Feedback Feedback
|
Table Of Contents
Cisco ASA 5500 Migration to Version 8.3 and Later
Automatic Backup of the Old Configuration, NAT Migration File, Bootup Error Log
Saving the Migrated Configuration
Real IP Addresses in Access List Migration
Features That Use Real IP Addresses
Features That Continue to Use Mapped IP Addresses
Real IP Address Migration Naming Conventions
Sample Real IP Address Migration
Real IP Address Migration Messages and Limitations
Real IP Address Migration Messages
For Interface IP Address in ACE, Real vs. Mapped Status Cannot Be Determined
Preserving the Order of NAT Rules
NAT Migration Guidelines and Limitations
Sample NAT Migration from 8.3 and 8.4 to 8.4(2)
Sample NAT Migration from 8.2 and Earlier
Network and Service Object Migration
Supported Features for Objects
Object Migration Naming Conventions
name Command Naming Conventions
Inline IP Address Naming Conventions
Inline Protocol Naming Conventions
Network Object Naming Conventions with Multiple global Commands with the Same NAT ID
Information About Activation Key Compatibility
Cisco ASA 5500 Migration to Version 8.3 and Later
Released: March 8, 2010
Updated: April 3, 2013This guide describes the configuration migration process when you upgrade from an earlier version of the Cisco ASA 5500 operating system (OS) to Version 8.3 and later.
This guide includes the following sections:
•
Real IP Addresses in Access List Migration
•
Network and Service Object Migration
Upgrading the Software
To upgrade the software using the CLI, see the "Managing Software and Configurations" chapter in Cisco ASA 5500 Series Configuration Guide using the CLI:
http://www.cisco.com/en/US/docs/security/asa/asa83/configuration/guide/admin_swconfig.html
To upgrade the software using ASDM, see the "Managing Software and Configurations" chapter in Cisco ASA 5500 Series Configuration Guide using ASDM:
http://www.cisco.com/en/US/docs/security/asa/asa83/asdm63/configuration_guide/admin_swconfig.html
Information About Migration
This section describes the migrated features, automatic backup of the original configuration file, and saving your new migrated configuration. This section includes the following topics:
•
Automatic Backup of the Old Configuration, NAT Migration File, Bootup Error Log
•
Saving the Migrated Configuration
Migrated Features
The major changes in Version 8.3 that require migration are as follows:
•
Real IP addresses in access lists, where access lists are used in supported features—When using NAT or PAT, you used to have to specify the mapped addresses and ports in an access list for all features that use access lists. Now, for several supported features, you must use the real, untranslated IP address and ports. (Other features continue to use the mapped IP address).
•
NAT—The NAT feature has been redesigned for increased flexibility and functionality. All NAT and NAT-related commands have been redesigned.
•
Named Network and Service Objects—Network and service objects are automatically created for NAT.
Note
Although you can use named network and service objects in other features, such as access lists and object groups, objects are not automatically created for any feature other than NAT.
When upgrading from 8.3 or 8.4(1) to 8.4(2), migration for static identity NAT will occur to preserve existing functionality. See the "Sample NAT Migration from 8.3 and 8.4 to 8.4(2)" section for more information.
Automatic Backup of the Old Configuration, NAT Migration File, Bootup Error Log
The old startup configuration is automatically saved in flash memory. The NAT migration file and the bootup error log, which includes any migration messages, is automatically saved to flash memory as well.
This section includes the following topics:
Backup Configuration Files
The following old startup configuration files are saved in flash memory:
•
Single mode configuration file or multiple mode system configuration—disk0:major_minor_maint_interim_startup_cfg.sav where major_minor_maint_interim is the old OS version number.
For example, 8_2_1_0_startup_cfg.sav.
•
Multiple mode context configuration (if present in flash memory)—disk0:major_minor_maint_interim_context_cfg.sav where major_minor_maint_interim is the old OS version number and context is the context name.
For example, 8_2_1_0_context1_cfg.sav.
If there is insufficient memory to save configuration files, an error message appears on the console of the ASA and is saved in the bootup error log file; any files saved as part of the migration will be removed, and the migration will be aborted.
NAT Migration File
When your NAT configuration is migrated, and the following file is added to the root directory: nat_ident_migrate. The presence of this empty file indicates that the configuration was migrated, and prevents re-migration at bootup.
