Feedback Feedback
|
Table Of Contents
Release Notes for Cisco Identity Services Engine, Release 1.1.x
Node Types, Personas, Roles, and Services
Cisco ISE Deployment Terminology
Supported Virtual Environments
Supported Devices, Browsers, and Agents
Supported Microsoft Active Directory
Upgrade from Cisco ISE, Release 1.1.3 to release 1.1.4
Upgrade from Cisco ISE, Release 1.1.2 to release 1.1.3
Upgrade from Cisco ISE, Release 1.1.1 to release 1.1.3
Upgrade from Cisco ISE, Release 1.1.1 to release 1.1.2
Upgrade from Cisco ISE, Release 1.1 to release 1.1.1
Upgrade from Cisco ISE, Release 1.0.4 to 1.1.1 with Inline Posture
Upgrade from Cisco ISE, Release 1.0.3.377
Cisco Secure ACS to Cisco ISE Migration
New Features in Cisco ISE, Release 1.1.4
New Features in Cisco ISE, Release 1.1.3
New Features in Cisco ISE, Release 1.1.2
Global Setting for Endpoint Attribute Filter
New Features in Cisco ISE, Release 1.1.1
New Default Authorization Profile ("Blacklist")
Dictionary Attribute-to-Attribute Authorization Policy Configuration
New Device Registration Task Navigator
Native Supplicant Provisioning Profile Configuration Page
Enhanced Client Provisioning Policy Configuration
SCEP Authority Profile Configuration Page
EAP-TLS as an Inner Method for EAP-FAST
New Reports in Cisco ISE, Release 1.1.1
Cisco ISE Install Files, Updates, and Client Resources
Cisco ISE Downloads from the Cisco Download Software Center
Support for Windows 8.1 and Mac OS X 10.9
Cisco ISE, Release 1.1.4 Patch Updates
Resolved Issues in Cisco ISE Version 1.1.4.218—Cumulative Patch 8
Resolved Issues in Cisco ISE Version 1.1.4.218—Cumulative Patch 7
Resolved Issues in Cisco ISE Version 1.1.4.218—Cumulative Patch 6
Resolved Issues in Cisco ISE Version 1.1.4.218—Cumulative Patch 5
Resolved issues in Cisco ISE Version 1.1.4.218—Cumulative Patch 4
Resolved issues in Cisco ISE Version 1.1.4.218—Cumulative Patch 3
Resolved Issues in Cisco ISE Version 1.1.4.218—Cumulative Patch 2
Resolved Issues in Cisco ISE Version 1.1.4.218—Cumulative Patch 1
Cisco ISE, Release 1.1.3 Patch Updates
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 8
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 7
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 6
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 5
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 4
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 3
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 2
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 1
Cisco ISE, Release 1.1.2 Patch Updates
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 10
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 9
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 8
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 7
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 6
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 5
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 4
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 3
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 2
Cisco ISE, Release 1.1.1 Patch Updates
Resolved Issues in Cisco ISE Version 1.1.1.268—Cumulative Patch 7
Resolved Issues in Cisco ISE Version 1.1.1.268—Cumulative Patch 6
Resolved Issues in Cisco ISE Version 1.1.1.268—Cumulative Patch 5
Resolved Issues in Cisco ISE Version 1.1.1.268—Cumulative Patch 4
Resolved Issues in Cisco ISE Version 1.1.1.268—Cumulative Patch 3
Resolved Issues in Cisco ISE Version 1.1.1.268—Cumulative Patch 2
Resolved Issues in Cisco ISE Version 1.1.1.268—Cumulative Patch 1
Cisco ISE Antivirus and Antispyware Support
Cisco NAC Agent Interoperability Between NAC Appliance and Identity Services Engine
Integration with Cisco Prime Network Control System
Cisco ISE Release 1.1.x Open Caveats
Cisco ISE Release 1.1.x Resolved SPW Caveats
Cisco ISE Release 1.1.4 Resolved Caveats
Cisco ISE Release 1.1.3 Resolved Caveats
Cisco ISE Release 1.1.2 Resolved Caveats
Cisco ISE Release 1.1.1 Resolved Caveats
Cisco ISE Hostname Character Length Limitation with Active Directory
Windows Internet Explorer 8 Known Issues
Issues With 2k Message Size in Monitoring and Troubleshooting
Issues With More Than Three Users Accessing Monitoring and Troubleshooting Concurrently
Cisco IP phones using EAP-FAST
Internationalization and Localization
Issues with Monitoring and Troubleshooting Restore
Obtaining Documentation and Submitting a Service Request
Release Notes for Cisco Identity Services Engine, Release 1.1.x
Revised: November 11, 2013, OL-26136-01These release notes describe the features, limitations and restrictions (caveats), and related information for Cisco Identity Services Engine (Cisco ISE), Release 1.1.1, 1.1.2, 1.1.3, and 1.1.4. These release notes supplement the Cisco ISE documentation that is included with the product hardware and software release.
Cisco Identity Services Engine, Release 1.1.4
Cisco ISE, Release 1.1.4 provides support for the Cisco SNS-3400 Series appliance. In addition to the hardware support for installation on the SNS-3400 Series appliance, Cisco ISE 1.1.4 supports all the features in Cisco ISE 1.1.3. You can also install Cisco ISE 1.1.4 on previously supported appliances, such as ISE-3315-K9, ISE-3355-K9, and ISE-3395-K9.
Cisco Identity Services Engine, Release 1.1.3
Cisco ISE, Release 1.1.3 features critical bug fixes derived from Cisco ISE, Release 1.0.4, 1.1, 1.1.1, and 1.1.2 while rolling patch fixes for Cisco ISE, Release 1.1.1 and 1.1.2 into 1.1.3.
Cisco Identity Services Engine, Release 1.1.2
Cisco ISE, Release 1.1.2 features critical bug fixes derived from Cisco ISE, Release 1.0.4, 1.1, and 1.1.1, while rolling three patch fixes for Cisco ISE, Release 1.1.1 into 1.1.2.
Cisco Identity Services Engine, Release 1.1.1
Cisco ISE, Release 1.1.1 features a number of important product function enhancements and new capabilities, as well as critical bug fixes derived from Cisco ISE, Release 1.0.4 and 1.1.
Contents
•
Node Types, Personas, Roles, and Services
•
Installing Cisco ISE Software
•
Cisco Secure ACS to Cisco ISE Migration
•
Cisco ISE License Information
•
New Features in Cisco ISE, Release 1.1.4
•
New Features in Cisco ISE, Release 1.1.3
•
New Features in Cisco ISE, Release 1.1.2
•
New Features in Cisco ISE, Release 1.1.1
•
Cisco ISE Install Files, Updates, and Client Resources
•
Support for Windows 8.1 and Mac OS X 10.9
•
Cisco ISE, Release 1.1.4 Patch Updates
•
Cisco ISE, Release 1.1.3 Patch Updates
•
Cisco ISE, Release 1.1.2 Patch Updates
•
Cisco ISE, Release 1.1.1 Patch Updates
•
Cisco ISE Antivirus and Antispyware Support
•
Cisco ISE Release 1.1.x Open Caveats
•
Cisco ISE Release 1.1.x Resolved SPW Caveats
•
Cisco ISE Release 1.1.4 Resolved Caveats
•
Cisco ISE Release 1.1.3 Resolved Caveats
•
Cisco ISE Release 1.1.2 Resolved Caveats
•
Cisco ISE Release 1.1.1 Resolved Caveats
Introduction
The Cisco ISE platform is a comprehensive, next-generation, contextually-based access control solution. Cisco ISE offers authenticated network access, profiling, posture, guest management, and security group access services along with monitoring, reporting, and troubleshooting capabilities on a single physical or virtual appliance. Cisco ISE ships on a range of physical appliances with different performance characterization and also allows the addition of more appliances to a deployment for performance, scale, and resiliency. Cisco ISE has a highly available and scalable architecture that supports standalone and distributed deployments, but with centralized configuration and management. Cisco ISE also allows for configuration and management of distinct Cisco ISE personas and services. This feature gives you the ability to create and apply Cisco ISE services where they are needed in the network, but still operate the Cisco ISE deployment as a complete and coordinated system.
Node Types, Personas, Roles, and Services
Cisco ISE provides a highly available and scalable architecture that supports both standalone and distributed deployments. In a distributed environment, you configure one primary Administration node and the rest are secondary nodes. The topics in this section provide information about Cisco ISE terminology, supported node types, distributed deployment, and the basic architecture.
Cisco ISE Deployment Terminology
Table 1 describes some of the common terms used in Cisco ISE deployment scenarios.
Types of Nodes and Personas
A Cisco ISE network has only two types of nodes:
•
Cisco ISE node—An ISE node could assume any of the following three personas:
–
Administration—Allows you to perform all administrative operations on Cisco ISE. It handles all system-related configuration and configurations related to functionality such as authentication, authorization, auditing, and so on. In a distributed environment, you can have only one or a maximum of two nodes running the Administration persona. The Administration persona can take on any one of the following roles: standalone, primary, or secondary. If the primary Administration node goes down, you have to manually promote the secondary Administration node. There is no automatic failover for the Administration persona.
–
Policy Service—Provides network access, posture, guest access, and profiling services. This persona evaluates the policies and makes all the decisions. You can have more than one node assuming this persona. Typically, there would be more than one Policy Service persona in a distributed deployment. All Policy Service personas that reside behind a load balancer share a common multicast address and can be grouped together to form a node group. If one of the nodes in a node group fails, the other nodes in that group process the requests of the node that has failed, thereby providing high availability.
Note
At least one node in your distributed setup should assume the Policy Service persona.
–
Monitoring—Enables Cisco ISE to function as the log collector and store log messages from all the Administration and Policy Service personas on the ISE nodes in your network. This persona provides advanced monitoring and troubleshooting tools that you can use to effectively manage your network and resources.
A node with this persona aggregates and correlates the data that it collects to provide you with meaningful information in the form of reports. Cisco ISE allows you to have a maximum of two nodes with this persona that can take on primary or secondary roles for high availability. Both the primary and secondary Monitoring personas collect log messages. In case the primary Monitoring persona goes down, the secondary Monitoring persona automatically assumes the role of the primary Monitoring persona.
Note
At least one node in your distributed setup should assume the Monitoring persona. It is recommended that the Monitoring persona be on a separate, designated node for higher performance in terms of data collection and report launching.
•
Inline Posture node—A gatekeeping node that is positioned behind network access devices such as wireless LAN controllers (WLCs) and virtual private network (VPN) concentrators on the network. Inline Posture enforces access policies after a user has been authenticated and granted access, and handles Change of Authorization (CoA) requests that a WLC or VPN are unable to accommodate. Cisco ISE allows up to 10,000 Inline Posture Nodes in a deployment. You can pair two Inline Posture nodes together for high availability as a failover pair.
Note
An Inline Posture node is dedicated solely to that service, and cannot operate concurrently with other ISE services. Likewise, due to the specialized nature of its service, an Inline Posture node cannot assume any persona. Inline Posture nodes are not supported on VMware server systems.
Note
Each ISE node in a deployment can assume more than one of the three personas (Administration, Policy Service, or Monitoring) at a time. By contrast, each Inline Posture node operates only in a dedicated gatekeeping role.
The following table lists the recommended minimum and maximum number of nodes/personas in a distributed deployment:
•
One primary Administration node and one secondary Administration node
•
One primary Monitoring node, with an optional secondary node
•
One or more Policy Service nodes
•
One primary Inline Posture node, with an optional secondary node
You can change the persona of a node. See the "Setting Up ISE in a Distributed Environment" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x for information on how to configure these personas on Cisco ISE nodes.
Hardware Requirements
This section describes the following topics:
•
Supported Virtual Environments
•
Supported Devices, Browsers, and Agents
•
Supported Microsoft Active Directory
Note
For more details on Cisco ISE hardware platforms and installation, see the Cisco Identity Services Engine Hardware Installation Guide, Release 1.1.x.
Supported Hardware
Cisco ISE software is packaged with your appliance or image for installation. After installation, you can configure Cisco ISE as any of the specified component personas (Administration, Policy Service, and Monitoring) or as an Inline Posture node on the platforms that are listed in Table 3.
Table 3 Supported Hardware and Personas
Cisco ISE-3315-K9 (small)
Any
•
1x Xeon 2.66 GHz quad-core processor
•
4 GB RAM
•
4x 1 GB NIC3
Cisco ISE-3355-K9 (medium)
Any
•
1x Nehalem 2.0 GHz quad-core processor
•
4 GB RAM
•
2 x 300 GB 2.5 in. SATA HDD
•
RAID4 (disabled)
•
4x 1 GB NIC
•
Redundant AC power
Cisco ISE-3395-K9 (large)
Any
•
2x Nehalem 2.0 GHz quad-core processor
•
4 GB RAM
•
4 x 300 GB 2.5 in. SAS II HDD
•
RAID 1
•
4x 1 GB NIC
•
Redundant AC power
Cisco SNS-3415-K9
Any
Inline Posture is not supported
•
Cisco UCS C220 M3
•
Single socket Intel E5-2609 2.4Ghz CPU, 4 total cores, 4 total threads
•
16-GB RAM
•
1 x 600-GB disk
•
No RAID
•
4 GE network interfaces
Cisco SNS-3495-K9
Stand-alone Administration, Monitoring, and Policy Service
Inline Posture is not supported
•
Cisco UCS C220 M3
•
Dual socket Intel E5-2609 2.4Ghz CPU, 8 total cores, 8 total threads
•
32-GB RAM
•
2 x 600-GB disk
•
RAID 0+1
•
4 GE network interfaces
Cisco ISE-VM-K9 (VMware)
Stand-alone Administration, Monitoring, and Policy Service (no Inline Posture)
•
CPU—Intel Dual-Core; 2.13 GHz or faster
•
Memory—4 GB RAM5
•
Hard Disks (minimum allocated memory):
–
Stand-alone—600 GB
–
Administration—200 GB
–
Policy Service and Monitoring—600 GB
–
Monitoring—500 GB
–
Policy Service—100 GB
Note
For an evaluation and demo purposes, the minimum required disk space is 60 GB to support 100 endpoints. Cisco does not recommend allocating any more than 600 GB maximum space for any node.
•
NIC—1 GB NIC interface required (you can install up to 4 NICs)
•
Supported VMware versions include:
–
ESX 4.x
–
ESXi 4.x
–
ESXi 5.x
1 SATA = Serial Advanced Technology Attachment
2 HDD = hard disk drive
3 NIC = network interface card
4 RAID = redundant array of independent disks
5 Memory allocation of less than 4GB is not supported for any VMware appliance configuration. In the event of a Cisco ISE behavior issue, all users will be required to change allocated memory to at least 4GB prior to opening a case with the Cisco Technical Assistance Center.
If you are moving from Cisco Secure Access Control System (ACS) or Cisco NAC Appliance to Cisco ISE, the Cisco Secure ACS 1121 and Cisco NAC 3315 appliances support small deployments, Cisco NAC 3355 appliances support medium deployments, and Cisco NAC 3395 appliances support large deployments.
Supported Virtual Environments
Cisco ISE supports the following virtual environment platforms:
•
VMware ESX 4.x
•
VMware ESXi 4.x
•
VMware ESXi 5.x
Supported Devices, Browsers, and Agents
Refer to Cisco Identity Services Engine Network Component Compatibility, Release 1.1.x for information on supported devices, browsers, and agents.
Supported Microsoft Active Directory
Cisco ISE, Release 1.1.x is tested with Microsoft Active Directory servers 2003, 2003 R2, 2008, 2008 R2, and 2012 at all functional levels. Microsoft Active Directory version 2000 or its functional level are not supported by Cisco ISE.
FIPS Compliance
Product Cisco Identity Services Engine, Release 1.1.x uses embedded FIPS 140-2 validated cryptographic modules Cisco Common Cryptographic Module (Certificate #1643) and Network Security Services (NSS) Cryptographic Module (Certificate #1497) running on a Cisco ADE-OS platform. For details of the FIPS compliance claims, read the compliance letter for Cisco Identity Services Engine (ISE) 1.1 listed under Current Certifications at the following URL: http://wwwin.cisco.com/osp/gov/ggsg_eng/gct/fips.shtml.
Installing Cisco ISE Software
The following steps summarize how to install new Cisco ISE Release 1.1.x DVD software on supported hardware platforms (see Supported Hardware for support details).
With Cisco ISE Release 1.1.x, installation occurs in two phases:
1.
The software is installed using the following options:
•
For the Cisco ISE 3300 Series appliance, the software is installed from the DVD. When the installation completes, the DVD is ejected from the appliance.
•
For the Cisco ISE 3400 Series appliance (SNS 3415 or 3495 Hardware), the software is installed using CIMC or by creating a bootable USB drive to begin the installation process.
Note
For more information on using CIMC, refer to the following section in the ISE 1.1.4 Installation Guide: http://www.cisco.com/en/US/docs/security/ise/1.1.1/installation_guide/ise_ins.html#wp1136661. Also, see Configuring CIMC. For more information on the USB boot option, see Creating a Bootable USB Drive.
2.
The administrator logs in and performs the initial configuration.
You can re-image a Cisco SNS-3400 series appliance over the Cisco Integrated Management Controller Interface (CIMC) or with a USB key installation. You can download the ISE_114_USB_Installation_tools.zip file from the Cisco download page, unzip the file, and follow the instructions in the README.txt that is included with the zip file to create a bootable USB key.
The following sections describe how to configure CIMS and the process of creating a bootable USB key:
•
Creating a Bootable USB Drive
For more information on the Installation of ISE 3400 Series hardware, refer to the following sections in the ISE 1.1.4 Installation Guide:
•
http://www.cisco.com/en/US/docs/security/ise/1.1.1/installation_guide/ise_app_b-hw_ins_3400.html
•
http://www.cisco.com/en/US/docs/security/ise/1.1.1/installation_guide/ise_ins.html#wp1136661
Note
When using virtual machines (VMs), Cisco recommends that the guest VM have the correct time set using an NTP server before installing the .ISO image on the VMs.
Step 1
Log into Cisco Download Software at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm. You might be required to provide your Cisco.com login credentials.
Step 2
Navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software.
Step 3
Download the appropriate Cisco ISE .ISO image (for example. ise-1.1.1.268.i386.iso) and burn the image as a bootable disk to a DVD-R.
Step 4
Insert the bootable device.
•
For the Cisco ISE 3300 Series appliance, insert the DVD into the DVD-R drive of each appliance, and reboot the appliance to initiate the Cisco ISE DVD installation process.
•
For the Cisco ISE 3400 Series appliance, use the USB boot option to initiate the Cisco ISE installation process. For more information on the USB boot option, see Creating a Bootable USB Drive. For more information on CIMC, see Configuring CIMC.
Step 5
(If necessary) Install a valid FlexLM product license file and perform Cisco ISE initial configuration according to the instructions in the Cisco Identity Services Engine Hardware Installation Guide, Release 1.1.x. Before you run the setup program, ensure that you know the configuration parameters listed in Table 4.
