN with G.729r8 codec
1 384-KB video call over the WAN
2 transcoding sessions
1 three-party conference
80 local calls
•
Call duration of voice and video calls is 180 seconds with intercall delay of 10 seconds.
•
Call duration for conferences is 10 minutes.
6.
Use the following data traffic profile:
•
HTTP: 75% of the traffic
•
FTP: 10% of the traffic
•
SMTP: 10% of the traffic
•
DNS: 5% of the traffic
For HTTP, use two different object sizes:
•
16-KB object size for large HTML files (10 URLs)
•
4-KB object size for transactional type data (10 URLs)
For FTP, use a 1-MB file size.
For SMTP, use 4-KB fixed object size.
For DNS, use 89 bytes.
7.
Start all the voice and video calls. When the calls have stabilized, take a couple of CPU utilization measurements 3 minutes apart. Stop all the voice and video traffic.
8.
Start the data traffic, and take CPU utilization measurement after stabilization. The CPU utilization measurement should be very close to 75% as measured in the baseline performance test.
9.
Adjust the data traffic throughput to accommodate all the voice and video traffic, while maintaining 75% CPU utilization. When the router has stabilized, take performance readings for about 1 hour and stop all the traffic. Wait for about 30 minutes to record the memory readings.
10.
In addition to the metrics mentioned in the Baseline Performance Test, collect the following metrics:
•
Calls per second rate
•
Voice and video call completion rate
•
Throughput in bits per second
There are no router tracebacks.
There are no router memory leaks.
There are no router crashes.
Most of the traffic should be Cisco Express Forwarding switched.
Passed
Baseline Plus Voice Plus Cisco WAAS Performance Test
Enable all the baseline services in the branch and headend routers. The baseline features include BGP routing, OSPF/EIGRP routing, IPsec using DMVPN or GETVPN, ZPF, NAT, IPS, QoS, NBAR, ACL, NetFlow, DHCP, AAA RADIUS server, NTP, syslog, SNMP, PIM-v2, and IGMP v2.
Configure L2 and L3 switching on the access and distribution layer switches.
Enable QoS on the L3 distribution switches.
Enable Cisco Unified SRST on the branch router.
Enable Cisco WCCPv2 and Cisco WCCP 61 and 62 on the branch router.
Set up the Cisco WAAS module to do WAN optimization.
Measure the performance of the branch router in terms of CPU utilization, throughput of WAN and LAN interfaces, and processor and IO memory consumption.
Figure 1, Private WAN, Cisco Unified CME Mode, or
Figure 2, Private WAN, Cisco Unified SRST Mode, or
Figure 3, MPLS WAN, Cisco Unified CME Mode, or
1.
Before the start of the test, measure the CPU utilization and memory utilization of the router.
2.
Initially disable WAN optimization.
3.
Start the data traffic, and take a CPU utilization measurement after stabilization. The CPU utilization measurement should be very close to 75% as measured in the baseline performance test.
4.
Enable the WAN optimization, and run the baseline performance test again. Measure the CPU utilization. Since Cisco WAAS optimizes the TCP traffic, the CPU utilization may be lower than 75%. Record CPU measurements. Stop the data traffic.
5.
Start all the voice and video calls. When the calls have stabilized, take a couple of CPU utilization measurements 3 minutes apart. Stop all the voice and video traffic.
6.
Adjust the data traffic throughput to accommodate all the voice and video traffic, while maintaining 75% CPU utilization. When the router has stabilized, take performance readings for about 1 hour, and stop all the traffic. Wait for about 30 minutes to record the memory readings.
7.
In addition to the metrics mentioned in the Baseline Plus Voice Performance Test with Cisco Unified CME, collect the following metrics:
•
TFO statistics in the Cisco WAAS module
•
DRE statistics in the Cisco WAAS module
There are no router tracebacks.
There are no router memory leaks.
There are no router crashes.
Most of the traffic should be Cisco Express Forwarding switched.
The system throughput achieved should be higher than in the Baseline Plus Voice Performance Test with Cisco Unified CME or the Baseline Plus Voice Performance Test with Cisco Unified CM and Cisco Unified SRST.
Passed