Bootup Error Log File
To view the bootup error log, enter the show startup-config errors command. See the following sample log:
hostname# show startup-config errorsReading from flash...!REAL IP MIGRATION: WARNINGIn this version access-lists used in 'access-group', 'class-map','dynamic-filter classify-list', 'aaa match' will be migrated fromusing IP address/ports as seen on interface, to their real values.If an access-list used by these features is shared with per-user ACLthen the original access-list has to be recreated.INFO: Note that identical IP addresses or overlapping IP ranges ondifferent interfaces are not detectable by automated Real IP migration.If your deployment contains such scenarios, please verify your migratedconfiguration is appropriate for those overlapping addresses/ranges.Please also refer to the ASA 8.3 migration guide for a completeexplanation of the automated migration process.INFO: MIGRATION - Saving the startup configuration to fileINFO: MIGRATION - Startup configuration saved to file 'flash:8_2_1_15_startup_cfg.sav'*** Output from config line 4, "ASA Version 8.2(1)15 "NAT migration logs:INFO: NAT migration completed.Real IP migration logs:ACL <1> has been migrated to real-ip versionSaving the Migrated Configuration
The migrated configuration is in running memory only; be sure to save the configuration to the startup configuration. If you do not save it, the next time you reload, the original configuration goes through the migration process again.
•
CLI—Enter the write memory command.
•
ASDM—Click Save at the top of the window.
Real IP Addresses in Access List Migration
When using NAT or PAT, mapped addresses and ports are no longer required in an access list for several features. You should now always use the real, untranslated addresses and ports for these features. Using the real address and port means that if the NAT configuration changes, you do not need to change the access lists. This section includes the following topics:
•
Features That Use Real IP Addresses
•
Features That Continue to Use Mapped IP Addresses
•
Real IP Address Migration Naming Conventions
•
Sample Real IP Address Migration
•
Real IP Address Migration Messages and Limitations
Features That Use Real IP Addresses
The following commands and features now use real IP addresses in the access lists. All of the access-list commands used for these features are automatically migrated unless otherwise noted. For access lists that use network object groups (the object-group network command), the IP addresses within the object group are migrated to the real IP addresses.
•
access-group command
•
Modular Policy Framework match access-list command
•
Botnet Traffic Filter dynamic-filter enable classify-list command
•
AAA aaa ... match commands
•
WCCP wccp redirect-list group-list command
Note
The WCCP wccp redirect-list group-list command is not automatically migrated. The WCCP access list is downloaded after startup, so automatic migration cannot occur. You need to manually change the wccp redirect-list group-list command to use an access list with the real IP address.
For example, formerly if you wanted to allow an outside host to access an inside host that used NAT, you applied an inbound access list on the outside interface using the access-group command. In this scenario, you needed to specify the mapped address of the inside host in the access list because that address was the address that can be used on the outside network. Starting in 8.3, you need to specify the real address in the access list.
ASDM
Real IP addresses are now used in the following features instead of mapped addresses:
•
Access Rules
•
AAA Rules
•
Service Policy Rules
•
Botnet Traffic Filter classification
•
WCCP redirection
Note
WCCP redirection is not automatically migrated. The WCCP ACL is downloaded after startup, so automatic migration cannot occur. You need to manually change the ACL to use the real IP address.
Features That Continue to Use Mapped IP Addresses
The following features use access lists, but these access lists will continue to use the mapped values as seen on an interface:
•
IPSec access lists
•
capture command access lists
•
Per-user access lists
•
Routing protocol access lists
•
All other feature access lists...
Real IP Address Migration Naming Conventions
•
In most cases after migration, the new access-list commands will be recreated with the original name so there will be no changes to the configuration that references the access list name. If an access list is applied to two or more features, and the conversion results in different ACEs, then two different access lists will be created; the original access list is removed. The new access lists will have the original name with appended suffixes: oldname_migration_X, where X is a number starting with 1.
•
When contents of an object group need to be changed to the real IP addresses, a new object-group command called oldname_X is created, where X is a number starting with 1. The new object-group command is referenced in the access list.
Syslog Message Migration
For the following syslog messages, the destination IP address has been changed from mapped-ip to real-ip format so that the addresses in the syslog will match what is configured:
•
Syslog ID 106001 is changed for the access-group command.