Table 4 Identity Services Engine Network Configuration Parameters for Setup
Hostname
Must not exceed 19 characters. Valid characters include upper- and lower-case alphanumeric characters (A-Z, a-z, 0-9) with the requirement that the first character must be an alphabetic character.
isenode1
(eth0) Ethernet interface address
Must be a valid IPv4 address for the eth0 Ethernet interface.
10.12.13.14
Netmask
Must be a valid IPv4 address for the netmask.
255.255.255.0
Default gateway
Must be a valid IPv4 address for the default gateway.
10.12.13.1
DNS domain name
Cannot be an IP address. Valid characters include ASCII characters, any numbers, hyphen (-), and period (.).
mycompany.com
Primary name server
Must be a valid IPv4 address for the primary Name server.
10.15.20.25
Add/Edit another name server
Must be a valid IPv4 address for an additional Name server.
(Optional) Allows you to configure multiple Name servers. To do so, enter y to continue.
Primary NTP server
Must be a valid NTP server in a domain reachable from Cisco ISE.1
clock.nist.gov
Add/Edit another NTP server
Must be a valid NTP server in a domain reachable from Cisco ISE.1
(Optional) Allows you to configure multiple NTP servers. To do so, enter y to continue.
System Time Zone
Must be a valid time zone. Refer to the Cisco Identity Services Engine CLI Reference Guide, Release 1.1.x for a table of time zones that Cisco ISE supports. The default value is UTC.2
Note
The table lists the frequently used time zones. You can run the show timezone command from the Cisco ISE CLI for a complete list of supported time zones.
PST
Username
Identifies the administrative username used for CLI access to the Cisco ISE system. If you choose not to use the default, you must create a new username, which must be from 3 to 8 characters in length, and be composed of valid alphanumeric characters (A-Z, a-z, or 0-9).
admin (default)
Password
Identifies the administrative password used for CLI access to the Cisco ISE system. You must create this password (there is no default). The password must be a minimum of six characters in length and include at least one lowercase letter (a-z), at least one uppercase letter (A-Z), and at least one number (0-9).
MyIseYP@@ss
Database Administrator Password
Identifies the Cisco ISE database system-level password. You must create this password (there is no default). The password must be a minimum of 11 characters in length and include at least one lowercase letter (a-z), at least one uppercase letter (A-Z), and at least one number (0-9).
Note
Once you configure this password, Cisco ISE uses it "internally." That is, you do not have to enter it when logging into the system at all.
ISE4adbp@ss
Database User Password
Identifies the Cisco ISE database access-level password. You must create this password (there is no default). The password must be a minimum of 11 characters in length and include at least one lowercase letter (a-z), at least one uppercase letter (A-Z), and at least one number (0-9).
Note
Once you configure this password, Cisco ISE uses it "internally." That is, you do not have to enter it when logging into the system at all.
ISE5udbp@ss
1 Changing the NTP server specification after Cisco ISE installation will likely affect the entire deployment.
2 Changing the time zone specification after Cisco ISE installation will likely affect the entire deployment.
Note
For additional information on configuring and managing Cisco ISE, use the list of documents in Release-Specific Documents to access other documents in the Cisco ISE documentation suite.
Configuring CIMC
You can perform all operations on the Cisco ISE 3400 series appliances through the CIMC. To do this, you must first configure an IP address and IP gateway to access the CIMC from a web-based browser.
Step 1
Plug in the power cord.
Step 2
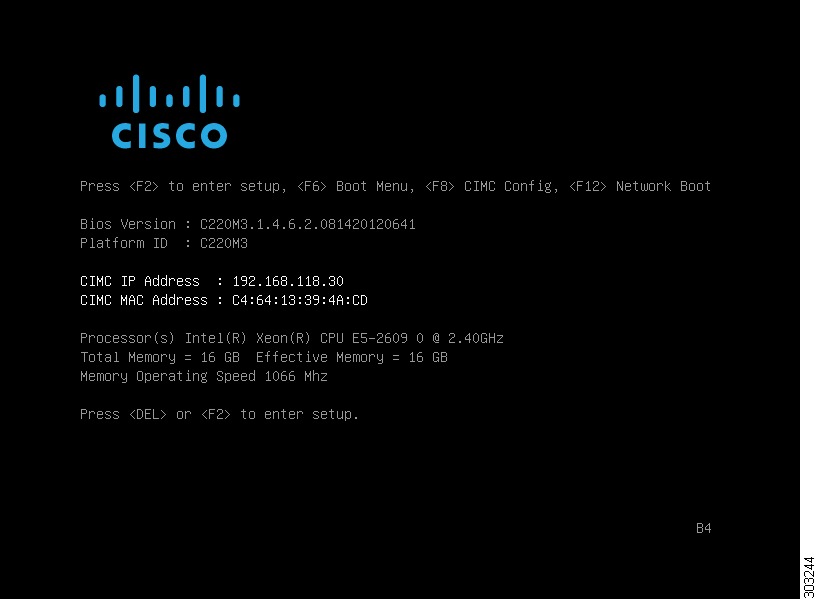
Press the Power button to boot the server. Watch for the prompt to press F8 as shown in TBD.
Step 3
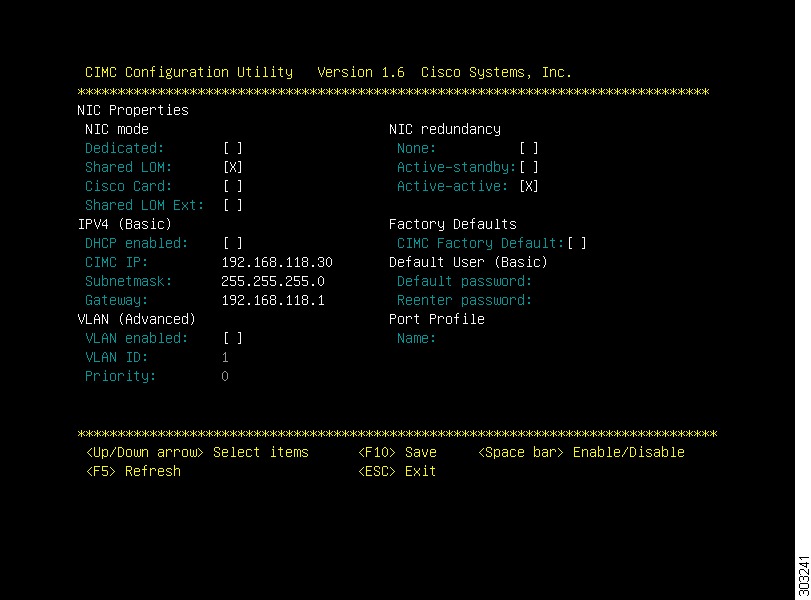
During boot up, press F8 when prompted to open the BIOS CIMC Configuration Utility. The following screen appears.
Step 4
Set the NIC mode to your choice for which ports to use to access the CIMC for server management (see Figure 1-3 on page 1-3 for identification of the ports):
–
Dedicated—The 1-Gb Ethernet management port is used to access the CIMC. You must select NIC redundancy None and select IP settings.
–
Shared LOM (default)—The two 1-Gb Ethernet ports are used to access the CIMC. This is the factory default setting, along with Active-active NIC redundancy and DHCP enabled.
–
Cisco Card—The ports on an installed Cisco UCS P81E VIC are used to access the CIMC. You must select a NIC redundancy and IP setting.
Note
The Cisco Card NIC mode is currently supported only with a Cisco UCS P81E VIC (N2XX-ACPCI01) that is installed in PCIe slot 1. Refer to the following section in the Cisco UCS C220 Server Installation and Service Guide: Special Considerations for Cisco UCS Virtual Interface Cards.
Step 5
Use this utility to change the NIC redundancy to your preference. This server has three possible NIC redundancy settings:
–
None—The Ethernet ports operate independently and do not fail over if there is a problem.
–
Active-standby—If an active Ethernet port fails, traffic fails over to a standby port.
–
Active-active—All Ethernet ports are utilized simultaneously.
Step 6
Choose whether to enable DHCP for dynamic network settings, or to enter static network settings.
Note
Before you enable DHCP, your DHCP server must be preconfigured with the range of MAC addresses for this server. The MAC address is printed on a label on the rear of the server. This server has a range of six MAC addresses assigned to the CIMC. The MAC address printed on the label is the beginning of the range of six contiguous MAC addresses.
Step 7
Optional: Use this utility to make VLAN settings, and to set a default CIMC user password.
Note
Changes to the settings take effect after approximately 45 seconds. Refresh with F5 and wait until the new settings appear before you reboot the server in the next step.
Step 8
Press F10 to save your settings and reboot the server.
Note
If you chose to enable DHCP, the dynamically assigned IP and MAC addresses are displayed on the console screen during boot up.
Creating a Bootable USB Drive
The Cisco ISE 1.1.4 ISO image contains an "images" directory that has a Readme file and a script to create a bootable USB to install Cisco ISE 1.1.4.
Before You Begin
•
Ensure that you have read the Readme in the "images" directory
•
You need the following:
–
Linux machine with RHEL-5 or above, CentOS 5.x or above. If you are going to use your PC or MAC, ensure that you have installed a Linux VM on it.
–
An 8-GB USB drive
–
The iso-to-usb.sh script
Step 1
Plug in your USB drive into the USB port.
Step 2
Copy the iso-to-usb.sh script and the Cisco ISE 1.1.4 ISO image to a directory on your linux machine.
Step 3
Enter the following command:
iso-to-usb.sh source_iso usb_device
For example, # ./iso-to-usb.sh ise-1.1.4.218.i386.iso /dev/sdb where iso-to-usb.sh is the name of the script, ise-1.1.4.218.i386.iso is the name of the ISO image, and /dev/sdb is your USB device.
Step 4
A screen appears prompting you to specify the type of appliance (Cisco SNS 3415 or Cisco SNS 3495) that you want to install.
Step 5
Enter a value corresponding to your appliance type to create a bootable USB drive.
Step 6
Enter Y to continue.
Step 7
A success message appears.
Step 8
Unplug your USB drive.
Upgrading Cisco ISE Software
If you installed Cisco Identity Services Engine Release 1.0 or Cisco Identity Services Engine Maintenance Release 2 (MR2) previously and are planning to upgrade to the latest Cisco ISE release, review the open caveats in this section before following the upgrade instructions in the "Upgrading Cisco ISE" chapter of the Cisco Identity Services Engine Hardware Installation Guide, Release 1.1.x.
Note
When you upgrade to Cisco ISE, Release 1.1.x, you may be required to open some network ports you may not have been using in previous releases of Cisco ISE. Ensure you consult the table of required ports to open in Cisco ISE in the "Cisco ISE 3300 Series Appliance Ports Reference" appendix of the Cisco Identity Services Engine Hardware Installation Guide, Release 1.1.x.
This section covers the following upgrade issues:
•
Upgrade from Cisco ISE, Release 1.1.3 to release 1.1.4
•
Upgrade from Cisco ISE, Release 1.1.2 to release 1.1.3
•
Upgrade from Cisco ISE, Release 1.1.1 to release 1.1.3
•
Upgrade from Cisco ISE, Release 1.1.1 to release 1.1.2
•
Upgrade from Cisco ISE, Release 1.1 to release 1.1.1
•
Upgrade from Cisco ISE, Release 1.0.4 to 1.1.1 with Inline Posture
•
Upgrade from Cisco ISE, Release 1.0.3.377
Upgrade from Cisco ISE, Release 1.1.3 to release 1.1.4
Prerequisite
Before you upgrade, ensure that you delete all policies that use the "Blacklist_Access" authorization profile. For more details, refer to CSCub17140.
You can upgrade from Cisco ISE, Release 1.1.3 to release 1.1.4 normally, as described in the upgrade instructions in the Cisco Identity Services Engine Upgrade Guide, Release 1.1.x.
Upgrade from Cisco ISE, Release 1.1.2 to release 1.1.3
Prerequisite
Before you upgrade, ensure that you delete all policies that use the "Blacklist_Access" authorization profile. For more details, refer to CSCub17140.
You can upgrade from Cisco ISE, Release 1.1.2 to release 1.1.3 normally, as described in the upgrade instructions in the Cisco Identity Services Engine Upgrade Guide, Release 1.1.x.
Upgrade from Cisco ISE, Release 1.1.1 to release 1.1.3
Prerequisite
Before you upgrade, ensure that you delete all policies that use the "Blacklist_Access" authorization profile. For more details, refer to CSCub17140.
Before you can upgrade to Cisco ISE, Release 1.1.3, you must first be sure you have upgraded your machine to Cisco ISE, Release 1.1.1 with patch 3 applied. For specific instructions on performing the upgrade procedure, see the Cisco Identity Services Engine Upgrade Guide, Release 1.1.x.
Upgrade from Cisco ISE, Release 1.1.1 to release 1.1.2
Prerequisite
Before you upgrade, ensure that you delete all policies that use the "Blacklist_Access" authorization profile. For more details, refer to CSCub17140.
Before you can upgrade to Cisco ISE, Release 1.1.2, you must first be sure you have upgraded your machine to Cisco ISE, Release 1.1.1 with patch 3 applied. For specific instructions on performing the upgrade procedure, see the Cisco Identity Services Engine Upgrade Guide, Release 1.1.x.
Upgrade from Cisco ISE, Release 1.1 to release 1.1.1
Prerequisite
Before you upgrade, ensure that you delete all policies that use the "Blacklist_Access" authorization profile. For more details, refer to CSCub17140.
Before you can upgrade to Cisco ISE, Release 1.1.1 from Release 1.1, you must first be sure you have applied Cisco Identity Services Engine Cumulative Patch 3 to your Release 1.1 machine(s). For information on obtaining Cisco ISE, Release 1.1 patch 3, see the Release Notes for the Cisco Identity Services Engine, Release 1.1. For specific instructions on performing the upgrade procedure, see the Cisco Identity Services Engine Upgrade Guide, Release 1.1.x.
Upgrade from Cisco ISE, Release 1.0.4 to 1.1.1 with Inline Posture
In Cisco ISE 1.1.1, the Inline Posture node uses certificate based authentication and cannot connect to the Administrative ISE node. Therefore you are required to disconnect the Inline Posture node from the deployment prior to starting the upgrade procedure, then reconfigure the Inline Posture node after the upgrade. To do so, follow the procedure outlined in this section.
WarningYou must have the proper certificates in place for your Inline Posture deployment to mutually authenticate.
Prerequisite
Record all the configuration data for your Inline Posture node before you de-register the node. Alternatively, you can save screenshots of each of the Inline Posture tabs (in the Admin user interface) to record the data. Having this data on hand speeds up the process of re-registering the Inline Posture node to complete the following task.
To upgrade to Cisco ISE 1.1.1 with Inline Posture, complete the following steps:
Step 1
From the Cisco Administration ISE node, de-register the Cisco Inline Posture node.
Note
You can verify that the Inline Posture node has returned to ISE node status by going to the CLI and entering the following command: show application status ise If you discover that the node has not reverted to an ISE node, then you can enter the following at the command prompt: pep switch outof-pep However, it is recommended that you only do this as a last resort.
Step 2
Upgrade the Cisco Administration ISE node to 1.1.1, as described in the Cisco Identity Services Engine Hardware Installation Guide, Release 1.1.x.
Step 3
Import CA root certificate, make CSR, create certificates on the Administration ISE node.
Note
Certificates must have extended key usage for both client authentication and server authentication. For an example of this type of extended key usage, see the Microsoft CA Computer template.
Step 4
Perform a fresh installation of ISE 1.1.1 on the ISE node (that was the former Inline Posture node), as described in the Cisco Identity Services Engine Hardware Installation Guide, Release 1.1.x.
Step 5
Import CA root certificate, make CSR, create certificates on the ISE node (that was the former Inline Posture node), now in standalone mode.
Note
Certificates must have extended key usage; client authentication and server authentication. For example, select the computer template from Microsoft CA.
Step 6
Register the newly upgraded ISE Node as an Inline Posture node.
Step 7
Reconfigure the Cisco Inline Posture node.
Upgrade from Cisco ISE, Release 1.0.3.377
Prerequisite
Before you upgrade, ensure that you delete all policies that use the "Blacklist_Access" authorization profile. For more details, refer to CSCub17140.
There is a known issue regarding default "admin" administrator user interface access following upgrade from Cisco Identity Services Engine Release version 1.0.3.377. This issue can affect Cisco ISE customers who have not changed their default "admin" account password for administrator user interface login since first installing Cisco Identity Services Engine Release 1.0.3.377.
Upon upgrading, administrators can be "locked out" of the Cisco ISE administrator user interface when logging in via the default "admin" account where the password has not yet been updated from the original default value.
To avoid this issue, Cisco recommends you do one or more of the following:
1.
Verify they have changed password per the instructions in the "Managing Identities" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x prior to upgrade.
2.
Disable or modify the password lifetime setting in the Administration > System > Admin Access > Password Policy page of the administrator user interface prior to upgrade to ensure the upgraded policy behavior does not impact the default "admin" account.
3.
Enable password lifetime setting reminders in the Administration > System > Admin Access > Password Policy page to alert admin users of imminent expiry. Administrators should change the password when notified.
Note
Although the above conditions apply to all administrator accounts, the change in behavior from Cisco ISE version 1.0.3.377 only impacts the default "admin" account.
Cisco Secure ACS to Cisco ISE Migration
Complete instructions for moving your Cisco Secure ACS 5.1 or 5.2 database to Cisco ISE, Release 1.1.x are covered in the Cisco Identity Services Engine Migration Guide for Cisco Secure ACS 5.1 and 5.2, Release 1.1.x.
Note
You must upgrade your Cisco Secure ACS deployment to Release 5.1 or 5.2 before you attempt to perform the migration process to Cisco Identity Services Engine.
After you have moved your Cisco Secure ACS 5.1 or 5.2 database over, you will notice some differences in existing data types and elements as they appear in the new Cisco ISE environment. Microsoft Windows Internet Explorer (IE8 and IE7) browsers are not currently supported in this release.
Cisco ISE License Information
For detailed information on license types and obtaining licenses for Cisco ISE, see "Performing Post-Installation Tasks" chapter of the Cisco Identity Services Engine Hardware Installation Guide, Release 1.1.x.
New Features in Cisco ISE, Release 1.1.4
Cisco ISE, Release 1.1.4 provides support for the Cisco SNS 3400 Series appliance. For details on the installing and configuring the Cisco SNS 3400 Series appliance, refer to the ISE 1.1.4 Installation Guide at the following location:
•
http://www.cisco.com/en/US/docs/security/ise/1.1.1/installation_guide/ise_install_guide.html
New Features in Cisco ISE, Release 1.1.3
Cisco ISE, Release 1.1.3 features critical bug fixes derived from Cisco ISE, Release 1.0.4, 1.1, 1.1.1, and 1.1.2 while rolling patch fixes for Cisco ISE, Release 1.1.1 and 1.1.2 into 1.1.3.
