Table Of Contents
Cisco Security Control Framework (SCF) Model
Cisco Security Control Framework
Organizing Controls with the Cisco SCF
Example Controls, Techniques, and Technologies Mapping
Cisco Security Control Framework (SCF) Model
Contents
Introduction
The IT infrastructure architecture must be designed and implemented with security at its core in order to enable key business activities, while ensuring the confidentiality, integrity, and availability of the IT infrastructure and critical business and customer data. An organization's security requirements are derived from many sources, including organization goals and objectives, industry and international standards, and industry and government regulations. The process of designing, implementing, and operating an infrastructure that meets these business and security requirements benefits from the application of a coherent model to view and organize the myriad security control requirements.
The Cisco Security Control Framework (SCF) model defines a structure of security objectives and supporting security actions to organize security controls. The Cisco SCF model is based on proven industry best practices and security architecture principles, and the vast practical experience of Cisco engineers in designing, implementing, assessing, and managing service provider, enterprise, and small and medium-sized business (SMB) infrastructures. Using the Cisco SCF model, organizations can align security requirements and controls into logical groups to facilitate the understanding and communication of the control architecture for their IT infrastructure.
The organization of the Cisco SCF model is designed to increase the focus on three primary goals related to the security of the IT infrastructure and assets. These goals are as follows:
•
Protect the IT infrastructure
•
Protect the IT assets using network-based controls
•
Mitigate and respond to security incidents using network-based controls
The design of the Cisco SCF model brings together the regulation- and standards-based requirements with fundamental architectural principles, industry best practices, and a wide breadth of engineering experience from inside and outside of Cisco. The result is a vendor-agnostic model that supports the organization and definition of control sets to meet each organization's specific objectives.
Terms and Definitions
Table 1 defines the terms relevant to the Cisco SCF model.
Cisco Security Control Framework
The Cisco SCF is composed of a model, methodology, control structure, and control sets designed to support the assessment of technical risk in an infrastructure architecture. The Cisco SCF integrates into an ongoing process of continuous improvement to incrementally improve the security posture of the infrastructure architecture to address current key threats and to identify, track, and defend against new and evolving threats. The Cisco SCF's ability to do this is its base of sound architectural principles rather than a focus on specific individual threats, technologies, vendor products, or implementation configurations.
The Cisco SCF is composed of the following three sections:
•
Model (addressed in this document)
The model defines the security objectives and their supporting security actions as a mechanism to organize individual controls and address the underlying architectural principles.
•
Control Structure (not addressed in this document)
The control structure defines the organization of individual controls and control sets and how they relate to the Cisco SCF model and methodology.
•
Methodology (Not addressed in this document)
The methodology defines the primary steps required to conduct a security architecture assessment using the Cisco SCF. The structure of controls, the scoring process, and the mechanism for aggregating these scores into meaningful results are also defined in the methodology.
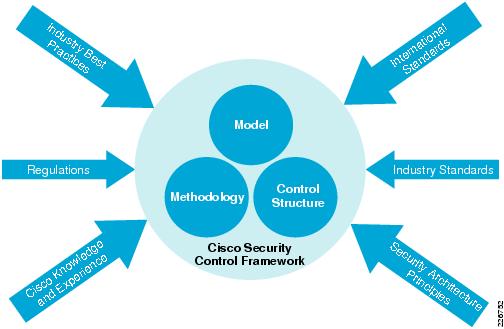
The model and methodology sections provide the overall architecture for the Cisco SCF, including the various components, the interactions between the components, and the way in which components should be used to achieve the specific security objectives of an infrastructure security architecture assessment. As such, the Cisco SCF is not a design or implementation, but consist of guidelines—a set of rules or a playbook used to assess architectures in an orderly manner. Well-defined security infrastructure architectures, based on key foundational principles, have proven to be more robust and tolerant, surviving changes in technology, organizational boundaries, and external influences. The Cisco SCF is designed to be configurable and extensible through the definition and use of the appropriate control sets for a specific assessment's objectives and business environment. Figure 1 summarizes the components of the Cisco SCF and the major sources of influence on its design.
Figure 1 Cisco Security Control Framework
Cisco SCF Model
The Cisco SCF model is the application of foundational security principles to define the guidelines and rules for achieving a secure infrastructure. The security architecture does not define how to build or implement a secure infrastructure, but instead defines the properties, capabilities, processes, and controls that a secure infrastructure must possess to protect against a range of threats. The Cisco SCF model provides a useful organizational structure to capture the architectural aspects that the foundational principles require.