•
Syslog ID 106100 is changed for the access-group command.
•
Syslog ID 106023 is changed for the access-group command.
•
Syslog ID 201010, 201011, 201012, 201013 are changed for the set connection command.
Sample Real IP Address Migration
Table 1 shows how access lists are migrated to use the real IP address. The NAT configuration is shown in the old configuration for reference. For NAT migration, see the "NAT Migration" section.
Real IP Address Migration Messages and Limitations
This section describes messages associated with real IP address migration. Some messages relate to configurations that cannot be migrated, and require user intervention. This section also lists any other conditions that do not result in a message. This section includes the following topics:
•
Real IP Address Migration Messages
•
For Interface IP Address in ACE, Real vs. Mapped Status Cannot Be Determined
Real IP Address Migration Messages
When you first reload with 8.3, you see the following message:
REAL IP MIGRATION: WARNING
In this version access-lists used in 'access-group', 'class-map','dynamic-filter classify-list', 'aaa match' will be migrated fromusing IP address/ports as seen on interface, to their real values.If an access-list used by these features is shared with per-user ACLthen the original access-list has to be recreated.Please refer to documentation for more details.Table 2 lists other messages you might see.
For Interface IP Address in ACE, Real vs. Mapped Status Cannot Be Determined
If you have an ACE with an IP address that belongs to an interface, but the corresponding NAT command uses the interface keyword to identify the interface IP address, then the migration script cannot match the NAT command with the ACE, and it cannot know if the IP address in the ACE is real or mapped.
In this case, the migration script will not migrate the IP address; you will have to manually change the IP address to the real IP address. Alternatively, you can change the ACE to use the interface keyword.
For example, pre-migration, outside interface PAT is defined for an inside host:
static (inside,outside) tcp interface 80 10.2.2.2 80You define an access list using the interface IP address, instead of the interface keyword:
access-list outside_access_in permit tcp any host 192.168.1.1 eq 80access-group outside_access_in in interface outsideWhen you migrate to 8.3, the access list will not be migrated to the real IP address (10.2.2.2) because the static command could not be matched to the access-list command. If you had used the interface keyword, then the access list would have migrated correctly to use the real IP address instead of the interface keyword.
To fix the access list after migration, change the access list to use the real IP address (10.2.2.2):
access-list outside_access_in permit tcp any host 10.2.2.2 eq 80NAT Migration
The NAT feature has been redesigned for increased flexibility and functionality. All NAT and NAT-related commands have been redesigned. This section describes how your NAT configuration is migrated to the new NAT commands. For ASDM users, see the relevant "ASDM" subsections. This section includes the following topics:
•
Preserving the Order of NAT Rules
•
NAT Migration Guidelines and Limitations
•
Sample NAT Migration from 8.3 and 8.4 to 8.4(2)
•
Sample NAT Migration from 8.2 and Earlier
Note
Almost all NAT configurations will migrate seamlessly. In the rare cases when user intervention is required, you will be notified. There will never be an unreported loss of security after migration. See the "NAT Migration Messages" section.
Old NAT Commands
The following commands are no longer supported; they are migrated to new commands, and are then removed from the configuration.
•
alias
•
global
•
nat (old version)
•
nat-control
•
static
•
sysopt nodnsalias—This command is not migrated; instead, configure the dns option within the new NAT commands.
ASDM
The alias command was never supported in ASDM.
New NAT Commands
Table 3 lists the new NAT commands. See also the "Supporting Commands for NAT" section.
Note
The no-proxy-arp, route-lookup, pat-pool, and round-robin keywords were added in 8.4(2).
ASDM
For ASDM, the existing NAT rules will be migrated to two new types of rules:
•
Network Object NAT:
Configuration > Firewall > Objects > Network Objects/Groups > Add/Edit Network Object.
•
Twice NAT:
Configuration > Firewall > NAT Rules
Supporting Commands for NAT
To achieve migration to the new NAT commands, additional commands are created as shown in Table 4:
See the "Network and Service Object Migration" section for more information about network and service objects, including naming conventions for these generated commands.
ASDM
ASDM has supported named network objects for a number of releases; now, the platform has the commands to properly support them as well. In addition to showing all named network objects in the configuration, ASDM automatically creates objects for any IP addresses used in the configuration; these auto-created objects are identified by the IP address, and are not present as objects in the platform configuration. If you assign a name to one of these objects, then ASDM adds the named network object to the platform configuration.