New Features in Cisco ISE, Release 1.1.2
Cisco ISE, Release 1.1.2 offers the following features and services:
•
Global Setting for Endpoint Attribute Filter
Global Setting for Endpoint Attribute Filter
In Cisco ISE, Release 1.1.2, you can globally configure endpoint attribute filtering to help Cisco ISE reduce the amount of profiling traffic replicated in the local database. This enhancement introduces a new function called a "whitelist," which drops any attributes that are not present in the whitelist to ensure Cisco ISE database replication takes place as efficiently as possible. The whitelist is a dynamic list of attributes based on the attribute(s) you use in your profiling policies. When profiling is enabled, the Policy Service nodes in your deployment collect information from various probes and send it to the Administration ISE node. The Administration ISE node then stores and replicates this information. Earlier releases of Cisco ISE do not feature any control over which attributes can be saved, and as a result, would collect a significant amount of unnecessary information.
New Features in Cisco ISE, Release 1.1.1
Cisco ISE, Release 1.1.1 offers the following features and services:
•
New Default Authorization Profile ("Blacklist")
•
Dictionary Attribute-to-Attribute Authorization Policy Configuration
•
New Device Registration Task Navigator
•
Native Supplicant Provisioning Profile Configuration Page
•
Enhanced Client Provisioning Policy Configuration
•
SCEP Authority Profile Configuration Page
•
EAP-TLS as an Inner Method for EAP-FAST
•
New Reports in Cisco ISE, Release 1.1.1
For more information on key features of Cisco ISE, see the "Overview of Cisco ISE" chapter in the Cisco Identity Services Engine User Guide, Release 1.1.x.
New Default Authorization Profile ("Blacklist")
The Cisco ISE administrator can now "blacklist" wireless user devices that get "lost," or otherwise become unusable or are taken out of circulation, until the device is reinstated or is completely removed from the network. Cisco ISE removes "blacklisted" devices from the network, and they are not allowed on the network again until the device is reinstated. In order to set up the authorization policy in Cisco ISE, you also must ensure you add a compatible dynamic ACL on any associated network access devices in your deployment to manage these wireless users.
This new default authorization profile is available in the Policy > Authorization Policy page of the Cisco ISE administrator user interface.
Dictionary Attribute-to-Attribute Authorization Policy Configuration
In Cisco ISE, Release 1.1.1, you now have the option, when constructing policy conditions in an authorization policy, to specify another dictionary attribute to which you can associate the source attribute during policy configuration. Traditionally, you could only specify a text entry following the requisite operators when setting conditions in authorization policies.
This enhancement affects the Policy > Authorization Policy page of the Cisco ISE administrator user interface.
New Device Registration Task Navigator
The Device Registration Task Navigator in Cisco ISE, Release 1.1.1 provides a visual path through the various Cisco ISE administration and configuration processes that are necessary to enable administrators to set up Cisco ISE to provide multiple, configurable device support for end users. (As with previous Task Navigator implementation, the linear presentation of the Task Navigator outlines the order in which the tasks should be completed, while also providing direct links to the pages that are needed to perform the tasks.)
Native Supplicant Provisioning Profile Configuration Page
In Cisco ISE, Release 1.1.1, you can now configure native supplicant profiles for client provisioning, in addition to the existing "ISE Posture Agent Profiles" that are currently available in Cisco ISE, Releases 1.0.4 and 1.1. This profile type allows you to specify settings for user registration via personal devices like iPhones, iPads, and Android devices.
Enhanced Client Provisioning Policy Configuration
In Cisco ISE, Release 1.1.1, you can now create or edit client provisioning policies to allow for expanded personal device support, including iPhones, iPads, and Android devices. For specific personal device support, you can configure the policy to upload the appropriate configuration wizard that is necessary to enable the personal device to negotiate and register with Cisco ISE.
SCEP Authority Profile Configuration Page
To support enhanced personal device registration functions, Cisco ISE Release 1.1.1 enables you to configure one or more Simple Certificate Enrollment Protocol (SCEP) authority profiles. Cisco ISE verifies and maintains connectivity with the SCEP authority servers that you specify, and it even performs load balancing among multiple servers to ensure optimal connectivity for users when they access the network using their personal devices.
RADIUS Proxy Attribute
The RADIUS proxy attribute in Cisco ISE, Release 1.1.1 is used to enhance the RADIUS sequence flows and processing. When the "Access-Accept" packet is received from an external RADIUS server, Cisco ISE continues to the configured authorization policy for further decision-making that is based on additional attributes and groups that are queried from Active Directory and LDAP.
EAP Chaining
In Cisco ISE, Release 1.1.1, Extensible Authentication Protocol (EAP) chaining solution allows you to authenticate both the machine and user in the same EAP-FAST authentication in a configurable order. When an EAP-FAST authentication result is determined, Cisco ISE allows you to apply an authorization policy, depending on the result of both authentications. When EAP chaining is turned off, Cisco ISE performs the usual EAP-FAST authentication.
EAP-TLS as an Inner Method for EAP-FAST
This feature in Cisco ISE, Release 1.1.1 allows you to use the Extensible Authentication Protocol-Transport Layer Security (EAP-TLS) protocol as an inner method for the EAP-FAST protocol. The implementation is the same as using EAP-TLS as the inner method for Protected Extensible Authentication Protocol (PEAP).
Device Registration Portal
The device registration portal is a standalone portal that can be completely customized to suit your organization. A network access user who is configured as an employee in an organization can access the portal which allows the user to bring personal devices into an enterprise network. This is done through an employee authentication and device registration process. Employees can manage their devices to add, edit, reinstate, and delete their devices through this portal. Cisco ISE adds these devices to the endpoints database and profiles them like any other endpoint. Cisco ISE administrators can manage the registered endpoints from the administrator user interface, by using the identities list and reports.
A default authorization policy exists in Cisco ISE that does not allow devices to access an enterprise network when they are marked "lost" in the device registration portal, and identified as blacklisted in an endpoint identity group. An employee can also reinstate a blacklisted device in the device registration portal, and register again to access the network.
New Reports in Cisco ISE, Release 1.1.1
Cisco ISE, Release 1.1.1 offers the following new reports:
•
Supplicant Provisioning Report—This report provides information about a list of endpoints that are registered through the Asset Registration Portal (ARP) for a specific period of time.
•
Registered Endpoint Report—This report provides information about a list of endpoints that are registered through the Asset Registration Portal (ARP) by a specific user for a selected period of time.
Change of Authorization
Cisco ISE triggers a CoA when an endpoint is added or removed from an endpoint identity group that is used by an authorization policy. A CoA is also triggered when an endpoint identity group assignment changes due to either dynamic profiling or a static assignment.
Creating Activated Guests
Sponsor user can create activated guests by assigning them to the ActivatedGuest identity group. This is a default identity group in Cisco ISE 1.1.1. Sponsor user should belong to a sponsor group that allows for assigning of guests to ActivatedGuest identity group.
Cisco ISE Install Files, Updates, and Client Resources
There are three resources you can use to download installation packages, update packages, and other client resources necessary to provision and provide policy service in Cisco ISE:
•
Cisco ISE Downloads from the Cisco Download Software Center
Cisco ISE Downloads from the Cisco Download Software Center
In addition to the .ISO installation package required to perform a fresh installation of Cisco ISE as described in Installing Cisco ISE Software, you can use the same software download location to retrieve other vital Cisco ISE software elements, like Windows and Mac OS X agent installers and AV/AS compliance modules.
Use this portal to get your first software packages prior to configuring your Cisco ISE deployment. Downloaded agent files may be used for manual installation on a supported endpoint or used with third-party software distribution packages for mass deployment.
To access the Cisco Download Software Center and download the necessary software from Cisco:
Step 1
Log into Cisco Download Software at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm. You might be required to provide your Cisco.com login credentials.
Step 2
Navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software.
Choose from the following Cisco ISE installers and software packages available for download:
•
Cisco ISE installer .ISO image
•
Windows client machine agent installation files (including MST and MSI versions for manual provisioning)
•
Mac OS X client machine agent installation files
•
AV/AS compliance modules
Step 3
Click Download Now or Add to Cart for any of the software items you require to set up your Cisco ISE deployment.
Cisco ISE Live Updates
Cisco ISE Live Update locations allow you to automatically download agent, AV/AS support, and agent installer helper packages that support the client provisioning and posture policy services. These live update portals should be configured in ISE upon initial deployment to retrieve the latest client provisioning and posture software directly from Cisco.com to the ISE appliance.
Prerequisite
If the default Update Feed URL is not reachable and your network requires a proxy server, you may need to configure the proxy settings in the Administration > System > Settings > Proxy before you are able to access the Live Update locations. For more information on proxy settings, see the "Specifying Proxy Settings in Cisco ISE" section in the "Configuring Client Provisioning Policies" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x.
Client Provisioning and Posture Live Update portals:
•
Client Provisioning—https://www.cisco.com/web/secure/pmbu/provisioning-update.xml
The following software elements are available at this URL:
–
Windows and Mac OS X versions of the latest Cisco ISE persistent and temporal agents
–
ActiveX and Java Applet installer helpers
–
AV/AS compliance module files
For more information on automatically downloading the software packages that become available at this portal to Cisco ISE, see the "Downloading Client Provisioning Resources Automatically" section of the "Configuring Client Provisioning Policies" chapter in the Cisco Identity Services Engine User Guide, Release 1.1.x.
•
Posture—https://www.cisco.com/web/secure/pmbu/posture-update.xml
The following software elements are available at this URL:
–
Cisco predefined checks and rules
–
Windows and Mac OS X AV/AS support charts
–
Cisco ISE operating system support
For more information on automatically downloading the software packages that become available at this portal to Cisco ISE, see the "Dynamic Posture Updates" section of the "Configuring Client Posture Policies" chapter in the Cisco Identity Services Engine User Guide, Release 1.1.x.
If you do not enable the automatic download capabilities described above in Cisco ISE, you can choose offline updates. See Cisco ISE Offline Updates.
Cisco ISE Offline Updates
Cisco ISE offline updates allow you to manually download agent, AV/AS support, and agent installer helper packages that support the client provisioning and posture policy services. This option allows you to upload client provisioning and posture updates in environments where direct Internet access to Cisco.com from the ISE appliance is not available or not permitted by security policy.
To upload offline client provisioning resources, complete the following steps:
Step 1
Log into Cisco Download Software at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm. You might be required to provide your Cisco.com login credentials.
Step 2
Navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software.
Choose from the following Off-Line Installation Packages available for download:
•
compliancemodule-<version>-isebundle.zip — Off-Line Compliance Module Installation Package
•
macagent-<version>-isebundle.zip — Off-Line Mac Agent Installation Package
•
nacagent-<version>-isebundle.zip — Off-Line NAC Agent Installation Package
•
webagent-<version>-isebundle.zip — Off-Line Web Agent Installation Package
Step 3
Click Download Now or Add to Cart for any of the software items you require to set up your Cisco ISE deployment.
For more information on adding the downloaded Installation Packages to Cisco ISE, refer to "Adding Client Provisioning Resources from a Local Machine" section of the "Configuring Client Posture Policies" chapter in the Cisco Identity Services Engine User Guide, Release 1.1.x.
You can update the checks, rules, antivirus and antispyware support charts for both the Windows and Macintosh operating systems, and operating systems information offline from an archive on your local system using the posture updates.
For offline updates, you need to ensure that the versions of the archive files match the version in the configuration file. Use this portal once you have configured Cisco ISE and want to enable dynamic updates for the posture policy service.
To upload offline posture updates, complete the following steps:
Step 1
Go to https://www.cisco.com/web/secure/pmbu/posture-offline.html.
The File Download window appears. From the File Download window, you can choose to save the posture-offline.zip file to your local system. This file is used to update the checks, rules, antivirus and antispyware support charts for both the Windows and Macintosh operating systems, and operating systems information.
Step 2
Access the Cisco ISE administrator user interface and choose Administration > System > Settings > Posture.
Step 3
Click the arrow to view the settings for posture.
Step 4
Choose Updates. The Posture Updates page appears.
Step 5
From the Posture Updates page, choose the Offline option.
Step 6
From the File to update field, click Browse to locate the single archive file (posture-offline.zip) from the local folder on your system.
Note
The File to update field is a required (mandatory) field and it cannot be left empty. You can only select a single archive file (.zip) that contains the appropriate files. Archive files other than .zip (like .tar, and .gz) are not allowed.
Step 7
Click the Update Now button.
Once updated, the Posture Updates page displays the current Cisco updates version information as a verification of an update under Update Information.
Support for Windows 8.1 and Mac OS X 10.9
Cisco ISE 1.1.4 Patch 8 and 1.1.3 Patch 8 supports clients using the Windows 8.1 and Mac OS X 10.9 operating systems.
See Cisco ISE Release 1.1.x Open Caveats for workarounds for issues with Safari 7 and Internet Explorer 11.
Cisco ISE, Release 1.1.4 Patch Updates
The following patch releases apply to Cisco ISE release 1.1.4:
•
Resolved Issues in Cisco ISE Version 1.1.4.218—Cumulative Patch 7
•
Resolved Issues in Cisco ISE Version 1.1.4.218—Cumulative Patch 6
•
Resolved Issues in Cisco ISE Version 1.1.4.218—Cumulative Patch 5
•
Resolved issues in Cisco ISE Version 1.1.4.218—Cumulative Patch 4
•
Resolved issues in Cisco ISE Version 1.1.4.218—Cumulative Patch 3
•
Resolved Issues in Cisco ISE Version 1.1.4.218—Cumulative Patch 2
•
Resolved Issues in Cisco ISE Version 1.1.4.218—Cumulative Patch 1
Resolved Issues in Cisco ISE Version 1.1.4.218—Cumulative Patch 8
Table 12 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.4.218 cumulative patch 8.
ISE 1.1.4 patch 8 also includes support for Windows 8.1 and Mac OS X 10.9. See Support for Windows 8.1 and Mac OS X 10.9 for more information.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.4, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.4.218—Cumulative Patch 7
Table 6 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.4.218 cumulative patch 7.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.4, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.4.218—Cumulative Patch 6
Table 7 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.4.218 cumulative patch 6.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.4, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.4.218—Cumulative Patch 5
Table 8 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.4.218 cumulative patch 5.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.4, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved issues in Cisco ISE Version 1.1.4.218—Cumulative Patch 4
Table 9 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.4.218 cumulative patch 4.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.4, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved issues in Cisco ISE Version 1.1.4.218—Cumulative Patch 3
Table 10 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.4.218 cumulative patch 3.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.4, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.4.218—Cumulative Patch 2
Table 11 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.4.218 cumulative patch 2.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.4, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
While upgrading from Cisco ISE Release 1.1.4 patch 1 to patch 2, the log targets configured for `Authentication Flow Diagnostics' might get removed. You need to manually reconfigure the log targets. See Also CSCuh81724.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.4.218—Cumulative Patch 1
Table 12 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.4.218 cumulative patch 1.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.4, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Cisco ISE, Release 1.1.3 Patch Updates
The following patch releases apply to Cisco ISE release 1.1.3:
•
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 8
•
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 7
•
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 6
•
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 5
•
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 4
•
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 3
•
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 2
•
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 1
The following patch releases apply to Cisco ISE release 1.1.2 and have been rolled into release 1.1.3:
•
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 6
•
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 5
•
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 4
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 8
Table 12 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.3.124 cumulative patch 8.
ISE 1.1.3 patch 8 also includes support for Windows 8.1 and Mac OS X 10.9. See Support for Windows 8.1 and Mac OS X 10.9 for more information.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.3, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 7
Table 12 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.3.124 cumulative patch 7.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.3, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 6
Table 15 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.3.124 cumulative patch 6.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.3, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 5
Table 16 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.3.124 cumulative patch 5.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.3, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 4
Table 17 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.3.124 cumulative patch 4.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.3, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 3
Table 18 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.3.124 cumulative patch 3.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.3, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 2
Table 19 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.3.124 cumulative patch 2.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.3, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.3.124—Cumulative Patch 1
Table 20 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.3.124 cumulative patch 1.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.3, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Cisco ISE, Release 1.1.2 Patch Updates
The following patch release applies to Cisco ISE release 1.1.2
•
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 10
•
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 9
•
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 8
•
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 7
•
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 6
The following patch releases apply to Cisco ISE release 1.1.2 and have been rolled into release 1.1.3:
•
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 6
•
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 5
•
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 4
•
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 3
•
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 2
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 10
Table 22 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.2.145 cumulative patch 10.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.2, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 9
Table 22 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.2.145 cumulative patch 9.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.2, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 8
Table 23 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.2.145 cumulative patch 8.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.2, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 7
Table 24 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.2.145 cumulative patch 7.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.2, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 6
Table 25 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.2.145 cumulative patch 6 (Revision Number 77241).
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.2, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 5
Table 26 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.2.145 cumulative patch 5.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.2, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 4
Table 27 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.2.145 cumulative patch 4.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.2, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 3
Table 28 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.2.145 cumulative patch 3.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.2, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.2.145—Cumulative Patch 2
Note
There is no Patch 1 available for general deployment on the Cisco Download Software Site. Patch 1 was a limited availability patch which is now superseded by Patch 2.
Table 29 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.2.145 cumulative patch 2.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.2, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Table 29 Cisco ISE Patch Version 1.1.2.145—Patch 2 Resolved Caveats
CSCto28988
Session cache entry not found with failed authentication entries
This fix addresses an issue where Cisco ISE would intermittently return session failures citing the wrong password, unknown user, and/or EAP protocol failures.
Before this resolution, you would need to disconnect and reconnect to any wired interface experiencing this issue, and (for wireless connections) either disconnect from the interface and wait five minutes before reconnecting, or ask your network administrator to manually clear the client session from a Wireless LAN Controller.
Note
This issue was not unique to guest login session flows.
CSCub32594
Inline posture node does not accept a policy from the associated Policy Service node
This resolution addresses an issue that could occur when multiple user sessions trigger concurrent exchanges of RADIUS messages between the Inline Posture node and the Policy Service node (in the case of an "Authorize-Only" query or DACL download, for example) due to a race condition between two simultaneous threads. To reproduce this issue, the best way is to generate many concurrent RADIUS sessions.
Note
Historically, this issue might only occur on a very infrequent basis, possibly taking months between subsequent occurrences.
CSCuc13075
Endpoints are being saved with EndpointPolicy as Unknown
This update fixes an issue where endpoint profiles were appearing in the Cisco ISE administrator interface as designed, reading "Apple-Device," but upon editing the endpoint entry, the endpoint attributes "Endpoint Policy" and "Matched Policy" appeared as "UNKNOWN."
CSCuc21814
Incorrect profiler policy with Rate limiter delayed updates in few cases
This fix addresses an issue where the Cisco ISE profiling policy represents to an incorrect value in certain cases due to delayed profiling updates by the previously-implemented Rate Limiter enhancement.
CSCuc46719
High CPU usage observed when profiling data cannot be written to database
When profiler fails to write data to the Cisco ISE database, the process does not drop that data and, instead, keeps trying to update the database, driving up CPU usage due to the extra services required. One example recorded involved a RADIUS probe where each user had a very large Active Directory group membership field. The value of this field was larger than what the Cisco ISE database could store reliably, and when Profiler tried repeatedly to add the data, the result was extremely high CPU usage.