The definition of the Cisco SCF model starts with the fundamental security principles as summarized in Table 2. These fundamental principles are factored into the security objectives and security actions that define the Cisco SCF model.
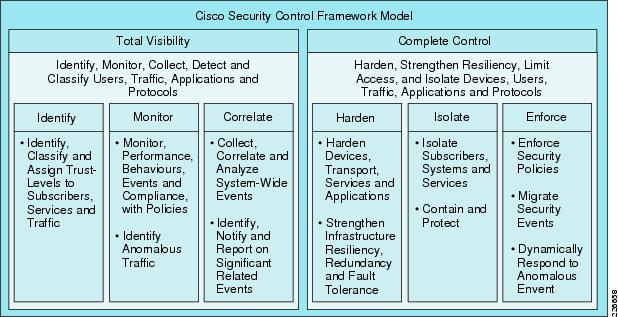
The Cisco SCF model defines the two fundamental security objectives of total visibility and complete control. The success of a security architecture and infrastructure implementation ultimately depends on the degree to which they enhance visibility and control. Without visibility there is no control and without control there is no security. Therefore, the Cisco SCF's main focus is on security actions and the underlying controls that enhance the fundamental principles of visibility and control. In practice, the Cisco SCF is used to drive the selection and deployment of platforms and capabilities to achieve a desirable degree of visibility and control. The definitions of visibility and control are elaborated in the following section.
Security Objectives
The Cisco SCF defines six security actions that support security objectives by improving visibility and control. The actions, three each for visibility and control, define logical groupings for organizing the more detailed security controls. Figure 2 depicts the six security actions and their relationships with the visibility and control objectives.
Figure 2 Cisco Security Control Framework Model
The following descriptions outline key considerations for total visibility and complete control.
Total Visibility
Total visibility consists of the following elements: identity, trust, compliance, event monitoring, and performance monitoring. Key considerations for total visibility include the following:
•
Identifying and classifying users, traffic, applications, protocols, and usage behavior
•
Monitoring and recording activity and patterns
•
Collecting and correlating data from multiple sources to identify trends, and system-wide events
•
Detecting and identifying anomalous traffic and threats
Complete Control
Complete control consists of hardening individual devices, increasing the resiliency of the network, isolating users, systems and services, security policy enforcement, and event mitigation. Key considerations for complete control include the following:
•
Hardening IT infrastructure, including individual devices and increasing network resiliency
•
Limiting access and usage per user, protocol, service, and application
•
Isolating users, services, and applications
•
Protecting against known threats and exploits
•
Dynamically reacting in response to anomalous events
Security Actions
Security actions provide organizational groupings of related attributes, capabilities, and functionality required in a security architecture to support a security objective. These security actions are described in the following subsections.
Total Visibility
The total visibility security objective is supported by the identify, monitor, and correlate security actions described in the following subsections.
Identify
The identify controls deliver the capabilities for a system to identify and classify entities accessing a given resource and to then determine a trust level or state of trust for that entity. Usually, trust is established through mechanisms other than inspection of an IP address, including inspection of credentials. Identifying an entity applies to traffic from within the network and possibly external traffic entering a network.
Monitor
The monitor controls address the fundamental capabilities and instrumentation to facilitate security visibility, combined with the ability to monitor the behavior and usage of the infrastructure components, including resources, connected systems, users, applications, and IP traffic.
Correlate
The correlate controls focus on the ability of the system to derive and present intelligence related to the state of the infrastructure based on correlation and management of visibility data.
Correlation is the interpretation, dissemination, analysis, and classification of visibility data into meaningful operational information through the contextualization of seemingly unrelated events or changes. From a security operations perspective, it provides the foundation to apply policy enforcement and isolation controls.
Management is the ability to represent visually, in near real-time, the intelligence derived from various network elements including audit logs, event monitoring, fault knowledge, and health/status information.
Complete Control
The complete control security objective is supported by the harden, isolate, and enforce security actions described in the following subsections.
Harden
The harden controls address the ability of an infrastructure to withstand, adjust to and/or recover from adverse uncontrolled circumstances. Hardening includes both securing individual devices and the infrastructure as a whole through increased resilience, fault tolerance, route duplication and other means.