Note
ASDM no longer shows any objects derived from the name command. Previously, you might have used named objects derived from the name command in ASDM. If the name command IP address was not migrated (see the "Network and Service Object Migration" section), then these objects are replaced by auto-created objects identified by an IP address.
Preserving the Order of NAT Rules
In the old NAT configuration, the order that NAT commands were assessed depended on the type of NAT, and in some cases, the order in which the commands appeared in the configuration. The new NAT order uses a table with three sections:
•
Section 1 (twice NAT rules)—These rules are assessed based on the order they appear in the configuration. For migration purposes, this section includes migrated policy NAT rules.
•
Section 2 (network object NAT (generated) rules)—These rules are assessed according to internal rules; the order they appear in the configuration does not matter (For more information, see the Cisco ASA 5500 Series Configuration Guide using ASDM or the Cisco ASA 5500 Series Configuration Guide using the CLI). For migration purposes, this section includes regular NAT rules.
•
Section 3 (twice NAT rules that you specifically want to be evaluated after the network object NAT rules)—Like section 1, these rules are assessed in the order they appear in the configuration. However, they are assessed after section 1 and section 2 rules. This section is not used for NAT migration.
In the case of overlapping networks (for example, if a regular static NAT rule overlaps with a dynamic policy NAT rule), the regular static NAT rule will be migrated to section 1 instead of section 2 to preserve the order of the configuration. For example, the following old configuration has overlapping networks. In this case, the static command will be migrated to a twice NAT rule in section 1.
static (inside,outside) 209.165.202.129 10.1.1.6 netmask 255.255.255.255access-list NET1 permit ip 10.1.1.0 255.255.255.0 209.165.202.0 255.255.255.0nat (inside) 100 access-list NET1NAT Migration Guidelines and Limitations
•
Dynamic identity NAT (the nat 0 command) will not be migrated. See the "NAT Migration Messages" section. Static identity NAT is treated like any other static command, and is converted depending on whether it is regular or policy NAT.
•
NAT exemption (the nat 0 access-list command) is migrated differently depending on the release to which you are upgrading. See the "NAT Exemption" section for more information.
•
When upgrading to 8.4(2) from 8.3(1), 8.3(2), or 8.4(1), migration for identity NAT will occur to preserve existing functionality. See the "Sample NAT Migration from 8.3 and 8.4 to 8.4(2)" section for more information.
•
Regular NAT commands with the dns option will be migrated. The dns option in static PAT and policy NAT commands will be ignored.
•
Connection Settings in old NAT commands—Options such as conn-max, emb-limit, norandomseq, or nailed will be moved to service policies.
The following naming conventions are used for the new service policies:
–
class-map—class-conn-param-protocol-n
–
access-list—acl-conn-param-protocol-n
–
policy-map—policy-conn-param-interface
For other naming conventions related to NAT migration, see the "Object Migration Naming Conventions" section.
Sample NAT Migration from 8.3 and 8.4 to 8.4(2)
If you are already running 8.3(1), 8.3(2), or 8.4(2). then to preserve existing functionality, all identity NAT statements are migrated to use the following new keywords:
•
no-proxy-arp
•
route-lookup (routed firewall mode only)
Starting in version 8.4(2), identity NAT now performs proxy ARP and uses the NAT configuration to determine the egress interface by default. To maintain the functionality that was in 8.3(1), 8.3(2), and 8.4(2), proxy ARP is disabled, and a route lookup is performed to determine the egress interface using the new keywords. If you want to enable proxy ARP (a rare requirement) or use the NAT configuration to determine the egress interface, you must manually remove the keyword(s) after migration.
If the unidirectional keyword is present (for example, from an original migration of NAT exemption rules to 8.3(2) or 8.4(1)), then the keyword is removed.
Table 5 lists static identity NAT migration examples.
Sample NAT Migration from 8.2 and Earlier
This section includes the following topics:
Static NAT/PAT
Table 6 lists static NAT/PAT migration examples.
Dynamic NAT/PAT
Table 7 lists dynamic NAT/PAT migration examples.