CSCud04633
Java causing "Out of Memory" errors in Cisco ISE
This issue was observed in Cisco ISE, Release 1.1.1 where client machines were attempting to register with Cisco ISE using the EAP-TLS and PEAP protocols, as well as during standard profiling functions.
Before this fix addressed the issue, you would have to manually restart services on the Cisco ISE node in question to remedy the situation.
CSCud11139
XSS Vulnerability in Cisco ISE Guest Portal
A security scan of the Cisco ISE Guest Portal indicated that the product could be vulnerable to an XSS cross-scripting attack. This issue was observed on Cisco ISE, Release 1.1.1 and has now been addressed in this patch release.
Note
There is no known workaround for this issue.
PSIRT Evaluation
The Cisco PSIRT has assigned this bug the following CVSS version 2 score. The Base and Temporal CVSS scores as of the time of evaluation are 4.3/4.1:
CVE ID CVE-2012-5744 has been assigned to document this issue.
Additional information on Cisco's security vulnerability policy can be found at the following URL:
http://www.cisco.com/en/US/products/products_security_vulnerability_policy.html
CSCud12095
Purge job fails to complete in Cisco ISE, Release 1.1.1
This fix addresses an issue resulting in an "explosion" of Monitoring and Troubleshooting node tables reaching as high as 150GB in size, and the presence of many associated "database failure" messages in the Cisco ISE alarm entries.
Prior to this fix, you would need to contact the Cisco TAC to get instructions necessary to manually clean the oversized Monitoring and Troubleshooting node tables.
CSCud20871
Session cache entry missing during Guest authentication
This fix addresses an issue with Cisco ISE Guest authentication failures returning "86107-Session cache entry missing" errors from the Guest Portal.
In order to resolve the issue prior to this fix, you would have to:
1.
Manually remove the Guest login session from the access point.
2.
Wait for the resulting idle-timeout or session timeout to elapse on the access point, and then attempt to re-establish the connection.
Cisco ISE, Release 1.1.1 Patch Updates
The following patch releases apply to Cisco ISE release 1.1.1
•
Resolved Issues in Cisco ISE Version 1.1.1.268—Cumulative Patch 7
The following patch releases apply to Cisco ISE release 1.1.1 and 1.1.3:
•
Resolved Issues in Cisco ISE Version 1.1.1.268—Cumulative Patch 6
•
Resolved Issues in Cisco ISE Version 1.1.1.268—Cumulative Patch 5
•
Resolved Issues in Cisco ISE Version 1.1.1.268—Cumulative Patch 4
The following patch releases apply to Cisco ISE release 1.1.1 and have been rolled into release 1.1.2 and 1.1.3:
•
Resolved Issues in Cisco ISE Version 1.1.1.268—Cumulative Patch 3
•
Resolved Issues in Cisco ISE Version 1.1.1.268—Cumulative Patch 2
•
Resolved Issues in Cisco ISE Version 1.1.1.268—Cumulative Patch 1
Resolved Issues in Cisco ISE Version 1.1.1.268—Cumulative Patch 7
Table 30 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.1.268 cumulative patch 7.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.1, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.1.268—Cumulative Patch 6
Table 31 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.1.268 cumulative patch 6.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.1, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.1.268—Cumulative Patch 5
Table 32 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.1.268 cumulative patch 5.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.1, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.1.268—Cumulative Patch 4
Note
To properly apply patch 4 to your Cisco ISE nodes and gain the benefits of CSCua55485, you must install the patch according to whether your nodes are deployed in different network domains:
•
If all of your Cisco ISE nodes are deployed are in same domain, you can apply patch 4 using the standard administrator user interface method described below.
•
If your Cisco ISE nodes are deployed in different domains, you must install this patch on your Cisco ISE nodes via the administrator CLI. Once the patch has been applied on the deployment, you can then apply future patches using the standard Administrator user interface method.
Table 33 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.1.268 cumulative patch 4.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.1, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.1.268—Cumulative Patch 3
Table 34 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.1.268 cumulative patch 3.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.1, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.1.268—Cumulative Patch 2
Table 35 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.1.268 cumulative patch 2.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.1, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Resolved Issues in Cisco ISE Version 1.1.1.268—Cumulative Patch 1
Table 36 lists the issues that are resolved in Cisco Identity Services Engine Maintenance Release 1.1.1.268 cumulative patch 1.
To obtain the patch file necessary to apply the patch to Cisco ISE Release 1.1.1, log into the Cisco Download Software site at http://www.cisco.com/cisco/software/navigator.html?a=a&i=rpm (you might be required to provide your Cisco.com login credentials), navigate to Security > Access Control and Policy > Cisco Identity Services Engine > Cisco Identity Services Engine Software, and save a copy of the patch file to your local machine.
Then refer to the "Installing a Software Patch" section of the "Administering Cisco ISE" chapter of the Cisco Identity Services Engine User Guide, Release 1.1.x. for instructions on how to apply the patch to your system.
If you experience problems installing the patch, contact Cisco Technical Assistance Center.
Cisco ISE Antivirus and Antispyware Support
See the following Cisco ISE documents for specific antivirus and antispyware support details using Cisco NAC Agent and NAC Web Agent:
•
Cisco Identity Services Engine Release 1.1.x Supported Windows AV/AS Products
•
Cisco Identity Services Engine Release 1.1.x Supported Mac OS X AV/AS Products
Cisco NAC Agent Interoperability Between NAC Appliance and Identity Services Engine
Cisco supports different versions of the NAC Agent for integration with NAC Appliance and ISE. Current releases are developed to work in either environment, however, interoperability between deployments is not guaranteed. Therefore, there is no explicit interoperability support for a given NAC Agent version intended for one environment that will necessarily work in the other. If you require support for both NAC Appliance and ISE using a single NAC Agent, be sure to test NAC Agent in your specific environment to verify compatibility.
Unless there is a specific defect or feature required for your NAC Appliance deployment, Cisco recommends deploying the most current agent certified for your ISE deployment. If an issue arises, Cisco recommends restricting the NAC Agent's use to its intended environment and contacting Cisco TAC for assistance. Cisco will be addressing this issue through the standard Cisco TAC support escalation process, but NAC Agent interoperability is not guaranteed.
Cisco is working on an approach to address NAC Agent interoperability testing and support in an upcoming release.
Integration with Cisco Prime Network Control System
Cisco Identity Services Engine, Release 1.1. x integrates with Cisco Prime Network Control System (Prime NCS), Release 1.2 to manage wired and wireless networks.
Cisco ISE Release 1.1.x Open Caveats
Table 37 Cisco ISE Release 1.1.x Open Caveats
CSCul13185
When installing the NAC/Web Agent using ActiveX in Internet Explorer11, the browser shows the loading symbol indefinitely without downloading the agent.
Workaround
Close and reopen the browser.
CSCuj61976
Admin UI fails to display certain pages using Firefox 25
The ISE admin UI pages with tree view are not displayed correctly when using FF25 and above versions.</B>
Workaround
Downgrade to Firefox 24.
CSCuj80131
ISE Client Provisioning - NSP does not launch on Safari 7 (Mac OS X 10.9)
Java Applet fails to install SPW/Agent from Client Provisioning page on Safari browser version 7 available with Mac OSX 10.9.
Explicitly let it run by changing the website settings on the browser. The default setting encourages users to whitelist individual sites/pages where JAVA is used.
Workaround
To let the applet install agent/SPW, connect to ISE and get re-directed to Client Provisioning page. Before clicking Click to Install Agent, go to: Safari->Preferences->Security->Manage Website Settings->Java->Click on your ISE URL->Run in unsafe mode.
CSCtc70053
Browser "Back" button not working properly
This issue has been observed in the Cisco ISE list page when switching from the list view to edit view (i.e., when you click the Create or Edit button).
Workaround
There is no known workaround for this issue.
CSCti60114
The Mac OS X agent 4.9.0.x install is allowing downgrade
The Mac OS X NAC Agent is allowing downgrades without warnings.
Note
Mac OS X Agent builds differ in minor version updates only. For example, 4.9.0.638 and 4.9.0.637.
CSCti71658
The Mac OS X Agent shows user as "logged-in" during remediation
The menu item icon for Mac OS X Agent might appear logged-in before getting full network accesses
The client endpoints are connecting to an ISE 1.0 network or NAC using device-filter/check with Mac OS X Agent 4.9.0.x.
Workaround
Please ignore the icon changes after detecting the server and before remediation is done.
CSCtj00178
Group QuickFilters not working as designed
After the administrator runs and saves an advanced filter, Cisco ISE does not display the "Successful Save" pop-up after the filter is saved.
This issue has been observed using the Admin Groups, User Identity Groups, Endpoint Identity Groups, and Guest Sponsor Groups filter options.
Workaround
There is no known workaround for this issue.
CSCtj22050
Certificate dialog seen multiple times when certificate is not valid
When the certificate used by the agent to communicate with the server is not trusted, the error message can be seen multiple times.
Workaround
Make sure you have a valid certificate installed on the server and that it has also been accepted and installed on the client.
Note
The additional certificate error message is primarily informational in nature and can be closed without affecting designed behavior.
CSCtj25158
Exported admin should not be imported back as Network Access User
This problem occurs when Cisco ISE promote Network Access Users to Administrators, and then export those users. When you re-import those users, they appear as Network Access Users only. Cisco ISE does not import the promoted users as Administrators.
Workaround
There is no known workaround for this issue.
CSCtj31552
Pop-up Login windows option not used with 4.9 Agent and Cisco ISE
When right clicking on the Windows taskbar tray icon, the Login option is still present, but is not used for Cisco ISE. The login option should be removed or greyed out.
Workaround
There is no known workaround for this issue.
CSCtj76835
Unable to retrieve a saved Authentication Trend report
Symptom Two steps are necessary to save an Authentication Trend report:
1.
Select the folder.
2.
Name the file.
If you do not select a folder from the list that is presented, the report should be saved in the root folder and should appear in the Reports tab. You can observe that the files are saved, but they do not appear in the left side pane and there is no option to retrieve the files.
Conditions
Saving an Authentication Trend report without selecting a folder.
Workaround
Do not save the report under the root folder. Always choose a subfolder.
CSCtj81255
Two MAC addresses detected on neighboring switch of ACS 1121 Appliance.
Symptom Two MAC addresses are detected on the switch interface connected to an ACS 1121 Appliance although only one interface is connected on the ACS 1121 Server eth0.
Conditions
Only one Ethernet interface, eth0 is connected between ACS and Switch.
Workaround
Disable BMC (Baseboard Management Controller) feature using BIOS setup.
CautionTo help prevent a potential network security threat, Cisco strongly recommends physically disconnecting from the Cisco ISE console management port when you are not using it. For more details, see http://seclists.org/fulldisclosure/2011/Apr/55, which applies to the Cisco ISE, Cisco NAC Appliance, and Cisco Secure ACS hardware platforms.
CSCtj94813
Left side administrator user interface pane "Search Result" option is not working as expected
1.
If you enter available data and click the search option, it does not display properly.
2.
If the option displays some data and if you enter another value, it does not refresh the data properly.
3.
The option does not display the layered/structured model as designed.
In addition, you are not able to go back to previous menu.
Workaround
There is no known workaround for this issue.
CSCtk34851
XML parameters passed down from server are not using the mode capability
The Cisco ISE Agent Profile editor can set parameter modes to merge or overwrite. Mac OS X agent is not processing the mode correctly. Instead, the complete file is overwritten each time.
Workaround
To use a unique entry, the administrator must set up a different user group for test purposes, or set the file to read only on the client machine and manually make the necessary changes to the local file.
CSCtk37360
Administrator is not able to customize report in Internet Explorer 8
Monitoring and troubleshooting reporting functions related to column selection and entry deletion/aggregation, etc. are not working as designed.
This issue can come up using the following versions of Internet Explorer 8:
•
IE 8.0.6001.18702 on Windows XP
•
IE 8.0.6001.18702IC on Windows XP
Workaround
There is no known workaround other than to avoid using the problematic browser versions.
CSCtk46958
Cisco ISE does not display a warning when navigating away from a modified page without saving
When a user changes configuration context, there is no warning indicating that the information configured on the current page is not saved, nor is there a warning indicating that all configuration changes will be lost when the user completes that context change.
Workaround
Save before navigating away from the page in question.
CSCtk82864
AAA Servers incorrectly filter with "Contains" option
When AAA servers are added to the AAA servers list (for example: a, ab) and a filter is added which includes regular expressions, Cisco ISE generates an incorrect filtered list.
Workaround
Do not use regular expressions in filters.
CSCtl53966
Agent icon stuck on Windows taskbar
The taskbar icon should appear when the user is already logged in.
Workaround
Right-click on the icon in the taskbar tray and choose Properties or About. After you close the resulting Cisco NAC Agent dialog, the taskbar icon goes away.
CSCtl70056
"Today" is not validated against the Cisco ISE Monitoring node End Date
Reports run with a custom time range (where "today" is the specified End Date) does not work and the Monitoring node returns a validation error. This issue has been observed where the time on the client machine (where a browser session is active) is earlier than that of the Cisco ISE node (for example, where the client is on PST and the Cisco ISE node is on UTC time zone).
Workaround
Change the time zone or clock on the client machine so that the current time on that server is the same or ahead of the Monitoring node.
CSCtl77592
Unable to create authorization policy with RadiusCallingStation ID condition
When the administrator uses a MAC address with a xx-xx-xx-xx-xx-xx format as the right hand side (RHS) of a condition with RADIUS "Calling station ID" dictionary attribute, it fails to match the policy decision.
Cisco ISE does not perform validation on the string value that is entreated on the RHS when constructing a condition.
Workaround
Use the MAC address format xx:xx:xx:xx:xx:xx when defining conditions.
CSCtn44427
No progress indicator is displayed when importing collections of random or CSV guests
Workaround
There is no known workaround for this issue. The administrator must simply wait for the process to complete.
CSCtn53084
Incorrect export of DER imported server and trusted certificate authority certificates
When exporting a local certificate using the Administration > System > Certificates > Local Certificates > Export page, the administrator may find that the certificate is in Distinguished Encoding Rules (DER) format when another format like Privacy Enhanced Mail (PEM) is desired.
The certificate export function exports a certificate using the same format it had when imported. In Cisco ISE, there is no format conversion option available.
Note
One way to avoid this is to simply import all certificates in PEM format. You can convert DER to PEM using tools like openssl, and your certificate authority may have an option for PEM output.
CSCtn65437
Report timestamp incorrect with Asia/Kolkata time zone
This behavior has been observed only using the Asia/Kolkata time zone. The result is minus 5.30 hours when compared to the actual record in the Cisco ISE database.
Workaround
There is no workaround for this issue at this time.
CSCtn76441
Custom conditions are not updated under Rules in profiling policies
If you rename a profiler condition used by a profiling policy, the new name is not reflected in the rule summary display. It is, however, reflected in the associated expanded rule expression.
Workaround
If you expand and collapse the rule expression in the anchored overlay and click Save, the correct description displayed in the rule summary repeater will be displayed in the future. If you change the condition name a second time, however, and expand/collapse the summary overlay on the policy page a second time and click Save, the policy page will not reload until and unless you reload the server.
CSCtn78676
When a user name has a space between words and another similar name contains two or more spaces, Cisco ISE displays the same user name for both users.
Workaround
There is no known workaround for this issue. Even though the multiple spaces are trimmed and shown as one space in the UI, the data is saved correctly in the database.
CSCtn78899
When a user group name has a space between words and another similar user group name contains two or more spaces, Cisco ISE displays the same user group name for both groups.
Workaround
Avoid giving spaces in the name field while creating Identity Group.
CSCtn92594
Quickpicker filters are not working correctly during Client Provisioning policy configuration
This issue has been observed with the following three filter options:
•
Identity Groups
•
Operating Systems
•
Other conditions
Workaround
There is no known workaround for this issue.
CSCtn95548
Filter behaving case sensitive for Network Device groups
The results for network device group filtering in the network device group (NDG) page are incorrect. This is because the filtering in the network device group page is case sensitive.
Workaround
Enter network device groups values using lower-case letters.
CSCto05172
The Profiler detail log does not display some attributes.
"Certainty Metric," "Matched Rule," and "Endpoint Action" name values are not updated in the Profiler endpoint detail log.
Workaround
There is no known workaround for this issue.
CSCto09989
Cisco ISE browser session redirects to Monitoring login page using Internet Explorer 8
As soon as you login to Cisco ISE via IE8 the page gets redirected to a Monitoring node administrator login page (even before the initial page displays completely).
Note
This issue has also been observed using Mozilla Firefox, but the redirection in Firefox only takes place after a couple of minutes of inactivity.
Workaround
Immediately after entering your login credentials,. navigate from the main Cisco ISE page to any configuration page (like Posture, Authorization, or Client Provisioning, for example).
For more information, see Issue Accessing the Cisco ISE Administrator User Interface.
CSCto32002
The Cisco ISE MAC address authentication summary report displays IP addresses where MAC addresses should be
CSCto33933
Login Success display does not disappear when user clicks OK
This can occur if the network has not yet settled following a network change.
Workaround
Wait a few seconds for the display to close.
CSCto41340
Authentication Policy replication failure from Primary to Secondary if the time zone changes after installation
In release 1.0 time change is not supported after the deployment is setup because of the dependencies on time synchronization.
Note
Support for time change within an existing deployment will be postponed to a later release.
CSCto45199
"Failed to obtain a valid network IP" message does not go away after the user clicks OK
This issue has been observed in a wired NAC network with IP address change that is taking longer then normal. (So far, this issue has only been only seen on Windows XP machines.)
Workaround
None. The user needs to wait for the IP address refresh process to complete and for the network to stabilize in the background.
CSCto48555
Mac OS X agent does not rediscover the network after switch from one SSID to another in the same subnet
Agent does not rediscover until the temporary role (remediation timer) expires.
Workaround
The user needs to click Complete or Cancel in the agent login dialog to get the agent to appear again on the new network.
CSCto52210
Authorization and authentication policy rules pages load and save times are high
This issue has been observed with 50 or more authentication rules, where each rule has at least conditions. The Load and save times approach one-and-a-half minutes.
CSCto54536
Local certificates disappear on the secondary node following "application reset-config ise" command in CLI
When displaying the local certificates on the Administration > System > Certificates > Local Certificates page of a deregistered node that is now in Standalone mode.
The administrator should not reset the configuration of a node prior to de-registering it. The correct process is as follows:
1.
Node A is registered.
2.
Node A is deregistered.
3.
Enter "application reset-config ise" in node A CLI.
Workaround
If the node is reset before deregistration, you can make the local certificates reappear by entering the following commands in the CLI:
•
application stop ise
•
application start ise
CSCto60148
Java crashes during high posture load
This issue has been observed under extreme load condition where Cisco ISE is hit with large number of concurrent users for posture.
Workaround
None. You must restart the Cisco ISE Policy Service.