Isolate
The isolate controls focus on the ability of a system to limit the scope and minimize the impact upon users, services, and systems from known and unknown disturbances. Implementation of the isolate controls provides the ability to isolate logical and physical functional blocks of an infrastructure into security zones to control or to prevent access between the functional blocks in the infrastructure and to limit the scope of security breech exploitation.
Enforce
The enforce controls deliver the capabilities required to enforce the allowed behavior of connected systems, users, applications, and IP traffic. Policy enforcement may either be static (a control is applied on a permanent basis) or dynamic (a control is applied to specifically mitigate some discrete event or security incident).
Organizing Controls with the Cisco SCF
This section provides examples of the types of control techniques and technologies that are mapped to each of the security actions. This list is provided as an example to help describe the scope and intent of each of the security actions and to help define different specific controls that address the required attributes, capabilities, or functions of the security actions.
Example Controls, Techniques, and Technologies Mapping
Total Visibility
Identify
•
Identity-based network solutions (802.1x, NAC, and so on)
•
Authentication, Authorization, and Accounting (AAA)—Authentication
•
Biometric recognition
•
Routing authentication (MD5)
•
Secure messaging (encrypted E-mail)
•
VPN authentication
–
Digital certificates
–
Pre-shared keys
–
User authentication
Monitor
•
AAA—Accounting
•
Anomaly Detection System
•
Intrusion Detection System (IDS) and Intrusion Prevention System (IPS)
•
Network flow data collection
•
Simple Network Management Protocol (SNMP)/Remote Monitoring (RMON)/Management Information Base (MIB)
–
CPU, memory threshold
•
Syslog
–
Topologies: Cisco Discovery Protocol (CDP); routing protocols; multiprotocol label switching (MPLS) Label Distribution Protocol (LDP)
•
Sinkholes
Correlate
•
Analysis of network flow data (Arbor, Cisco Security Monitoring, Analysis, and Response System (CS-MARS), and so on)
•
Host intrusion protection event correlation
•
Security incident management system
•
Event analysis and correlation
–
Syslog
–
SNMP
–
AAA
–
Antivirus
•
Network Time Protocol (NTP) synchronization
Complete Control
Harden
•
Control plane policing
•
Device hardening
–
Disable unused services
–
Latest patch level
–
Restrict device accessibility
•
Component redundancy
–
Power supply
–
Link and interface
•
Device redundancy
•
Topology redundancy
Isolate
•
Firewall access control policies
•
Network and segment isolation
•
Out of band management
•
VPN encryption
•
Management traffic encryption—Secure Shell (SSH), SNMP, and so on
•
Virtual LAN (VLAN)
Enforce
•
Content filtering
•
Distributed-denial-of-service (DDoS) protection
•
Host intrusion prevention
•
Port security
•
Quality-of-Service (QoS) enforcement
•
Network access control
–
Access control lists (ACL), filters
–
Unicast reverse path forwarding (uRFP)
–
Anti-spoofing
•
Policy-based routing
•
AAA authorization
CCDE, CCENT, Cisco Eos, Cisco HealthPresence, the Cisco logo, Cisco Lumin, Cisco Nexus, Cisco StadiumVision, Cisco TelePresence, Cisco WebEx, DCE, and Welcome to the Human Network are trademarks; Changing the Way We Work, Live, Play, and Learn and Cisco Store are service marks; and Access Registrar, Aironet, AsyncOS, Bringing the Meeting To You, Catalyst, CCDA, CCDP, CCIE, CCIP, CCNA, CCNP, CCSP, CCVP, Cisco, the Cisco Certified Internetwork Expert logo, Cisco IOS, Cisco Press, Cisco Systems, Cisco Systems Capital, the Cisco Systems logo, Cisco Unity, Collaboration Without Limitation, EtherFast, EtherSwitch, Event Center, Fast Step, Follow Me Browsing, FormShare, GigaDrive, HomeLink, Internet Quotient, IOS, iPhone, iQuick Study, IronPort, the IronPort logo, LightStream, Linksys, MediaTone, MeetingPlace, MeetingPlace Chime Sound, MGX, Networkers, Networking Academy, Network Registrar, PCNow, PIX, PowerPanels, ProConnect, ScriptShare, SenderBase, SMARTnet, Spectrum Expert, StackWise, The Fastest Way to Increase Your Internet Quotient, TransPath, WebEx, and the WebEx logo are registered trademarks of Cisco Systems, Inc. and/or its affiliates in the United States and certain other countries.
All other trademarks mentioned in this document or website are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (0812R)