NAT Exemption
NAT exemption (the nat 0 access-list command) is a form of policy NAT, and is converted to static twice NAT. Rules are created between the exempted interface and all lower-security level interfaces. For outside NAT, rules are created between the exempted interface and all higher-security level interfaces. If you enabled same security level communication, rules are also created between the exempted interface and same-security level interfaces.
These rules will be placed at the top of section 1.
NAT exemption (the nat 0 access-list command) is migrated to a twice NAT rule. See the following notes for the version you are upgrading to for specific information about how NAT exemption is migrated:
•
For Version 8.3(1)—In some cases, you might see caveat #CSCtf89372. We recommend migrating directly to 8.4(2). For more information about this caveat, see the Bug Toolkit at the following URL:
http://tools.cisco.com/Support/BugToolKit/action.do?hdnAction=searchBugs
•
For Version 8.3(2) through 8.4(1)—The unidirectional keyword was added. The unidirectional keyword only allows traffic on the source network to initiate connections. This migration change was made to fix CSCtf89372. Because NAT exemption is normally bidirectional, you might need to remove the unidirectional keyword to restore the original function. Specifically, this change adversely affects many VPN configurations that include NAT exemption rules (see CSCti36048 for this new issue). To avoid manual intervention, we recommend migrating to 8.4(2) instead.
If you are impacted by this issue, you will see a syslog message like the following:%ASA-5-305013: Asymmetric NAT rules matched for forward and reverse flows; Connection for icmp src Outside:192.168.1.5 dst inside:10.10.5.20 (type 8, code 0) denied due to NAT reverse path failure•
For Version 8.4(2) and later—The unidirectional keyword is no longer added. Instead, the new no-proxy-arp and route-lookup keywords are added. Both the CSCtf89372 and CSCti36048 caveats are resolved in this release.
The examples in this section are for a system with three interfaces: inside (level 100), outside (level 0), and dmz (level 50).
Table 8 lists NAT exemption migration examples.
NAT Control
The nat-control command is deprecated. To maintain the requirement that all traffic from a higher security interface to a lower security interface be translated, a NAT rule will be inserted at the end of section 2 for each interface to disallow any remaining traffic. The nat-control command was used for NAT configurations defined with earlier versions of the ASA. The best practice is to use access rules for access control instead of relying on the absence of a NAT rule to prevent traffic through the ASA.
Table 9 lists NAT control migration examples.
DNS Rewrite
Regular NAT commands with the dns option will be migrated. The dns option in static PAT and policy NAT commands will be ignored.
Table 10 lists DNS rewrite migration examples.
Connection Settings
Connection Settings in old NAT commands—Options such as conn-max, emb-limit, norandomseq, or nailed will be moved to service policies.
For naming conventions, see the "NAT Migration Guidelines and Limitations" section.
Table 11 lists connection setting migration examples.
Source and Destination NAT
Before 8.3, policy NAT let you specify the source and destination addresses, but NAT was only performed on the source address. In 8.3 and later, you can also configure NAT for the destination address if desired. In the old configuration to achieve this functionality, you had to configure two separate NAT rules for source and destination NAT for a single connection. As part of migration the two, independent NAT rules are tied together to form a single twice NAT command.
Table 12 lists source and destination NAT migration examples.
alias Command
The alias command translates addresses on an IP network residing on any interface into addresses on another IP network connected through a different interface.
Table 13 lists alias migration examples.
NAT Migration Messages
Some NAT configurations cannot be migrated automatically, or are slightly different from the original configuration. Table 14 lists error messages you might see, and information about the messages.
Table 14 NAT Migration Messages
Explanation Missing global command. If a nat command does not have a matching global command, the nat command will be removed and will not be migrated.
Recommended Action If you intended to have a matching global command, you will need to recreate the configuration using the new NAT commands.
Example:Old Configuration
nat (dmz) 1 10.1.1.0 255.255.255.0Migrated Configuration
Not migrated.
Explanation alias command migration. The alias command is applied between same and lower security level interfaces. After migration, the rules are added between a given interface and any. This is semantically different as the new rule applies to all interfaces including itself.
Recommended Action This is relatively safe to migrate and needs no attention in most cases. See the "alias Command" section for an example migration.