CSCto63069
The nacagentui.exe application memory usage doubles when using "ad-aware"
This issue has been observed where the nacagentui.exe memory usage changes from 54 to 101MB and stays there.
Workaround
Disable the Ad-Watch Live Real-time Protection function.
CSCto64028
"Fail to receive server response..." seen when deleting profiling policy
A "Fail to receive server response due to the network error (ex. HTTP timeout)" error message may appear when deleting Profiling policies, and some of the policies may not be deleted.
Workaround
Log out from Cisco ISE, log back in, and try deleting the policies again.
CSCto72015
Authorization policy with condition as "Identity grp" does not work
Create an Identity Group with the following attributes:
User Identity Groups:
•
Employee
–
Location1
–
Location2
Create Authorization Policy containing the "IdentityGroup:Name Equals Location1" condition and perform user authentication. Authentication fails because the rule in the condition has not been satisfied.
This problem occurs only using the "IdentityGroup:Name" dictionary attribute in the Authorization Policy.
Workaround
To implement the workaround:
1.
Instead of using a Dictionary Attribute (IdentityGroup:Name) in the policy, specify the Identity Group to be "Location1" in the Identity Group selection rather than "Any."
2.
Assign the "Location1" Identity Group to the Internal User.
3.
In the Authorization Policy condition, specify one of the following:
–
"Internal Users.Identity Group Equals IdentityGroup:User Identity Groups:Employee:Location1"
–
"Internal Users.Identity Group Matches.*Location1"
CSCto82519
Saving your Active Directory configuration while the DNS is down takes a very long time
Cisco ISE requires connectivity to Active Directory (including DNS) when saving the configuration. If the DNS is not reachable, then the save function may time out before it can complete.
Workaround
Ensure that the DNS is available and reachable before saving your Active Directory configuration.
CSCto84932
The Cisco NAC Agent takes too long to complete IP refresh following VLAN change
The Cisco NAC agent is taking longer than normal to refresh IP address due to double IP refresh by supplicant and NAC agent.
Workaround
Disable the Cisco NAC Agent IP address change function if there is a supplicant present capable of doing the same task.
CSCto97486
The Mac OS X VLAN detect function runs between discovery, causing a delay
VLAN detect should refresh the client IP address after a VLAN detect interval (5) X retry detect (3) which is ~ 30 sec, however it is taking an additional 30 sec.
This issue has been observed in both a wired and wireless deployment where the Cisco NAC agent changes the client IP address in compliant or non-compliant state since Mac OS X supplicant cannot.
An example scenario involves the user getting a "non-compliant" posture state where the Cisco ISE authorization profile is set to Radius Reauthentication (default) and session timer of 10 min (600 sec). After 10 min the session terminates and a new session is created in the pre-posture VLAN. The result is that the client machine still has post-posture VLAN IP assignment and requires VLAN detect to move user back to the pre-posture IP address.
Workaround
Disconnect and then reconnect the client machine to the network.
CSCtq02332
Windows agent does not display IP refresh during non-compliant posture status
The IP refresh is happening on the client machine as designed, but the Agent interface does not display the change appropriately (for example, following a move from preposture (non-compliant) to postposture (compliant) status).
Workaround
There is no known workaround for this issue.
CSCtq02533
The Cisco NAC Agent takes too long to complete IP refresh following VLAN change
The Cisco NAC agent is taking longer than normal to refresh IP address due to double IP refresh by supplicant and Cisco NAC agent.
Workaround
Disable the Cisco NAC Agent IP address change function if there is a supplicant present capable of doing the same task.
CSCtq06832
Time and Date conditions need to be updated correctly when changing time zones
Configure the Time Zone in Cisco ISE to be "IndianStandardTime," for example, and create a Time and Date condition (Ex: From Time 10:00 AM & To Time 8:00 PM). Then update the Time Zone from IST to UTC. The existing Time and Date condition does not get updated per the new specified Time Zone.
This issue comes up when changing the Time Zone after creating the Time and Date condition in the Policy > Conditions > Common > Time and Date page.
Workaround
There is no known workaround for this issue.
CSCtq07271
Cisco ISE returns a misleading message after Change of Authorization on an Inline Posture node
When the administrator issues a Change of Authorization Session Termination, Cisco ISE returns a "successful" message, but the Inline Posture node cannot find the session and drops the request.
CSCtq07311
Change of Authorization shows "0" sessions on Policy Service node are down
This issue has been observed where when one or more Policy Service nodes are behind an Inline Posture node, a client machine connected via a particular Policy Service node has authenticated, but has not yet completed posture assessment, and that Policy Service node then goes down (administratively or otherwise).
Note
As designed, another Policy Service node in the node group detects that the peer node has gone down and issues a Change of Authorization to terminate the pre-posture session on the client machine, but that measure does not succeed.
Workaround
If the client machine re-initiates authentication, the new request goes to another Policy Service nod (assuming that the Network Access Device is configured with multiple RADIUS servers) and authentication and posture assessment should work as designed.
CSCtq09004
Windows 7 guest access not successful from IE8 and Chrome 10
Guest access fails over a wireless LAN controller connection. The login session does not appropriately redirect the user authentication request. This is likely due to IE8 and Chrome10 browsers on Windows 7 being unable to redirect the RADIUS authentication request to the controller.
Note
This issue has not been observed using Mozilla Firefox.
Workaround
Ensure that the certificates in the controller are accepted by the IE8 browser on the Windows 7 client correctly.
CSCtq12630
Guest page not redirecting to original URL after wireless login using Internet Explorer 8 or 9
Workaround
In Internet Explorer 8, end user should click No in the resulting login dialog that pops up to be redirected to the correct page. In Internet Explorer 9, after the login success message appears, re-enter the original URL in the browser address bar.
CSCtq15859
IP address refresh does not work with 64-bit Internet Explorer
IP address refresh via ActiveX is not supported on 64-bit versions of the Internet Explorer browser. Such functions are only available in 32-bit versions of Internet Explorer.
CSCtq53690
Scheduled Monitoring and Troubleshooting incremental backup switches off following failed backup attempt
Workaround
If one of the scheduled Monitoring and Troubleshooting node backup events fails, the administrator needs to enable the "Incremental Backup" option again in the Administration > System > Operations > Monitoring Node > Scheduled Backup page.
CSCtr09694
MAC address search at Reports > Query and Run should not be case sensitive
While launching reports, the MAC address search is case sensitive, but should not be.
Note
There is no known workaround for this issue.
CSCtr32014
Three-hour Cisco ISE upgrade time on scale configuration
This problem occurs during upgrade from one Cisco ISE running release 1.0 software to release 1.1.x.
Note
There is no known workaround for this issue.
CSCtr45402
Server Authentication Summary Report takes more than 1 minute to launch
This issue has been observed when viewing more 30 days worth of data on a larger (3395) Cisco ISE platform running Cisco ISE, Release 1.0.4.
CSCtr57280
IP-to-MAC address binding fails in wireless environment with RADIUS and HTTP probe
RADIUS accounting messages from a WLC do not send the endpoint IP address. This is different from the RADIUS accounting messages from wired infrastructure. This makes the RADIUS method ineffective for IP-to-MAC address binding on Cisco ISE.
Workaround
Enable a DHCP probe and configure the setup for Cisco ISE to profile endpoints with DHCP packets.
CSCtr58811
Need to log out and log back in to get Advanced License functionality
After installing an Advanced License on top of an existing Base license, the administrator is not able to view advanced feature pages such as Posture, Profiler, and Security Group Access.
Workaround
Log out and log back in again to view Advanced feature pages.
CSCtr66929
Selected month and year while configuring file "Date" condition
If you specify either just the year or month in the "Date" field of the Policy > Policy Element > Conditions > File Condition configuration window, the date does not get saved along with the policy.
Workaround
Always specify the correct date.
CSCtr68491
Windows Internet Explorer 8 Info button on compound condition format is empty
When you hover over the "Info" button in the Go to Policy > Policy Elements > Conditions > Posture > Compound Condition page, the pop-up bubble remains empty.
This issue has been observed using IE8, but the text appears as designed in Mozilla Firefox.
CSCtr88091
You may experience slow response times for some user interface elements when using Internet Explorer 8.
Symptom When using Internet Explorer 8, the check- boxes on pop-up dialogs for selecting and deselecting groups and attributes may be slow to respond to clicks for changing states.
Conditions
The use of Internet Explorer 8.
Workaround
Do any of the following:
•
Consider using an alternative web browser. Firefox does not show the same symptoms.
•
Be patient. The check-boxes in IE8 respond after clicking them several times.
•
Enter the group names manually, and avoid using the pop-up dialogs.
CSCts10323
Internet Explorer running slow during client provisioning
Internet Explorer has an option where you can turn the "check for revocation lists" function on or off.
When this option is enabled and the dACL simultaneously does not allow access to CDP servers, Internet Explorer "freezes up" for about a minute while it tires to access the requisite CDPs.
CSCts20529
Authorization profile getting saved with incomplete information
This issue occurs when using the "auto-smart-port," "Filter_ID," "wireless lan controller," or "Posture Discovery" fields in the configuration page.
Note
Because of this mismatch in attribute values, the resulting authorization policy may not work properly.
Workaround
Click anywhere in the window while creating an authorization profile when using any of the above mentioned attributes. The authorization profile is then saved properly.
CSCts36792
No "Cisco ISE Configuration Changes" alarms appearing on Conditions
Guest simple and compound conditions can be created, edited, and deleted on the admin UI, but no logs are generated in Cisco ISE accounting.
This problem is limited to creating, modifying, and deleting guest simple and compound conditions in the Policy > Policy Management > Conditions > Guest page
Workaround
There is no known workaround for this issue.
CSCts48857
Failed to send notification from UTF-8 Email address
An "Internal error encountered. Please see logs for more details." error message appears when attempting to notify a Guest user by email of their new account information.
This problem occurs only for user IDs that contain UTF-8 characters outside the US ACSCII range.
Workaround
There is no actual workaround at this time, however, you could try substituting a traditional ASCII Email address for the address containing UTF-8 characters.
CSCts80116
OPSWAT SDK 3.4.27.1 causes memory leak on some PCs
Client machines that have version 8.2.0 of Avira AntiVir Premium or Personal may experience excessive memory usage.
Note
This has only been observed with version 8.2.0 of Avira AntiVir Premium or Personal. Later versions of the application do not have this issue.
Workaround
Install later version of Avira AntiVir Premium or Personal.
CSCts89508
Authorization fails when a UTF-8 username and password credentials are used
Microsoft native supplicants for Windows 7, Windows XP and Windows Vista require the following hot fixes in order to support UFT-8 RADIUS user names:
•
For Windows XP
http://support.microsoft.com/default.aspx?scid=kb;EN-US;957218•
For Windows Vista, Windows 7, and Windows Server 2008
http://support.microsoft.com/kb/957424Workaround
Cisco AnyConnect 3.1 conducts EAP authentication with UTF-8 username successfully.
CSCtt17378
Cisco NAC Agent does not pop up if TLS 1.0 is not enabled in Internet Explorer settings
The problem occurs when all the following conditions are met:
•
Cisco ISE is operating with a FIPS 140-2 module
•
The client machine "Local security settings > System cryptography: Use FIPS algorithm" is enabled.
•
The client machine Internet Explorer Advanced settings, SSL3.0/TLS 1.0 is option is disabled.
Workaround
Ensure TLS 1.0 is enabled in Internet Explorer and restart the Cisco NAC Agent.
CSCtt25262
Externally-authenticated administrator users cannot register nodes
Workaround
Cisco ISE will not allow the external administrator to register nodes. Create an internal user to perform the registration process.
CSCtt93787
Files without extensions are not downloaded correctly using Cisco NAC Web Agent
When the Cisco NAC Web Agent invokes file remediation, it does not download the file as designed. Instead, the Agent attempts to open the file.
Workaround
There is no known workaround for this issue.
CSCtu39612
Cisco ISE Inline Posture node is not accessible from the Admin ISE node user interface after an upgrade to ISE 1.1.x
Workaround
Follow the instructions provided in Upgrade from Cisco ISE, Release 1.0.4 to 1.1.1 with Inline Posture.
CSCuh75971
Issue running applet with latest Java 7 update 25 on Windows / Mac
If Java 7 update 25 or above is installed, launching of Agents or Network Setup Assistants during client provisioning or onboarding process on Windows or Mac clients would take about 3 minutes as this Java update has Perform revocation checks enabled by default. This causes the applets signed certificates to be verified against issuers CA server, which is currently blocked, and there is no way to open the traffic to CA server on a switch because switch does not support host name based ACL.
Workaround
If you are using Java 7 update 25, make sure to turn off Perform certificate revocation checks in Java.
Open Java Control Panel, click the Advanced tab, go to Perform certificate revocation checks on and select Do not check.
CSCuh81724
ISE - Authentication Flow Diagnostics log targets removed in 1.1.4 p2
While upgrading from Cisco ISE Release 1.1.4 patch 1 to patch 2, the log targets configured for `Authentication Flow Diagnostics' might get removed.
Workaround
After upgrading to release 1.1.4 patch 2, navigate to Administration > Logging > Logging Categories and re-configure the log targets.
CSCtv17606
Monitoring and Troubleshooting requires an appropriate error message if backup/restore process fails
When you try and perform a Monitoring and Troubleshooting backup/restore from the Cisco ISE administrator user interface, which is intended only to restore Administrator ISE nodes, the message displayed reads, "% Error: Cannot find ise_backup_instance.log in the backup file % Application restore failed." Instead, a message like "% Error: Cannot ISE M&T backup can only be restored web interface % Application restore failed" would better advise users of the issue.
CSCtv21758
You are unable to Unquarantine an endpoint (with Endpoint Protection Services) using the IP address of the endpoint.
Workaround
Use the MAC address to unquarantine the endpoint.
CSCtw79431
Exiting the Cisco Mac Agent while in "pending" state displays the wrong user message
When exiting a Cisco Mac Agent that has not successfully logged in yet, reveals a "successfully logged out from network" message to the user, when in fact there is no log-in status change.
Workaround
There is no known workaround for this issue.
CSCtw98454
Guest accounting report filter not working
If you specify a particular username in the Guest user filter in the guest accounting report, Cisco ISE still shows results from other users, as well.
CSCtx03427
Create Alarm Schedule returning XSS error messages
This issue has been observed when the configured alarm name contains "onChange".
Workaround
Rename the alert name to something that does not contain "onChange".
CSCtx31601
Cannot add Network Access user, but able to import users
When the string "alert" appears in the Network Access user name, the Cisco ISE user interface prevents it from being created.
Workaround
If you import a user with that name, it will work.
CSCtx59957
A warning/pop-up appears while creating a Guest Time profile
A pop-up with the message "Warning: Unresponsive script" can appear when adding a time profile in Guest settings under Administration.
Workaround
Dismiss the pop-up message and try again.
CSCtx60819
Database restoration runs out of space on VMware systems with only 60 GB disk size
This issue only occurs on unsupported (EVAL) VMware disk installations where the restoration server has a single disk of only about 60-70 GB of disk space.
Workaround
Use a VMware server installation with a larger disk size (like 100 GB) if possible.
CSCtx62403
Admin can control sessions on a node on which replication has been disabled
When a Cisco ISE certificate has expired, replication is disabled on that node. When replication is disabled on a node, active sessions affecting that node can be controlled from the Administrator ISE node. Therefore, the Cisco ISE administrator can see active sessions on nodes where replication has been disabled and can issue Change of Authentication for associated endpoints.
Note
Certificate validity is validated every 24 hours in a deployment for each node.
CSCtx62657
Cannot deregister an Inline Posture node
On the Deployment List Page, when you attempt to deregister a node by clicking the appropriate button, the administrator user interface is grayed out until a message reading "Deregister is done. Node will be re-started." appears.
Workaround
Log out and log in to the administrator user interface again. The deregistered node is no longer visible in the user interface.
CSCtx68334
Promotion for Secondary Monitoring and Troubleshooting fails if the Primary node is down
While promoting the secondary Monitoring and Troubleshooting node while the primary node is down, then Cisco ISE returns a transition failure and the database rolls back.
Workaround
Try to perform the operation again to overcome this issue.
CSCtx69191
Mozilla Firefox does not function with OpenSC middleware software
If you create certificate an authentication profile using the Cisco ISE Active Directory > Groups page, install the OpenSC middleware software, then go to the management station connected to a CAC authentication device and insert the CAC card while attempting to log in via Mozilla Firefox, authentication does not take place as designed.
The key issue is that the e-mail certificate that Cisco ISE normally uses to authenticate the administrator does not appear for selection by the browser, and any other certificate fails during connection.
Note
This issue has been observed using OpenSC middleware on Mac OS X (Safari and Chrome both work as designed). CACkey middleware works as designed with Safari, Chrome, and Firefox.
CSCtx79725
Cisco ISE freezes during startup if first DNS does not respond
This issue has been observed if/when primary DNS is misconfigured or down.
Workaround
Specify a different (operational) DNS server.
CSCtx80886
When switching to FIPS mode, there is no way to delete the self-signed certificate on an Inline Posture node
This issue occurs when the original self-signed certificates still installed on the Inline Posture node, even though it is not actually used by Cisco ISE.
Note
Do not remove the default self signed certificate and join the Inline Posture node to the deployment using FIPS compliant CA certificates.
Workaround
Deregister the Inline Posture node, remove the self-signed certificate, and re-register the Inline Posture node.
CSCtx90696
Cisco ISE does not work after updating the IP address
This issue may be that the primary DNS server used by Cisco ISE has not yet been updated with the new IP address.
Note
Do not use the
ise/admin#command when you change the Cisco ISE appliance IP address. Instead, simply set the new IP address with theSelection ISE configuration optioncommand.Workaround
Use the "ip address" command in the CLI to specify a new IP address. (Make sure the primary DNS server is also updated with new records.)
CSCtx92251
Using the Cisco ISE "Replace" function on a secondary node does not assign protocols or replace the certificate
Using the "Replace" button when replacing a certificate on a secondary node (such as a Monitoring and Troubleshooting or Policy Service node) does not move the protocols to the new certificate or remove the old certificate.
This issue has been observed when you install the certificate on a Monitoring and Troubleshooting node, take the same Certificate Signing Request and have it signed by a different Certificate Authority, then install the certificate on the Monitoring and Troubleshooting node with the "Replace" option enabled.
Note
Both certificates are still present on the node and EAP and MGMT protocols are not part of the new certificate from the second Certificate Authority.
Workaround
Create a new certificate from the second Certificate Authority, edit protocols, and then delete the old certificate from the original Certificate Authority.
CSCtx93416
Database restoration fails when upgrading from software release 1.0.4 to release 1.1.x
The restore process fails the Cisco ISE Release 1.1.x deployment has been installed via upgrade and the hostnames in the topology have different assigned roles, but hostname of the original primary node name (when the release 1.0.4 backup image was created) is still a node name appearing in the new deployment, but is no longer the primary node in your deployment.
Workaround
There are two possible workarounds for this issue:
•
Change hostname on the new release 1.1.x primary node to match what it was during the backup, and try to restore the database again.