Example:Old Configuration
alias (inside) 209.165.200.225 192.168.100.10
Migrated Configuration
object network obj-192.168.100.10
host 192.168.100.10nat (any,inside) static 209.165.200.225 dnsExplanation Identity NAT not migrated. Identity NAT (the nat 0 command) is not migrated; also a nat-control command on that interface is not migrated.
Recommended Action Manually add a new Identity NAT rule using a static NAT command (either object or twice NAT).
Example:Old Configuration
nat (inside) 0 192.168.1.0 255.255.255.0
Migrated Configuration
Not migrated.
Explanation Outside static policy NAT with overlapping destination and broadcast address. You used to be able to configure the old global command to automatically remove the broadcast addresses from the global pool by using a /31 subnet. You cannot configure the same functionality in the new NAT commands. If there is a dynamic NAT rule and an outside static policy NAT rule with overlapping destinations, then the migrated configuration will include the broadcast address in the mapped source. User intervention is required to manually remove those addresses.
Recommended Action Remove the broadcast address from the mapped object.
Example:Old Configuration
nat (inside) 10 10.0.0.0 255.0.0.0
global (outside) 10 192.168.1.3-192.168.2.3 netmask 255.255.255.254
(The following broadcast address is automatically removed from the pool: 192.168.1.255.)
access-list SNAT extended permit ip 10.10.10.0 255.255.255.0 192.168.2.0 255.255.255.0
static (outside,inside) 10.1.1.0 access-list SNAT
Migrated Configuration
object network obj-192.168.1.3-192.168.2.3
range 192.168.1.3 192.168.2.3(192.168.1.255 is not automatically removed from this pool. To avoid assigning 192.168.1.255, you should instead create a network group, and use it in the nat command:
object network global_pool1
range 192.168.1.3 192.168.1.254object network global_pool2
range 192.168.2.1 192.168.2.3object-group network global_pool
network-object object global_pool1network-object object global_pool2)
object network obj-10.10.10.0
subnet 10.10.10.0 255.255.255.0object network obj-10.1.1.0
subnet 10.1.1.0 255.255.255.0object network obj-192.168.2.0
subnet 192.168.2.0 255.255.255.0
object network obj-10.0.0.0
subnet 10.0.0.0 255.0.0.0nat (inside,outside) dynamic obj-192.168.1.3-192.168.2.3
nat (inside,outside) source dynamic obj-10.0.0.0 obj-192.168.1.3-192.168.2.3 destination static obj-10.1.1.0 obj-10.10.10.0
nat (outside,inside) source static obj-10.10.10.0 obj-10.1.1.0 destination static obj-192.168.2.0 obj-192.168.2.0
Explanation sysopt nodnsalias command not migrated. The sysopt nodnslias command is deprecated because the alias command is no longer supported.
Recommended Action Use the dns option in the new NAT commands to enable/disable DNS rewrite.
Example:Old Configuration
sysopt nodnsalias
Migrated Configuration
Not migrated.
Network and Service Object Migration
This section describes network and service object migration and includes the following topics:
•
Supported Features for Objects
Supported Features for Objects
Version 8.3 introduces named network and service objects for use with the following features:
•
NAT—See the "NAT Migration" section for more information. You can no longer use a named IP address (using the name command) in NAT.
•
Access lists—access-list command. You can no longer use a named IP address (using the name command) in an access list.
•
Object groups—object-group network and object-group service commands. Named IP addresses are still allowed in object groups, as well as network objects.
Object Migration
New network and service objects (the object network and object service commands) are substituted into existing commands in the following cases:
•
For each network object NAT command, an object network command is created to represent the real IP address that you want to translate.
•
When new nat commands require an object instead of an inline value, network and service objects are automatically created.
•
If you use a named IP address in NAT (using the name command) and the names command is enabled, then a network object is created even if an inline IP address could be used in the new nat command.
•
If an access-list command includes an IP address that was used in NAT, and the NAT migration created a network object for that IP address, then the network object replaces the IP address in the access-list command.
•
If you use a named IP address in the access-list command (using the name command) and the names command is enabled, then an object replaces the name.
•
For multiple global commands that share the same NAT ID, a network object group is created that contains the network objects created for the inline IP addresses.
Objects are not created for the following cases:
•
A name command exists in the configuration, but is not used in a nat or access-list command.
•
An inline value that is still allowed in the nat command.
•
name commands used under object-group commands.
•
IP addresses used in access-list commands that are not used in NAT or named with a name command.
Note
The name commands continue to exist in your configuration for use with other features that do not yet support network objects.
ASDM
ASDM has supported named network objects for a number of releases; now, the platform has the commands to properly support them as well.
ASDM also automatically creates non-named objects for any IP addresses used in the configuration. These auto-created objects are identified by the IP address only, do not have a name, and are not present as named objects in the platform configuration.
If you manually assign a name to one of these non-named ASDM objects, then ASDM adds the named network object to the platform configuration. If you do not add a name, it remains an ASDM-only object.
When the ASA creates named objects as part of the migration, the matching non-named ASDM-only objects are replaced with the named objects. The only exception are non-named objects in a network object group. When the ASA creates named objects for IP addresses that are inside a network object group, ASDM retains the non-named objects as well, creating duplicate objects in ASDM. To merge these objects, choose Tools > Migrate Network Object Group Members.
Note
ASDM no longer shows any objects derived from the name command. Previously, you might have used named objects derived from the name command in ASDM. If the name command IP address was not migrated, then these objects are replaced by auto-created objects identified by an IP address.
Object Migration Naming Conventions
This section includes the following topics:
•
name Command Naming Conventions
•
Inline IP Address Naming Conventions
•
Inline Protocol Naming Conventions
•
Network Object Naming Conventions with Multiple global Commands with the Same NAT ID
For details about when a name or IP address is migrated, see the "Object Migration" section.
name Command Naming Conventions
When the names command is enabled, then for migrated name commands, the same name is used for the object network command.
For example, for the following name command used in NAT:
name 10.1.1.1 testAn object network command is created:
object network testhost 10.1.1.1If the names command is not enabled, and IP addresses are migrated to network objects, then your configuration might include network objects where the IP addresses are the same as in name commands, but the name of the network object is automatically generated (see the "Inline IP Address Naming Conventions" section), and not the same name as the name command.
Inline IP Address Naming Conventions
For migrated IP addresses used inline, network objects are created using the following naming convention:
•
Hosts and subnets—obj-a.b.c.d.
Note
Only one instance of NAT can be enabled on an object. If you have more than one NAT policy applied on a given host or subnet, then a separate network object will be created: obj-a.b.c.d-01.
Table 15 lists host and subnet inline object migration naming examples.
Table 15 Host and Subnet Inline Object Migration Naming Examples
10.76.6.111 255.255.255.255
obj-10.76.6.111
10.76.0.0 255.255.0.0
obj-10.76.0.0
•
Ranges—obj-a.b.c.d-p.q.r.s
Table 16 lists range inline object migration naming examples.
Table 16 Range Inline Object Migration Naming Examples
10.76.6.111-10.76.6.112
obj-10.76.6.111-10.76.6.112
Inline Protocol Naming Conventions
For migrated protocols used inline, service objects are created using the following naming convention: obj-inline_text.
Table 17 lists protocol inline object migration naming examples.
Table 17 Protocol Inline Object Migration Naming Examples
tcp source range 20 50 eq 2000
obj-tcp_source_range_20_50_eq_2000
tcp gt 1500
obj-tcp_gt_1500
Network Object Naming Conventions with Multiple global Commands with the Same NAT ID
For multiple global commands that share the same NAT ID, a network object group is created that contains the network objects created for the inline IP addresses. The following naming convention is used: og-global-interface_nat-id.
Old Configuration
global (outside) 1 10.76.6.111
global (outside) 1 10.76.6.109-10.76.6.110
New Network Objects and Groups
object network obj-10.76.6.111
host 10.76.6.111object network obj-10.76.6.109-10.76.6.110
range 10.76.6.109-10.76.6.110object-group og-global-outside_1
network-object obj-10.76.6.111network-object obj-10.76.6.109-10.76.6.110Downgrading from Version 8.3
When you upgrade to Version 8.3, your configuration is migrated. The old configuration is automatically stored in flash memory. For example when you upgrade from 8.2(1) to 8.3(1), the old 8.2(1) configuration is stored in flash memory in a file called 8_2_1_0_startup_cfg.sav.