•
Change hostname on new release 1.1.x primary node to be something completely new (a name that was not used at all in the original release 1.0.4 deployment).
CSCtx94533
Some endpoints appear as "pending" following posture assessment
It can take up to 10-15 minutes to get the endpoint status updated to reflect a "Registered" state, where the endpoint goes through posture assessment and gains full access to the network.
CSCtx95251
Deployment page load exceeds six minutes when two or more nodes are unreachable
This problem may occur only if the nodes are not reachable, there are lots of pending messages in the secondary node, and if there is possibly a firewall issue.
Workaround
Make sure all the nodes are reachable, there are no pending messages, and there are no firewall issues.
CSCty00899
LiveLog Reports cannot be opened
When you drill down on LiveLog details to launch a detail report, Cisco ISE returns an error message.
Note
This issue is seen only if you leave your browser idle for more than one day.
Workaround
Users can logout and log in again to drill down to report details from live logs.
CSCty02167
IP refresh fails intermittently for Mac OS 10.7 guest users
This problem stems from the way Mac OS 10.7 handles certificates. Marking the certificate as "trusted" in the CWA flow is not good enough to download the java applet required to perform the DHCP refresh function.
Workaround
The Cisco ISE certificate must be marked as "Always Trust" in the Mac OS 10.7 Keychain.
CSCty05129
"Monitor All" function does not take effect after policy refresh
When the administrator enables or disables the Monitor All function, devices do not get policy updates as designed. This has been observed in cases where the cells are not updated manually.
Workaround
Cisco recommends using the Monitor Mode function on a per cell basis, rather than Monitor All. If you have enabled the Monitor All function, edit at least one cell per column in which a value exists. You can also manually remove the policies from the network device and update them again from Cisco ISE.
CSCty05157
The Cisco ISE dashboard is not working for administrator user names with more than 15 non-English characters contained in the username
This issue has only been observed for user names created using a language other than English.
Workaround
Update the administrator user names so that they are less than 15 characters in length.
CSCty08194
The administrator password character list is restricted during the reset-config function
When the administrator tries to perform a "reset-config" function from the Cisco ISE CLI, the password character list for the administrator password is more restricted than at the time of installation. For example, during installation "!" is valid special character accepted for the administrator password. During the "reset-config" operation, however, "!" is not accepted as a valid password character.
CSCty10369
Management functions operate slowly on VM with UCS SATA-2 storage
The following issues have been cited:
•
Importing 1,000 users in a deployment setup takes 8 more minutes than a dedicated hardware appliance (or VM SCSI HDD 10K rpm).
•
Full synchronization functions take up to 12 hours on a VM UCS with SATA2 HDD.
•
Disk latency is up to 50% greater on SATA-2 7200 rpm storage devices.
Workaround
Ensure external storage units connected to UCS feature SCSI/SAS 10K or 15K RPM technology.
CSCty10692
Requirement is used by Policy - Need tooltip on OS
When a requirement is used by a policy in Cisco ISE, the operating system of the policy and the requirement need to match. Currently, the requirement operating system field is disabled in the requirement page and the administrator is not able to tell with which operating systems this requirement is associated.
Workaround
There is no known workaround for this issue.
CSCty19010
Editing Cisco ISE failure reason information returns error message
If user edit some of the failure reason codes in the Administration > System > Settings > Monitoring > Failure Reason Editor page, Cisco ISE may display an error 500 message.
"12818 Expected TLS acknowledge for last alert but received another message 24466 ISE Active Directory agent is down"
Note
This issue can occur when failure reason information includes data that can indicate a cross site scripting attack; such as the string "alert" and "<" and ">" characters.
CSCty19774
Client Provisioning is not working when an Inline Posture node is connected to a VPN
This can happen when the client machine successfully passes authentication and ACLs are downloaded to the Inline Posture node and there is connectivity to Policy Service node, but the URL redirect function is not working correctly.
Note
This issue has been observed on a on non-Windows 7 client machine. (XP clients do not update automatically because the root certificate list is not up to date.)
Workaround
One way to get around this problem is to do update your root certificates.
CSCty28274
System and RBAC administrator data access permission issue
When an administrator other than the Cisco ISE administrator user created during installation logs into the Administrator ISE node user interface and navigates to Administration > System > Admin Access, they should be able view and update the administrator information when clicking on their own username. Instead, Cisco ISE displays a "Permission Denied" message.
Workaround
Administrators facing this issue can click on the logged-in username in the top right corner of the on user interface and edit their details from the pop-up dialog that appears.
CSCty39209
IPsec and SSL VPNs do not work if FIPS function is enabled or the PAP protocol is disabled
If you enable FIPS 140-2 functionality you must also turn off PAP authentication in the Allowed Protocols page.
Once you turn off PAP, then any VPN client that uses group authentication, which always requires PAP, becomes incompatible with Cisco ISE.
CSCty42816
Wireless Guest login fails using Google Chrome browser
Self-service guest users are unable to get on to the network from Chrome Browser during Wireless Local Web Authentication. Cisco ISE displays an error page with user credentials after the self service guest user changes the password and tries to get onto the network.
Workaround
Cisco recommends using another browser for this operation.
CSCtw50782
Agent hangs awaiting posture report response from server
Workaround

The issue occurs with Mac OS X 10.7.2 clients.
Kill the CCAAgent Process and then start CCAAgent.app.
Perform the following:
1.
Go to Keychain Access.
2.
Inspect the login Keychain for corrupted certificates, like certificates with the name "Unknown" or without any data
3.
Delete any corrupted Certificates
4.
From the pull-down menu, select Preferences and click the Certificates tab
5.
Set OCSP and CRL to off.
CSCty51216
Upgrading Mac OS X Agent version 4.9.0.638 to later versions fails.
Workaround

1.
Remove the "CCAAgent" folder from temporary directory
2.
Reboot the client
3.
Connect to Web login page and install the Agent from there
CSCty52694
Mac OS X Agent needs to be installed from Client Provisioning Portal for VPN
When a Mac OS X user connects through VPN, the Mac OS X Agent does not pop up as designed.
This can happen if the Mac OS X Agent has been installed directly from Cisco Connection Online (CCO) or via application installation from an IT department instead of through The Cisco ISE client provisioning portal.
Workaround
Uninstall the agent from the system in question and reinstall the agent from the Cisco ISE client provisioning portal.
CSCty61980
Cannot get Out-of-Band Security Gateway Access PAC for network devices after upgrade
This issue can occur on a system that has been upgraded from Cisco ISE, Release 1.0.4 where device definitions were also updated as part of this upgrade. (The PAC file that is downloaded is invalid and Cisco ISE returns an error message.)
Workaround
Delete and recreate the network device definition for any device where you need to generate an Out-of-Band PAC. You can do this by creating the necessary entry in the administrator user interface or exporting the device definition, deleting the entry, and adding the device definition again.
CSCty91514
Custom Guest Portal does not enforce Details Policy during Self Service
When creating a custom Guest Portal under Multi-Portal Configurations, which allows Self Service in Cisco ISE 1.1.x, the Details Policy is not enforced when a user creates their Guest Account.
CSCtz01339
Getting directed to Windows client provisioning flow on Android 2.3.3
Following user authentication via the Guest Portal and device registration, the device is going through the Windows client provisioning flow instead of being redirected to the Android Market place.
CSCtz01754
The certificate and Cisco ISE CA names are missing in Android 2.3.3. EAP-TLS
After a user authenticates via the Guest Portal and registers their device, they are then able to download and run the Supplicant Provisioning Wizard from the Android market place. After running the wizard, however, the "name" field is blank in the user certificate and the Cisco ISE certificate is blank as well.
CSCtz21155
Assigned profile is missing under Network > 802.1X on Mac OS 10.6.3 machines
Once the TLS profile gets configured, the end user is presented the following message:
"Device configured. Go to System Preferences, choose Network, choose the wired (Ethernet) network, select <profile name> from the 802.1X menu, and click connect."
However, the profile is missing under System Preferences > Network > 802.1X, and the user is stranded in that step of the login process.
Workaround
Close the Network window and open it again. You should be able to see the appropriate profile under Network > 802.1X. (This is applicable only for wireless deployment scenarios.)
CSCtz25101
Asset Registration Portal login event not shown in Live log
Sponsor Portal login events are showing up as designed, however.
CSCtz28932
Client Provisioning for Supplicant Provisioning flows is broken after upgrade
Policies that were previously working now result in the "register" tab not appearing to users logging in via the Self-Provisioning page for Windows devices.
This issue has been observed using Apple iPhone/iPad over a dual- SSID environment.
CSCtz31672
NullPointer Exception when user redirects to CPP evaluate page from mobile
Cisco ISE returns a "Cisco ISE is unable to determine access privileges in order to access the network. Please contact your system administrator." message, and exceptions also appear in the ise-psc.log file. This issue is likely because the login session is trying to use an old session for the same device MAC address, which is not found in session directory.
Workaround:
The user logging in via their endpoint must open a new browser instance or clear the existing URL, and type enter the destination URL again to be redirected to the CCP evaluate page with expected device information.
CSCtz36060
ARP authentication should show up in AAA diagnostics even with default log level
MyDevices portal login audit can be seen in the AAA Diagnostics log as long as ARP logging is set to INFO or DEBUG.
CSCtz37988
Two primary Administrative ISE nodes appear in deployment
This issue can occur after the primary Administrative ISE node becomes disconnected and the secondary Administrative ISE node gets promoted to the primary role after 20 minutes or so. Then much (a day or so) later, the original primary is brought back online, two primary and secondary Administrative ISE nodes appear in the deployment setup.
CSCtz40127
Certificate issue after SCEP failover where servers reside in different domains
(This issue has been observed in a Windows 7 environment.)
CSCtz41262
Authorization policy does not match when the MAC address uses the colon delimiter (00:00:00:00:00:00)
When configuring policies using the Calling-Station-ID as a component, the authorization attempt does not match the rule if you use the value in the Cisco ISE report. When configuring this type of policy in Cisco ISE, Release 1.0.4 or 1.1, you will have to rely on the RADIUS packet information and not the ISE report.
Workaround
Use the TCPDump function in Cisco ISE to see the correct value that is being sent from the network access device and configure the Calling-Station-Id (MAC address in this case) using the hyphen-delimited format (00-00-00-00-00-00).
CSCtz42775
Java "unknown host" exceptions appear when downloading Client Provisioning resources
Cisco ISE still reflects that the "Resources downloaded successfully" in the bottom right corner of the Cisco ISE administrator user interface.
Workaround
Please make sure the DNS server is up and running and the client provisioning Feed Server is reachable from ISE.
Note
This issue may occur more commonly where the DNS server has gone down.
CSCtz49846
Cisco ISE does not contain the ASA attribute 146 Tunnel Group Name which is sent on the Access Request
This issue can appear when the name of the attribute added in Cisco ISE includes a "." character.
Workaround
Ensure that the attribute name does not include a "." character. This also applies to some of the existing attributes in the Cisco-VPN300 dictionary. The attribute names should also be modified so that they do not include a "." character.
CSCtz55815
Default Gateway is not changed if the new value is a part of old value
If the administrator specifies a new default gateway on the Cisco ISE that is too similar to the old default gateway (like a different address on the same 24-bit subnet for example), the gateway address does not change.
Note
This issue was observed on a VMware ESX 4.1 environment.
CSCtz56547
Cisco ISE does not display alarms or notifications on "OutofSync" issues
This has been observed when there is a time-shift event on an Administrative ISE or Policy Service node. Cisco ISE should notify admin user on all arising issues due to NTP dependency, as this issue can consume considerable time to troubleshoot.
CSCtz61792
Administrator Username column in EPS Report shows incorrect data
The Cisco ISE EPS operation history report displays the user as "internal" instead of the actual administrator user ID.
Workaround
Cisco recommends using the REST API, instead.
CSCtz63899
Previously registered device is not able to re-connect
Once a device has been registered with Cisco ISE and attempts to connect to the network again (as if a new device), the device should automatically attempt to connect to the secure network. However, the device is able to connect to secure network on second or third attempt. This issue can occur if the device is unable to complete the full EAP handshake with the NAD or WLC.
Workaround
Device can connect to closed network automatically in second or third attempts. or user can try flapping the interface to be connected to closed network.
CSCtz67158
IP address is not refreshed after reinstating the device
Reinstating a blacklisted device in the My Devices portal does not refresh the IP address. This can happen when the administrator modifies the default blacklist authorization profile so that it includes ACCESS-ACCEPT and different sets of ACLs and VLANs.
Since reinstating the device issues a CoA and triggers reauthentication, the IP address is not refreshed by the blacklisted device.
Workaround
The user can perform an IP address release/renew or turn off Wi-Fi on the device.
CSCtz67372
External Admin Groups are not available until authentication password is changed
This issue can come up when you configures external identity source (LDAP or Active Directory), import groups from the source, and then try to create an "external" RBAC Admin Group that refers to one or more groups imported from the external ID source. (That is, the Identity Source in the Authentication Method' page under 'Administration > System > Admin Access page has not yet been set to the external ID source containing the groups.) As a result, the groups from the external ID source are not shown in the Admin Group page in Cisco ISE.
Per the current design, you can configure multiple identity sources, but only one may be enabled at a time.
Note
The External Group section in the Admin Group create/edit page in Cisco ISE only shows groups from the external identity source that are currently enabled.
CSCtz74022
The device registration page is blank on a Windows 7 phone on which a language locale other than English is specified
This issue has been observed when running performing device registration in a single SSID environment.
Workaround
Set the client browser locale to English.
CSCtz80240
Secondary node never becomes standalone after de-registration
The secondary node is de-registered successfully but a "The following deregistered nodes are not currently reachable: <name>. Be sure to reset the configuration on these nodes manually, as they may not revert to Standalone on their own." message appears to the administrator.
Workaround
Log in to the administrator user interface with internal Cisco ISE administrator credentials when de-registering a node.
CSCtz81107
Android registration fails if the user modifies the certificate while installing
Android users are able to modify certificate names when installing the Cisco Supplicant Provisioning Wizard. If the user does in fact modify the certificate name, then the device is not able to connect to the secure network.
Note
This issue applied to both single- and dual-SSID deployments.
CSCtz83096
Cisco ISE ignores authorization exceptions when working with an option that matches multiple policy rules
If you add a standard rule within an authorization policy, for example, "if Network Access: Username STARTS_WITH letters `te' then DenyAccess," add an additional Exception Rule like, "Network Access:Username EQUALS `testUser' then PermitAccess," specify that the policy should operate using the "Multi-Matched" option, and authenticate a user called "testUser," the result is that Cisco ISE denies access to that user when it should permit access.
CSCtz83530
Android devices must manually connect to the secure network if the user reboots the device
This is due to the fact that users be required to enter storage credentials again to connect to the secure network using certificates that were installed during initial device registration.
CSCtz84351
Cisco ISE stops responding to authentication requests
Cisco ISE intermittently stops authenticating and returns "WARN RADIUS: RADIUS request dropped due to system overload" messages. This issue has been observed even when CPU usage is low and there is plenty of free memory.
Workaround
Disable and then re-enable Cisco ISE services.
CSCtz90726
An error appears when attempting to create an inline "Allow Protocols" definition after having previously canceled the operation
This issue can appear when you select the option to create an Allowed Protocols definition, click Cancel during the process, and then attempt to create the definition again.
Workaround
Clear the browser cache and attempt to create the definition again.
CSCtz91998
New client provisioning ports need accommodated during upgrade
After upgrade to Cisco ISE, Release 1.1.1, users are unable to download Cisco NAC Agent or NAC Web Agent after clicking the install button if the appropriate client provisioning port (8909) has not been opened across the network.
Workaround
Open up ACL for port 8909 to allow client access to ISE server. This ACL can be statically defined on the NAD or dynamically downloaded through ISE authorization policy
CSCtz93520
Exceptions noted in logs while registering a node
In a split domain upgrade older certificate is not working when older secondary is made as primary.
Workaround
After upgrade Export the secondary certificate into primary before registration.
CSCtz97075
Device registration session directed to wrong location when Administrative ISE node and Policy Service node become disconnected
As a result, users are not able to complete device registration, account for lost devices, or remove old devices from Cisco ISE.
Users are supposed to be redirected to the self-provisioning portal during both single- and dual-SSID sessions. This function requires an active connection between the Administrative ISE node and Policy Service node. If the two become disconnected, device registration fails. (This also applies to users trying to account for lost devices, or remove old devices from Cisco ISE.)
CSCtz97833
HTTP time out error received during user session quarantine period
Certificates used in Cisco ISE can be PEM- or DER-formatted. Cisco ISE also accepts certificate chains of multiple certificates. Cisco ISE does not, however, accept certificate chains which have a mix of both PEM- and DER- formatted certificates. This error is not reported as precisely in EPS REST calls, it just shows up as generic failed request.
Workaround
Check to see whether you are inadvertently mixing both PEM and DER formatted certificates.
CSCtz98295
Opera browser "Back" button displays My Devices portal after user has logged out
After logging out of the My Devices portal, the user can click the back button and the previous page appears.
Workaround
Recommend not using Opera if concerned.
CSCtz99443
Policy Service nodes on the other side of WAN links display "IN-PROGRESS" status continuously
This issue can occur on secondary nodes that are deployed over WAN links where there are a large number of replication events generated on the Administrator ISE node.
Note
This issue is sometimes due to latency issues impacting WAN links. If there are a significant number of replication events generated by the Administrator ISE node, these events take longer time to be replicated and applied to the Policy Service nodes that are deployed over a WAN link. As a result, replication events accumulate on the node and the replication status appears as though replication is continuously in progress.
CSCua00821
Error messages appear when you configure Active Directory via the CLI
When performing Active Directory configuration via the Cisco ISE CLI, selecting option number 5 (Clear Active Directory Trusts Cache and restart/apply Active Directory settings), the following errors may appear:
•
log4j:WARN No appenders could be found for logger (com.cisco.cpm.acs.nsf.config.handlers.ad.cli.ADAgentRestart).
•
log4j:WARN Please initialize the log4j system properly.
Workaround
From the Cisco ISE CLI, enter the "application configure ise" command and select option number 5 again.
CSCua03362
Need to enable automatic connection polling on Mac OS 10.7.x wired connection
The Cisco ISE profile selection dialog does not appear if the "Enable automatic connection" option is not enabled (under System Preferences > Network > Ethernet > Advanced > 802.1X) on the Mac OS X client machine after the supplicant provisioning wizard is downloaded and installed.
Workaround
Be sure Mac OS 10.7.x wired device users know to choose the profile manually (like Mac OS 10.6.8, for example).
CSCua03889
Guest users are asked to accept the Acceptable Use Policy twice when first logging into Cisco ISE with password change
When the administrator sets up a multi-portal configuration, sets the Acceptable Use Policy to be accepted on "First Login," and enables the "Requires guest users to change password at expiration and first option" option, the guest user needs to accept the Acceptable Use Policy twice.
CSCua05003
Service status is not correct if the ARP port number changes
This issue has been observed when an end-user attempts to access the My Devices portal via the configured port, but is not able to.
Note
Accessing the My Devices portal via the last configured network port works as designed (although and error message appears).
Workaround
If you have changed the port used for the My Devices portal, restart the Administrator ISE node and My Devices portal should restart on the correct port.
CSCua05261
Windows XP 32-bit OS cannot connect to closed network if not broadcasting
This issue can occur when the open network connection mode is set to "Automatically connect to network" (which is a default option on Windows XP.
Note
This issue has not been observed in a Windows 7 environment.
Workaround
Set the connection mode for Windows XP open networks to "manual" or "on demand":
1.
Select the open network profile.
2.
Uncheck the "Connect when this network is in range" option.
CSCua08884
Restore failed in release 1.1.1 with customer backup of 1.0 version
This issue is most likely due to a corrupted backup file resulting from an unknown operating system issue
CSCua12479
HTTP profiling in Cisco ISE, Release 1.1 is performed after Guest Authentication
Cisco ISE, Release 1.1 does not call upon user-to-agent information until the Guest user authenticates via the Guest portal.
Note
This behavior is different then what is seen in ISE 1.0.4 where profiling kicks off as soon as the user hits the guest portal.
Workaround
You can redirect users to the client provisioning portal. Even if no client provisioning rules exist, the user-to-agent information is called upon when the Guest user reaches that page.
CSCua12479
Profiling via HTTP probes in Cisco ISE, Release 1.1 done after Guest authentication
Cisco ISE, Release 1.1 does not use user-agent information until the Guest user authenticates to the Guest Portal. This behavior is different then what was seen in Cisco ISE, Release 1.0.4 where profiling would initiate as soon as the user hit the Guest Portal.
Workaround
Direct users to the Client Provisioning Portal. Even if no Client Provisioning rules exist, the user-agent information will be picked up when the user hits that page.
CSCua18804
Authorization RADIUS packets fail due to incorrect delimiter
Wireless LAN Controllers can send endpoint MAC addresses in RADIUS packets in various formats, including a series of colons, hyphens, or no delimiter at all. Cisco ISE authorization policies look for hyphen-formatted MAC addresses.
Workaround
Set the MAC address delimiter on the Wireless LAN Controller for the calling station-id to specify hyphens.
CSCua19003
"hostname" and "ip domain-name" warnings are hard to understand
Cisco ISE returns warnings when you attempt to change the Cisco ISE hostname or domain name after initial setup.
Because the warnings are ambiguous and the affect on the system unknown, Cisco recommends that you do not change the hostname or domain name on any deployed Cisco ISE appliances. If it becomes necessary to change these parameters, the only reliable way to accomplish such a change is to re-image and specify different values for these parameters during initial configuration.
Note
There is no known workaround for this issue.
CSCua25187
Employees whose user names are 41 digits long will not see their devices
If the employee name is 41 digits long, then the devices added through the My Devices portal do not show up in the list of employee devices.
Note
Using a 40-digit user ID works as designed, as does a 48-alphanumeric character ID and a 40-digit alphanumeric character ID with one leading alphabetical character.
Workaround
Use less than 41 digits in the user name policy.
CSCua25333
Unable to login to the administration user interface using the username and password credentials set during the initial setup wizard
After running the initial setup wizard with some specific set of username and password values, this problem will occur. The administrator is, however, able to log in to the Command Line Interface with the same username and password.
Workaround
Run the CLI "application reset-passwd" command to reset the administration user interface password to the value specified during the initial setup wizard or another value if desired.
CSCua32575
Firefox browser is not working on Android devices for registration
When the Mozilla Firefox browser is used for registering an Android device, it receives an "unsupported OS device" response From Cisco ISE.
Note
When users register the device via the native Android browser, registration completes correctly.
CSCua38966
Policy Service node replication is disabled
Policy service nodes in which large numbers of (bulk) users have been imported display signs of decreased performance. (The performance level of the three (of 40) Policy Service nodes were below that of other appliances.)
Note
This issue has been observed on a "large" deployment of 40 nodes.
Workaround
Manually synchronize node information.
CSCua40773
IP refresh function is not working in Mac OS X after the session terminates
The VLAN switching function does not take place on Macintosh client machines after Cisco ISE issues the requisite "change of authorization" during login. When Cisco ISE issues the "change of authorization," and open/authenticated networks are in different VLANs, the Macintosh client does not refresh the IP/switch network (VLAN) automatically following re-authentication.
Workaround
The user must manually refresh the IP address:
1.
Launch System preferences.
2.
In the TCP/IP tab, go to Network > Advanced.
3.
Click Renew DHCP Lease button.
CSCua55531
"Anonymous" user authentication fails when operating with CSSC
CSSC expects both "Session Resume" and "Fast Reconnect" PEAP functions. When Cisco ISE transmits a valid TLS Session ID, but either or both of these PEAP functions are disabled or the session time out has elapsed, then CSSC drops the conversation before running the PEAP inner method. The result is that the PEAP outer identity is protected (e.g., "Anonymous") but the conversation is dropped before revealing the unprotected user US, which then compromises the posture validation process because the user name has been "changed."
Workaround
Enabling both of the "Session Resume" and "Fast Reconnect" options in "PEAP Settings" can reduce the frequency, but this issue will still likely occur when Cisco ISE terminates an expired session. To fully resolve the issue, Cisco recommends upgrading from CSSC to AnyConnect version 3.x.
CSCua60073
Changing the log level for system statistics yields incorrect results
After the log level for "System Statistics" is set to "ERROR," the "System Summary" area on the Cisco ISE dashboard is empty.
Workaround
Do not change the log level for the "System Statistics" logging category. (Continue to use the default "INFO" value.)
CSCua71361
Android 2.3.6 devices are not getting a new IP address following the change of authentication session terminate event
Android devices such as Android RAZR are not refreshing their IP address after moving to a new subnet. This issue has been observed on certain Android O/S such as 2.3.6 and ISE issuing CoA session terminate
Workaround
Manually disconnect and reconnect to the network by turning Wi-Fi off and back on again.
CSCua72137
Cisco ISE does not delete old files when the preset localStore size limit is reached
CSCua97013
Apple iOS devices are prompted to accept "Not Verified" certificates
Apple iOS devices (iPhone & iPad) are asked to accept the certificate, appearing to them as "Not Verified," when connecting to WLAN (802.1X).
By design, Apple iOS devices are prompted to accept a proprietary certificate, but Apple OS X and Android devices work without being prompted to accept a certificate.
This happens even when the certificate is signed by a known CA, as there is an intermediate certificate in the server certificate chain.
Workaround
Click Accept to acknowledge the certificate. While browsing any URL, the user is redirected to provision the device. After provisioning, the intermediate certificate is installed on the iDevice.
CSCub01822
Cannot roll back patch when administrator is authenticated using an Active Directory identity store
When the administrator, who is authenticated via an external identity store, applies a patch to Cisco ISE, the patch application process reboots Cisco ISE and the administrator is automatically logged out. After patch application, however, the same administrator cannot them log back into the system and roll back the installed patch.
CSCub16453
Android Self-Provisioning Certificate installation and application erroneously informs the user of a Factory Reset event
This issue has been observed on a device running Android OS version 4.0.3. A pattern lock factory reset message appears when installing the certificate in a device registration flow from the Cisco ISE self-provisioning page. No actual factory reset event actually takes place after the user clicks OK, and the device connects to the network without issues.
Workaround
Set a pin lock and then configure back to pattern lock. This time there are no reset messages. This was tested after removing the cert and supplicant config to start fresh
CSCub17140
Upgrade to Cisco ISE 1.1 and 1.1.x fails when policies use the Blacklist_Access authorization profile.
This issue has been observed when you upgrade the following Cisco ISE releases:
•
Upgrade from Cisco ISE, Release 1.1.3 to release 1.1.4
•
Upgrade from Cisco ISE, Release 1.1.2 to release 1.1.3
•
Upgrade from Cisco ISE, Release 1.1.1 to release 1.1.3
•
Upgrade from Cisco ISE, Release 1.1.1 to release 1.1.2
•
Upgrade from Cisco ISE, Release 1.1 to release 1.1.1
•
Upgrade from Cisco ISE, Release 1.0.3.377
Workaround
Before you upgrade, ensure that you delete all policies that use the "Blacklist_Access" authorization profile.
CSCub17522
IP Phone 802.1X authentication reverts to PAC-based authentication when the "Accept client on authenticated provisioning" option is not enabled
When the "Accept client on authenticated provisioning" option is off then Cisco IP Phone EAP-FAST authentication sessions always end with an Access-Reject event. This requires the IP phone to perform PAC-based authentication to pass authentication. Since Cisco IP Phones perform authentication via authenticated provisioning and not via PAC-based authentication, it is not possible for the phone to authenticate when this option is off.
Workaround
Try one of the following:
•
Turn on the Cisco IP Phone "Accept client on authenticated provisioning" option.
•
Switch from EAP-FAST protocol to PAC-less mode.
•
Authenticate Cisco IP Phones via EAP-TLS rather than EAP-FAST.
CSCub18575
Issue with Cisco ISE sponsor-initiated accounts starting with a "0"
If you create a Guest user starting with a "0," then log out and log back in, you are not able to see the Guest user entry as expected.
Note
There is no known workaround for this issue.
CSCub26470
Wireless license shows Advanced and Base license as "Eval"
Cisco ISE may display Base and Advanced license as "Eval" after installing a purchased Wireless license. This is a cosmetic issue, the license is functional and expires in the expected date.
This issue has been observed in Cisco ISE, Release 1.1.1.
CSCub44915
Activated Guest fails RADIUS authentication where the applicable role uses "FromFirstLogin"
Workaround
Use time profile "FromCreation," or log in first via the Web Portal.
CSCub45799
Wired Mac OS X 10.8 clients fail to auto re-connect to the Cisco ISE network using a new profile
After successfully provisioning the Mac OS X 10.8 client machine with an 802.1X profile for wired a network, the client machine may not provide the user an option to select the specified 802.1X network profile.
When the user is not able to select the "Enable automatic connection" checkbox in System Preference > Network > 802.1X for a wired interface, or if the user manually disconnects from the 802.1X network, the client machine may not present the pop up that would enable the user to select the 802.1X network profile.
Workaround
The user must manually connect to the 802.1X network:
1.
If the System Preference pane is already open, close it.
2.
Navigate to System Preference > Network and select "Wired Network" from the left pane.
3.
Select the appropriate user profile from the right-hand pane and click Connect under 802.1X.
CSCub45895
Unable to save external LDAP/AD groups
Cisco ISE returns a "UTFDataFormatException" message upon saving LDAP groups with multiple Organizational Units and/or Domain Controllers.
Workaround
If possible, reduce the number of Organizational Units and/or Domain Controllers in the deployment.
CSCub56607
Cisco ISE applies a wireless access session against the Advanced license allowable user count when it should not
The wireless session in question should be applied against the Base license count. This issue has been observed in Cisco ISE, Release 1.1.1 where the following functions are set:
•
MAC Filtering is enabled on the SSID and the Central Web Authentication authorization policy is applied
•
Profiling is disabled
•
Posture is disabled
•
The device in question has not been registered via the My Devices Portal
Note
There is no known workaround for this issue.
CSCub56607
Cisco ISE, Release 1.1.1 uses Advanced license for web authentication when it should not consume one
This issue has been observed when a wireless user consumes an Advanced license instead of just a Base license slot, MAC Filtering is enabled on the SSID, and the Cisco ISE authorization policy is designed to support Central Web Authentication.
Note
There is no known workaround for this issue.
CSCub56814
Unable to provision Android 4.1.x device
When registering a new Android 4.1 (Nexus 7) via the Cisco ISE Network Setup Assistant, Cisco ISE is unable to register the device and the user receives an "Unable to apply the Wi-Fi profile" message.
Note
There is no known workaround for this issue.
CSCub57456
Cisco ISE is not sending RADIUS Request messages to external RADIUS server
This issue has been observed in Cisco ISE, Release 1.1 with a wireless-only license. Cisco ISE is not sending the appropriate RADIUS request message to the external RADIUS server, which has been configured as a RADIUS proxy.
Workaround
Uninstall Wireless Only license and Install an Advance License.
CSCub70759
Guest Email IDs greater than 24 characters in length are truncated
When Cisco ISE handles Email IDs, the last characters are getting truncated such that all Email IDs are a maximum of 24 characters in length.
Workaround
Delete the user entry and create a new user again with correct email ID.
CSCub73901
Cisco AV-pair is not accepted if it contains the term "Alert"
Cisco ISE rejects the AV-pair configuration and returns a "Bad Request Parameters" error message. (Scripts in input fields are not processed.)
Note
There is no known workaround for this issue.
CSCub77801
Cisco ISE returns a "Can't create new service" message when adding new allowed protocols
When attempting to add a new Allowed Protocols Service in Cisco ISE, Release 1.1.1, saving a policy without the "Allow EAP-FAST or EAP-TLS" option enabled may result in a "Can't create new service" error.
Workaround
Add the Allowed Protocols service with the default protocols first. After saving, go back into the policy and deselect the protocols that you want, and save the service again.
CSCub82418
Dual SSID registration fails when profiled endpoint's MAC address changes to the Policy Service node MAC address
On reaching the Device registration page, the device MAC addresses is populated using the Policy Service node MAC address. This issue occurs on user devices during registration if there is no MAC address in the Cisco ISE session cache.
Workaround
There are two possible workarounds for this issue:
1.
The user can contact the system administrator so that the session can be cleared from the Wireless LAN Controller (WLC). (The user must be able to supply the Wi-Fi MAC address from the device to do so.)
2.
The user can turn off Wi-Fi for a period of time (equal to slightly more than the session timeout period set on the WLC) and then reactivate Wi-Fi so that the device negotiates a new session with the WLC.
CSCub87687
Acceptable Use policy text character limit in Guest Language Templates
When you attempt to modify the Acceptable Use Policy text under Administration > Web Portal Management > Settings > Guest > Language Template > German_Deutsch, it works as expected if fewer than 4000 characters. If attempting to input larger text content, then upon saving, Cisco ISE returns a "Server Response Language Template successfully saved" message. However, upon refresh, the changes have not been applied to the Acceptable Use Policy text.
Workaround
Use fewer than 4000 characters in the Acceptable Use Policy text field on the Language template, or employ a customized portal with its own logos and HTML pages.
CSCub89895
SNMP process stops randomly due to an issue in netsnmp
The netsnmp daemon on Cisco ISE can halt, causing any SNMP monitoring of the Cisco ISE node to fail until the daemon is restarted. This issue has been observed in Cisco ISE, Release 1.1.1.
Workaround
Remove all SNMP commands and re-add them to start the daemon again or restart the ISE node.
For more information, see: http://sourceforge.net/tracker/index.php?func=detail&aid=3400106&group_id=12694&atid=112694
CSCuc13075
Endpoints are saved with "EndpointPolicy" as "Unknown"
Change of Authorization is continuously sent for an endpoint, causing the CPU usage on the Administration ISE node to run extremely high. (The endpoint may or may no longer be connected to the device the CoA is being sent to.)
This issue can occur in Cisco ISE, Release 1.1.1 where Profiling is enabled as well as CoA.
Note
There is no known workaround for this issue.
CSCuc18502
Cisco ISE upgrade from release 1.1 to 1.1.1 fails because of Blacklist authorization
The Cisco ISE support bundle log returns an error message inside the latest isedbupgrade-data-global-date-time.log file:
[1]Reset Active Directory settings to defaultsWorkaround
If the ISE upgrade fails once, then you need to restart everything from scratch.
1.
Access the primary appliance that has not been configured yet and create a compound condition called "Wireless_802.1X" manually under Policy > Policy Elements > Conditions > Authorization > Compound Conditions.
2.
Configure the rule to include "
[2]Display Active Directory settings."3.
Re-image the secondary appliance that you were trying to upgrade, add the Secondary to the Primary, and wait until the Secondary node gets its configuration from the Primary.
4.
Restart the upgrade progress by breaking the pri/sec relation and doing the upgrade on the secondary again.
CSCuc21037
Cisco ISE uses PEAP for outer identity when performing authorization
Traditionally, authorization was accomplished in Cisco ISE, Release 1.1 using PEAP as the inner identity. In release 1.1.1, however, PEAP is used as the outer identity when performing authorization.
Note
It seems that the "Network Access:UserName" value is mapping to the "RADIUS Username," and only applies to PEAP-EAP-TLS authentications.
Workaround
If you would like to match on the certificate fields (for example, the Subject field), change the authorization rule to use the "Certificate:Subject" attribute and match on CN\... (rather than using the "Network Access:UserName" attribute). Cisco recommends using the attributes from the Certificate dictionary when matching certificate fields.
CSCuc22732
Cisco ISE drops RADIUS requests with no "calling-station-id" attribute
When using MAB and sending a RADIUS request to Cisco ISE, the packet is dropped if the "calling-station-id" attribute is not included.
Workaround
Configure the remote access device to send the "calling-station-id" attribute if possible.
CSCuc44766
My Devices Portal descriptions missing
Periodically, after onboarding devices using the self provisioning flow (NSP) SPW, descriptions of endpoint devices may be missing form the My Devices Portal.
Note
There is no known workaround for this issue.
CSCuc50247
Cisco ISE does not recognize the certificate if the Certificate Authority name contains a space
This issue can occur when the SubCA name contains a space. Cisco ISE records "Unknown CA" during processing and adds "%20" to the string, causing EAP-TLS authenticating to fail.
Workaround
Since the "Subject" is part of the FQDN or vice versa, do not use spaces in CN.
CSCuc52368
Authenticating users using an alternative UPN fails
In Cisco ISE, Release 1.1.1 with Centrify version 4.5, authenticating users against Active Directory with an alternative UPN fails.
For example:
*. considering a domain name sec.lab and an alternative UPN of sec.alt
*. a user defined in AD as user@sec.alt
Authentication using user@sec.alt fails. The domain name is not stripped from the username prior to authentication and Cisco ISE interprets the username as user@sec.alt@sec.lab (user@2nd_UPN@domain-name).
Workaround
Modify all users to use the primary UPN.
CSCuc61143
Cisco ISE redirects to default login portal (instead of custom) when cookies are disabled
Workaround
Enable cookies on client browser.
CSCuc62197
Unable to add or edit authorization compound conditions
Adding or editing authorization compound conditions under Policy > Policy Elements > Conditions > Authorization > Compound Condition takes several minutes.
When editing and saving a Condition Expression, the entry is duplicated. If you attempt to delete a Condition Expression, Cisco ISE returns a "Please enter a valid expression for the condition" error, and when adding and saving a Condition Expression, a Condition Expression entry is removed from the Authorization Compound condition expression list.
CSCuc62197
Unable to add or edit authorization compound conditions
The following issues have been observed when attempting to add or edit authorization compound conditions:
•
When editing and saving a Condition Expression, the entry is duplicated.
•
When adding and saving a Condition Expression, a Condition Expression entry gets removed from the Authorization Compound condition expression list.