This section describes how to downgrade, and includes the following topics:
•
Information About Activation Key Compatibility
Information About Activation Key Compatibility
Your activation key remains compatible if you upgrade to the latest version from any previous version. However, you might have issues if you want to maintain downgrade capability:
•
Downgrading to Version 8.1 or earlier—After you upgrade, if you activate additional feature licenses that were introduced before 8.2, then the activation key continues to be compatible with earlier versions if you downgrade. However if you activate feature licenses that were introduced in 8.2 or later, then the activation key is not backwards compatible. If you have an incompatible license key, then see the following guidelines:
–
If you previously entered an activation key in an earlier version, then the ASA uses that key (without any of the new licenses you activated in Version 8.2 or later).
–
If you have a new system and do not have an earlier activation key, then you need to request a new activation key compatible with the earlier version.
•
Downgrading to Version 8.2 or earlier—Version 8.3 introduced more robust time-based key usage as well as failover license changes:
–
If you have more than one time-based activation key active, when you downgrade, only the most recently activated time-based key can be active. Any other keys are made inactive. If the last time-based license is for a feature introduced in 8.3, then that license still remains the active license even though it cannot be used in earlier versions. Reenter the permanent key or a valid time-based key.
–
If you have mismatched licenses on a failover pair, then downgrading will disable failover. Even if the keys are matching, the license used will no longer be a combined license.
–
If you have one time-based license installed, but it is for a feature introduced in 8.3, then after you downgrade, that time-based license remains active. You need to reenter the permanent key to disable the time-based license.
Performing the Downgrade
To downgrade from 8.3, perform the following steps.
Detailed Steps
For the CLI:
Step 1
Enter the following command:
hostname(config)# downgrade [/noconfirm] old_image_url old_config_url [activation-key old_key]Where the /noconfirm option downgrades without prompting. The image_url is the path to the old image on disk0, disk1, tftp, ftp, or smb. The old_config_url is the path to the saved, pre-migration configuration (by default this was saved on disk0). If you need to revert to a pre-8.3 activation key, then you can enter the old activation key.
This command is a shortcut for completing the following functions:
1.
Clearing the boot image configuration (clear configure boot).
2.
Setting the boot image to be the old image (boot system).
3.
(Optional) Entering a new activation key (activation-key).
4.
Saving the running configuration to startup (write memory). This sets the BOOT environment variable to the old image, so when you reload, the old image is loaded.
5.
Copying the old configuration to the startup configuration (copy old_config_url startup-config).
6.
Reloading (reload).
For example:
hostname(config)# downgrade /noconfirm disk0:/asa821-k8.bin disk0:/8_2_1_0_startup_cfg.savFor ASDM:
Step 1
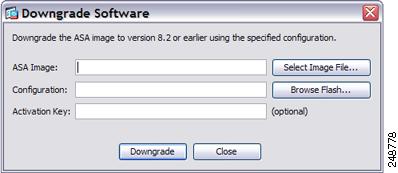
Choose Tools > Downgrade Software.
The Downgrade Software dialog box appears.
Figure 1 Downgrade Software
Step 2
For the ASA Image, click Select Image File.
The Browse File Locations dialog box appears.
Step 3
Click one of the following radio buttons:
•
Remote Server—Choose ftp, smb, or http from the drop-down list, and type the path to the old image file.
•
Flash File System—Click Browse Flash to choose the old image file on the local flash file system.
Step 4
For the Configuration, click Browse Flash to choose the pre-migration configuration file. (By default this was saved on disk0).
Step 5
(Optional) In the Activation Key field, enter the old activation key if you need to revert to a pre-8.3 activation key.
Step 6
Click Downgrade.
This tool is a shortcut for completing the following functions:
1.
Clearing the boot image configuration (clear configure boot).
2.
Setting the boot image to be the old image (boot system).
3.
(Optional) Entering a new activation key (activation-key).
4.
Saving the running configuration to startup (write memory). This sets the BOOT environment variable to the old image, so when you reload, the old image is loaded.
5.
Copying the old configuration to the startup configuration (copy old_config_url startup-config).
6.
Reloading (reload).
Cisco and the Cisco logo are trademarks or registered trademarks of Cisco and/or its affiliates in the U.S. and other countries. To view a list of Cisco trademarks, go to this URL: www.cisco.com/go/trademarks. Third-party trademarks mentioned are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (1110R)
Copyright © 2010-2013 Cisco Systems, Inc. All rights reserved.