•
If attempting to delete a Condition Expression, Cisco ISE returns a "Please enter a valid expression for the condition" error.
CSCuc71950
Network device .csv import function fails if Protocol field is "radius"
When importing a .csv file of network devices to Cisco ISE running release 1.1.1 where the Protocol field is "radius," the import function may fail and leave the network devices user interface page in loading state—not displaying any devices.
Workaround
Replace "radius" with "RADIUS," and try the import operation again.
CSCuc72034
Combined Base and Advanced license generated in incorrect order
This issue has been observed where the administrator is unable to add combination Base-Advanced license file to Cisco ISE via the administrator user interface, and the appliance returns a message indicating that a Base license is required.
Workaround
Request individual Base and Advanced license files. If that does not address the issue, contact Cisco Technical Assistance Center (TAC).
CSCuc76477
First-time Guest login fails when using the "DefaultFirstLogin" attribute
This issue has been observed with an activated Group even though the user appears as "Active" on the portal.
Workaround
Use other time profiles like "DefaultOneHour" or "DefaultStartEnd."
CSCuc81940
Cisco ISE database process stops due to internal errors
As a result, you can view "ORA-00600" errors seen in the Cisco ISE database trace logs.
Workaround
Restart Cisco ISE services.
CSCuc82135
Guest accounts need to be removed from the network on suspend/delete
When a guest user is deleted from the system, the RADIUS sessions associated with that guest user still exist.
Workaround
Re-issue the CoA from the Monitoring and Troubleshooting reports page for the sessions associated with that guest user.
CSCuc82135
Guests need to be removed from the network on Suspend/Delete/Expiration
When a guest user is deleted from the system, the RADIUS sessions associated with that guest user still exists.
Workaround
Reissue the Change of Authorization using the session information from Monitoring reports for the sessions associated with that guest user.
CSCuc91726
My Devices Portal friendly name is not working
Unable to access My Devices Portal using the URL specified in the "Default My Devices Portal URL" field on the Web Portal Management > Settings > General > Ports page after upgrade to release 1.1.1.
Workaround
Go to the Web Portal Management > Settings > General > Ports page and click Save. This will update Cisco ISE tomcat configuration files with the changes necessary for the redirect to work. (Note that this will restart the Cisco ISE appliances.)
CSCuc95915
Cisco ISE, Release 1.1.1 system database becomes full
This issue may be addressed by obtaining the updated Oracle version 11.2.0.2 (Server Patch Set) and applying it to Cisco ISE, which will be available in an upcoming release of Cisco ISE.
CSCud02566
Administration ISE node not able to join non-Administration ISE nodes to Active Directory
When Cisco ISE nodes are deployed in different domains or sub-domains and you attempt to join any Cisco ISE node (except another Administration ISE node) to Active Directory, the operation fails and returns a "No Response from ISE Node" error message.
To ensure the Active Directory join operation is successful, ensure that:
•
The Cisco ISE nodes in your deployment are not in different domains (e.g., Administration ISE node as pap1.sj.cisco.com Policy Service node1: pdp1.hyd.cisco.com, Policy Service node2: pdp2.webex.com would cause this issue)
•
The Cisco ISE node you are trying to join to Active Directory is NOT another Administration ISE node
•
You are not trying to join Active Directory from the Administrator web portal on the Administration ISE node
Workaround
Go to the respective Administrator web portal on the non-Administration ISE node and join that node to Active Directory, instead of trying to join using the Administrator web portal on the Administration ISE node.
CSCud08618
Profiler is not recording all of the expected DHCP probe attributes
This issue may come up if padding <0's> appear between fields.
Workaround
Use an IOS sensor on the network access device or a combination of other probes to achieve similar results.
CSCud31796
External RBAC fails if user member of group containing apostrophe
When the RBAC function utilizes an external identity store (AD, LDAP), group mapping fails for a user with the correct group(s) to gain access to the administrator user interface, and a "Authentication failure for user: username: No admin groups" message is displayed:
Cisco recommends renaming all groups in the external identity store so that they do not contain apostrophes, and removing any users participating in Cisco ISE administration from any external groups that contain apostrophes.
Note
There is no known workaround for this issue.
CSCud36451
Swapped NICs seen on Cisco ISE 3315s
Some Cisco ISE 3315 appliances running Cisco ISE, Release 1.x appear as though NICs have been "swapped" with other NICs. (GigabitEthernet0 maybe end up being eth3, for example.)
Workaround
You can try to reimage the machine, but results have been mixed.
CSCue05861
Cisco ISE imports duplicate attributes which corrupt the system
Cisco ISE discarding RADIUS packets and returns a "Network Device Not found" message when duplicate RADIUS attributes are imported in the dictionary.
Workaround
Remove any duplicate RADIUS attributes and restart Cisco ISE services.
CSCue11380
Mozilla Firefox18 is not compatible for viewing reports
System administrators running Firefox 18 may not be able to view pie charts in the Operations > Catalog > User > Guest Sponsor Summary Report page. This is likely due to the fact that the current ACCUTE version used in Cisco ISE is not supported by the latest versions of Firefox.
CSCue16801
Cisco ISE Reports do not show all data when the report period crosses years
The Cisco ISE report does not display any entries later than 31 December when the report period spans multiple years.
Workaround
You may use a time period falling within a single calendar year.
CSCue38038
Users are unable to log in when cookies are disabled
Users who are not accessing the Cisco ISE network via client provisioning or native supplicant provisioning are unable to log in using the Guest Portal and receive a "Cookies are disabled, please enable cookies" error message on the page.
Note
For Android devices (Samsung Galaxy, Motorola Tab) using default browsers, no warning message is displayed if cookies are disabled, and the end user is redirected to the login page without any warning.
Workaround
End users may resolve this issue by enabling cookies in their browser.
CSCug66959
Cisco ISE displays Certification Expiration alarms for all nodes in the deployment.
You might receive Certification Expiration warning messages in Cisco ISE, Release 1.1.x deployment. This alarm gets triggered because of an issue in Cisco ISE 1.1.x and can be ignored.
Workaround
Delete and import the certificates again.
CSCug79657
Catalyst 3850 fails to profile an endpoint coming from Wireless MAB/MAC-Filtering-ISE
While connecting to wireless MAB from Windows 7 client using Catalyst 3850 switch, the client is not able to connect to MAB SSID due to missing attributed in the RADIUS packet sent by the switch. The endpoints do not get profiled and the MAB request fails.
Workaround
Add the additional configuration 'radius-server attribute 31 send nas-port-detail mac-only' in the switch.
CSCug79736
Redirection is unsuccessful intermittently at client from Catalyst 3850 Switch
While authenticating clients with wireless MAB/Dot1x using Catalyst 3850, the redirection to pages like Client Provisioning, Native Supplicant Provisioning, or Guest Portal does not happen automatically.
Workaround
Clear the existing session in the switch, and then try again.
CSCug83908
Getting Blank Page for Client Provisioning Redirect if JavaScript is disabled
A blank page is displayed when a Client Provisioning redirect occurs and JavaScript is disabled. This issued occurs on IE, Firefox, or Chrome when a normal dot1X flow is configured and a device connects to a dot1X SSID. It also occurs if a Guest user comes through MAC Address Bypass (MAB) and Client Provisioning is configured for Guest users.
Workaround
There is no known workaround for this issue.
CSCug85725
Cisco ISE patch may not work as expected if you run the application reset-config ise command from the CLI after patch installation.
Some of the bug fixes resolved in the patch are uninstalled when you run the application reset-config command after patch installation.
Workaround
We recommend that you to uninstall the applied patch(es) first before running the application reset-config command and then install the patch(es) as necessary once the Cisco ISE application configuration is reset.
CSCug85972
Sometimes, the Authorization Policy page is not listing authorization policies in the Mozilla Firefox 20.0.0 browser
The Mozilla Firefox 20.0.0 browser displays authorization policies intermittently while editing endpoint identity groups when they are used in authorization policies. It displays all authorization policies properly, if you navigate away from the Authorization Policy page and return back to the Authorization Policy page.
CSCuh05898
Message should say "Enable JavaScript" instead of "Enable Java" in MAC OSX
This issue occurs on the Mac OSX and the Safari browser when JavaScript is disabled on the client and a single SSID flow is configured. The wrong message is displayed when the Safari browser is redirected to the NSP portal.
Workaround
There is no known workaround for this issue.
CSCuh09116
Inconsistent message when JavaScript is disabled in Android browser
When JavaScript is disabled and an Authorization policy is configured for either as single or dual SSID BYOD flows, a message displayed saying that "JavaScript is disabled." but the instructions for enabling JavaScript are for either the Chrome browser or the Safari browser.
Workaround
There is no known workaround for this issue.
CSCuh29820
Windows surface tablets are being detected as Microsoft Workstations EP
Windows surface tablets hit the wrong authentication policy, which leads to issues in the BYOD/Guest Flow.
Workaround
There is no known workaround for this issue.
CSCuh37511
Unexpected Acct-Status-Type: [Stop] for method MAB after URL redirect
While trying wired MAB to Dot1x with PEAP flow in a Windows 7 client using WS-C3780-48P-S, it is not redirected to the Client Provisioning page. The issue happens as the switch sends Accounting Stop request before being directed to the Client Provisioning page.
Workaround
Disconnect and connect the network adaptor after NSP is finished to get the Client Provisioning page.
Cisco ISE Release 1.1.x Resolved SPW Caveats
The following tables list the resolved SPW caveats in Cisco ISE Release 1.1.x.
Cisco ISE Release 1.1.4 Resolved Caveats
The following table lists the resolved server-side caveats in Cisco ISE, Release 1.1.4.
Cisco ISE Release 1.1.3 Resolved Caveats
The following table lists the resolved server-side caveats in Cisco ISE, Release 1.1.3.
Cisco ISE Release 1.1.2 Resolved Caveats
The following table lists the resolved server-side caveats in Cisco ISE, Release 1.1.2.
Cisco ISE Release 1.1.1 Resolved Caveats
The following table lists the resolved server-side caveats in Cisco ISE, Release 1.1.1.
Known Issues
•
Cisco ISE Hostname Character Length Limitation with Active Directory
•
Windows Internet Explorer 8 Known Issues
–
Issue Accessing the Cisco ISE Administrator User Interface
–
Cisco Secure ACS-to-Cisco ISE Migration User Interface Issue Using IE8
–
User Identity Groups User Interface Issue With IE 8
•
Issues With 2k Message Size in Monitoring and Troubleshooting
•
Issues With More Than Three Users Accessing Monitoring and Troubleshooting Concurrently
•
Cisco IP phones using EAP-FAST
•
Internationalization and Localization
•
Issues with Monitoring and Troubleshooting Restore
Cisco ISE Release 1.1.3 and Earlier Does Not Support Google Chrome For the Administrative User Interface
Google Chrome is not a supported browser for use with the Administrative User Interface of the Cisco Identity Service Engine (ISE), Release 1.1.3 and earlier versions.
If you use Google Chrome to edit the authorization policy rules, the policy ranking order might change, which impacts authorization of end users.
This issue is limited to authenticated admin users with permissions to manage Cisco ISE authorization polices. This issue does not apply to end users who use Google Chrome for web authentication for network access.
Cisco ISE Hostname Character Length Limitation with Active Directory
It is important that Cisco ISE hostnames be limited to 15 characters or less in length, if you use Active Directory on your network. Active Directory does not validate hostnames larger than 15 characters. This can cause a problem if you have multiple ISE hosts in your deployment whose hostnames are identical through the first 15 characters, and are only distinguishable by the characters that follow (the first 15).
Windows Internet Explorer 8 Known Issues
•
Issue Accessing the Cisco ISE Administrator User Interface
•
Cisco Secure ACS-to-Cisco ISE Migration User Interface Issue Using IE8
•
User Identity Groups User Interface Issue With IE 8
Issue Accessing the Cisco ISE Administrator User Interface
When you access the Cisco ISE administrator user interface using the host IP address as the destination in the Internet Explorer 8 address bar, the browser automatically redirects your session to a different location. This situation occurs when you install a real SSL certificate issued by a Certificate Authority like VeriSign.
If possible, Cisco recommends using the Cisco ISE hostname or fully qualified domain name (FQDN) you used to create the trusted SSL certificate to access the administrator user interface via Internet Explorer 8.
Cisco Secure ACS-to-Cisco ISE Migration User Interface Issue Using IE8
There is a known migration consideration that affects successful migration of Cisco Secure ACS 5.1/5.2 data to the Cisco ISE appliance using the Cisco Secure ACS 5.1/5.2-ISE 1.0 Migration Tool.
The only currently supported browser for downloading the migration tool files is Firefox version 3.6.x. Microsoft Windows Internet Explorer (IE8 and IE7) browsers are not currently supported for this function.
For more information, see the Cisco Identity Services Engine Migration Guide for Cisco Secure ACS 5.1 and 5.2, Release 1.1.x.
User Identity Groups User Interface Issue With IE 8
If you create and operate 100 User Identity Groups or more, a script in the Cisco ISE administrator user interface Administration > Identity Management > User Identity Groups page can cause Internet Explorer 8 to run slowly, looping until a pop-up appears asking you if you want to cancel the running script. (If the script continues to run, your computer might become unresponsive.)
Issues With 2k Message Size in Monitoring and Troubleshooting
Cisco ISE monitoring and troubleshooting functions are designed to optimize data collection performance messages of 8k in size. As a result, you may notice a slightly different message performance rate when compiling 2k message sizes regularly.
Issues With More Than Three Users Accessing Monitoring and Troubleshooting Concurrently
Although more than three concurrent users can log into Cisco ISE and view monitoring and troubleshooting statistics and reports, more than three concurrent users accessing Cisco ISE can result in unexpected behavior like (but not limited to) monitoring and troubleshooting reports and other pages taking excessive amounts of time to launch, and the application sever restarting on its own.
Inline Posture Restrictions
•
Inline Posture is not supported in a virtual environment, such as VMware.
•
The Simple Network Management Protocol (SNMP) Agent is not supported by Inline Posture.
•
The Cisco Discovery Protocol (CDP) is not supported by Inline Posture.
Cisco IP phones using EAP-FAST
Cisco ISE, Release 1.0 does not support Cisco IP phones that are using EAP-FAST with certificates. Cisco recommends using EAP-TLS with IP phones in your network.
Internationalization and Localization
This section covers the known issues relating to internationalization and localization.
Custom Language Templates
If you create a custom language template with a name that conflicts with a default template name, your template is automatically renamed after an upgrade and restore. After an upgrade and restore, default templates revert back to their default settings, and any templates with names that conflict with defaults are renamed as follows: user_{LANG_TEMP_NAME}.
Issues with Monitoring and Troubleshooting Restore
During the Monitoring and Troubleshooting restore, Cisco ISE application on the Monitoring node restarts and the GUI is unavailable until the restore completes.
Documentation Updates
Related Documentation
This section provides lists of related release-specific and platform-specific documentation.
Release-Specific Documents
Table 45 lists the product documentation available for the Cisco ISE Release. General product information for Cisco ISE is available at http://www.cisco.com/go/ise. End-user documentation is available on Cisco.com at http://www.cisco.com/en/US/products/ps11640/tsd_products_support_series_home.html.
Table 45 Product Documentation for Cisco Identity Services Engine
Release Notes for the Cisco Identity Services Engine, Release 1.1.x
http://www.cisco.com/en/US/products/ps11640/prod_release_notes_list.html
Cisco Identity Services Engine Network Component Compatibility, Release 1.1.x
http://www.cisco.com/en/US/products/ps11640/products_device_support_tables_list.html
Cisco Identity Services Engine User Guide, Release 1.1.x
http://www.cisco.com/en/US/products/ps11640/products_user_guide_list.html
Cisco Identity Services Engine Hardware Installation Guide, Release 1.1.x
http://www.cisco.com/en/US/products/ps11640/prod_installation_guides_list.html
Cisco Identity Services Engine Upgrade Guide, Release 1.1.x
http://www.cisco.com/en/US/products/ps11640/prod_installation_guides_list.html
Cisco Identity Services Engine Migration Guide for Cisco Secure ACS 5.1 and 5.2, Release 1.1.x
http://www.cisco.com/en/US/products/ps11640/prod_installation_guides_list.html
Cisco Identity Services Engine Sponsor Portal User Guide, Release 1.1.x
http://www.cisco.com/en/US/products/ps11640/products_user_guide_list.html
Cisco Identity Services Engine CLI Reference Guide, Release 1.1.x
http://www.cisco.com/en/US/products/ps11640/prod_command_reference_list.html
Cisco Identity Services Engine API Reference Guide, Release 1.1.x
http://www.cisco.com/en/US/products/ps11640/prod_command_reference_list.html
Cisco Identity Services Engine Troubleshooting Guide, Release 1.1.x
http://www.cisco.com/en/US/products/ps11640/prod_troubleshooting_guides_list.html
Regulatory Compliance and Safety Information for Cisco Identity Services Engine, Cisco 1121 Secure Access Control System, Cisco NAC Appliance, Cisco NAC Guest Server, and Cisco NAC Profiler
http://www.cisco.com/en/US/products/ps11640/prod_installation_guides_list.html
Cisco Identity Services Engine In-Box Documentation and China RoHS Pointer Card
http://www.cisco.com/en/US/products/ps11640/products_documentation_roadmaps_list.html
Platform-Specific Documents
Links to other platform-specific documentation are available at the following locations:
•
Cisco ISE
http://www.cisco.com/en/US/products/ps11640/prod_installation_guides_list.html•
Cisco NAC Appliance
http://www.cisco.com/en/US/products/ps6128/tsd_products_support_series_home.html•
Cisco NAC Profiler
http://www.cisco.com/en/US/products/ps8464/tsd_products_support_series_home.html•
Cisco NAC Guest Server
http://www.cisco.com/en/US/products/ps10160/tsd_products_support_series_home.html•
Cisco Secure ACS
http://www.cisco.com/en/US/products/ps9911/tsd_products_support_series_home.htmlObtaining Documentation and Submitting a Service Request
For information on obtaining documentation, using the Cisco Bug Search Tool (BST), submitting a service request, and gathering additional information, see What's New in Cisco Product Documentation at: http://www.cisco.com/en/US/docs/general/whatsnew/whatsnew.html.
Subscribe to What's New in Cisco Product Documentation, which lists all new and revised Cisco technical documentation, as an RSS feed and deliver content directly to your desktop using a reader application. The RSS feeds are a free service.
his document is to be used in conjunction with the documents listed in the "Related Documentation" section.
Cisco and the Cisco logo are trademarks or registered trademarks of Cisco and/or its affiliates in the U.S. and other countries. To view a list of Cisco trademarks, go to this URL: www.cisco.com/go/trademarks. Third-party trademarks mentioned are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (1110R)
Any Internet Protocol (IP) addresses and phone numbers used in this document are not intended to be actual addresses and phone numbers. Any examples, command display output, network topology diagrams, and other figures included in the document are shown for illustrative purposes only. Any use of actual IP addresses or phone numbers in illustrative content is unintentional and coincidental.
© 2013 Cisco Systems, Inc. All rights reserved.